What is Microsoft Defender for Cloud?
Microsoft Defender for Cloud helps you prevent, detect, and respond to threats with increased visibility into and control over the security of your resources. It provides integrated security monitoring and policy management across your subscriptions, helps detect threats that might otherwise go unnoticed, and works with a broad ecosystem of security solutions.
Defender for Cloud uses monitoring components to collect and store data. For in-depth details, see Data collection in Microsoft Defender for Cloud.
How do I get Microsoft Defender for Cloud?
Microsoft Defender for Cloud is enabled with your Microsoft Azure subscription and accessed from the Azure portal. To access it, sign in to the portal, select Browse, and scroll to Defender for Cloud.
Is there a trial version of Defender for Cloud?
Defender for Cloud is free for the first 30 days. Any usage beyond 30 days is automatically charged as per the pricing scheme. Learn more. Note that malware scanning in Defender for Storage is not included for free in the first 30 day trial and will be charged from the first day.
Which Azure resources are monitored by Microsoft Defender for Cloud?
Microsoft Defender for Cloud monitors the following Azure resources:
- Virtual machines (VMs) (including Cloud Services)
- Virtual Machine Scale Sets
- The many Azure PaaS services listed in the product overview
Defender for Cloud also protects on-premises resources and multicloud resources, including Amazon AWS and Google Cloud.
How can I see the current security state of my Azure, multicloud, and on-premises resources?
The Defender for Cloud Overview page shows the overall security posture of your environment broken down by Compute, Networking, Storage & data, and Applications. Each resource type has an indicator showing identified security vulnerabilities. Selecting each tile displays a list of security issues identified by Defender for Cloud, along with an inventory of the resources in your subscription.
What is a security initiative?
A security initiative defines the set of controls (policies) that are recommended for resources within the specified subscription. In Microsoft Defender for Cloud, you assign initiatives for your Azure subscriptions, AWS accounts, and GCP projects according to your company's security requirements and the type of applications or sensitivity of the data in each subscription.
The security policies enabled in Microsoft Defender for Cloud drive security recommendations and monitoring. Learn more in What are security policies, initiatives, and recommendations?.
Who can modify a security policy?
To modify a security policy, you must be a Security Administrator or an Owner of that subscription.
To learn how to configure a security policy, see Setting security policies in Microsoft Defender for Cloud.
What is a security recommendation?
Microsoft Defender for Cloud analyzes the security state of your Azure, multicloud, and on-premises resources. When potential security vulnerabilities are identified, recommendations are created. The recommendations guide you through the process of configuring the needed control. Examples are:
- Provisioning of anti-malware to help identify and remove malicious software
- Network security groups and rules to control traffic to virtual machines
- Provisioning of a web application firewall to help defend against attacks targeting your web applications
- Deploying missing system updates
- Addressing OS configurations that don't match the recommended baselines
Only recommendations that are enabled in Security Policies are shown here.
What triggers a security alert?
Microsoft Defender for Cloud automatically collects, analyzes, and fuses log data from your Azure, multicloud, and on-premises resources, the network, and partner solutions like antimalware and firewalls. When threats are detected, a security alert is created. Examples include detection of:
- Compromised virtual machines communicating with known malicious IP addresses
- Advanced malware detected using Windows error reporting
- Brute force attacks against virtual machines
- Security alerts from integrated partner security solutions such as Anti-Malware or Web Application Firewalls
What's the difference between threats detected and alerted on by Microsoft Security Response Center versus Microsoft Defender for Cloud?
The Microsoft Security Response Center (MSRC) performs select security monitoring of the Azure network and infrastructure and receives threat intelligence and abuse complaints from third parties. When MSRC becomes aware that customer data was accessed by an unlawful or unauthorized party or that the customer's use of Azure doesn't comply with the terms for Acceptable Use, a security incident manager notifies the customer. Notification typically occurs by sending an email to the security contacts specified in Microsoft Defender for Cloud or the Azure subscription owner if a security contact isn't specified.
Defender for Cloud is an Azure service that continuously monitors the customer's Azure, multicloud, and on-premises environment and applies analytics to automatically detect a wide range of potentially malicious activity. These detections are surfaced as security alerts in the workload protection dashboard.
How can I track who in my organization enabled a Microsoft Defender plan in Defender for Cloud?
Azure Subscriptions might have multiple administrators with permissions to change the pricing settings. To find out which user made a change, use the Azure Activity Log.

If the user's info isn't listed in the Event initiated by column, explore the event's JSON for the relevant details.
![]()
What happens when one recommendation is in multiple policy initiatives?
Sometimes, a security recommendation appears in more than one policy initiative. If you have multiple instances of the same recommendation assigned to the same subscription, and you create an exemption for the recommendation, it affects all of the initiatives that you have permission to edit.
If you try to create an exemption for this recommendation, you'll see one of the two following messages:
If you have the necessary permissions to edit both initiatives, you'll see:
This recommendation is included in several policy initiatives: [initiative names separated by comma]. Exemptions will be created on all of them.
If you don't have sufficient permissions on both initiatives, you'll see this message instead:
You have limited permissions to apply the exemption on all the policy initiatives, the exemptions will be created only on the initiatives with sufficient permissions.
Are there any recommendations that don't support exemption?
These generally available recommendations don't support exemption:
- All advanced threat protection types should be enabled in SQL managed instance advanced data security settings
- All advanced threat protection types should be enabled in SQL server advanced data security settings
- Container CPU and memory limits should be enforced
- Container images should be deployed from trusted registries only
- Container with privilege escalation should be avoided
- Containers sharing sensitive host namespaces should be avoided
- Containers should listen on allowed ports only
- Default IP Filter Policy should be Deny
- File integrity monitoring should be enabled on machines
- Immutable (read-only) root filesystem should be enforced for containers
- IoT Devices - Open Ports On Device
- IoT Devices - Permissive firewall policy in one of the chains was found
- IoT Devices - Permissive firewall rule in the input chain was found
- IoT Devices - Permissive firewall rule in the output chain was found
- IP Filter rule large IP range
- Kubernetes clusters should be accessible only over HTTPS
- Kubernetes clusters should disable automounting API credentials
- Kubernetes clusters should not use the default namespace
- Kubernetes clusters should not grant CAPSYSADMIN security capabilities
- Least privileged Linux capabilities should be enforced for containers
- Overriding or disabling of containers AppArmor profile should be restricted
- Privileged containers should be avoided
- Running containers as root user should be avoided
- Services should listen on allowed ports only
- SQL servers should have a Microsoft Entra administrator provisioned
- Usage of host networking and ports should be restricted
- Usage of pod HostPath volume mounts should be restricted to a known list to restrict node access from compromised containers
Are there any limitations to Defender for Cloud's identity and access protections?
There are some limitations to Defender for Cloud's identity and access protections:
- Identity recommendations aren't available for subscriptions with more than 6,000 accounts. In these cases, these types of subscriptions are listed under Not applicable tab.
- Identity recommendations aren't available for Cloud Solution Provider (CSP) partner's admin agents.
- Identity recommendations don't identify accounts that are managed with a privileged identity management (PIM) system. If you're using a PIM tool, you might see inaccurate results in the Manage access and permissions control.
- Identity recommendations don't support Microsoft Entra conditional access policies with included Directory Roles instead of users and groups.
What operating systems for my EC2 instances are supported?
For a list of the AMIs with the SSM Agent preinstalled, see this page in the AWS docs.
For other operating systems, the SSM Agent should be installed manually using the following instructions:
For the CSPM plan, what IAM permissions are needed to discover AWS resources?
The following IAM permissions are needed to discover AWS resources:
| DataCollector | AWS Permissions |
|---|---|
| API Gateway | apigateway:GET |
| Application Auto Scaling | application-autoscaling:Describe* |
| Auto scaling | autoscaling-plans:Describe* autoscaling:Describe* |
| Certificate manager | acm-pca:Describe* acm-pca:List* acm:Describe* acm:List* |
| CloudFormation | cloudformation:Describe* cloudformation:List* |
| CloudFront | cloudfront:DescribeFunction cloudfront:GetDistribution cloudfront:GetDistributionConfig cloudfront:List* |
| CloudTrail | cloudtrail:Describe* cloudtrail:GetEventSelectors cloudtrail:List* cloudtrail:LookupEvents |
| CloudWatch | cloudwatch:Describe* cloudwatch:List* |
| CloudWatch logs | logs:DescribeLogGroups logs:DescribeMetricFilters |
| CodeBuild | codebuild:DescribeCodeCoverages codebuild:DescribeTestCases codebuild:List* |
| Config Service | config:Describe* config:List* |
| DMS - database migration service | dms:Describe* dms:List* |
| DAX | dax:Describe* |
| DynamoDB | dynamodb:Describe* dynamodb:List* |
| Ec2 | ec2:Describe* ec2:GetEbsEncryptionByDefault |
| ECR | ecr:Describe* ecr:List* |
| ECS | ecs:Describe* ecs:List* |
| EFS | elasticfilesystem:Describe* |
| EKS | eks:Describe* eks:List* |
| Elastic Beanstalk | elasticbeanstalk:Describe* elasticbeanstalk:List* |
| ELB - elastic load balancing (v1/2) | elasticloadbalancing:Describe* |
| Elastic search | es:Describe* es:List* |
| EMR - elastic map reduce | elasticmapreduce:Describe* elasticmapreduce:GetBlockPublicAccessConfiguration elasticmapreduce:List* elasticmapreduce:View* |
| GuardDuty | guardduty:DescribeOrganizationConfiguration guardduty:DescribePublishingDestination guardduty:List* |
| IAM | iam:Generate* iam:Get* iam:List* iam:Simulate* |
| KMS | kms:Describe* kms:List* |
| Lambda | lambda:GetPolicy lambda:List* |
| Network firewall | network-firewall:DescribeFirewall network-firewall:DescribeFirewallPolicy network-firewall:DescribeLoggingConfiguration network-firewall:DescribeResourcePolicy network-firewall:DescribeRuleGroup network-firewall:DescribeRuleGroupMetadata network-firewall:ListFirewallPolicies network-firewall:ListFirewalls network-firewall:ListRuleGroups network-firewall:ListTagsForResource |
| RDS | rds:Describe* rds:List* |
| RedShift | redshift:Describe* |
| S3 and S3Control | s3:DescribeJob s3:GetEncryptionConfiguration s3:GetBucketPublicAccessBlock s3:GetBucketTagging s3:GetBucketLogging s3:GetBucketAcl s3:GetBucketLocation s3:GetBucketPolicy s3:GetReplicationConfiguration s3:GetAccountPublicAccessBlock s3:GetObjectAcl s3:GetObjectTagging s3:List* |
| SageMaker | sagemaker:Describe* sagemaker:GetSearchSuggestions sagemaker:List* sagemaker:Search |
| Secret manager | secretsmanager:Describe* secretsmanager:List* |
| Simple notification service SNS | sns:Check* sns:List* |
| SSM | ssm:Describe* ssm:List* |
| SQS | sqs:List* sqs:Receive* |
| STS | sts:GetCallerIdentity |
| WAF | waf-regional:Get* waf-regional:List* waf:List* wafv2:CheckCapacity wafv2:Describe* wafv2:List* |
Is there an API for connecting my GCP resources to Defender for Cloud?
Yes. To create, edit, or delete Defender for Cloud cloud connectors with a REST API, see the details of the Connectors API.
What GCP regions are supported by Defender for Cloud?
Defender for Cloud supports and scans all available regions on GCP public cloud.
Does workflow automation support any business continuity or disaster recovery (BCDR) scenarios?
When preparing your environment for BCDR scenarios, where the target resource is experiencing an outage or other disaster, it's the organization's responsibility to prevent data loss by establishing backups according to the guidelines from Azure Event Hubs, Log Analytics workspace, and Logic Apps.
For every active automation, we recommend you create an identical (disabled) automation and store it in a different location. When there's an outage, you can enable these backup automations and maintain normal operations.
Learn more about Business continuity and disaster recovery for Azure Logic Apps.
What are the costs involved in exporting data?
There's no cost for enabling a continuous export. Costs might be incurred for ingestion and retention of data in your Log Analytics workspace, depending on your configuration there.
Many alerts are only provided when you enabled Defender plans for your resources. A good way to preview the alerts you get in your exported data is to see the alerts shown in Defender for Cloud's pages in the Azure portal.
Learn more about Log Analytics workspace pricing.
Learn more about Azure Event Hubs pricing.
For general information about Defender for Cloud pricing, see the pricing page.
Does the continuous export include data about the current state of all resources?
No. Continuous export is built for streaming of events:
- Alerts received before you enabled export aren't exported.
- Recommendations are sent whenever a resource's compliance state changes. For example, when a resource turns from healthy to unhealthy. Therefore, as with alerts, recommendations for resources that haven't changed state since you enabled export won't be exported.
- Secure score per security control or subscription is sent when a security control's score changes by 0.01 or more.
- Regulatory compliance status is sent when the status of the resource's compliance changes.
Why are recommendations sent at different intervals?
Different recommendations have different compliance evaluation intervals, which can range from every few minutes to every few days. So, the amount of time that it takes for recommendations to appear in your exports varies.
How can I get an example query for a recommendation?
To get an example query for a recommendation, open the recommendation in Defender for Cloud, select Open query, and then select Query returning security findings.

Does continuous export support any business continuity or disaster recovery (BCDR) scenarios?
Continuous export can be helpful in to prepare for BCDR scenarios where the target resource is experiencing an outage or other disaster. However, it's the organization's responsibility to prevent data loss by establishing backups according to the guidelines from Azure Event Hubs, Log Analytics workspace, and Logic App.
Learn more in Azure Event Hubs - Geo-disaster recovery.
Can I programmatically update multiple plans on a single subscription simultaneously?
We don't recommend programmatically updating multiple plans on a single subscription simultaneously (via REST API, ARM templates, scripts, etc.). When using the Microsoft.Security/pricings API, or any other programmatic solution, you should insert a delay of 10-15 seconds between each request.
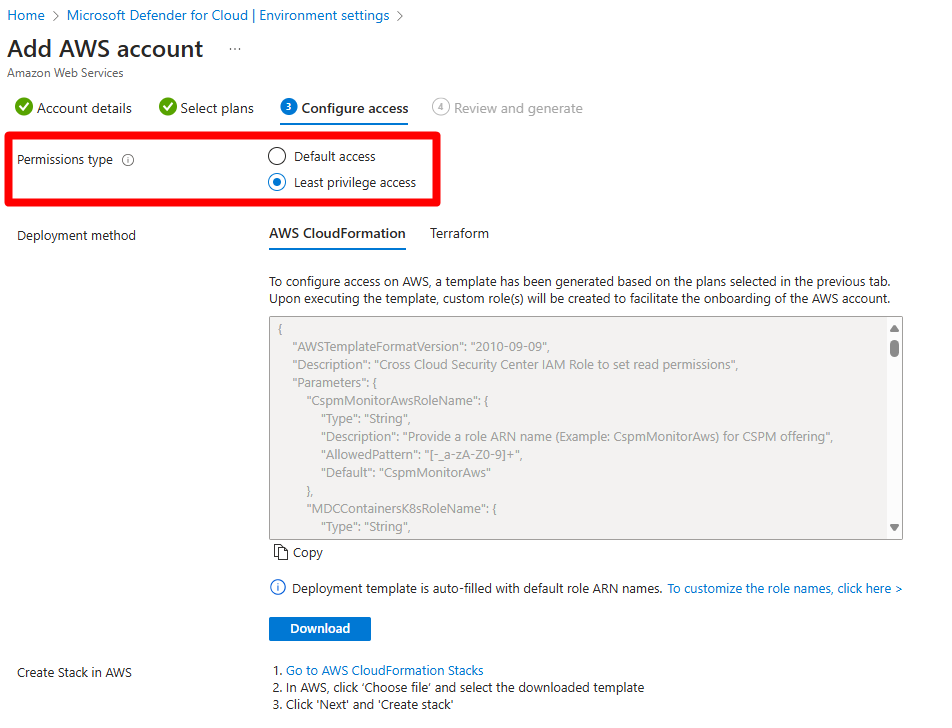
When I enable default access, in which situations do I need to re-run the Cloud Formation template, Cloud Shell script, or Terraform template?
Modifications to Defender for Cloud plans or their options, including features within those plans, necessitate running the deployment template. This applies regardless of the permission type selected during the creation of the security connector. If regions have been changed, as in this screenshot, you don't need to re-run the Cloud Formation template or Cloud Shell script.

When you configure permission types, least privilege access supports features available at the time the template or script was run. New resource types can be supported only by re-running the template or script.
If I change the region or the scan interval for my AWS connector, do I need to re-run the CloudFormation template or Cloud Shell script?
No, if the region or scan interval is changed, there is no need to re-run the CloudFormation template or Cloud Shell script. The changes will be applied automatically.
How does onboarding an AWS organization or management account to Microsoft Defender for Cloud work?
Onboarding an organization or a management account to Microsoft Defender for Cloud initiates the process of deploying a StackSet. The StackSet includes the necessary roles and permissions. The StackSet also propagates the required permissions across all accounts within the organization.
The included permissions allow Microsoft Defender for Cloud to deliver the selected security features through the created connector in Defender for Cloud. The permissions also allow Defender for Cloud to continuously monitor all accounts that might be added using the auto-provisioning service.
Defender for Cloud is capable of identifying the creation of new management accounts and can leverage the granted permissions to automatically provision an equivalent member security connector for each member account.
This feature is available for organizational onboarding only and allows Defender for Cloud to create connectors for newly added accounts. The feature also allows Defender for Cloud to edit all member connectors when the management account is edited, delete all member accounts when the management account is deleted, and remove specific member account if the corresponding account is removed.
A separate stack must be deployed specifically for the management account.