Megjegyzés
Az oldalhoz való hozzáféréshez engedély szükséges. Megpróbálhat bejelentkezni vagy módosítani a címtárat.
Az oldalhoz való hozzáféréshez engedély szükséges. Megpróbálhatja módosítani a címtárat.
A következőkre vonatkozik:SQL Server Linux rendszeren
Ez az oktatóanyag bemutatja, hogyan konfigurálhatja az SQL Servert Linux-tárolókon az Active Directory-hitelesítés, más néven integrált hitelesítés támogatására. A SQL Server Linuxon történő Active Directory-hitelesítés áttekintéséhez tekintse meg témakört.
Jegyzet
A hálózati konfigurációval kapcsolatos aktuális útmutatásért tekintse meg az operációs rendszer (OS) dokumentációját.
Ez az oktatóanyag a következő feladatokból áll:
- Az adutil telepítése
- Csatlakozás Linux-gazdagéphez az Active Directory-tartományhoz
- Active Directory-felhasználó létrehozása az SQL Serverhez, és a szolgáltatásnév (SPN) beállítása az adutil eszközzel
- Az SQL Server szolgáltatáshoz tartozó kulcsfájl létrehozása
- Az SQL Server-tároló által használandó
mssql.conféskrb5.conffájlok létrehozása - A konfigurációs fájlok csatlakoztatása és az SQL Server-tároló üzembe helyezése
- Active Directory-alapú SQL Server-bejelentkezések létrehozása Transact-SQL
- Csatlakozás AZ SQL Serverhez Active Directory-hitelesítéssel
Előfeltételek
Az Active Directory-hitelesítés konfigurálása előtt a következőkre van szükség:
- Active Directory tartományvezérlő (Windows) használata a hálózaton.
- Telepítse az adutil programot egy Linux rendszerű gépre, amely tartományba van csatlakoztatva. A részletekért kövesse az Install adutil szakaszt.
Tároló üzembe helyezése és előkészítése
A tároló beállításához előzetesen tudnia kell, hogy a tároló milyen portot fog használni a gazda gépen. Előfordulhat, hogy az alapértelmezett port (1433) másként van leképezve a tároló gazdagépén. Ebben az oktatóanyagban a gazdagép 5433 portját a tároló 1433 portjára fogjuk leképezni. További információért nézze meg a gyorsindítónkat: Quickstart: SQL Server Linux-konténerképek futtatása Dockerrel.
A szolgáltatásnévnevek (SPN) regisztrálásakor használhatja a gép állomásnevét vagy a tároló nevét. Azonban, a tárolóhoz való külső csatlakozáskor úgy kell konfigurálnia, hogy az megfeleljen az Ön elképzeléseinek.
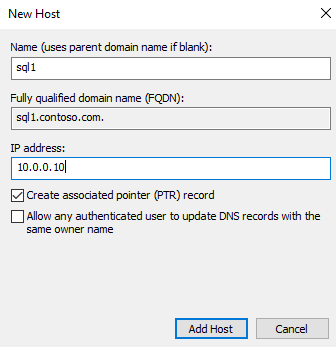
Győződjön meg arról, hogy van egy továbbítási állomás (A) bejegyzés az Active Directoryban a Linux-gazdagép IP-címéhez, és megfelelteti az SQL Server-tároló nevének. Ebben az oktatóanyagban a sql1 gazdagép IP-címe 10.0.0.10, az SQL Server tároló neve pedig sql1. Adja hozzá a továbbítási gazdagép bejegyzését az Active Directoryban a módon, ahogyan az a képernyőképen látható. A bejegyzés biztosítja, hogy amikor a felhasználók sql1.contoso.comcsatlakoznak, a megfelelő gazdagéphez érnek.
Ebben az oktatóanyagban egy azure-beli környezetet használunk három virtuális géppel. Windows tartományvezérlőként (DC) működő virtuális gép, amelynek tartományneve contoso.com. A tartományvezérlő neve adVM.contoso.com. A második gép egy winboxnevű Windows-gép, amely a Windows 10 desktopot futtatja, amelyet ügyféldobozként használnak, és telepítve van az SQL Server Management Studio (SSMS). A harmadik gép egy sql1nevű Ubuntu 18.04 LTS-gép, amely az SQL Server-tárolókat üzemelteti. Minden gép csatlakozik a contoso.com tartományhoz. További információ: Csatlakozás SQL Serverhez Linux-gazdagépen Active Directory-tartományhoz.
Jegyzet
A gazdagéptároló-gép tartományhoz való csatlakoztatása nem kötelező, ahogy a cikk későbbi részében is látható.
Az adutil telepítése
Az adutiltelepítéséhez kövesse Bevezetés az adutil – Active Directory segédprogramcímű témakörben leírt lépéseket a tartományhoz csatlakoztatott gazdagépen.
Active Directory-felhasználó, SPN-k és SQL Server-szolgáltatáskulcsok létrehozása
Ha nem szeretné, hogy a tároló gazdagép a tartomány része legyen, és nem követte a gép tartományhoz való csatlakoztatásához szükséges lépéseket, kövesse az alábbi lépéseket egy másik Linux-gépen, amely már része az Active Directory-tartománynak:
Hozzon létre egy Active Directory-felhasználót az SQL Serverhez, és állítsa be az SPN-t az adutilhasználatával.
Hozza létre és konfigurálja az SQL Server service keytab fájlt.
Másolja a létrehozott mssql.keytab fájlt az SQL Server tárolóját futtató gazdagépre, és állítsa be a tárolót, hogy a másolt mssql.keytab-et használja. Opcionálisan csatlakozhat a Linux-gazdagéphez is, amely az SQL Server-tárolót az Active Directory-tartományba futtatja, és ugyanazon a gépen követi az alábbi lépéseket.
Active Directory-felhasználó létrehozása az SQL Serverhez, és szolgáltatásnév beállítása az adutil használatával
Az Active Directory-hitelesítés Linux-tárolókon futó SQL Serveren való engedélyezéséhez az alábbi lépéseket kell végrehajtani az Active Directory-tartomány részét képező Linux-gépen.
Szerezze be vagy újítsa meg a Kerberos TGT-t (jegykiadó jegy) a
kinitparanccsal. Használjon emelt szintű fiókot akinitparancshoz. A fióknak engedéllyel kell rendelkeznie a tartományhoz való csatlakozáshoz, és képesnek kell lennie fiókokat és szolgáltatásnév főnévrekordokat létrehozni a tartományban.Ebben a példaszkriptben már létrehozott egy
privilegeduser@CONTOSO.COMnevű kiemelt felhasználót a tartományvezérlőn.kinit privilegeduser@CONTOSO.COMAz adutilhasználatával hozza létre azt az új felhasználót, amelyet az SQL Server kiemelt Active Directory-fiókként fog használni. Cserélje le a
<password>érvényes jelszóra.adutil user create --name sqluser --distname CN=sqluser,CN=Users,DC=CONTOSO,DC=COM --password '<password>'A jelszavakat a következő három módon lehet megadni:
- Jelszójelző:
--password <password> - Környezeti változók –
ADUTIL_ACCOUNT_PWD - Interaktív bemenet
A jelszóbeviteli módszerek elsőbbsége a fent felsorolt beállítások sorrendjét követi. Az ajánlott beállítások a jelszó környezeti változók vagy interaktív bemenetek használatával történő megadása, mivel biztonságosabbak a jelszójelzőhöz képest.
A fiók nevét a fent látható megkülönböztető névvel (
-distname) adhatja meg, vagy használhatja a szervezeti egység (szervezeti egység) nevét is. A szervezeti egység neve (--ou) elsőbbséget élvez a megkülönböztető névvel szemben, ha mindkettőt megadja. További részletekért futtassa az alábbi parancsot:adutil user create --help- Jelszójelző:
Regisztrálja az SPN-eket a fent létrehozott felhasználónak. Igény szerint a gazdagép nevét is használhatja a tároló neve helyett, attól függően, hogy a kapcsolat külsőleg hogyan nézzen ki. Ebben az oktatóanyagban a port
5433lesz használva1433helyett. Ez a tároló portleképezése. A portszám eltérő lehet.adutil spn addauto -n sqluser -s MSSQLSvc -H sql1.contoso.com -p 5433-
addautoautomatikusan létrehozza az SPN-eket, feltéve, hogy elegendő jogosultság van a kinit fiókhoz. -
-n: Annak a fióknak a neve, amelyhez a szolgáltatási főnév megnevezések (SPN-ek) hozzá lesznek rendelve. -
-s: Az SPN-ek (Szolgáltatásnév-azonosítók) létrehozásához használandó szolgáltatásnév. Ebben az esetben az SQL Server szolgáltatáshoz tartozik, ezért a szolgáltatás neve MSSQLSvc. -
-H: Az SPN-ek (Szolgáltatási Főnevek) létrehozásához használt állomásnév. Amennyiben nincs megadva, a helyi gazdagép teljes tartományneve (FQDN) kerül felhasználásra. Adja meg a tároló nevének teljes tartománynevét is. Ebben az esetben a tároló nevesql1, a teljes tartománynév pedigsql1.contoso.com. -
-p: Az SPN-k létrehozásához használt port. Ha nincs megadva, a SPN-k port nélkül jönnek létre. A kapcsolatok ebben az esetben csak akkor működnek, ha az SQL Server az alapértelmezett portot figyeli,1433.
-
SQL Server service keytab fájl létrehozása
Hozza létre a keytab-fájlt, amely a korábban létrehozott négy egyszerű szolgáltatásnév mindegyikéhez tartalmaz bejegyzéseket, egyet pedig a felhasználó számára. A keytab-fájl a tárolóhoz lesz csatlakoztatva, így a gazdagép bármely pontján létrehozható. Biztonságosan módosíthatja ezt az elérési utat, feltéve hogy a keletkező keytab helyesen van csatolva a tároló docker/podman használatával történő üzembe helyezésekor.
Az összes SPN keytabjának létrehozásához használhatjuk a createauto opciót. Cserélje le a <password> érvényes jelszóra.
adutil keytab createauto -k /container/sql1/secrets/mssql.keytab -p 5433 -H sql1.contoso.com --password '<password>' -s MSSQLSvc
-
-k: Elérési út, ahol létre szeretné hozni amssql.keytabfájlt. Az előző példában a/container/sql1/secretskönyvtárnak már léteznie kell a gazdagépen. -
-p: Az SPN-k létrehozásához használt port. Ha nincs megadva, a SPN-k port nélkül jönnek létre. -
-H: Az SPN-ek (Szolgáltatási Főnevek) létrehozásához használt állomásnév. Ha nincs megadva, a rendszer a helyi gazdagép teljes tartománynevét használja. Adja meg a tároló nevének teljes tartománynevét is. Ebben az esetben a tároló nevesql1, a teljes tartománynév pedigsql1.contoso.com. -
-s: Az SPN-ek (Szolgáltatásnév-azonosítók) létrehozásához használandó szolgáltatásnév. Ebben az esetben az SQL Server szolgáltatáshoz tartozik, ezért a szolgáltatás neve MSSQLSvc. -
--password: Ez a korábban létrehozott kiemelt Active Directory-felhasználói fiók jelszava. -
-evagy--enctype: A keytab bejegyzés titkosítási típusai. Használjon vesszővel tagolt értéklistát. Ha nincs megadva, megjelenik egy interaktív üzenet.
Ha választhat a titkosítási típusok közül, több közül is választhat. Ebben a példában aes256-cts-hmac-sha1-96 és arcfour-hmacválasztottuk. Győződjön meg arról, hogy a gazdagép és a domain által támogatott titkosítási típust választja.
Ha nem interaktív módon szeretné kiválasztani a titkosítás típusát, megadhatja a titkosítás típusát a fenti parancs -e argumentumával. Az adutil parancsokkal kapcsolatos további segítségért futtassa az alábbi parancsot.
adutil keytab createauto --help
Vigyázat
arcfour-hmac gyenge titkosítás, és nem ajánlott titkosítási típus éles környezetben.
A felhasználó kulcstáblájának létrehozásához a parancs a következő. Cserélje le a <password> érvényes jelszóra.
adutil keytab create -k /container/sql1/secrets/mssql.keytab -p sqluser --password '<password>'
-
-k: Elérési út, ahol létre szeretné hozni amssql.keytabfájlt. Az előző példában a/container/sql1/secretskönyvtárnak már léteznie kell a gazdagépen. -
-p: Principal hozzáadása a keytab-hoz.
Az adutil keytab create/autocreate nem írja felül az előző fájlokat; ha már létezik, hozzáfűzi a fájlhoz.
Győződjön meg arról, hogy a létrehozott kulcstartó rendelkezik a megfelelő engedélyekkel a tároló üzembe helyezésekor.
chmod 440 /container/sql1/secrets/mssql.keytab
Ezen a ponton átmásolhatja mssql.keytab az aktuális Linux-gazdagépről arra a Linux-gazdagépre, ahol üzembe helyezné az SQL Server-tárolót, és kövesse az SQL Server-tárolót futtató Linux-gazdagép többi lépését. Ha a fenti lépéseket ugyanazon a Linux-gazdagépen hajtották végre, ahol az SQL Server-tárolók üzembe lesznek helyezve, kövesse a következő lépéseket ugyanazon a gazdagépen is.
Az SQL Server-tároló által használandó konfigurációs fájlok létrehozása
Hozzon létre egy
mssql.conffájlt az Active Directory beállításaival. Ez a fájl bárhol létrehozható a gazdagépen, és a docker futtatási parancs során megfelelően kell csatolni. Ebben a példában ezt a fájltmssql.conf/container/sql1alá helyeztük, amely a tárolókönyvtárunk. Amssql.conftartalma a következőképpen jelenik meg:[network] privilegedadaccount = sqluser kerberoskeytabfile = /var/opt/mssql/secrets/mssql.keytab-
privilegedadaccount: Az Active Directory-hitelesítéshez használható kiemelt Active Directory-felhasználó. -
kerberoskeytabfile: Annak a tárolónak az elérési útja, ahol amssql.keytabfájl található.
-
Hozzon létre egy
krb5.conffájlt, például az alábbi mintát. Ezekben a fájlokban a burkolat számít.[libdefaults] default_realm = CONTOSO.COM default_keytab_name = /var/opt/mssql/secrets/mssql.keytab default_ccache_name = "" [realms] CONTOSO.COM = { kdc = adVM.contoso.com admin_server = adVM.contoso.com default_domain = CONTOSO.COM } [domain_realm] .contoso.com = CONTOSO.COM contoso.com = CONTOSO.COMMásolja az összes fájlt,
mssql.conf,krb5.conf,mssql.keytabegy olyan helyre, amely az SQL Server-tárolóhoz lesz csatlakoztatva. Ebben a példában ezek a fájlok a gazdagépen a következő helyeken találhatók:mssql.conféskrb5.conf/container/sql1/.mssql.keytaba/container/sql1/secrets/helyén van elhelyezve.Győződjön meg arról, hogy elegendő engedély van ezeken a mappákon a docker/podman parancsot futtató felhasználó számára. A tároló indításakor a felhasználónak hozzá kell férnie a létrehozott mappa elérési úthoz. Ebben a példában az alábbi engedélyeket adtuk meg a mappa elérési útjának:
sudo chmod 755 /container/sql1/
Konfigurációs fájlok csatlakoztatása és SQL Server-tároló üzembe helyezése
Futtassa az SQL Server-tárolót, és csatlakoztassa a korábban létrehozott megfelelő Active Directory-konfigurációs fájlokat:
Fontos
A SA_PASSWORD környezeti változó elavult. Használjon inkább MSSQL_SA_PASSWORD.
sudo docker run -e "ACCEPT_EULA=Y" -e "MSSQL_SA_PASSWORD=<password>" \
-p 5433:1433 --name sql1 \
-v /container/sql1:/var/opt/mssql \
-v /container/sql1/krb5.conf:/etc/krb5.conf \
-d mcr.microsoft.com/mssql/server:2019-latest
Vigyázat
A jelszónak az SQL Server alapértelmezett jelszóházirendetkell követnie. Alapértelmezés szerint a jelszónak legalább nyolc karakter hosszúnak kell lennie, és a következő négy készletből három karakterből kell állnia: nagybetűk, kisbetűk, 10 számjegyből és szimbólumokból. A jelszavak legfeljebb 128 karakter hosszúak lehetnek. Használjon olyan jelszavakat, amelyek a lehető legkomplexebbek és hosszúak.
Amikor konténert futtat Linux biztonsági modulon (LSM), mint például az SELinux-engedélyezett gazdagépeken, csatlakoztatnia kell a köteteket a Z beállítással, amely arra utasítja a Dockert, hogy címkézze meg a tartalmat egy privát, nem tagolt címkével. További információ: SE Linux-címke konfigurálása.
A példánk a következő parancsokat tartalmazza. Cserélje le a <password> érvényes jelszóra.
sudo docker run -e "ACCEPT_EULA=Y" -e "MSSQL_SA_PASSWORD=<password>" -p 5433:1433 --name sql1 \
-v /container/sql1:/var/opt/mssql/ \
-v /container/sql1/krb5.conf:/etc/krb5.conf \
--dns-search contoso.com \
--dns 10.0.0.4 \
--add-host adVM.contoso.com:10.0.0.4 \
--add-host contoso.com:10.0.0.4 \
--add-host contoso:10.0.0.4 \
-d mcr.microsoft.com/mssql/server:2019-latest
- A fájlok
mssql.conféskrb5.confa gazdagépfájl elérési útján találhatók/container/sql1. - A létrehozott
mssql.keytaba gazdagép fájl elérési útján található/container/sql1/secrets. - Mivel a gazdagép az Azure-ban található, az Active Directory adatait ugyanabban a sorrendben kell hozzáfűzni a
docker runparancshoz. A példánkban aadVMtartományvezérlő acontoso.comtartományba tartozik,10.0.0.4IP-címmel. A tartományvezérlő DNS-t és KDC-t futtat.
Active Directory-alapú SQL Server-bejelentkezések létrehozása Transact-SQL
Csatlakozzon az SQL Server-tárolóhoz. Az alábbi parancsokkal hozza létre a bejelentkezést, és győződjön meg arról, hogy létezik.
Jegyzet
Az SQL Server egy példányához bármilyen ismerős SQL Server-ügyféleszközzel csatlakozhat, például sqlcmd, SQL Server Management Studio (SSMS) vagy a Visual Studio Code MSSQL-bővítményével.
CREATE LOGIN [contoso\amvin]
FROM WINDOWS;
SELECT name
FROM sys.server_principals;
Csatlakozás az SQL Serverhez Active Directory-hitelesítéssel
Az SQL Server egy példányához bármilyen ismerős SQL Server-ügyféleszközzel csatlakozhat, például sqlcmd, SQL Server Management Studio (SSMS) vagy a Visual Studio Code MSSQL-bővítményével.
Lépjen be az SQL szerverre Windows azonosító adatokkal az SQL szerver nevének és portszámának megadásával (a név lehet a tároló neve vagy a gép neve). Példánkban a kiszolgáló neve sql1.contoso.com,5433lenne.
Az alábbi parancs bemutatja, hogyan csatlakozhat a tárolóhoz sqlcmd használatával.
sqlcmd -E -S 'sql1.contoso.com,5433'
Erőforrások
- Az SQL Server Active Directory-hitelesítésének ismertetése Linuxon és tárolókon
- Linuxon és tárolókon futó SQL Server Active Directory-hitelesítésének hibaelhárítása