Search the audit log
Search in Microsoft Purview Audit (Standard) and Audit (Premium) give your organization access to critical audit log event data to gain insight and further investigate user activities.
- Search jobs initiated via the compliance portal no longer require the web browser window to remain open in order to complete. These jobs will continue to run even after the browser window is closed.
- Completed search jobs are now stored for 30 days, giving you the ability to reference historical audit searches.
- Each admin Audit account user can have a maximum of 10 concurrent search jobs in progress with a maximum of one unfiltered search job.
Tip
If you're not an E5 customer, use the 90-day Microsoft Purview solutions trial to explore how additional Purview capabilities can help your organization manage data security and compliance needs. Start now at the Microsoft Purview trials hub. Learn details about signing up and trial terms.
Before you search the audit log
Be sure to review the following items before you start searching the audit log.
Audit log search is turned on by default for Microsoft 365 and Office 365 enterprise organizations. To verify that audit log search is turned on, you can run the following command in Exchange Online PowerShell:
Get-AdminAuditLogConfig | Format-List UnifiedAuditLogIngestionEnabledThe value of
Truefor the UnifiedAuditLogIngestionEnabled property indicates that audit log search is turned on. For more information, see Turn audit log search on or off.Important
Be sure to run the previous command in Exchange Online PowerShell. Although the Get-AdminAuditLogConfig cmdlet is also available in Security & Compliance PowerShell, the UnifiedAuditLogIngestionEnabled property is always
False, even when audit log search is turned on.You have to be assigned the Audit Logs or View-Only Audit Logs roles in the Microsoft Purview portal or Microsoft Purview compliance portal to search the audit log. By default, these roles are assigned to the Audit Manager and Audit Reader role groups on the Permissions page in the compliance portal. For more information, see Get started with auditing solutions. To access audit cmdlets, you must be assigned the Audit Logs or View-Only Audit Logs roles in the Exchange admin center. You can also create custom role groups with the ability to search the audit log by adding the View-Only Audit Logs or Audit Logs roles to a custom role group.
For more information, see:
When an audited activity is performed by a user or admin, an audit record is generated and stored in the audit log for your organization. The length of time that an audit record is retained (and searchable in the audit log) depends on your Office 365 or Microsoft 365 Enterprise subscription, and specifically the type of the license that is assigned to specific users.
For users assigned an Office 365 E5 or Microsoft 365 E5 license (or users with a Microsoft 365 E5 Compliance or Microsoft 365 E5 eDiscovery and Audit add-on license), audit records for Microsoft Entra ID, Exchange, and SharePoint activity are retained for one year by default. Organizations can also create audit log retention policies to retain audit records for activities in other services for up to one year. For more information, see Manage audit log retention policies.
Note
If your organization participated in the private preview program for the one-year retention of audit records, the retention duration for audit records that were generated before the general availability rollout date will not be reset.
For users assigned any other (non-E5) Office 365 or Microsoft 365 license, audit records are retained for 180 days. For a list of Office 365 and Microsoft 365 subscriptions that support unified audit logging, see the subscription requirements for Audit (Standard) and Audit (Premium).
Important
The default retention period for Audit (Standard) has changed from 90 days to 180 days. Audit (Standard) logs generated before October 17, 2023 are retained for 90 days. Audit (Standard) logs generated on or after October 17, 2023 follow the new default retention of 180 days.
Note
Even when mailbox auditing on by default is turned on, you might notice that mailbox audit events for some users aren't found in audit log searches in the compliance portal or via the Office 365 Management Activity API. For more information, see More information about mailbox audit logging.
If you want to turn off audit log search for your organization, you can run the following command in Exchange Online PowerShell:
Set-AdminAuditLogConfig -UnifiedAuditLogIngestionEnabled $falseTo turn on audit search again, you can run the following command in Exchange Online PowerShell:
Set-AdminAuditLogConfig -UnifiedAuditLogIngestionEnabled $trueFor more information, see Turn off audit log search.
The underlying cmdlet used to search the audit log is an Exchange Online cmdlet, which is Search-UnifiedAuditLog. That means you can use this cmdlet to search the audit log instead of using the search tool on the Audit page in the compliance portal. You have to run this cmdlet in Exchange Online PowerShell. For more information, see Search-UnifiedAuditLog.
For information about exporting the search results returned by the Search-UnifiedAuditLog cmdlet to a CSV file, see the "Tips for exporting and viewing the audit log" section in Export, configure, and view audit log records.
If you want to programmatically download data from the audit log, we recommend that you use the Office 365 Management Activity API instead of using a PowerShell script. The Office 365 Management Activity API is a REST web service that you can use to develop operations, security, and compliance monitoring solutions for your organization. For more information, see Office 365 Management Activity API reference.
Microsoft Entra ID is the directory service for Microsoft 365. The unified audit log contains user, group, application, domain, and directory activities performed in the Microsoft 365 admin center or in the Azure management portal. For a complete list of Microsoft Entra events, see Microsoft Entra audit Report Events.
Microsoft doesn't guarantee a specific time after an event occurs for the corresponding audit record to be returned in the results of an audit log search. For core services (such as Exchange, SharePoint, OneDrive, and Teams), audit record availability is typically 60 to 90 minutes after an event occurs. For other services, audit record availability may be longer. However, some issues that are unavoidable (such as a server outage) may occur outside of the audit service that delays the availability of audit records. For this reason, Microsoft doesn't commit to a specific time.
To search for Power BI activities in the audit log, you have to enable auditing in the Power BI admin portal. For instructions, see the "Audit logs" section in Power BI admin portal.
Get started with search
Select the appropriate tab for the portal you're using. Depending on your Microsoft 365 plan, the Microsoft Purview compliance portal is retired or will be retired soon.
To learn more about the Microsoft Purview portal, see Microsoft Purview portal. To learn more about the Compliance portal, see Microsoft Purview compliance portal.
Complete the following steps to get started with search:
Sign into the Microsoft Purview portal.
Select the Audit solution card. If the Audit solution card isn't displayed, select View all solutions and then select Audit from the Core section.
On the Search page, configure the following search criteria as applicable:
Date and time range (UTC): The last seven days are selected by default. Select a date and time range to display the events that occurred within that period. The date and time are presented in Coordinated Universal Time (UTC). The maximum date range that you can specify is 180 days. An error is displayed if the selected date range is greater than 180 days.
Tip
If you're using the maximum date range of 180 days, select the current time for the Start date. Otherwise, you'll receive an error saying that the start date is earlier than the end date. If you've turned on auditing within the last 180 days, the maximum date range can't start before the date that auditing was turned on.
Keyword Search: Enter a keyword or phrase to search for in the audit log. The keyword or phrase is searched for in the audit log or in the file, folder, or sites (if specified) for the search. To search for text that contains special characters, replace the special characters with an asterisk(*) in your keyword search. For example, to search for test_search_document, use test*search*document.
Important
Terms entered in the Keyword Search field are only searched within indexed content (content within the Audit common schema). Audit data content in the audit log isn't searched for these keywords.
Admin Units: Select the drop-down list to display the administrative units you want the audited activities scoped to for your search. You can select one or more administrative units to scope your search to. Leave this box blank to return entries for all administrative units in your organization.
Activities - friendly names: Select the drop-down list to display the friendly names for audited activities that you can search for. Friendly names for user and admin activities are organized into groups of related activities. Using friendly names, you can select specific audited activities or you can select the activity group name to select all activities in the group. You can also select a selected activity to clear the selection. To search for a friendly name for the activities in the list, use the search box over the list.
Activities - operations names: Enter the exact operation names to search for audited activities to include in your search results. You can enter one or more operation names, separated by commas. This search criterion is similar to previous searches only available in PowerShell and provides greater flexibility helping you find the data that you need.
Important
Operation names must be entered exactly as they are named. If operation names are entered incorrectly, no results are returned.
For example, to search for all activities related to enabling and disabling information barriers for a SharePoint site in your organization, you would:
- Review the audit activities article to find the exact operation name for the information barriers activities you want to search for. In this example, the operation names are SPOIBIsEnabled and SPOIBIsDisabled.
- Enter SPOIBIsEnabled,SPOIBIsDisabled in operation search field. We recommend copying and pasting the operation names directly from the article to the operation search field to ensure that they're entered correctly and without typos.
Record types: Select the drop-down list to display the record types for audited activities that you can search for. You can select one or more record types to search for. To search for a record type in the list, use the search box over the list.
Specific record types are associated with specific Microsoft services and applications. For example, if you wanted to scope your search for specific record types associated with sensitivity labels in Microsoft Purview Information Protection (MIP), you could select the MIPLabel, MipAutoLabelExchangeItem, MipAutoLabelSharePointItem, and MipAutoLabelSharePointPolicyLocation record types from the list.Search name: Enter in a custom name for your search job. This name is used to identify your search job in the search job history. If you don't enter a name, the search job is automatically named using a combination of the date and time defined for the search and other defined search criteria values.
Users: Select this field and choose the names one or more users to display search results for. The audit log entries for the selected activity performed by the users you select in this box are displayed in the list of results. Leave this box blank to return entries for all users (and service accounts) in your organization.
File, folder, or site: Enter some or all of a file or folder name to search for activity related to the file of folder that contains the specified keyword. This search criterion returns all related results for corresponding file, folders, and sites. You can also specify a URL of a file or folder. If you use a URL, be sure the type the full URL path or if you type a portion of the URL, don't include any special characters or spaces (however, using the wildcard character (*) is supported). Leave this box blank to return entries for all files and folders in your organization.
Workloads: Enter or search for workload services to search for activity related to the selected workloads. Enter the name of a workload to jump to the workload in the list or scroll to the workloads you'd like to select.
Select Search to start your search job. A maximum of 10 search jobs can be run in parallel for one user account. If a user requires more than 10 search jobs, they must wait for an In progress job to finish or delete a search job.
Search job dashboard
Active and completed search jobs are displayed in the search job dashboard. The dashboard displays the following information for each search job:
- Search name: The name of the search job. The full search name for a job can be seen by hovering the cursor over the search job name.
- Job status: The status of the search job. The status can be Queued, In Progress, or Completed.
- Progress (%): The percentage of the search job that has been completed.
- Search time: The total running time that elapsed to complete the search job.
- Total results: The total number of results returned by the search job.
- Creation time: The date and time the search job was created in UTC.
- Search performed by: The user account that created the search job.
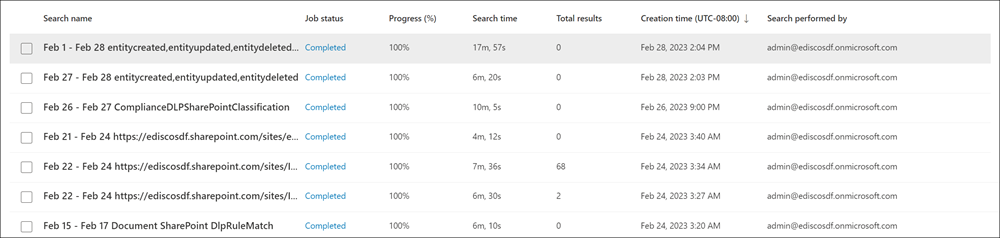
Delete search jobs by selecting the job and then selecting Delete on the command bar. Deleting a search job doesn't delete the backend data associated with search. It only deletes the search job definition and the associated search result.
To copy the search criteria for an existing search job, select the job and then select Copy this search on the command bar. The search criteria are copied to the search page and you can modify the search criteria as needed for a new search.
Search job details dashboard
To view details about a search job, select the search job. The total number of items in the job is included at the top of the dashboard. The total result number deducts duplicates, which is why it might be less than the number of items in the search job dashboard.
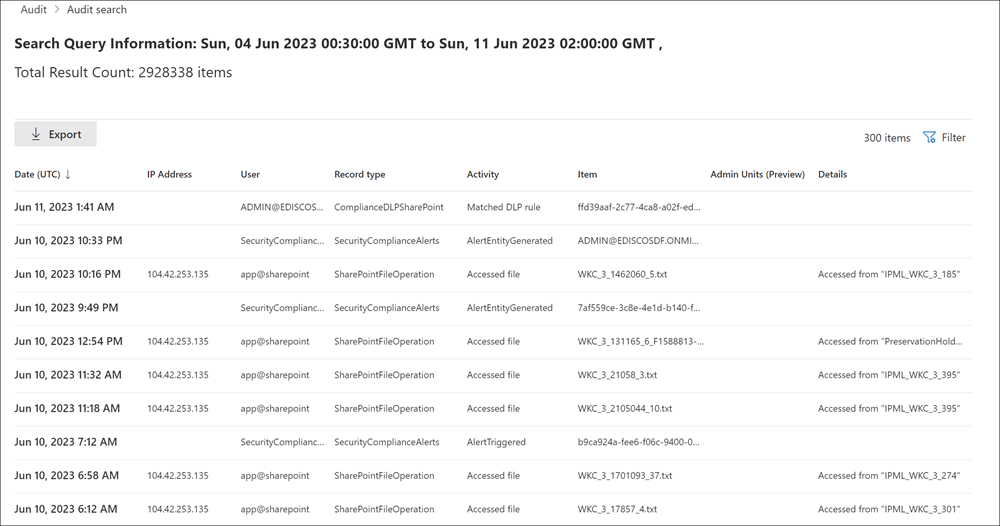
The search job details dashboard displays following information about the individual items gathered in the search job results:
- Date (UTC): The date and time the activity occurred.
- IP Address: The IP address of the device that was used to perform the activity.
- User: The user account that performed the activity.
- Record type: The record type associated with the activity.
- Activity: The friendly name of the activity that was performed.
- Item: The name of the file, folder, or site that the activity was acted on.
- Admin Units: The admin unit that the user account that performed the activity belongs to.
- Details: Additional details about the activity.
You can sort the search job items using the column headers or create a custom filter using the filter pane. Use the filter to filter the search job items for specific values for any of the dashboard column criteria. To export all search job items to a .csv file, select Export on the command bar. Export supports results up to 50 KB for Audit (Standard) and up to 500 KB (500,000 rows) for Audit (Premium).
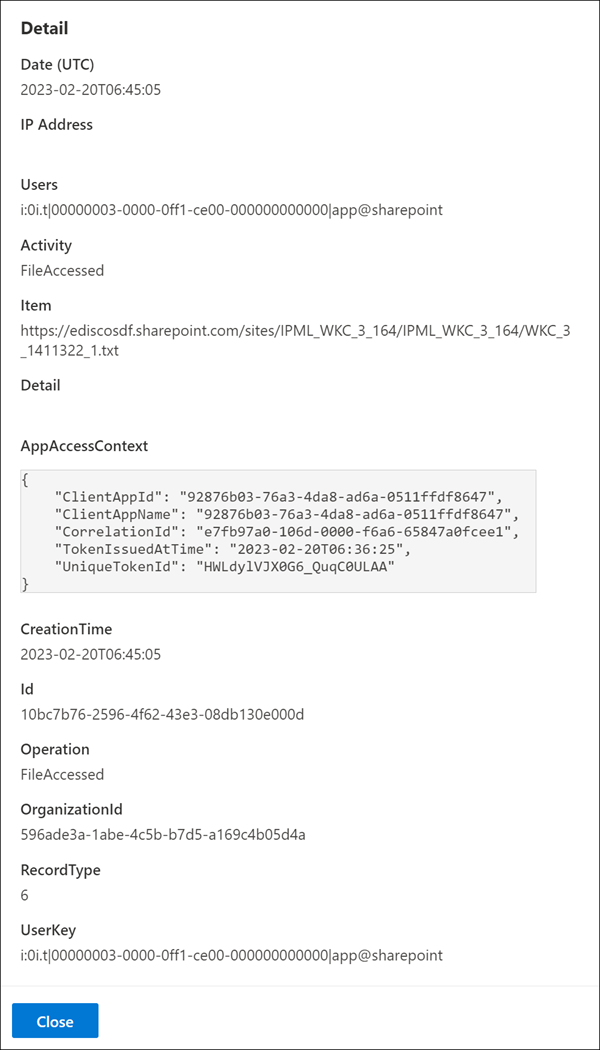
Select a specific activity to see more details about the activity in a fly-out window. The fly-out window displays the additional information about the activity.
Scoping access to audit logs using administrative units
Access to search the audit log is scoped based upon the administrative units assigned to the user accessing the audit log in the compliance portal. A restricted admin can only search and export user-generated audit logs within the scope of their administrative units. An unrestricted admin has access to all audit logs, including logs generated by non-user and system accounts. To access scoped activity logs from any Microsoft service, including Exchange mailbox activity logs, use the Search-UnifiedAuditLog cmdlet.
| Admin units assigned to admins | Admin units available to perform scoped search on | Access to search and export audit logs |
|---|---|---|
| None (Default): Unrestricted admin | All administrative units are available | Access to all activity logs from any user, non-user, or system account. |
| One or more administrative units: Restricted admin | Only those administrative units assigned to the admin are available | Access to activity logs from users with a matching administrative unit assignment. |
The following audit activities are only accessible by search queries performed by an unrestricted admin. We're working to ensure these logs are accessible when queried by a restricted admin. To view a complete list of audit logs for these activities, submit a search request using an unrestricted admin account.
| Service | Operation |
|---|---|
| Azure Information Protection | Discover |
| Dynamics 365 | CrmDefaultActivity |
| Endpoint data loss prevention | FileCreated FileCreatedOnNetworkShare FileCreatedOnRemovableMedia FileDeleted |
| Exchange | Set-Mailbox Set-MailboxPlan SupervisionBulkEmailExclusion |
| Microsoft Forms | ViewRuntimeForm |
For more information about administrative units, see Permissions in the Microsoft Purview compliance portal.