Tutorial: Configure Blink for automatic user provisioning
The objective of this tutorial is to demonstrate the steps to be performed in Blink and Microsoft Entra ID to configure Microsoft Entra ID to automatically provision and de-provision users to Blink.
Note
This tutorial describes a connector built on top of the Microsoft Entra user Provisioning Service. For important details on what this service does, how it works, and frequently asked questions, see Automate user provisioning and deprovisioning to SaaS applications with Microsoft Entra ID.
Prerequisites
The scenario outlined in this tutorial assumes that you already have the following prerequisites:
- A Microsoft Entra tenant
- A Blink tenant
- A user account in Blink with Admin permissions.
Note
This integration is also available to use from Microsoft Entra US Government Cloud environment. You can find this application in the Microsoft Entra US Government Cloud Application Gallery and configure it in the same way as you do from public cloud.
Assigning users to Blink
Microsoft Entra ID uses a concept called assignments to determine which users should receive access to selected apps. In the context of automatic user provisioning, only the users and/or group members that have been assigned to an application in Microsoft Entra ID are synchronized.
Before configuring and enabling automatic user provisioning, you should decide which users and/or group members in Microsoft Entra ID need access to Blink. Once decided, you can assign these users and/or groups to Blink by following the instructions here:
Important tips for assigning users to Blink
It is recommended that a single Microsoft Entra user is assigned to Blink to test the automatic user provisioning configuration. Additional users and/or groups may be assigned later.
When assigning a user to Blink, you must select any valid application-specific role (if available) in the assignment dialog. Users with the Default Access role are excluded from provisioning.
Setup Blink for provisioning
Log a Support Case or email Blink support at support@joinblink.com to request a SCIM token.
Copy the SCIM Authentication Token. This value will be entered in the Secret Token field in the Provisioning tab of your Blink application.
Add Blink from the gallery
Before configuring Blink for automatic user provisioning with Microsoft Entra ID, you need to add Blink from the Microsoft Entra application gallery to your list of managed SaaS applications.
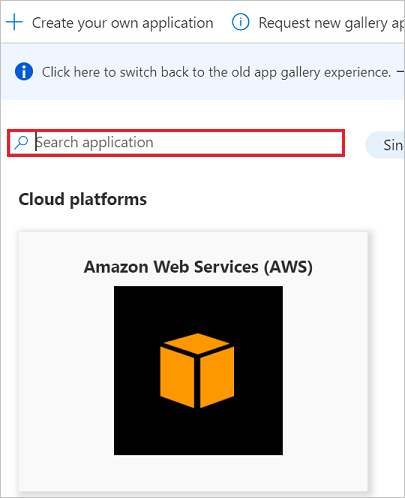
To add Blink from the Microsoft Entra application gallery, perform the following steps:
- Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
- Browse to Identity > Applications > Enterprise applications > New application.
- In the Add from the gallery section, type Blink, select Blink in the search box.
- Select Blink from results panel and then add the app. Wait a few seconds while the app is added to your tenant.
Configuring automatic user provisioning to Blink
This section guides you through the steps to configure the Microsoft Entra provisioning service to create, update, and disable users in Blink based on user and/or group assignments in Microsoft Entra ID.
Tip
You may also choose to enable SAML-based single sign-on for Blink, following the instructions provided in the Blink Single sign-on tutorial. Single sign-on can be configured independently of automatic user provisioning, though these two features complement each other
To configure automatic user provisioning for Blink in Microsoft Entra ID:
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
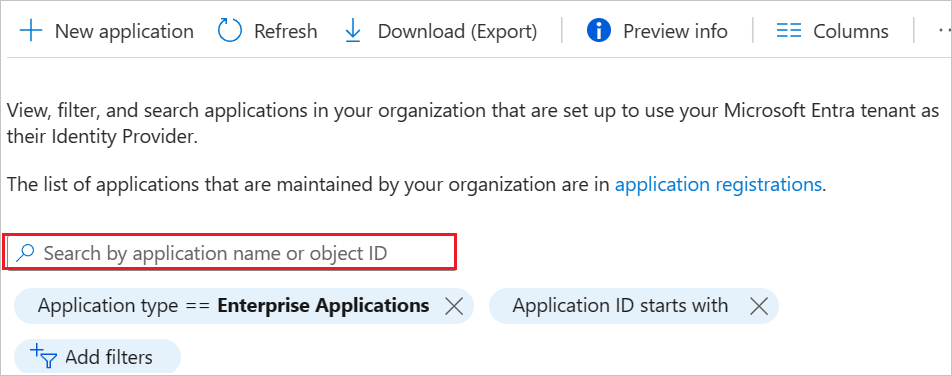
Browse to Identity > Applications > Enterprise applications
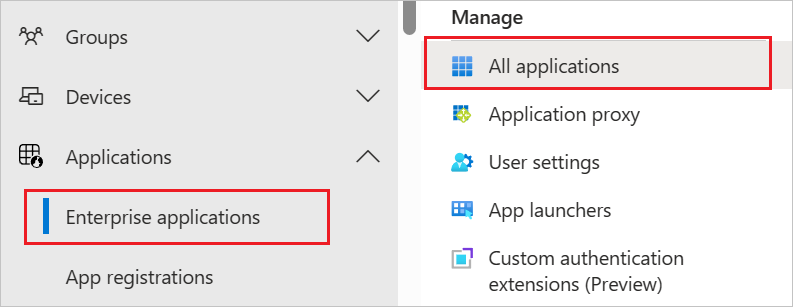
In the applications list, select Blink.
Select the Provisioning tab.
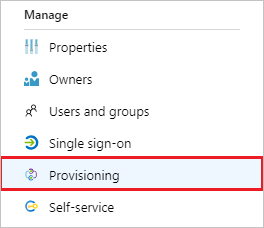
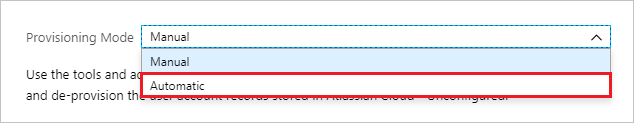
Set the Provisioning Mode to Automatic.
Under the Admin Credentials section, input
https://api.joinblink.com/scimin Tenant URL. Input the SCIM Authentication Token value retrieved earlier in Secret Token. Click Test Connection to ensure Microsoft Entra ID can connect to Blink. If the connection fails, ensure your Blink account has Admin permissions and try again.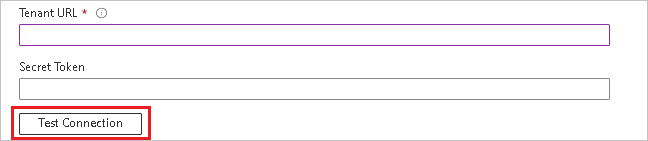
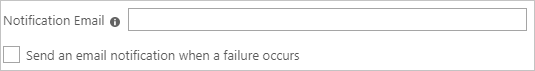
In the Notification Email field, enter the email address of a person or group who should receive the provisioning error notifications and check the checkbox - Send an email notification when a failure occurs.
Click Save.
Under the Mappings section, select Synchronize Microsoft Entra users to Blink.
Review the user attributes that are synchronized from Microsoft Entra ID to Blink in the Attribute Mapping section. The attributes selected as Matching properties are used to match the user accounts in Blink for update operations. Select the Save button to commit any changes.
Attribute Type Supported for filtering userName String ✓ active Boolean title String emails[type eq "work"].value String name.givenName String name.familyName String phoneNumbers[type eq "work"].value String phoneNumbers[type eq "mobile"].value String externalId String urn:ietf:params:scim:schemas:extension:enterprise:2.0:User:department String urn:ietf:params:scim:schemas:extension:enterprise:2.0:User:employeeNumber String urn:ietf:params:scim:schemas:extension:enterprise:2.0:User:manager Reference urn:ietf:params:scim:schemas:extension:blink:2.0:User:company String urn:ietf:params:scim:schemas:extension:blink:2.0:User:description String urn:ietf:params:scim:schemas:extension:blink:2.0:User:location String To configure scoping filters, refer to the following instructions provided in the Scoping filter tutorial.
To enable the Microsoft Entra provisioning service for Blink, change the Provisioning Status to On in the Settings section.

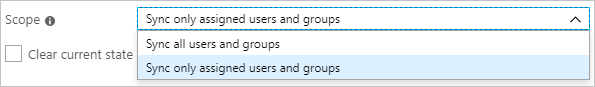
Define the users that you would like to provision to Blink by choosing the desired values in Scope in the Settings section.
When you are ready to provision, click Save.

This operation starts the initial synchronization of all users defined in Scope in the Settings section. The initial sync takes longer to perform than subsequent syncs, which occur approximately every 40 minutes as long as the Microsoft Entra provisioning service is running. You can use the Synchronization Details section to monitor progress and follow links to provisioning activity report, which describes all actions performed by the Microsoft Entra provisioning service on Blink.
For more information on how to read the Microsoft Entra provisioning logs, see Reporting on automatic user account provisioning.
Step 6: Monitor your deployment
Once you've configured provisioning, use the following resources to monitor your deployment:
- Use the provisioning logs to determine which users have been provisioned successfully or unsuccessfully
- Check the progress bar to see the status of the provisioning cycle and how close it is to completion
- If the provisioning configuration seems to be in an unhealthy state, the application will go into quarantine. Learn more about quarantine states here.
Change log
- 01/14/2021 - Custom extension attributes company, description, and location have been added.
Additional resources
- Managing user account provisioning for Enterprise Apps
- What is application access and single sign-on with Microsoft Entra ID?