Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Set up a data connector to import physical badging data, such as an employee's raw physical access events or any physical access alarms generated by your organization's badging system. Examples of physical access points are an entry to a building or an entry to server room or data center. Microsoft Purview Insider Risk Management solution uses physical badging data to help protect your organization from malicious activity or data theft inside your organization.
Setting up a physical badging connector consists of the following tasks:
- Create an app in Microsoft Entra ID to access an API endpoint that accepts a JSON payload that contains physical badging data.
- Create the JSON payload with a schema defined by physical badging data connector.
- Create a physical badging data connector in the Microsoft Purview portal.
- Run a script to push the physical badging data to the API endpoint.
- Optionally, schedule the script to run automatically to import currently physical badging data.
Before you begin
Assign the Data Connector Admin role to the user who creates the physical badging connector in Step 3. This role is required to add connectors on the Data connectors page in the Microsoft Purview portal. Multiple role groups include this role by default. For a list of these role groups, see Roles in Microsoft Defender for Office 365 and Microsoft Purview. Alternatively, an admin in your organization can create a custom role group, assign the Data Connector Admin role, and then add the appropriate users as members. For instructions, see:- Permissions in the Microsoft Purview portal - Roles and role groups in Microsoft Defender for Office 365 and Microsoft Purview compliance
Note
The Data Connector Admin role isn't currently supported in US Government GCC High and DoD environments. Therefore, assign the Mailbox Import Export role in Exchange Online to the user who creates the HR connector in GCC High and DoD environments. By default, no role group in Exchange Online has this role assigned. You can add the Mailbox Import Export role to the Organization Management role group in Exchange Online. Or, you can create a new role group, assign the Mailbox Import Export role, and add the appropriate users as members. For more information, see the Create role groups or Modify role groups sections in the article "Manage role groups in Exchange Online".
Determine how to retrieve or export data from your organization's physical badging system (on a daily basis) and create a JSON file as described in Step 2. The script that you run in Step 4 pushes the data in the JSON file to the API endpoint.
Understand that the sample script you run in Step 4 pushes the physical badging data from a JSON file to the connector API so the insider risk management solution can use it. This sample script isn't supported under any Microsoft standard support program or service. The sample script is provided AS IS without warranty of any kind. Microsoft further disclaims all implied warranties including, without limitation, any implied warranties of merchantability or of fitness for a particular purpose. You assume all risk arising from the use or performance of the sample script and documentation. In no event shall Microsoft, its authors, or anyone else involved in the creation, production, or delivery of the scripts be liable for any damages whatsoever (including, without limitation, damages for loss of business profits, business interruption, loss of business information, or other pecuniary loss) arising out of the use of or inability to use the sample scripts or documentation, even if Microsoft has been advised of the possibility of such damages.
-
This data connector is available in GCC environments in the Microsoft 365 US Government cloud. Third-party applications and services might involve storing, transmitting, and processing your organization's customer data on third-party systems that are outside of the Microsoft 365 infrastructure and therefore aren't covered by the Microsoft Purview and data protection commitments. Microsoft makes no representation that use of this product to connect to third-party applications implies that those third-party applications are FedRAMP compliant.
Step 1: Create an app in Microsoft Entra ID
First, create and register a new app in Microsoft Entra ID. The app corresponds to the physical badging connector that you create in Step 3. When you create the app, Microsoft Entra ID can authenticate the push request for a JSON payload containing physical badging data. During the creation of this Microsoft Entra app, save the following information. You use these values in later steps.
- Microsoft Entra application ID (also called the app Id or client Id)
- Microsoft Entra application secret (also called the client secret)
- Tenant Id (also called the directory Id)
For step-by-step instructions for creating an app in Microsoft Entra ID, see Register an application with the Microsoft identity platform.
Step 2: Prepare a JSON file with physical badging data
In this step, you create a JSON file that contains information about employees’ physical access data. As explained in the before you begin section, you need to determine how to generate this JSON file from your organization's physical badging system.
Note
Don't add non-English characters to the JSON file. The connector supports only English characters. If the JSON contains non-English characters, data ingestion might fail.
The JSON file must conform to the schema definition required by the connector. The following table describes the required schema properties for the JSON file:
| Property | Description | Data type |
|---|---|---|
| UserId | An employee can have multiple digital identities across the systems. The input needs to have the Microsoft Entra ID already resolved by the source system. | UPN or email address |
| AssetId | The reference ID of the physical asset or physical access point. | Alphanumeric string |
| AssetName | The friendly name of the physical asset or physical access point. | Alphanumeric string |
| EventTime | The time stamp of access. | Date and time, in UTC format |
| AccessStatus | Value of Success or Failed |
String |
The following example shows a JSON file that conforms to the required schema:
[
{
"UserId":"sarad@contoso.com",
"AssetId":"Mid-Sec-7",
"AssetName":"Main Building 1st Floor Mid Section",
"EventTime":"2019-07-04T01:57:49",
"AccessStatus":"Failed"
},
{
"UserId":"pilarp@contoso.com",
"AssetId":"Mid-Sec-7",
"AssetName":"Main Building 1st Floor Mid Section",
"EventTime":"2019-07-04T02:57:49",
"AccessStatus":"Success"
}
]
You can also download the schema definition for the JSON file from the workflow when you create the physical badging connector in Step 3.
{
"title" : "Physical Badging Signals",
"description" : "Access signals from physical badging systems",
"DataType" : {
"description" : "Identify what is the data type for input signal",
"type" : "string",
},
"type" : "object",
"properties": {
"UserId" : {
"description" : "Unique identifier AAD Id resolved by the source system",
"type" : "string",
},
"AssetId": {
"description" : "Unique ID of the physical asset/access point",
"type" : "string",
},
"AssetName": {
"description" : "friendly name of the physical asset/access point",
"type" : "string",
},
"EventTime" : {
"description" : "timestamp of access",
"type" : "string",
},
"AccessStatus" : {
"description" : "what was the status of access attempt - Success/Failed",
"type" : "string",
},
}
"required" : ["UserId", "AssetId", "EventTime" "AccessStatus"]
}
Step 3: Create the physical badging connector
In this step, you create a physical badging connector in the Microsoft Purview portal. When you run the script in Step 4, it processes the JSON file you created in this step and pushes it to the API endpoint you configured in Step 1. Be sure to copy the JobId generated when you create the connector. You'll use the JobId when you run the script.
Sign in to the Microsoft Purview portal.
Select Settings > Data connectors.
Select My connectors, then select Add connector.
From the list, select Physical badging.
On the Authentication credentials page, enter the following information, then select Next:
Enter or paste the Microsoft Entra application ID for the Azure app that you created in Step 1.
Download the sample schema for your reference to create the JSON file.
Enter a unique name for the physical badging connector.
On the Review page, review your settings and select Finish to create the connector.
View the status page that confirms the connector was created. This page also contains the job ID. You can copy the job ID from this page or from the flyout page for the connector. You need this job ID when running the script.
The status page also contains a link to the script. Refer to this script to understand how to post the JSON file to the API endpoint.
Select Done.
The new connector appears in the list on the Connectors tab.
Select the physical badging connector that you just created to display the flyout page, which contains properties and other information about the connector.
Step 4: Run the script to upload your physical badging data
To set up a physical badging connector, run a script that pushes the physical badging data in the JSON file (created in Step 2) to the API endpoint (created in Step 1). A sample script is provided for your reference. You can choose to use it or create your own script to post the JSON file to the API endpoint.
After you run the script, the JSON file containing the physical badging data is pushed to your Microsoft 365 organization where the insider risk management solution can access it. Post physical badging data daily. You can automate the process to generate the JSON file every day from your physical badging system and then schedule the script to push the data.
Note
The API can process a JSON file with up to 50,000 records.
Go to this GitHub site to access the sample script.
Select the Raw button to display the script in text view.
Copy all the lines in the sample script and save them to a text file.
Modify the sample script for your organization, if necessary.
Save the text file as a Windows PowerShell script file by using a filename suffix of .ps1; for example, PhysicalBadging.ps1.
Open a Command Prompt on your local computer, and go to the directory where you saved the script.
Run the following command to push the physical badging data in the JSON file to the Microsoft cloud; for example:
.\PhysicalBadging.ps1 -tenantId "<Tenant Id>" -appId "<Microsoft Entra app Id>" -appSecret "<Microsoft Entra app Secret>" -jobId "Job Id" -jsonFilePath "<records file path>"The following table describes the parameters to use with this script and their required values. Use the information you obtained in the previous steps for these values.
Parameter Description tenantId This is the Id for your Microsoft 365 organization that you obtained in Step 1. You can also get the tenantId for your organization on the Overview blade in the Microsoft Entra admin center. This value identifies your organization. appId This is the Microsoft Entra application Id for the app that you created in Microsoft Entra ID in Step 1. Microsoft Entra ID uses this value for authentication when the script attempts to access your Microsoft 365 organization. appSecret This is the Microsoft Entra application secret for the app that you created in Microsoft Entra ID in Step 1. Microsoft Entra ID also uses this value for authentication. jobId This is the Job Id for the physical badging connector that you created in Step 3. The script uses this value to associate the physical badging data that it pushes to the Microsoft cloud with the physical badging connector. JsonFilePath This is the file path on the local computer (the one you're using to run the script) for the JSON file that you created in Step 2. This file must follow the sample schema described in Step 3. Here's an example of the syntax for the physical badging connector script using actual values for each parameter:
.\PhysicalBadging.ps1 -tenantId aaaabbbb-0000-cccc-1111-dddd2222eeee -appId 00001111-aaaa-2222-bbbb-3333cccc4444 -appSecret Aa1Bb~2Cc3.-Dd4Ee5Ff6Gg7Hh8Ii9_Jj0Kk1Ll2 -jobId 00001111-aaaa-2222-bbbb-3333cccc4444 -jsonFilePath 'C:\Users\contosoadmin\Desktop\Data\physical_badging_data.json'If the upload is successful, the script displays the Upload Successful message.
If you have multiple JSON files, run the script for each file.
Step 5: Monitor the physical badging connector
After you create the physical badging connector and push your physical badging data, you can view the connector and upload status in the Microsoft Purview portal. If you schedule the script to run automatically on a regular basis, you can also view the current status after the last time the script runs.
Sign in to the Microsoft Purview portal.
Select Settings > Data connectors.
Select My connectors, then select the physical badging connector that you created to display the flyout page. This page contains the properties and information about the connector.
Under Last import, select the Download log link to open (or save) the status log for the connector. This log contains information about each time the script runs and uploads the data from the JSON file to the Microsoft cloud.
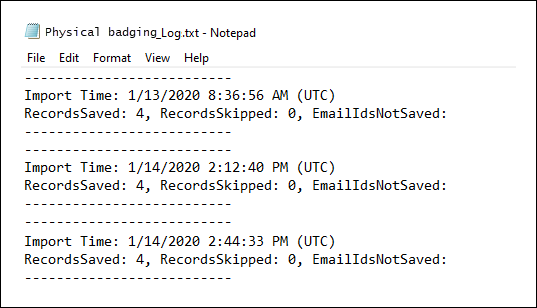
The RecordsSaved field shows the number of records in the JSON file that the script uploads. For example, if the JSON file contains four records, the value of the RecordsSaved fields is 4 when the script successfully uploads all the records in the JSON file. The RecordsSkipped field shows the number of records in the JSON file that the script skips. Before uploading records in the JSON file, the script validates the Email IDs. Any record with an invalid Email ID is skipped and the corresponding Email ID displays in the field EmailIdsNotSaved.
If you didn't run the script in Step 4, a link to download the script appears under Last import. You can download the script and then follow the steps in Step 4 to run it.
(Optional) Step 6: Schedule the script to run automatically
To make sure tools like the insider risk management solution always have the latest physical badging data from your organization, schedule the script to run automatically on a recurring basis, such as once a day. This schedule requires updating the physical badging data to JSON file on a similar (if not the same) schedule so that it contains the latest information about employees who leave your organization. The goal is to upload the most current physical badging data so that the physical badging connector can make it available to the insider risk management solution.
Use the Task Scheduler app in Windows to automatically run the script every day.
On your local computer, select the Windows Start button and then type Task Scheduler.
Select the Task Scheduler app to open it.
In the Actions section, select Create Task.
On the General tab, type a descriptive name for the scheduled task, such as physical badging connector Script. You can also add an optional description.
Under Security options, do the following things:
Decide whether to run the script only when you're logged on to the computer or run it when you're logged on or not.
Make sure that the Run with the highest privileges checkbox is selected.
Select the Triggers tab, select New, and then do the following things:
Under Settings, select the Daily option, and then choose a date and time to run the script for the first time. The script runs every day at the same specified time.
Under Advanced settings, make sure the Enabled checkbox is selected.
Select Ok.
Select the Actions tab, select New, and then do the following things:
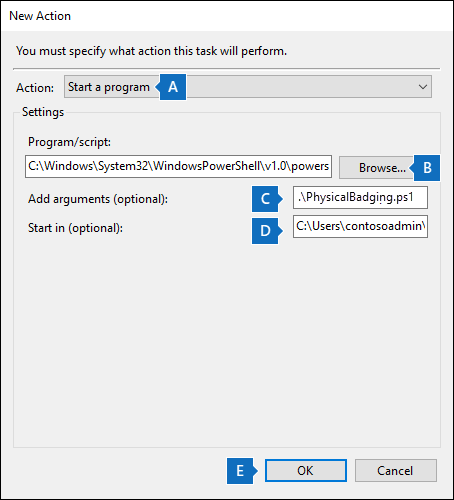
In the Action dropdown list, make sure that Start a program is selected.
In the Program/script box, select Browse, and go to the following location and select it so the path is displayed in the box:
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe.In the Add arguments (optional) box, paste the same script command that you ran in Step 4. For example,
.\PhysicalBadging.ps1 -tenantId "aaaabbbb-0000-cccc-1111-dddd2222eeee" -appId "00001111-aaaa-2222-bbbb-3333cccc4444" -appSecret "Aa1Bb~2Cc3.-Dd4Ee5Ff6Gg7Hh8Ii9_Jj0Kk1Ll2" -jobId "00001111-aaaa-2222-bbbb-3333cccc4444" -jsonFilePath "C:\Users\contosoadmin\Desktop\Data\physical_badging_data.json"In the Start in (optional) box, paste the folder location of the script that you ran in Step 4. For example,
C:\Users\contosoadmin\Desktop\Scripts.Select Ok to save the settings for the new action.
In the Create Task window, select Ok to save the scheduled task. You might be prompted to enter your user account credentials.
The new task is displayed in the Task Scheduler Library.
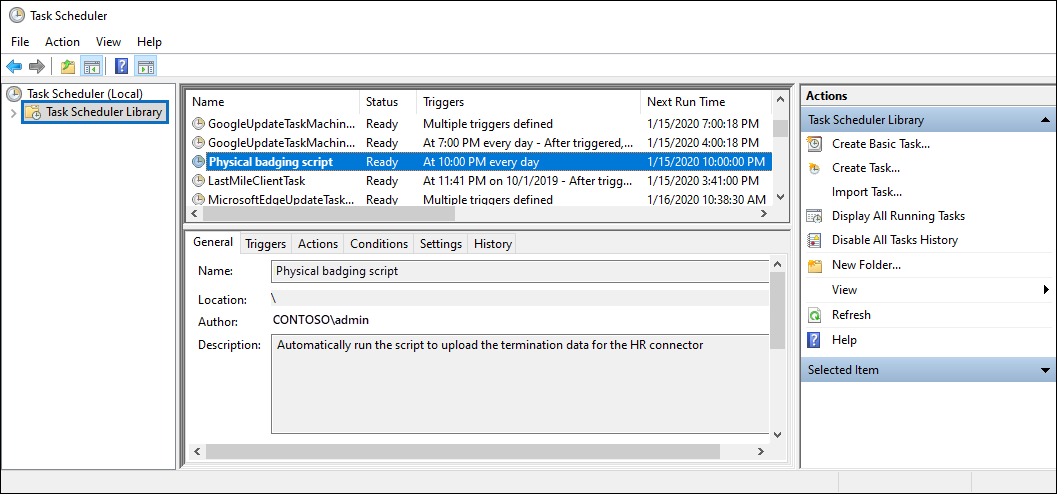
The last time the script ran and the next time it's scheduled to run is displayed. You can double-select the task to edit it.
You can also verify the last time the script ran on the flyout page of the corresponding physical badging connector in the Microsoft Purview portal.