Get started with enterprise IoT monitoring in Microsoft Defender XDR
This article describes how Microsoft Defender for Endpoint customers can monitor enterprise IoT devices in their environment, using added security value in Microsoft Defender XDR.
While IoT device inventory is already available for Defender for Endpoint P2 customers, turning on enterprise IoT security adds alerts, recommendations, and vulnerability data, purpose-built for IoT devices in your enterprise network.
IoT devices include printers, cameras, VOIP phones, smart TVs, and more. Turning on enterprise IoT security means, for example, that you can use a recommendation in Microsoft Defender XDR to open a single IT ticket for patching vulnerable applications across both servers and printers.
Prerequisites
Before you start the procedures in this article, read through Secure IoT devices in the enterprise to understand more about the integration between Defender for Endpoint and Defender for IoT.
Make sure that you have:
IoT devices in your network, visible in the Microsoft Defender XDR Device inventory
Access to the Microsoft Defender Portal as a Security administrator
Microsoft Defender for Endpoint agents deployed in your environment. For more information, see onboard Microsoft Defender for Endpoint.
One of the following licenses:
A Microsoft 365 E5 (ME5) or E5 Security license
Microsoft Defender for Endpoint P2, with an extra, standalone Microsoft Defender for IoT - EIoT Device License - add-on license, available for purchase or trial from the Microsoft 365 admin center.
Tip
If you have a standalone license, you don't need to toggle on Enterprise IoT Security and can skip directly to View added security value in Microsoft Defender XDR.
For more information, see Enterprise IoT security in Microsoft Defender XDR.
Turn on enterprise IoT monitoring
This procedure describes how to turn on enterprise IoT monitoring in Microsoft Defender XDR, and is relevant only for ME5/E5 Security customers.
Skip this procedure if you have one of the following types of licensing plans:
- Customers with legacy Enterprise IoT pricing plan and an ME5/E5 Security license.
- Customers with standalone, per-device licenses added on to Microsoft Defender for Endpoint P2. In such cases, the Enterprise IoT security setting is turned on as read-only.
To turn on enterprise IoT monitoring:
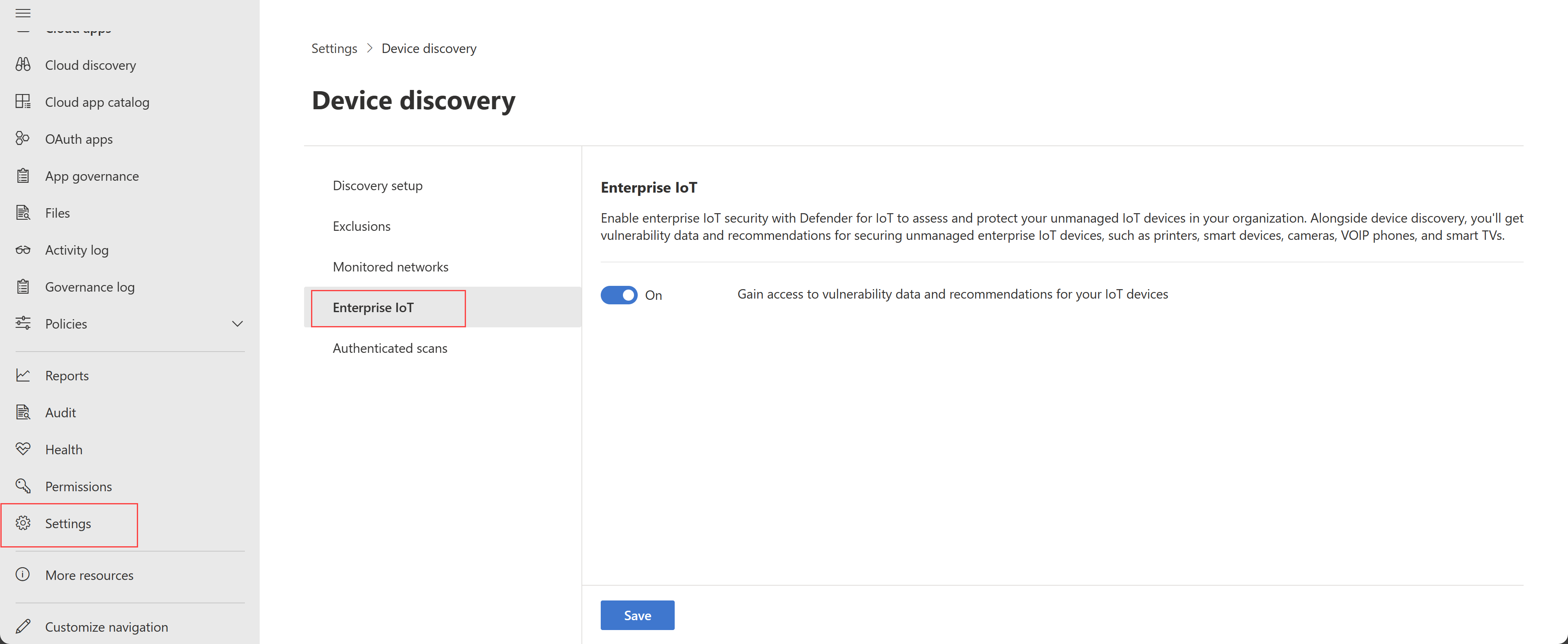
- In Microsoft Defender XDR, select Settings > Device Discovery > Enterprise IoT.
Note
Ensure you have turned on Device Discovery in Settings > Endpoints > Advanced Features.
Toggle the Enterprise IoT security option to On. For example:
View added security value in Microsoft Defender XDR
This procedure describes how to view related alerts, recommendations, and vulnerabilities for a specific device in Microsoft Defender XDR, when the Enterprise IoT security option is turned on.
To view added security value:
In Microsoft Defender XDR, select Assets > Devices to open the Device inventory page.
Select the IoT devices tab and select a specific device IP to drill down for more details. For example:
On the device details page, explore the following tabs to view data added by the enterprise IoT security for your device:
On the Alerts tab, check for any alerts triggered by the device. Simulate alerts in Microsoft 365 Defender for Enterprise IoT using the Raspberry Pi scenario available in the Microsoft 365 Defender Evaluation & Tutorials page.
You can also set up advanced hunting queries to create custom alert rules. For more information, see sample advanced hunting queries for Enterprise IoT monitoring.
On the Security recommendations tab, check for any recommendations available for the device to reduce risk and maintain a smaller attack surface.
On the Discovered vulnerabilities tab, check for any known CVEs associated with the device. Known CVEs can help decide whether to patch, remove, or contain the device and mitigate risk to your network. Alternatively, use advanced hunting queries to collect vulnerabilities across all your devices.
To hunt for threats:
On the Device inventory page, select Go hunt to query devices using tables like the DeviceInfo table. On the Advanced hunting page, query data using other schemas.
Sample advanced hunting queries for Enterprise IoT
This section lists sample advanced hunting queries that you can use in Microsoft 365 Defender to help you monitor and secure your IoT devices with Enterprise for IoT security.
Find devices by specific type or subtype
Use the following query to identify devices that exist in your corporate network by type of device, such as routers:
DeviceInfo
| summarize arg_max(Timestamp, *) by DeviceId
| where DeviceType == "NetworkDevice" and DeviceSubtype == "Router"
Find and export vulnerabilities for your IoT devices
Use the following query to list all vulnerabilities on your IoT devices:
DeviceInfo
| where DeviceCategory =~ "iot"
| join kind=inner DeviceTvmSoftwareVulnerabilities on DeviceId
For more information, see Advanced hunting and Understand the advanced hunting schema.
