Create, configure, and manage groups
A Microsoft Entra group helps organize users, which makes it easier to manage permissions. Using groups lets the resource owner (or Microsoft Entra directory owner), assign a set of access permissions to all the members of the group, instead of having to provide the rights one-by-one. Groups let you define a security boundary and then add and remove specific users to grant or deny access with a minimum amount of effort. Even better, Microsoft Entra ID supports the ability to define membership based on rules - such as what department a user works in, or the job title they have.
Microsoft Entra ID allows you to define two different types of groups.
- Security groups - the most common type of groups and are used to manage access to shared resources. Members of a security group can include users, devices, and service principals. For example, you can create a security group for a specific security policy. By doing it this way, you can give a set of permissions to all the members at once, instead of having to add permissions to each member individually. This option requires a Microsoft Entra administrator.
- Microsoft 365 groups - provide collaboration opportunities by giving members access to a shared mailbox, calendar, files, SharePoint site, and more. This option also lets you give people outside of your organization access to the group. This option is available to users and admins.
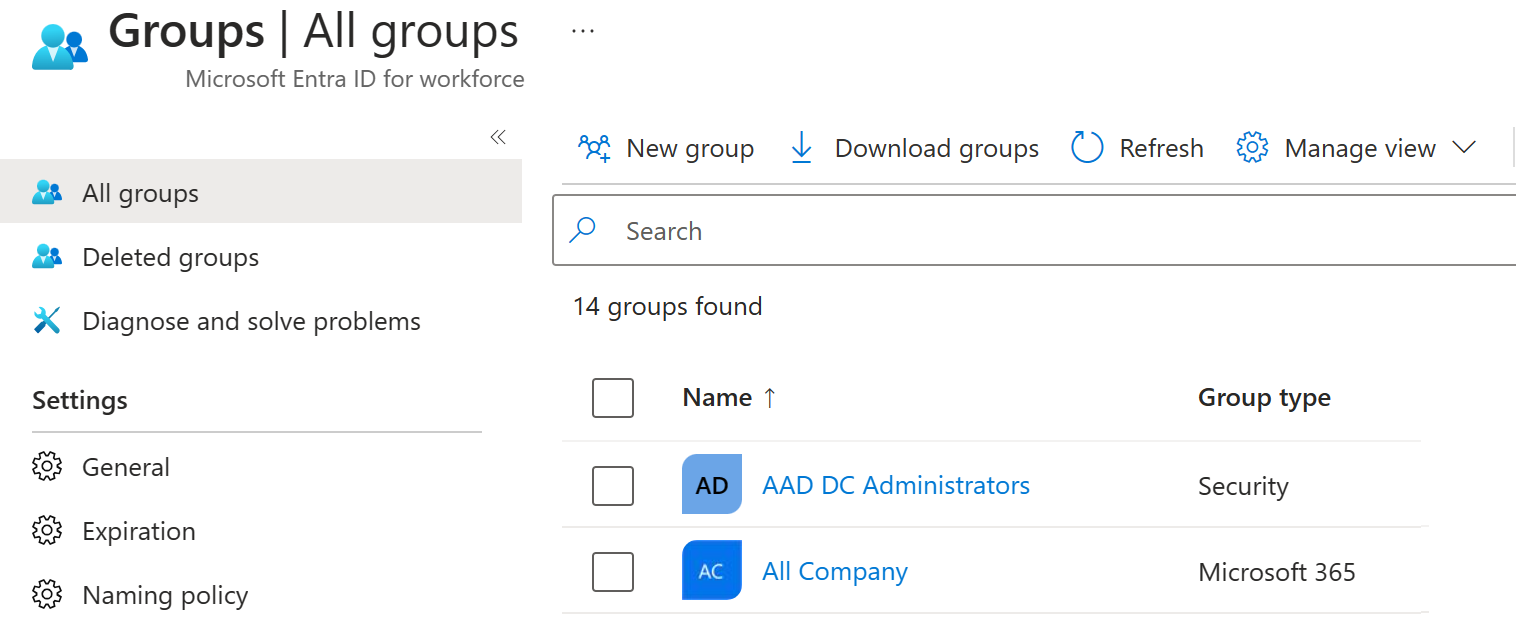
View available groups
You can view all groups through the Groups item under Identity in the Microsoft Entra admin center. A new Microsoft Entra ID deployment has no groups defined.
The second characteristic of a group that you need to be aware of is the Membership Type. This specifies how individual members are added to the group. The three types are:
- Assigned - members are added and maintained manually.
- Dynamic User - users are added and removed automatically based on rules that evaluate user attributes such as department, job title, or location.
- Dynamic Device - devices are added and removed automatically based on rules that evaluate device attributes. Applies to security groups only; Microsoft 365 groups support dynamic users but not dynamic devices.
Dynamic groups
With dynamic membership, Microsoft Entra ID automatically adds or removes users or devices from a group based on rules you define. When a member's attributes change—for example, a user moves to a different department—all dynamic membership rules in the tenant are reevaluated, and the user is added to or removed from groups accordingly.
Dynamic membership requires a Microsoft Entra ID P1 license (or Intune for Education for device-based rules).
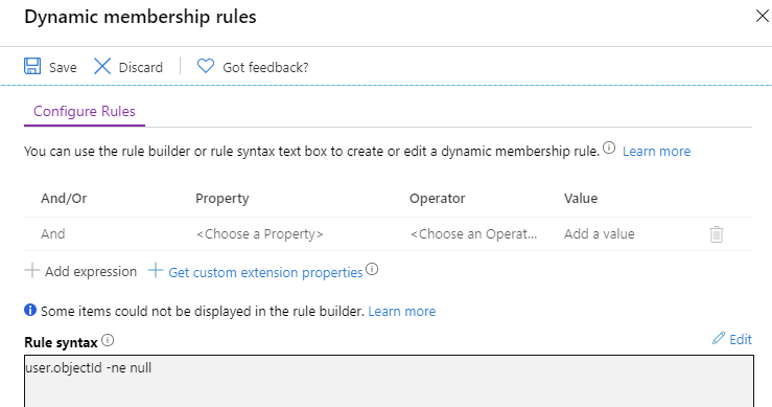
For example, you can create a rule that automatically adds all users whose Department attribute equals "Marketing" to a Marketing security group, keeping membership current without manual updates.