Connect your organization to Microsoft Entra ID
Azure DevOps Services
This article shows how to connect your Azure DevOps organization to Microsoft Entra ID. You can sign in with the same username and password that you use with Microsoft services. Add members to your Azure DevOps organization who are already a part of your work organization. You can also enforce policies for accessing your team's critical resources and key assets.
For more information about using Microsoft Entra ID with Azure DevOps, see the conceptual overview.
Prerequisites
-
Permissions: Be a member of the Project Collection Administrators group. Organization owners are automatically members of this group.
Access levels:
- Be a member in the destination Microsoft Entra ID. For more information, see how to convert a Microsoft Entra guest into a member.
- Be a member or a guest in the source Microsoft Entra ID.
User management:
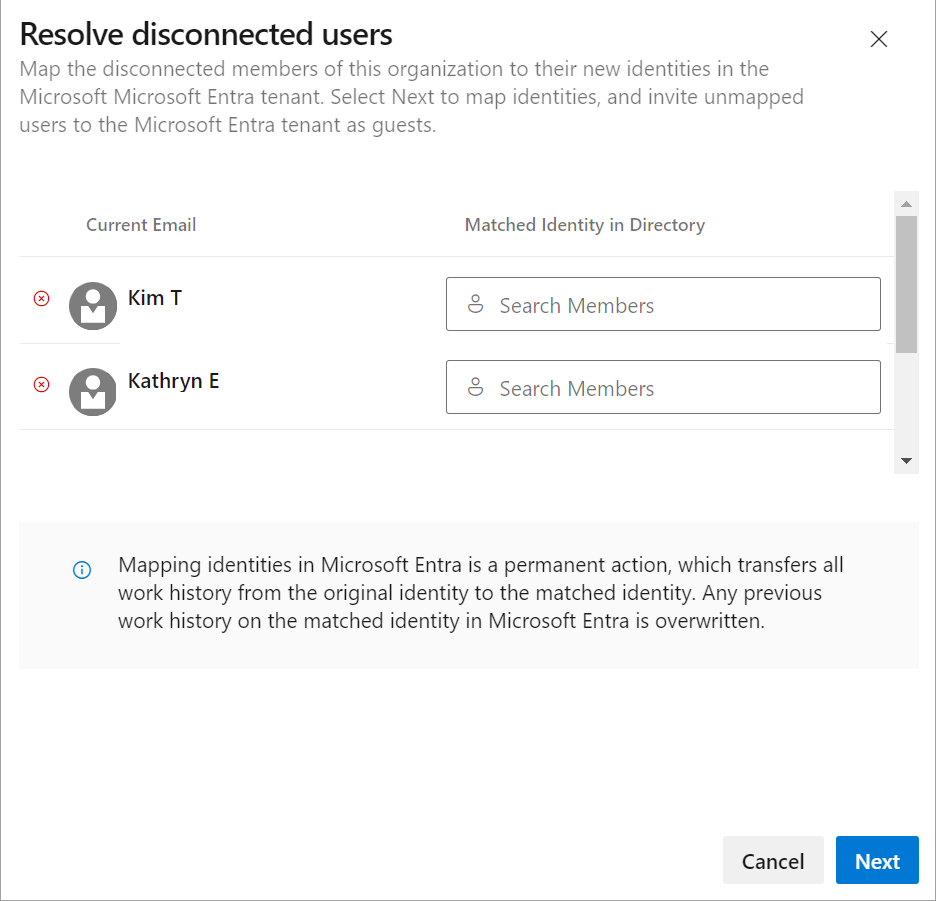
- Confirm there are 100 or fewer users in your organization. If your organization has more than 100 users, contact Support to resolve any disconnected users. You can map them to their Microsoft Entra identities in the new tenant.
- Don't add the users from the destination Microsoft Entra ID into the Azure DevOps organization.
- Delete unwanted users from your organization. For example, you can remove a user who left the company and is no longer an employee.
Inform users of the upcoming change. There's no downtime during this change, but users are affected. Let them know before you begin that there's a short series of steps they need to complete. As your company transitions from Microsoft account (MSA) to Microsoft Entra identities, your users' benefits continue with their new identity, as long as their emails match.
Compare your Azure DevOps email list with your Microsoft Entra ID email list. Create a Microsoft Entra ID email address entry for every user who's in the Azure DevOps organization and not in the Microsoft Entra ID. Afterward, you can invite users as guests who don't have Microsoft Entra ID email addresses.
Note
Ensure you're using Microsoft Entra Public. Connecting Azure DevOps Services organizations to Microsoft Entra Government and accessing Azure DevOps Services with user accounts from Microsoft Entra Government isn't supported.
Connect your organization to Microsoft Entra ID
To connect your organization to Microsoft Entra ID, do the following steps:
Sign in to your organization (
https://dev.azure.com/{yourorganization}).Select
 Organization settings.
Organization settings.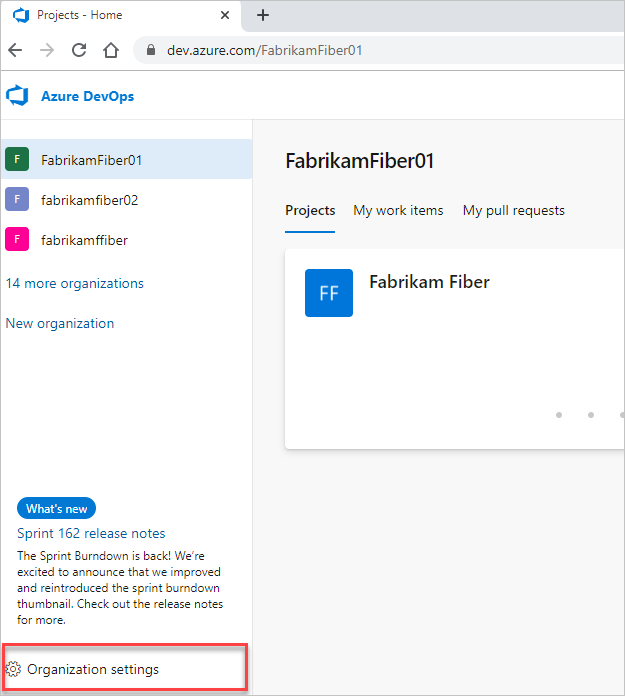
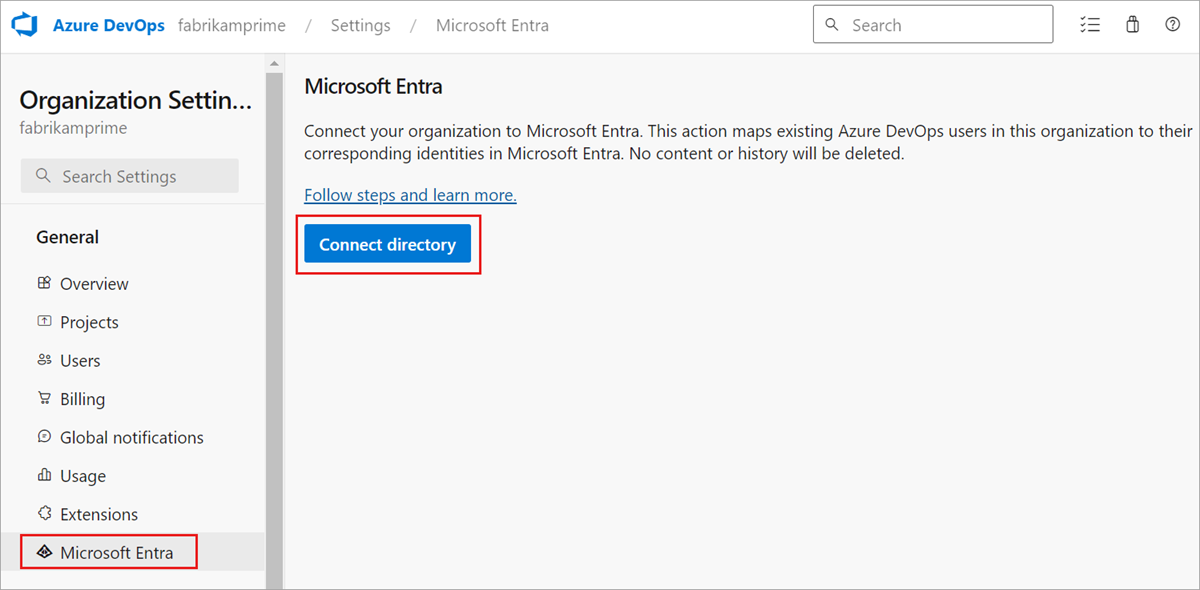
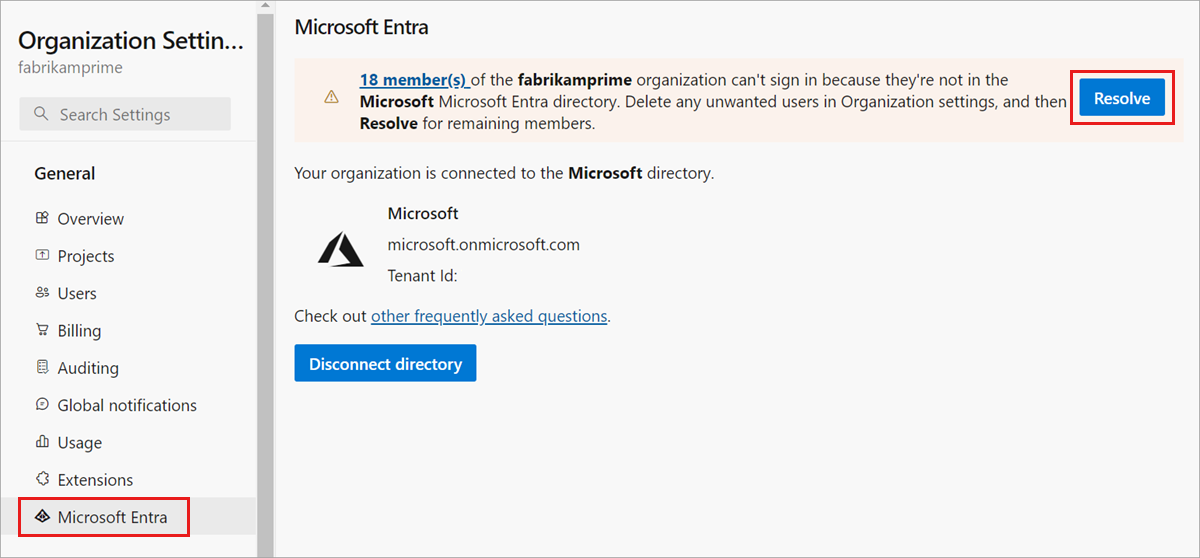
Select Microsoft Entra ID, and then select Connect directory.
Select a directory from the dropdown menu, and then select Connect.
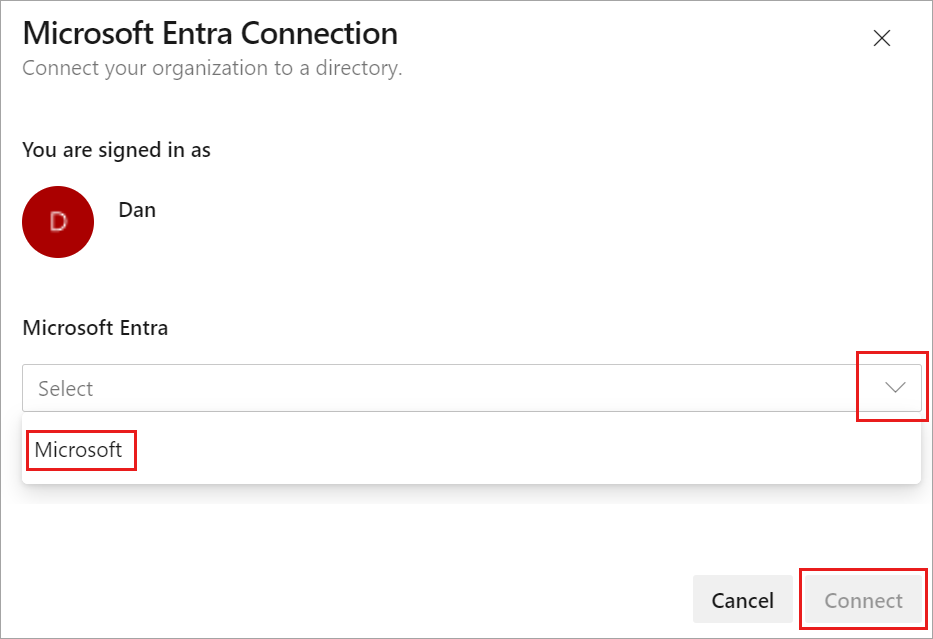
If you can't find your directory, contact your Microsoft Entra administrator and request that they add you as a member to the Microsoft Entra ID.
Select Sign out.
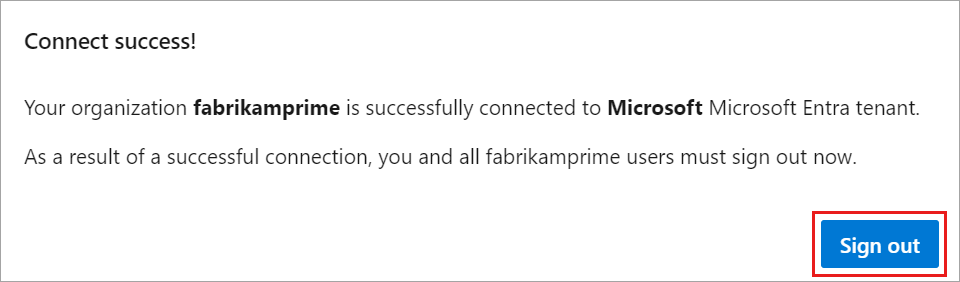
Your organization is connected to your Microsoft Entra ID.
Confirm that the process is complete. Sign out, and then open your browser in a private session and sign in to your organization with your Microsoft Entra ID or work credentials.
Sign back in to Azure DevOps and map any disconnected members to their Microsoft Entra identities. Or, you can invite them as guests into the Microsoft Entra ID. For more information, see the FAQs.
Inform users of the completed Microsoft Entra change
When you inform your users of the completed change, provide them with the following tasks to do:
Sign out of Azure DevOps.
Clear browser cache. If you use Visual Studio or the Git command-line too, clear the cache for the Git Credential Manager. Delete the %LocalAppData%\GitCredentialManager\tenant.cache file on each client machine.
Sign in to Azure DevOps using Microsoft Entra ID or work credentials.
Reconfigure any personal access tokens (PATs) or SSH keys, if necessary.
- PATs: Complete the steps in Use personal access tokens.
- SSH keys:
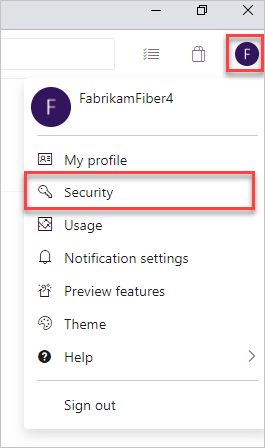
- In Azure DevOps, open your profile, and then select Security from the resulting dropdown menu.
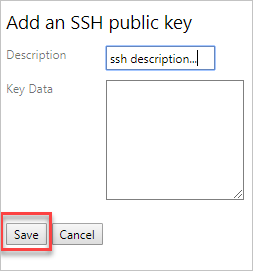
- Select SSH public keys, and then select Add.
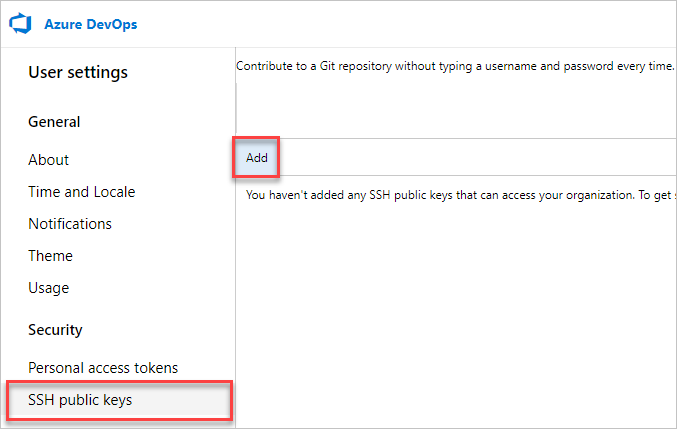
- Enter a description and key data, and then select Save.
- Copy your key and put it in a safe place, since you can't view it again.
Rename your Microsoft account (MSA). Rename your MSA to a different email that doesn't conflict with your Microsoft Entra identity. Doing so ensures that you aren't prompted to choose between accounts.
(Optional) Adjust your visual Studio (VS) subscription. If the UPN used inside your organization changed, adjust your Visual Studio subscription. You can reassign the subscription to your new UPN, or set that UPN as the alternate account inside the subscription. For more information, see how to add an alternate account to your subscription.