Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Enable the setting to support co-authoring for Office desktop apps so that when documents are labeled and encrypted by sensitivity labels, multiple users can edit these documents at the same time.
Without this setting enabled for your tenant, users must check out an encrypted document stored in SharePoint or OneDrive when they use Office desktop apps. As a result, they can't collaborate in real time. Or, they must use Office for the web when sensitivity labels are enabled for Office files in SharePoint and OneDrive.
In addition, enabling this functionality results in the AutoSave functionality being supported for these labeled and encrypted files.
To read the release announcement, see the blog post Co-authoring on Microsoft Information Protection encrypted documents is now generally available.
Tip
If you're not an E5 customer, use the 90-day Microsoft Purview solutions trial to explore how additional Purview capabilities can help your organization manage data security and compliance needs. Start now at the Microsoft Purview trials hub. Learn details about signing up and trial terms.
Metadata changes for sensitivity labels
Important
After you enable the setting for co-authoring, labeling information for unencrypted files is no longer saved in custom properties.
Do not enable this setting if you use any apps, services, scripts, or tools that reads or writes labeling metadata to the old location.
Before you enable the setting to support co-authoring for Office desktop apps, it's important to understand that this action makes changes to the labeling metadata that is saved to and read from Office files.
The labeling metadata includes information that identifies your tenant and applied sensitivity label. The change that this setting makes is the metadata format and location for Word, Excel, and PowerPoint files. You don't need to take any action for encrypted files or emails because the metadata change for encrypted files is backward-compatible, and there are no changes for emails. However, you do need to be aware of the metadata changes for encrypted files that can be automatically upgraded but aren't backward-compatible.
This change affects both files that are newly labeled and files that are already labeled. When you use apps and services that support the co-authoring setting:
- For files that are newly labeled, only the new format and location is used for the labeling metadata.
- For files that are already labeled, the next time the file is opened and saved, if the file has metadata in the old format and location, that information is copied to the new format and location.
You can read more about this metadata change from the following resources:
Blog post: Upcoming Changes to Microsoft Information Protection Metadata Storage
Open Specifications: 2.6.3 LabelInfo versus Custom Document Properties
Because of these changes, don't enable this setting if you have any apps, services, scripts, or tools in your organization that reads or writes labeling metadata to the old location. If you do, some example consequences:
A document that is labeled appears to users to be unlabeled.
A document displays an out-of-date label to users.
Co-authoring and AutoSave won't work for a labeled and encrypted document if another user has it open in an Office desktop app that doesn't support the new labeling metadata. Be aware that this scenario can also occur for users outside your organization if external users and invited guests have the file open.
An Exchange Online mail flow rule that identifies labels as custom properties in Office attachments fails to encrypt the email and attachment, or incorrectly encrypts them.
Check the following section for a list of apps and services that support this setting and the changes to the labeling metadata.
Prerequisites
Make sure you understand the following prerequisites before you turn on this feature.
To turn this capability on or off, you need at least the DLP Compliance Management or Information Protection Admin role. Alternative roles include the Security Administrator and Compliance Administrator roles.
Sensitivity labels must be enabled for Office files in SharePoint and OneDrive for the tenant. If this feature isn't already enabled, it is automatically enabled when you select the setting to turn on co-authoring for files with sensitivity labels.
Microsoft 365 Apps for enterprise:
- Windows: Minimum version 2107 from Current Channel or Monthly Enterprise Channel, or minimum version 2202 from Semi-Annual Enterprise Channel
- macOS: Minimum version 16.51
- iOS: Minimum version 2.58
- Android: Minimum version 16.0.14931
All apps, services, and operational tools in your tenant must support the new labeling metadata. If you use any of the following, check the minimum versions required:
Microsoft Purview Information Protection client and scanner:
- Minimum version of 3.0 that you can install from the Microsoft Download Center, or minimum version of 2.12.62.0 for the older Azure Information Protection unified labeling client and scanner
OneDrive sync app for Windows or macOS:
- Minimum version of 19.002.0121.0008
Endpoint data loss prevention (Endpoint DLP):
- Windows 10 1809 with KB 4601383
- Windows 10 1903 and 1909 with KB 4601380
- Windows 10 2004 with KB 4601382
- Windows versions later than Windows 10 2004 are supported without KB updates
Apps and services that use the Microsoft Information Protection SDK:
- Minimum version of 1.7
Microsoft 365 services automatically support the new labeling metadata when you turn on this feature. For example:
- Auto-labeling policies
- DLP policies that use sensitivity labels as conditions
- Microsoft Defender for Cloud Apps configured to apply sensitivity labels
Limitations
Before you enable the tenant setting for co-authoring for files encrypted with sensitivity labels, make sure you understand the following limitations of this feature.
Because of the labeling metadata changes, all apps, services, and operational tools in your tenant must support the new labeling metadata for a consistent and reliable labeling experience.
Specific to Excel: Metadata for a sensitivity label that doesn't apply encryption can be deleted from a file if somebody edits and saves that file by using a version of Excel that doesn't support the metadata changes for sensitivity labels.
Co-authoring and AutoSave aren't supported for Office documents that use the label encryption configuration User access to content expires when it's set to a value other than Never, or Double Key Encryption is configured.
Labels with these configurations do still display in Office apps. However, when users select these labels and nobody else is editing the document, they're warned that co-authoring and AutoSave won't be available. If somebody else is editing the document, users see a message that the labels can't be applied.
Co-authoring and AutoSave are now supported in preview with specific versions and limitations for sensitivity labels that are configured for user-defined permissions. This encryption configuration refers to the setting Let users assign permissions when they apply the label and the checkbox In Word, PowerPoint, and Excel, prompt users to specify permissions is selected.
How to enable co-authoring for files with sensitivity labels
Caution
Enable this option only after you have read and understood the metadata changes, prerequisites, limitations, and any known issues documented on this page.
For this configuration, use an account that has at least the DLP Compliance Management or Information Protection Admin role.
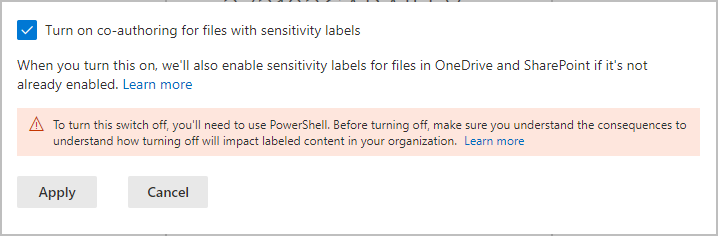
Sign in to the Microsoft Purview portal > Settings > Solution settings > Information Protection > Co-authoring for files with sensitivity labels.
On the Co-authoring for files with sensitivity labels page, read the summary description, prerequisites, and what to expect.
Then select Turn on co-authoring for files with sensitivity labels, and Apply:
Wait 24 hours for this setting to replicate across your environment before you use this new feature for co-authoring.
If you need to disable this feature
Important
If you do need to disable this feature, for example, you've discovered some apps don't support the metadata changes and you can't immediately update these apps, be aware that labeling information can be lost.
After you've enabled co-authoring for files with sensitivity labels for your tenant, you can't disable this setting in the Microsoft Purview portal, and this action is supported only by using PowerShell. This isn't a setting that you casually disable, and why it's so important that you check and understand the prerequisites, consequences, and limitations before you enable the setting.
If you do disable this setting for your tenant:
For apps and services that support the new labeling metadata, they now revert to the original metadata format and location when labels are read or saved.
The new metadata format and location for Office documents that were used while the setting was enabled won't be copied to the original format and location. As a result, this labeling information for unencrypted Word, Excel, and PowerPoint files will be lost.
Co-authoring and AutoSave no longer work in your tenant for labeled and encrypted documents.
Sensitivity labels remain enabled for Office files in OneDrive and SharePoint.
To disable co-authoring for your tenant
Use the Set-PolicyConfig cmdlet with the EnableLabelCoauth parameter.
In a PowerShell session, connect to Security & Compliance PowerShell.
Run the following command:
Set-PolicyConfig -EnableLabelCoauth:$false
The command completes without a prompt or confirmation.