Muistiinpano
Tämän sivun käyttö edellyttää valtuutusta. Voit yrittää kirjautua sisään tai vaihtaa hakemistoa.
Tämän sivun käyttö edellyttää valtuutusta. Voit yrittää vaihtaa hakemistoa.
Huomautus
DocuSign App Connector edellyttää aktiivista, maksullista DocuSign- ja DocuSign Monitor -tilausta tapahtumien käyttämiseen ja noutamiseen.
DocuSign auttaa organisaatioita hallitsemaan sähköisiä sopimuksia, joten DocuSign-ympäristösi sisältää luottamuksellisia tietoja organisaatiollesi. Pahantahtoisen toimijan docuSign-väärinkäyttö tai inhimillinen virhe voi altistaa kriittisimmät resurssisi mahdollisille hyökkäyksille.
DocuSign-ympäristön yhdistäminen Defender for Cloud Apps tarjoaa entistä parempia merkityksellisiä tietoja DocuSign-järjestelmänvalvojan toiminnoista ja hallittujen käyttäjien kirjautumisista. Lisäksi se tarjoaa poikkeavien toimintojen uhkien tunnistamisen.
Tämän sovellusliittimen avulla voit käyttää SaaS Security Posture Management (SSPM) -ominaisuuksia Microsoftin suojatussa pistemäärässä heijastelevan suojauksen hallinnan kautta. Lisätietoja.
Tärkeimmät uhat
- Vaarantuneet tilit ja insider-uhat
- Tietojen vuoto
- Riittämättömät suojaustiedot
- Hallitsematon tuo oma laitteesi (BYOD)
Miten Defender for Cloud Apps auttaa suojaamaan ympäristöäsi
Tunnista pilvipalveluuhkia, vaarantuneita tilejä ja haitallisia sisäpiiriläisiä
Käytä toimintojen kirjausketjua rikosteknisessä tutkimuksessa
SaaS-suojaustilan hallinta
Jos haluat nähdä DocuSign-suojausasentesuositukset Microsoftin suojatuissa pisteissä, luo ohjelmointirajapintaliitin Liittimet-välilehden kautta. Jos liitin on jo olemassa etkä vielä näe GitHub-suosituksia, päivitä yhteys katkaisemalla ohjelmointirajapintaliittimen yhteys ja yhdistämällä se sitten uudelleen.
Valitse Suojauspisteet-kohdassa Suositellut toiminnot ja suodata tuotteen = docuSign mukaan. DocuSign tukee suojaussuosituksia istunnon aikakatkaisu- ja salasanavaatimuksiin.
Lisätietoja on seuraavissa artikkeleissa:
- DocuSign-Microsoft Defender for Cloud Apps yhdistäminen
- SaaS-sovellusten suojaustilan hallinta
- Microsoftin suojauspisteet
DocuSign-ohjausobjekti käytäntöjen avulla
| Tyyppi | Name (Nimi) |
|---|---|
| Sisäinen poikkeamien tunnistuskäytäntö |
Anonyymien IP-osoitteiden toiminta Aktiviteetti epävakaista maista tai alueilta Epäilyttävän IP-osoitteen toiminta Mahdoton matka Lopetetun käyttäjän suorittama toiminto (edellyttää Microsoft Entra id as IdP) Useita epäonnistuneita kirjautumisyrityksiä |
| Toimintakäytäntö | Mukautetun käytännön luominen DocuSign-valvontalokin avulla |
Lisätietoja käytäntöjen luomisesta on artikkelissa Käytännön luominen.
Automatisoi hallinnon ohjausobjekteja
Mahdollisten uhkien seurannan lisäksi voit käyttää ja automatisoida seuraavia DocuSign-hallintatoimia havaittujen uhkien korjaamiseksi:
| Tyyppi | Toiminta |
|---|---|
| Käyttäjien hallinta | Ilmoita käyttäjälle ilmoituksesta (Microsoft Entra tunnuksen kautta) Edellytä käyttäjää kirjautumaan uudelleen sisään (Microsoft Entra tunnuksen kautta) Keskeytä käyttäjä (Microsoft Entra tunnuksen kautta) |
Lisätietoja uhkien korjaamisesta sovelluksista on kohdassa Yhdistettyjen sovellusten hallinnoiminen.
DocuSignin suojaaminen reaaliaikaisesti
Tutustu parhaisiin käytäntöihin, jotka koskevat ulkoisten käyttäjien suojaamista ja yhteistyötä sekä luottamuksellisten tietojen lataamisen estämistä ja suojaamista hallitsemattomiin tai riskialttiisiin laitteisiin.
DocuSign-Microsoft Defender for Cloud Apps yhdistäminen
Tässä osiossa on ohjeet Microsoft Defender for Cloud Apps yhdistämiseen aiemmin luotuun DocuSign-ympäristöön App Connector -ohjelmointirajapintoja käyttämällä. Tämän yhteyden avulla voit hallita organisaatiosi DocuSign-käyttöä.
Tämän sovellusliittimen avulla voit käyttää SaaS Security Posture Management (SSPM) -ominaisuuksia Microsoftin suojatussa pistemäärässä heijastelevan suojauksen hallinnan kautta. Lisätietoja.
Ennakkovaatimukset
DocuSign Enterprise Pro -tilisopimus, jossa monitorin ohjelmointirajapinta on käytössä.
- Lisätietoja DocuSign Monitor -ohjelmointirajapinnasta on kohdassa Valvontatietojen noutaminen | DocuSign ja Enable DocuSign Monitor organisaatiollesi | DocuSign.
Organisaatiossasi käytetyt DNS-toimialueet on lunastettava ja vahvistettava DocuSign-organisaatiossasi. Lisätietoja toimialueiden hakemisesta ja vahvistamisesta on kohdassa Toimialueet | DocuSign
DocuSign-kirjautumiseen käytettävä DocuSign-käyttäjä on yhdistettävä käyttäjärooliin "Docusign Administrator" ja hänen on oltava vain yhden organisaation järjestelmänvalvoja. Lisätietoja on kohdassa Valvontatietojen noutaminen | DocuSign ja organisaation järjestelmänvalvojat - DocuSign Hallinta organisaation hallintaan | DocuSign-tukikeskus.
DocuSignin ohjelmointirajapintarajoituksen vuoksi SaaS Security Posture Management (SSPM) -tuen tueksi siihen on tarpeen yhdistää uudelleen lisäkäyttöoikeudet: account_read account_write ja user_read organization_read.
DocuSign-tili on yhdistettävä organisaatioon. Lisätietoja on seuraavissa artikkeleissa:
Luo uusi organisaatio: organisaatiot - DocuSign Hallinta organisaation hallintaan | DocuSign-tukikeskus
Tilin linkittäminen olemassa olevaan organisaatioon: Tilien hallinta - DocuSign Hallinta organisaation hallintaa varten | DocuSign-tukikeskus
DocuSign Organisaation Hallinta opas: DocuSign Hallinta for Organization Management (PDF) | DocuSign-tukikeskus.
Määritä docuSign
Kirjaudu sisään DocuSign-tiliin, joka on yhdistetty organisaatioosi (sinun pitäisi olla tili, Hallinta kyseiselle tilille).
Valitse Asetukset ja sitten Sovellukset ja avaimet.
Kopioi käyttäjätunnus ja tilikannan URI. Tarvitset niitä myöhemmin.
Määritä Defender for Cloud Apps
Valitse Microsoft Defender portaalissa Asetukset. Valitse sitten Pilvisovellukset. Valitse Yhdistetyt sovellukset -kohdassa Sovellusliittimet.
Valitse Sovellusliittimet-sivulla+Yhdistä sovellus ja valitse sitten DocuSign.
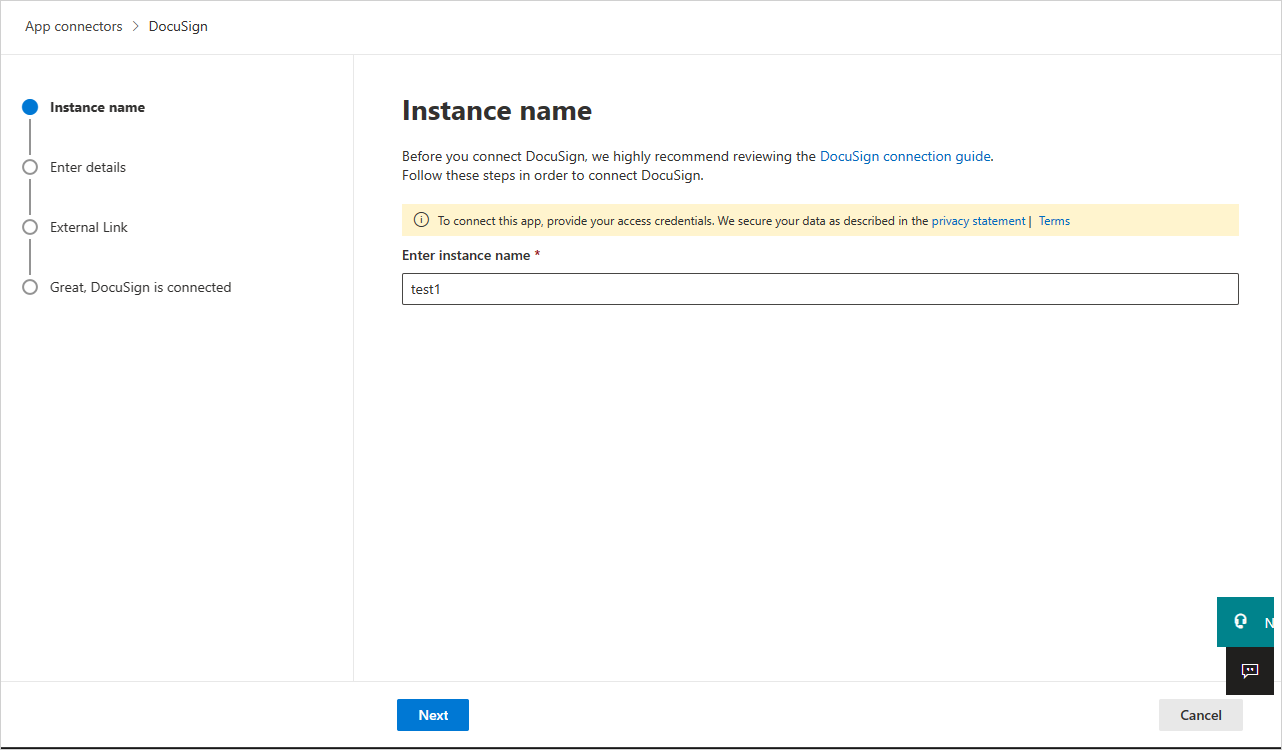
Anna avautuvassa ikkunassa liittimelle kuvaava nimi ja valitse sitten Seuraava.
Kirjoita seuraavaan näyttöön seuraavat tiedot:
- Käyttäjätunnus: aiemmin kopioimasi käyttäjätunnus.
- Päätepiste: aiemmin kopioimasi tilin perus-URI.
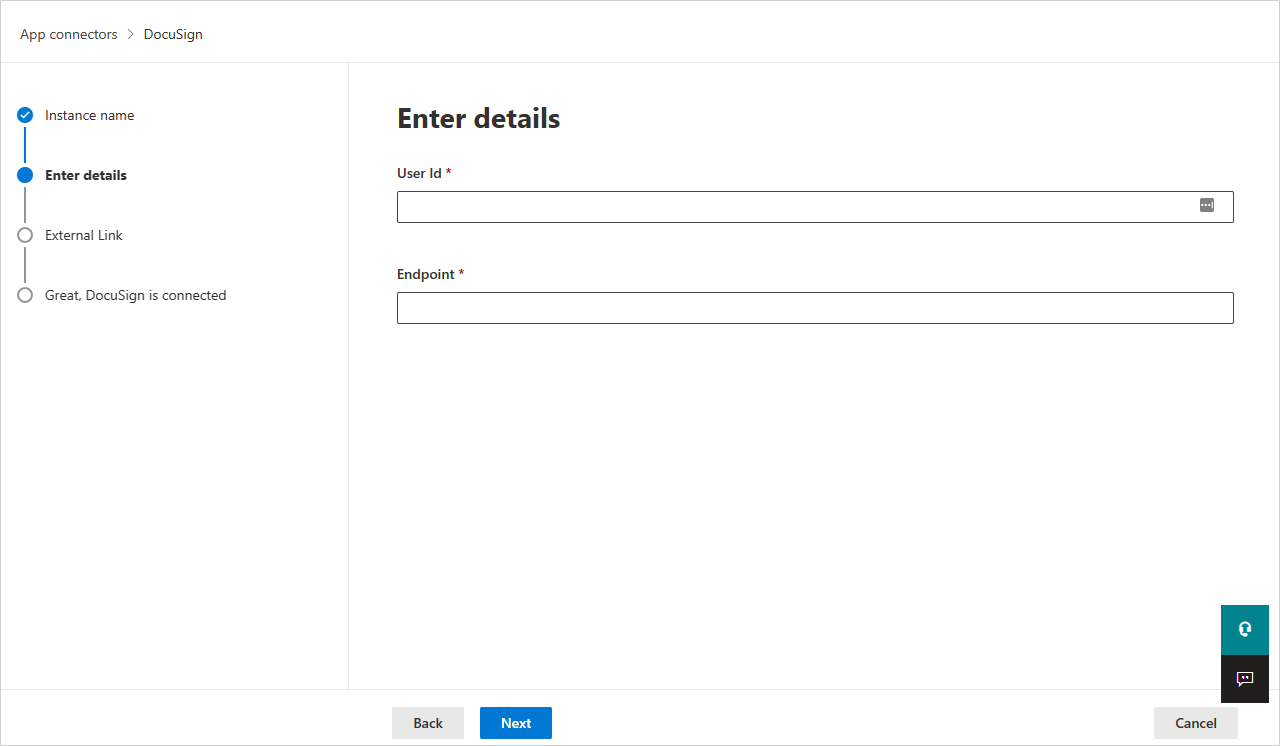
Valitse Seuraava.
Valitse seuraavassa näytössä Yhdistä docuSign.
Valitse Microsoft Defender portaalissa Asetukset. Valitse sitten Pilvisovellukset. Valitse Yhdistetyt sovellukset -kohdassa Sovellusliittimet. Varmista, että yhdistetyn App Connectorin tila on yhdistetty.
Huomautus
SaaS Security Posture Management (SSPM) -tiedot näytetään Microsoft Defender portaalissa Suojauspisteet-sivulla. Lisätietoja on kohdassa SaaS-sovellusten suojaustilan hallinta.
Rajoitukset
- Vain aktiiviset DocuSign-käyttäjät näytetään Defender for Cloud Apps.
- Jos käyttäjä ei ole aktiivinen kaikilla DocuSign-tileillä, jotka on yhdistetty yhdistettyyn DocuSign-organisaatioon, käyttäjä näytetään poistettuna Defender for Cloud Apps.
- SaaS Security Posture Management (SSPM) -tuen osalta annetuilla tunnistetiedoilla on oltava nämä oikeudet – account_read account_write ja user_read organization_read.
- Defender for Cloud Apps ei näytä, onko käyttäjä järjestelmänvalvoja vai ei.
- Defender for Cloud Apps näkyvät DocuSign-toiminnot ovat toimintoja tilitasolla (jokaisella tilillä, joka on yhdistetty Yhdistetty DocuSign-organisaatioon) ja organisaatiotasolla.
Seuraavat vaiheet
Jos kohtaat ongelmia, olemme täällä auttamassa. Jos haluat apua tai tukea tuoteongelmaasi varten, avaa tukipyyntö.