4703(S): A user right was adjusted.
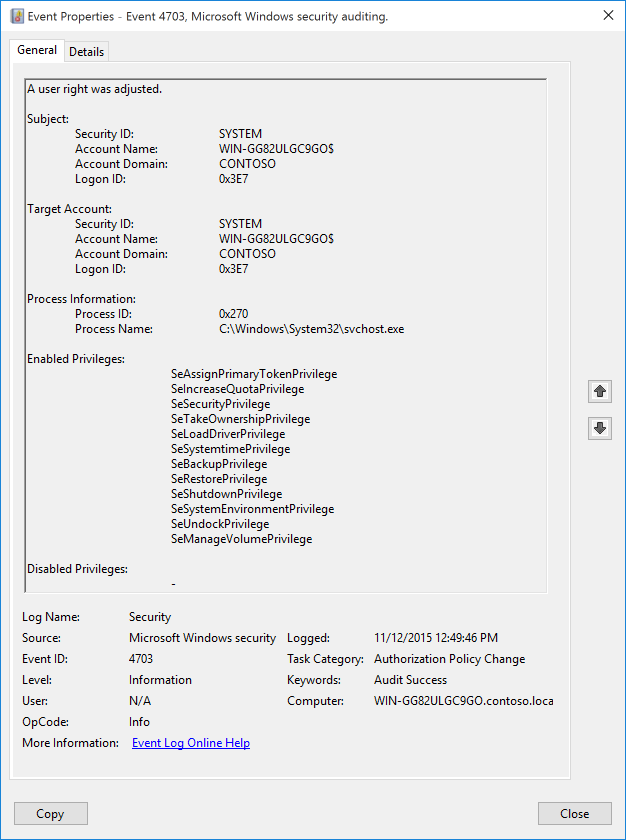
Subcategory: Audit Authorization Policy Change
Event Description:
This event generates when token privileges were enabled or disabled for a specific account’s token. As of Windows 10, event 4703 is also logged by applications or services that dynamically adjust token privileges. An example of such an application is Microsoft Configuration Manager, which makes WMI queries at recurring intervals and quickly generates a large number of 4703 events (with the WMI activity listed as coming from svchost.exe). If you are using an application or system service that makes changes to system privileges through the AdjustPrivilegesToken API, you might need to disable Success auditing for this subcategory (Audit Authorization Policy Change), or work with a very high volume of event 4703.
Note For recommendations, see Security Monitoring Recommendations for this event.
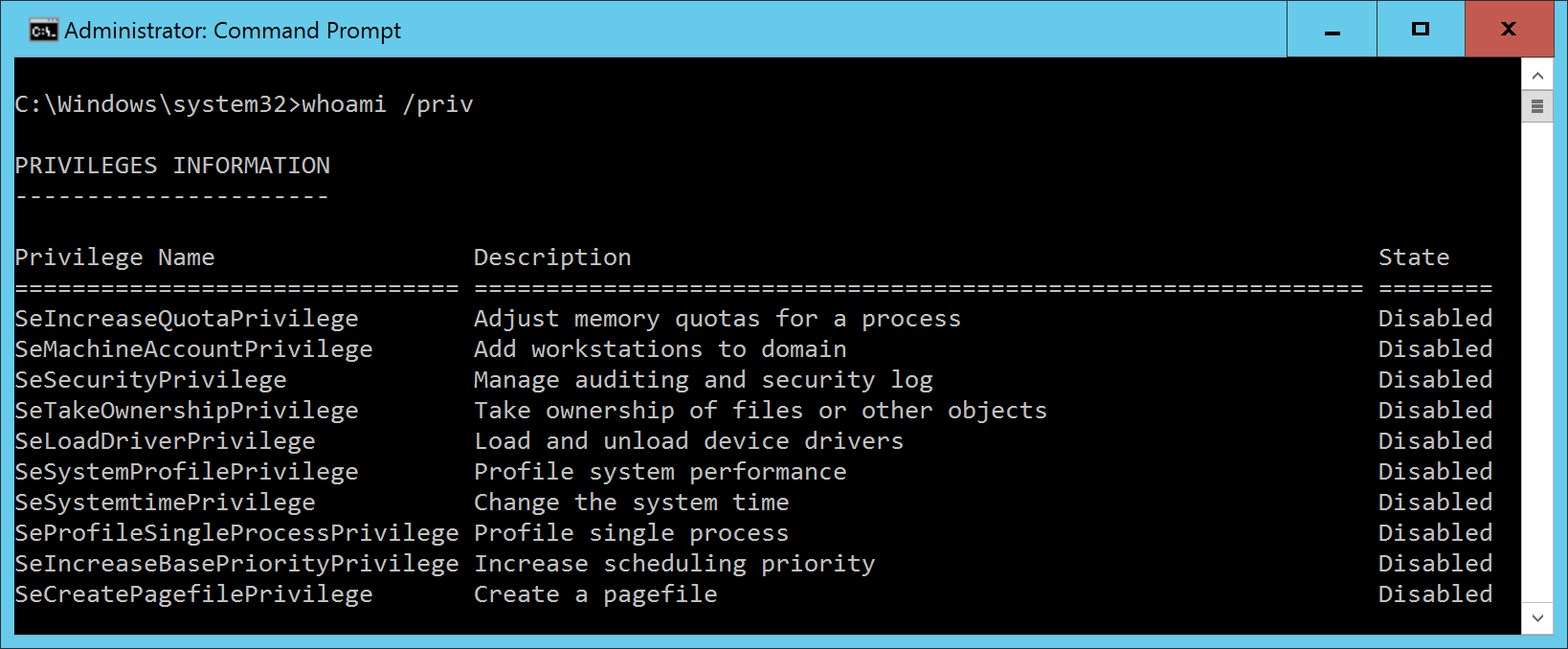
Token privileges provide the ability to take certain system-level actions that you only need to do at particular moments. For example, anybody can restart a computer, but the operating system doesn’t enable that privilege by default. Instead, the privilege is enabled when you click Shutdown. You can check the current state of the user’s token privileges using the whoami /priv command:
Event XML:
- <Event xmlns="http://schemas.microsoft.com/win/2004/08/events/event">
- <System>
<Provider Name="Microsoft-Windows-Security-Auditing" Guid="{54849625-5478-4994-A5BA-3E3B0328C30D}" />
<EventID>4703</EventID>
<Version>0</Version>
<Level>0</Level>
<Task>13570</Task>
<Opcode>0</Opcode>
<Keywords>0x8020000000000000</Keywords>
<TimeCreated SystemTime="2015-11-12T20:49:46.365958700Z" />
<EventRecordID>5245</EventRecordID>
<Correlation />
<Execution ProcessID="4" ThreadID="3632" />
<Channel>Security</Channel>
<Computer>WIN-GG82ULGC9GO.contoso.local</Computer>
<Security />
</System>
- <EventData>
<Data Name="SubjectUserSid">S-1-5-18</Data>
<Data Name="SubjectUserName">WIN-GG82ULGC9GO$</Data>
<Data Name="SubjectDomainName">CONTOSO</Data>
<Data Name="SubjectLogonId">0x3e7</Data>
<Data Name="TargetUserSid">S-1-5-18</Data>
<Data Name="TargetUserName">WIN-GG82ULGC9GO$</Data>
<Data Name="TargetDomainName">CONTOSO</Data>
<Data Name="TargetLogonId">0x3e7</Data>
<Data Name="ProcessName">C:\\Windows\\System32\\svchost.exe</Data>
<Data Name="ProcessId">0x270</Data>
<Data Name="EnabledPrivilegeList">SeAssignPrimaryTokenPrivilege SeIncreaseQuotaPrivilege SeSecurityPrivilege SeTakeOwnershipPrivilege SeLoadDriverPrivilege SeSystemtimePrivilege SeBackupPrivilege SeRestorePrivilege SeShutdownPrivilege SeSystemEnvironmentPrivilege SeUndockPrivilege SeManageVolumePrivilege</Data>
<Data Name="DisabledPrivilegeList">-</Data>
</EventData>
</Event>
Required Server Roles: None.
Minimum OS Version: Windows Server 2016, Windows 10.
Event Versions: 0.
Field Descriptions:
Subject:
- Security ID [Type = SID]: SID of account that requested the “enable” or “disable” operation for Target Account privileges. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
Note A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString]: the name of the account that requested the “enable” or “disable” operation for Target Account privileges.
Account Domain [Type = UnicodeString]: subject’s domain or computer name. Formats vary, and include the following:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, “4624: An account was successfully logged on.”
Target Account:
- Security ID [Type = SID]: SID of account for which privileges were enabled or disabled. Event Viewer automatically tries to resolve SIDs and show the account name. If the SID cannot be resolved, you will see the source data in the event.
Note A security identifier (SID) is a unique value of variable length used to identify a trustee (security principal). Each account has a unique SID that is issued by an authority, such as an Active Directory domain controller, and stored in a security database. Each time a user logs on, the system retrieves the SID for that user from the database and places it in the access token for that user. The system uses the SID in the access token to identify the user in all subsequent interactions with Windows security. When a SID has been used as the unique identifier for a user or group, it cannot ever be used again to identify another user or group. For more information about SIDs, see Security identifiers.
Account Name [Type = UnicodeString]: the name of the account for which privileges were enabled or disabled.
Account Domain [Type = UnicodeString]: subject’s domain or computer name. Formats vary, and include the following:
Domain NETBIOS name example: CONTOSO
Lowercase full domain name: contoso.local
Uppercase full domain name: CONTOSO.LOCAL
For some well-known security principals, such as LOCAL SERVICE or ANONYMOUS LOGON, the value of this field is “NT AUTHORITY”.
For local user accounts, this field will contain the name of the computer or device that this account belongs to, for example: “Win81”.
Logon ID [Type = HexInt64]: hexadecimal value that can help you correlate this event with recent events that might contain the same Logon ID, for example, “4624: An account was successfully logged on.”
Process Information:
Process ID [Type = Pointer]: hexadecimal Process ID of the process that enabled or disabled token privileges. Process ID (PID) is a number used by the operating system to uniquely identify an active process. To see the PID for a specific process you can, for example, use Task Manager (Details tab, PID column):
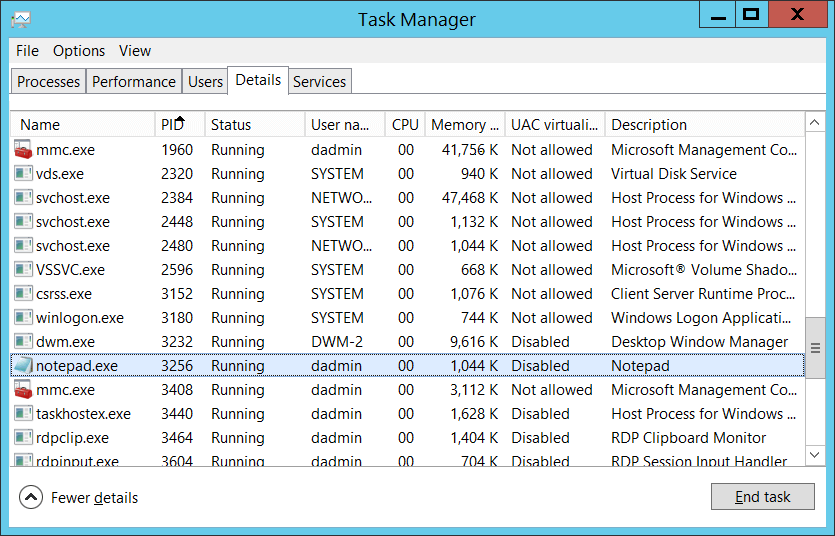
If you convert the hexadecimal value to decimal, you can compare it to the values in Task Manager.
You can also correlate this process ID with a process ID in other events, for example, “4688: A new process has been created” Process Information\New Process ID.
Process Name [Type = UnicodeString]: full path and the name of the executable for the process.
- Enabled Privileges [Type = UnicodeString]: the list of enabled user rights. This event generates only for user rights, not logon rights. Here is the list of possible user rights:
| Privilege Name | User Right Group Policy Name | Description |
|---|---|---|
| SeAssignPrimaryTokenPrivilege | Replace a process-level token | Required to assign the primary token of a process. With this privilege, the user can initiate a process to replace the default token associated with a started subprocess. |
| SeAuditPrivilege | Generate security audits | With this privilege, the user can add entries to the security log. |
| SeBackupPrivilege | Back up files and directories | - Required to perform backup operations. With this privilege, the user can bypass file and directory, registry, and other persistent object permissions for the purposes of backing up the system. This privilege causes the system to grant all read access control to any file, regardless of the access control list (ACL) specified for the file. Any access request other than read is still evaluated with the ACL. The following access rights are granted if this privilege is held: READ_CONTROL ACCESS_SYSTEM_SECURITY FILE_GENERIC_READ FILE_TRAVERSE |
| SeChangeNotifyPrivilege | Bypass traverse checking | Required to receive notifications of changes to files or directories. This privilege also causes the system to skip all traversal access checks. With this privilege, the user can traverse directory trees even though the user may not have permissions on the traversed directory. This privilege does not allow the user to list the contents of a directory, only to traverse directories. |
| SeCreateGlobalPrivilege | Create global objects | Required to create named file mapping objects in the global namespace during Terminal Services sessions. |
| SeCreatePagefilePrivilege | Create a pagefile | With this privilege, the user can create and change the size of a pagefile. |
| SeCreatePermanentPrivilege | Create permanent shared objects | Required to create a permanent object. This privilege is useful to kernel-mode components that extend the object namespace. Components that are running in kernel mode already have this privilege inherently; it is not necessary to assign them the privilege. |
| SeCreateSymbolicLinkPrivilege | Create symbolic links | Required to create a symbolic link. |
| SeCreateTokenPrivilege | Create a token object | Allows a process to create a token which it can then use to get access to any local resources when the process uses NtCreateToken() or other token-creation APIs. When a process requires this privilege, we recommend using the LocalSystem account (which already includes the privilege), rather than creating a separate user account and assigning this privilege to it. |
| SeDebugPrivilege | Debug programs | Required to debug and adjust the memory of a process owned by another account. With this privilege, the user can attach a debugger to any process or to the kernel. Developers who are debugging their own applications do not need this user right. Developers who are debugging new system components need this user right. This user right provides complete access to sensitive and critical operating system components. |
| SeEnableDelegationPrivilege | Enable computer and user accounts to be trusted for delegation | Required to mark user and computer accounts as trusted for delegation. With this privilege, the user can set the Trusted for Delegation setting on a user or computer object. The user or object that is granted this privilege must have write access to the account control flags on the user or computer object. A server process running on a computer (or under a user context) that is trusted for delegation can access resources on another computer using the delegated credentials of a client, as long as the account of the client does not have the Account cannot be delegated account control flag set. |
| SeImpersonatePrivilege | Impersonate a client after authentication | With this privilege, the user can impersonate other accounts. |
| SeIncreaseBasePriorityPrivilege | Increase scheduling priority | Required to increase the base priority of a process. With this privilege, the user can use a process with Write property access to another process to increase the execution priority assigned to the other process. A user with this privilege can change the scheduling priority of a process through the Task Manager user interface. |
| SeIncreaseQuotaPrivilege | Adjust memory quotas for a process | Required to increase the quota assigned to a process. With this privilege, the user can change the maximum memory that can be consumed by a process. |
| SeIncreaseWorkingSetPrivilege | Increase a process working set | Required to allocate more memory for applications that run in the context of users. |
| SeLoadDriverPrivilege | Load and unload device drivers | Required to load or unload a device driver. With this privilege, the user can dynamically load and unload device drivers or other code in to kernel mode. This user right does not apply to Plug and Play device drivers. |
| SeLockMemoryPrivilege | Lock pages in memory | Required to lock physical pages in memory. With this privilege, the user can use a process to keep data in physical memory, which prevents the system from paging the data to virtual memory on disk. Exercising this privilege could significantly affect system performance by decreasing the amount of available random access memory (RAM). |
| SeMachineAccountPrivilege | Add workstations to domain | With this privilege, the user can create a computer account. This privilege is valid only on domain controllers. |
| SeManageVolumePrivilege | Perform volume maintenance tasks | Required to run maintenance tasks on a volume, such as remote defragmentation. |
| SeProfileSingleProcessPrivilege | Profile single process | Required to gather profiling information for a single process. With this privilege, the user can use performance monitoring tools to monitor the performance of non-system processes. |
| SeRelabelPrivilege | Modify an object label | Required to modify the mandatory integrity level of an object. |
| SeRemoteShutdownPrivilege | Force shutdown from a remote system | Required to shut down a system using a network request. |
| SeRestorePrivilege | Restore files and directories | Required to perform restore operations. This privilege causes the system to grant all write access control to any file, regardless of the ACL specified for the file. Any access request other than write is still evaluated with the ACL. Additionally, this privilege enables you to set any valid user or group SID as the owner of a file. The following access rights are granted if this privilege is held: WRITE_DAC WRITE_OWNER ACCESS_SYSTEM_SECURITY FILE_GENERIC_WRITE FILE_ADD_FILE FILE_ADD_SUBDIRECTORY DELETE With this privilege, the user can bypass file, directory, registry, and other persistent objects permissions when restoring backed up files and directories and determines which users can set any valid security principal as the owner of an object. |
| SeSecurityPrivilege | Manage auditing and security log | Required to perform a number of security-related functions, such as controlling and viewing audit events in security event log. With this privilege, the user can specify object access auditing options for individual resources, such as files, Active Directory objects, and registry keys. A user with this privilege can also view and clear the security log. |
| SeShutdownPrivilege | Shut down the system | Required to shut down a local system. |
| SeSyncAgentPrivilege | Synchronize directory service data | This privilege enables the holder to read all objects and properties in the directory, regardless of the protection on the objects and properties. By default, it is assigned to the Administrator and LocalSystem accounts on domain controllers. With this privilege, the user can synchronize all directory service data. This is also known as Active Directory synchronization. |
| SeSystemEnvironmentPrivilege | Modify firmware environment values | Required to modify the nonvolatile RAM of systems that use this type of memory to store configuration information. |
| SeSystemProfilePrivilege | Profile system performance | Required to gather profiling information for the entire system. With this privilege, the user can use performance monitoring tools to monitor the performance of system processes. |
| SeSystemtimePrivilege | Change the system time | Required to modify the system time. With this privilege, the user can change the time and date on the internal clock of the computer. Users that are assigned this user right can affect the appearance of event logs. If the system time is changed, events that are logged will reflect this new time, not the actual time that the events occurred. |
| SeTakeOwnershipPrivilege | Take ownership of files or other objects | Required to take ownership of an object without being granted discretionary access. This privilege allows the owner value to be set only to those values that the holder may legitimately assign as the owner of an object. With this privilege, the user can take ownership of any securable object in the system, including Active Directory objects, files and folders, printers, registry keys, processes, and threads. |
| SeTcbPrivilege | Act as part of the operating system | This privilege identifies its holder as part of the trusted computer base. This user right allows a process to impersonate any user without authentication. The process can therefore gain access to the same local resources as that user. |
| SeTimeZonePrivilege | Change the time zone | Required to adjust the time zone associated with the computer's internal clock. |
| SeTrustedCredManAccessPrivilege | Access Credential Manager as a trusted caller | Required to access Credential Manager as a trusted caller. |
| SeUndockPrivilege | Remove computer from docking station | Required to undock a laptop. With this privilege, the user can undock a portable computer from its docking station without logging on. |
| SeUnsolicitedInputPrivilege | Not applicable | Required to read unsolicited input from a terminal device. |
Disabled Privileges [Type = UnicodeString]: the list of disabled user rights. See possible values in the table above.
Security Monitoring Recommendations
For 4703(S): A user right was adjusted.
As of Windows 10, event 4703 is generated by applications or services that dynamically adjust token privileges. An example of such an application is Microsoft Configuration Manager, which makes WMI queries at recurring intervals and quickly generates a large number of 4703 events (with the WMI activity listed as coming from svchost.exe). If you are using an application or system service that makes changes to system privileges through the AdjustPrivilegesToken API, you might need to disable Success auditing for this subcategory, Audit Authorization Policy Change, or work with a very high volume of event 4703.
Otherwise, see the recommendations in the following table.
| Type of monitoring required | Recommendation |
|---|---|
| High-value accounts: You might have high-value domain or local accounts for which you need to monitor each action. Examples of high-value accounts are database administrators, built-in local administrator account, domain administrators, service accounts, domain controller accounts and so on. |
Monitor this event with the “Subject\Security ID” that corresponds to the high-value account or accounts. |
| Anomalies or malicious actions: You might have specific requirements for detecting anomalies or monitoring potential malicious actions. For example, you might need to monitor for use of an account outside of working hours. | When you monitor for anomalies or malicious actions, use the “Subject\Security ID” (with other information) to monitor how or when a particular account is being used. |
| Non-active accounts: You might have non-active, disabled, or guest accounts, or other accounts that should never be used. | Monitor this event with the “Subject\Security ID” or “Target Account\Security ID” that correspond to the accounts that should never be used. |
| Account allowlist: You might have a specific allowlist of accounts that are the only ones allowed to perform actions corresponding to particular events. | If this event corresponds to an “allowlist-only” action, review the “Subject\Security ID” for accounts that are outside the allowlist. Also check the “Target Account\Security ID” and “Enabled Privileges” to see what was enabled. |
| Accounts of different types: You might want to ensure that certain actions are performed only by certain account types, for example, local or domain account, machine or user account, vendor or employee account, and so on. | If this event corresponds to an action you want to monitor for certain account types, review the “Subject\Security ID” to see whether the account type is as expected. |
| External accounts: You might be monitoring accounts from another domain, or “external” accounts that are not allowed to perform certain actions (represented by certain specific events). | Monitor this event for the “Subject\Account Domain” corresponding to accounts from another domain or “external” accounts. |
| Restricted-use computers or devices: You might have certain computers, machines, or devices on which certain people (accounts) should perform only limited actions, or no actions at all. | Monitor the target Computer: (or other target device) for actions performed by the “Subject\Security ID” that you are concerned about. Also check “Target Account\Security ID” to see whether the change in privileges should be made on that computer for that account. |
| User rights that should be restricted or monitored: You might have a list of user rights that you want to restrict or monitor. | Monitor this event and compare the “Enabled Privileges” to your list of user rights. Trigger an alert for user rights that should not be enabled, especially on high-value servers or other computers. For example, you might have SeDebugPrivilege on a list of user rights to be restricted. |
| Account naming conventions: Your organization might have specific naming conventions for account names. | Monitor “Subject\Account Name” for names that don’t comply with naming conventions. |