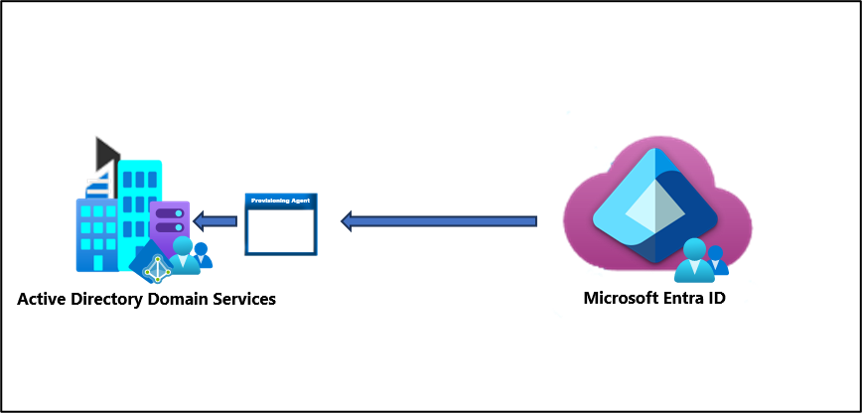
Group writeback with Microsoft Entra Cloud Sync
With the release of provisioning agent 1.1.1370.0, cloud sync now has the ability to perform group writeback. This feature means that cloud sync can provision groups directly to your on-premises Active Directory environment. You can also now use identity governance features to govern access to AD-based applications, such as by including a group in an entitlement management access package.
Important
The public preview of Group Writeback v2 in Microsoft Entra Connect Sync will no longer be available after June 30, 2024. This feature will be discontinued on this date, and you will no longer be supported in Connect Sync to provision cloud security groups to Active Directory. The feature will continue to operate beyond the discontinuation date; however, it will no longer receive support after this date and may cease functioning at any time without notice.
We offer similar functionality in Microsoft Entra Cloud Sync called Group Provision to Active Directory that you can use instead of Group Writeback v2 for provisioning cloud security groups to Active Directory. We're working on enhancing this functionality in Cloud Sync along with other new features that we're developing in Cloud Sync.
Customers who use this preview feature in Connect Sync should switch their configuration from Connect Sync to Cloud Sync. You can choose to move all your hybrid sync to Cloud Sync (if it supports your needs). You can also run Cloud Sync side by side and move only cloud security group provisioning to Active Directory onto Cloud Sync.
For customers who provision Microsoft 365 groups to Active Directory, you can keep using Group Writeback v1 for this capability.
You can evaluate moving exclusively to Cloud Sync by using the user synchronization wizard.
Provision Microsoft Entra ID to Active Directory - Prerequisites
The following prerequisites are required to implement provisioning groups to Active Directory.
License requirements
Using this feature requires Microsoft Entra ID P1 licenses. To find the right license for your requirements, see Compare generally available features of Microsoft Entra ID.
General requirements
- Microsoft Entra account with at least a Hybrid Identity Administrator role.
- On-premises Active Directory Domain Services environment with Windows Server 2016 operating system or later.
- Required for AD Schema attribute - msDS-ExternalDirectoryObjectId
- Provisioning agent with build version 1.1.1370.0 or later.
Note
The permissions to the service account are assigned during clean install only. In case you're upgrading from the previous version then permissions need to be assigned manually using PowerShell cmdlet:
$credential = Get-Credential
Set-AADCloudSyncPermissions -PermissionType UserGroupCreateDelete -TargetDomain "FQDN of domain" -EACredential $credential
If the permissions are set manually, you need to ensure that Read, Write, Create, and Delete all properties for all descendent Groups and User objects.
These permissions aren't applied to AdminSDHolder objects by default Microsoft Entra provisioning agent gMSA PowerShell cmdlets
- The provisioning agent must be able to communicate with one or more domain controllers on ports TCP/389 (LDAP) and TCP/3268 (Global Catalog).
- Required for global catalog lookup to filter out invalid membership references
- Microsoft Entra Connect Sync with build version 2.2.8.0 or later
- Required to support on-premises user membership synchronized using Microsoft Entra Connect Sync
- Required to synchronize AD:user:objectGUID to AAD:user:onPremisesObjectIdentifier
Supported groups and scale limits
The following is supported:
- Only cloud created Security groups are supported
- These groups can have assigned or dynamic membership groups.
- These groups can only contain on-premises synchronized users and / or additional cloud created security groups.
- The on-premises user accounts that are synchronized and are members of this cloud created security group, can be from the same domain or cross-domain, but they all must be from the same forest.
- These groups are written back with the AD groups scope of universal. Your on-premises environment must support the universal group scope.
- Groups that are larger than 50,000 members aren't supported.
- Tenants that have more than 150,000 objects aren't supported. Meaning, if a tenant has any combination of users and groups that exceeds 150K objects, the tenant isn't supported.
- Each direct child nested group counts as one member in the referencing group
- Reconciliation of groups between Microsoft Entra ID and Active Directory isn't supported if the group is manually updated in Active Directory.
Additional information
The following is additional information on provisioning groups to Active Directory.
- Groups provisioned to AD using cloud sync can only contain on-premises synchronized users and / or additional cloud created security groups.
- These users must have the onPremisesObjectIdentifier attribute set on their account.
- The onPremisesObjectIdentifier must match a corresponding objectGUID in the target AD environment.
- An on-premises users objectGUID attribute to a cloud users onPremisesObjectIdentifier attribute can be synchronized using either Microsoft Entra Cloud Sync (1.1.1370.0) or Microsoft Entra Connect Sync (2.2.8.0)
- If you're using Microsoft Entra Connect Sync (2.2.8.0) to synchronize users, instead of Microsoft Entra Cloud Sync, and want to use Provisioning to AD, it must be 2.2.8.0 or later.
- Only regular Microsoft Entra ID tenants are supported for provisioning from Microsoft Entra ID to Active Directory. Tenants such as B2C aren't supported.
- The group provisioning job is scheduled to run every 20 minutes.
Supported scenarios for group writeback with Microsoft Entra Cloud Sync
The following sections describe the supported scenarios for group writeback with Microsoft Entra Cloud Sync.
- Migrate Microsoft Entra Connect Sync group writeback V2 to Microsoft Entra Cloud Sync
- Govern on-premises Active Directory based apps (Kerberos) using Microsoft Entra ID Governance
Migrate Microsoft Entra Connect Sync group writeback V2 to Microsoft Entra Cloud Sync
Scenario: Migrate group writeback using Microsoft Entra Connect Sync (formerly Azure AD Connect) to Microsoft Entra Cloud Sync. This scenario is only for customers who are currently using Microsoft Entra Connect group writeback v2. The process outlined in this document pertains only to cloud-created security groups that are written back with a universal scope. Mail-enabled groups and DLs written back using Microsoft Entra Connect group writeback V1 or V2 aren't supported.
For more information see Migrate Microsoft Entra Connect Sync group writeback V2 to Microsoft Entra Cloud Sync.
Govern on-premises Active Directory based apps (Kerberos) using Microsoft Entra ID Governance
Scenario: Manage on-premises applications with Active Directory groups that are provisioned from and managed in the cloud. Microsoft Entra Cloud Sync allows you to fully govern application assignments in AD while taking advantage of Microsoft Entra ID Governance features to control and remediate any access related requests.
For more information see Govern on-premises Active Directory based apps (Kerberos) using Microsoft Entra ID Governance .