Policies for allowing guest access and B2B external user access
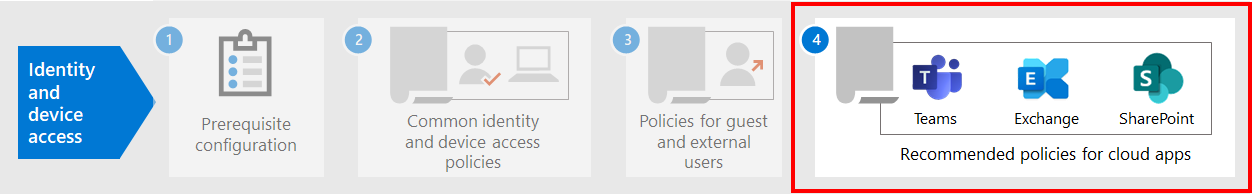
This article discusses adjusting the recommended Zero Trust identity and device access policies to allow access for guests and external users that have a Microsoft Entra Business-to-Business (B2B) account. This guidance builds on the common identity and device access policies.
These recommendations are designed to apply to the starting point tier of protection. But you can also adjust the recommendations based on your specific needs for enterprise and specialized security protection.
Providing a path for B2B accounts to authenticate with your Microsoft Entra tenant doesn't give these accounts access to your entire environment. B2B users and their accounts have access to services and resources, like files, shared with them by Conditional Access policy.
Updating the common policies to allow and protect guests and external user access
This diagram shows which policies to add or update among the common identity and device access policies, for B2B guest and external user access.
The following table lists the policies you either need to create and update. The common policies link to the associated configuration instructions in the Common identity and device access policies article.
| Protection level | Policies | More information |
|---|---|---|
| Starting point | Require MFA always for guests and external users | Create this new policy and configure:
|
| Require MFA when sign-in risk is medium or high | Modify this policy to exclude guests and external users. |
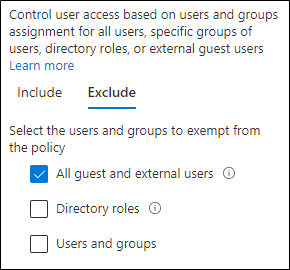
To include or exclude guests and external users in Conditional Access policies, for Assignments > Users and groups > Include or Exclude, check All guest and external users.
More information
Guests and external user access with Microsoft Teams
Microsoft Teams defines the following users:
Guest access uses a Microsoft Entra B2B account that can be added as a member of a team and have access to the communications and resources of the team.
External access is for an external user that doesn't have a B2B account. External user access includes invitations, calls, chats, and meetings, but doesn't include team membership and access to the resources of the team.
For more information, see the comparison between guests and external user access for teams.
For more information on securing identity and device access policies for Teams, see Policy recommendations for securing Teams chats, groups, and files.
Require MFA always for guest and external users
This policy prompts guests to register for MFA in your tenant, regardless of whether they're registered for MFA in their home tenant. Guests and external users accessing resources in your tenant are required to use MFA for every request.
Excluding guests and external users from risk-based MFA
While organizations can enforce risk-based policies for B2B users using Microsoft Entra ID Protection, there are limitations in the implementation of Microsoft Entra ID Protection for B2B collaboration users in a resource directory because their identity exists in their home directory. Due to these limitations, Microsoft recommends you exclude guests from risk-based MFA policies and require these users to always use MFA.
For more information, see Limitations of ID Protection for B2B collaboration users.
Excluding guests and external users from device management
Only one organization can manage a device. If you don't exclude guests and external users from policies that require device compliance, these policies block these users.
Next step
Configure Conditional Access policies for:
Palaute
Tulossa pian: Vuoden 2024 aikana poistamme asteittain GitHub Issuesin käytöstä sisällön palautemekanismina ja korvaamme sen uudella palautejärjestelmällä. Lisätietoja on täällä: https://aka.ms/ContentUserFeedback.
Lähetä ja näytä palaute kohteelle