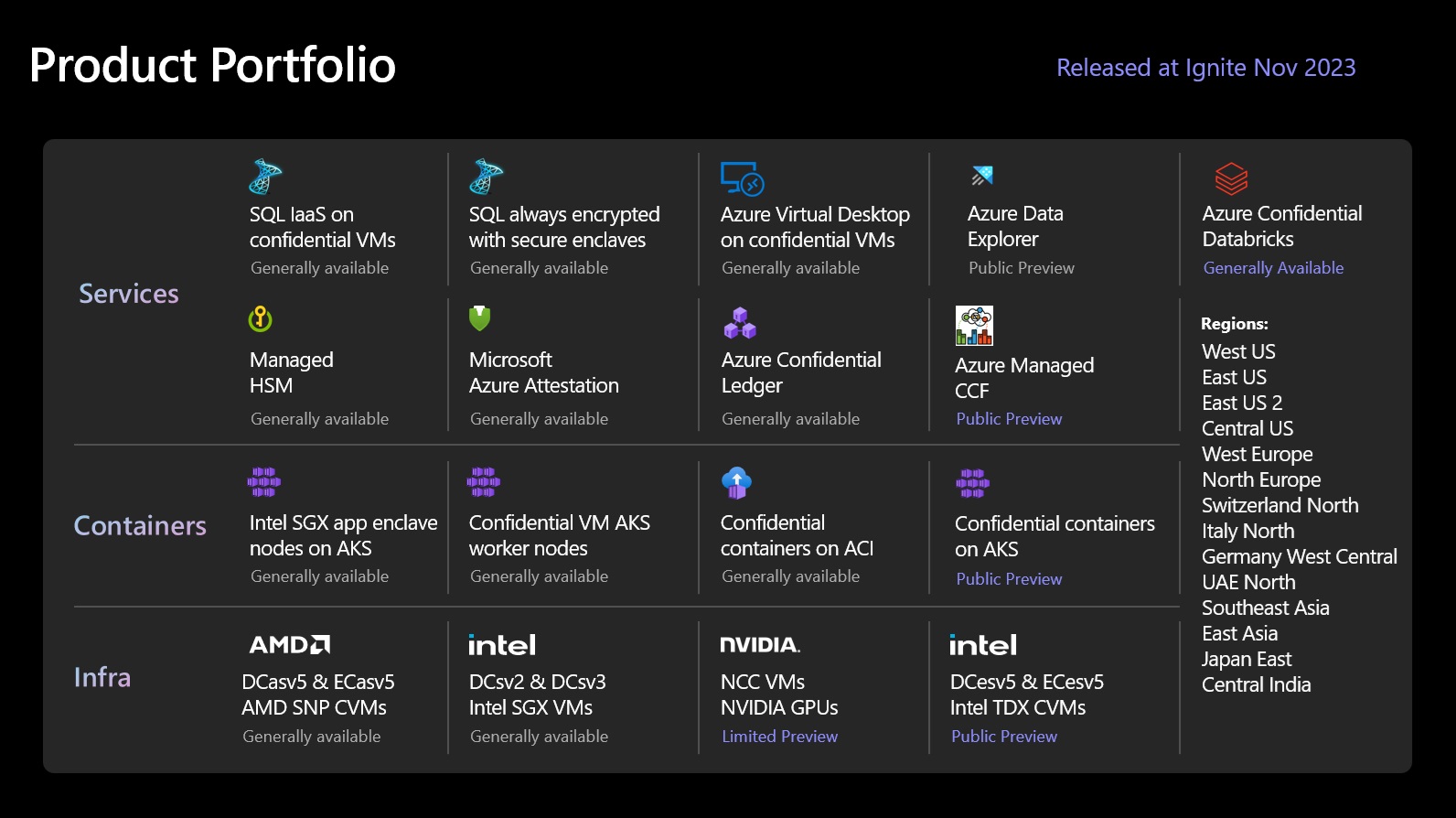
Azure offerings
Virtual machines and containers
Azure provides the broadest support for hardened technologies such as AMD SEV-SNP, Intel TDX and Intel SGX. All technologies meet our definition of confidential computing, helping organizations prevent unauthorized access or modification of code and data while in use.
Confidential VMs using AMD SEV-SNP. DCasv5 and ECasv5 enable lift-and-shift of existing workloads and helps protect data from the cloud operator with VM-level confidentiality.
Confidential VMs using Intel TDX. DCesv5 and ECesv5 enable lift-and-shift of existing workloads and helps protect data from the cloud operator with VM-level confidentiality.
VMs with Application Enclaves using Intel SGX. DCsv2, DCsv3, and DCdsv3 enable organizations to create hardware enclaves. These secure enclaves help protect from cloud operators, and your own VM admins.
App-enclave aware containers running on Azure Kubernetes Service (AKS). Confidential computing nodes on AKS use Intel SGX to create isolated enclave environments in the nodes between each container application.
Confidential services
Azure offers various PaaS, SaaS and VM capabilities supporting or built upon confidential computing, this includes:
Azure Key Vault Managed HSM, a fully managed, highly available, single-tenant, standards-compliant cloud service that enables you to safeguard cryptographic keys for your cloud applications, using FIPS 140-2 Level 3 validated Hardware Security Modules (HSM).
Always Encrypted with secure enclaves in Azure SQL. The confidentiality of sensitive data is protected from malware and high-privileged unauthorized users by running SQL queries directly inside a TEE.
Azure Databricks helps you bring more security and increased confidentiality to your Databricks Lakehouse using confidential VMs.
Azure Virtual Desktop ensures a user’s virtual desktop is encrypted in memory, protected in use, and backed by hardware root of trust.
Microsoft Azure Attestation, a remote attestation service for validating the trustworthiness of multiple Trusted Execution Environments (TEEs) and verifying integrity of the binaries running inside the TEEs.
Trusted Hardware Identity Management, a service that handles cache management of certificates for all TEEs residing in Azure and provides trusted computing base (TCB) information to enforce a minimum baseline for attestation solutions.
Azure Confidential Ledger. ACL is a tamper-proof register for storing sensitive data for record keeping and auditing or for data transparency in multi-party scenarios. It offers Write-Once-Read-Many guarantees, which make data non-erasable and non-modifiable. The service is built on Microsoft Research's Confidential Consortium Framework.
Supplementary offerings
Azure IoT Edge supports confidential applications that run within secure enclaves on an Internet of Things (IoT) device. IoT devices are often exposed to tampering and forgery because they're physically accessible by bad actors. Confidential IoT Edge devices add trust and integrity at the edge by protecting the access to data captured by and stored inside the device itself before streaming it to the cloud.
Confidential Inference ONNX Runtime, a Machine Learning (ML) inference server that restricts the ML hosting party from accessing both the inferencing request and its corresponding response.
Trusted Launch is available across all Generation 2 VMs bringing hardened security features – secure boot, virtual trusted platform module, and boot integrity monitoring – that protect against boot kits, rootkits, and kernel-level malware.
What's new in Azure confidential computing
Next steps
Palaute
Tulossa pian: Vuoden 2024 aikana poistamme asteittain GitHub Issuesin käytöstä sisällön palautemekanismina ja korvaamme sen uudella palautejärjestelmällä. Lisätietoja on täällä: https://aka.ms/ContentUserFeedback.
Lähetä ja näytä palaute kohteelle