Kommentar
Åtkomst till den här sidan kräver auktorisering. Du kan prova att logga in eller ändra kataloger.
Åtkomst till den här sidan kräver auktorisering. Du kan prova att ändra kataloger.
av Mike Wasson
Ett autentiseringsfilter är en komponent som autentiserar en HTTP-begäran. Webb-API 2 och MVC 5 stöder båda autentiseringsfilter, men de skiljer sig något åt, främst i namngivningskonventionerna för filtergränssnittet. I det här avsnittet beskrivs autentiseringsfilter för webb-API.
Med autentiseringsfilter kan du ange ett autentiseringsschema för enskilda styrenheter eller åtgärder. På så sätt kan din app stödja olika autentiseringsmekanismer för olika HTTP-resurser.
I den här artikeln visar jag kod från exemplet grundläggande autentisering på https://github.com/aspnet/samples. Exemplet visar ett autentiseringsfilter som implementerar HTTP Basic Access Authentication-schemat (RFC 2617). Filtret implementeras i en klass med namnet IdentityBasicAuthenticationAttribute. Jag visar inte all kod från exemplet, bara de delar som illustrerar hur du skriver ett autentiseringsfilter.
Ange ett autentiseringsfilter
Precis som andra filter kan autentiseringsfilter tillämpas per kontrollant, per åtgärd eller globalt på alla webb-API-kontrollanter.
Om du vill använda ett autentiseringsfilter på en kontrollant dekorerar du kontrollantklassen med filterattributet. Följande kod anger [IdentityBasicAuthentication] filtret på en kontrollantklass, vilket möjliggör grundläggande autentisering för alla kontrollantens åtgärder.
[IdentityBasicAuthentication] // Enable Basic authentication for this controller.
[Authorize] // Require authenticated requests.
public class HomeController : ApiController
{
public IHttpActionResult Get() { . . . }
public IHttpActionResult Post() { . . . }
}
Om du vill tillämpa filtret på en åtgärd dekorerar du åtgärden med filtret. Följande kod anger [IdentityBasicAuthentication] filtret på kontrollantens Post metod.
[Authorize] // Require authenticated requests.
public class HomeController : ApiController
{
public IHttpActionResult Get() { . . . }
[IdentityBasicAuthentication] // Enable Basic authentication for this action.
public IHttpActionResult Post() { . . . }
}
Om du vill tillämpa filtret på alla webb-API-kontrollanter lägger du till det i GlobalConfiguration.Filters.
public static class WebApiConfig
{
public static void Register(HttpConfiguration config)
{
config.Filters.Add(new IdentityBasicAuthenticationAttribute());
// Other configuration code not shown...
}
}
Implementera ett webb-API-autentiseringsfilter
I webb-API implementerar autentiseringsfilter gränssnittet System.Web.Http.Filters.IAuthenticationFilter . De bör också ärva från System.Attribute för att kunna användas som attribut.
Gränssnittet IAuthenticationFilter har två metoder:
- AuthenticateAsync autentiserar begäran genom att verifiera autentiseringsuppgifterna i begäran, om den finns.
- ChallengeAsync lägger till en autentiseringsutmaning i HTTP-svaret om det behövs.
Dessa metoder motsvarar det autentiseringsflöde som definierats i RFC 2612 och RFC 2617:
- Klienten skickar autentiseringsuppgifter i auktoriseringshuvudet. Detta inträffar vanligtvis när klienten får ett 401-svar (obehörigt) från servern. En klient kan dock skicka autentiseringsuppgifter med valfri begäran, inte bara efter att ha fått en 401.
- Om servern inte accepterar autentiseringsuppgifterna returneras ett 401-svar (obehörigt). Svaret innehåller en Www-Authenticate rubrik som innehåller en eller flera utmaningar. Varje utmaning anger ett autentiseringsschema som identifieras av servern.
Servern kan också returnera 401 från en anonym begäran. Det är vanligtvis så autentiseringsprocessen initieras:
- Klienten skickar en anonym begäran.
- Servern returnerar 401.
- Klienterna skickar begäran igen med autentiseringsuppgifter.
Det här flödet innehåller både autentiserings- och auktoriseringssteg .
- Autentisering bevisar klientens identitet.
- Auktorisering avgör om klienten kan komma åt en viss resurs.
I webb-API hanterar autentiseringsfilter autentisering, men inte auktorisering. Auktorisering bör utföras av ett auktoriseringsfilter eller inuti kontrollantåtgärden.
Här är flödet i web-API 2-pipelinen:
- Innan du anropar en åtgärd skapar webb-API en lista över autentiseringsfiltren för den åtgärden. Detta inkluderar filter med åtgärdsomfång, kontrollantomfång och globalt omfång.
- Webb-API anropar AuthenticateAsync för varje filter i listan. Varje filter kan verifiera autentiseringsuppgifter i begäran. Om ett filter validerar autentiseringsuppgifterna skapar filtret en IPrincipal och kopplar den till begäran. Ett filter kan också utlösa ett fel i det här läget. I så fall körs inte resten av pipelinen.
- Förutsatt att det inte finns något fel flödar begäran via resten av pipelinen.
- Slutligen anropar webb-API:et varje autentiseringsfilters ChallengeAsync-metod . Filter använder den här metoden för att lägga till en utmaning i svaret om det behövs. Vanligtvis (men inte alltid) så inträffar det som svar på ett 401-fel.
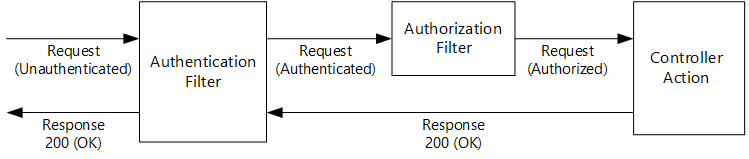
Följande diagram visar två möjliga fall. I det första autentiserar autentiseringsfiltret begäran, ett auktoriseringsfilter auktoriserar begäran och kontrollantåtgärden returnerar 200 (OK).
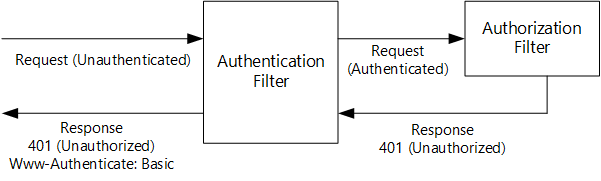
I det andra exemplet autentiserar autentiseringsfiltret begäran, men auktoriseringsfiltret returnerar 401 (Obehörig). I det här fallet anropas inte kontrollantåtgärden. Autentiseringsfiltret lägger till ett Www-Authenticate-huvud i svaret.
Andra kombinationer är möjliga, till exempel om kontrollantåtgärden tillåter anonyma begäranden kan du ha ett autentiseringsfilter men ingen auktorisering.
Implementera metoden AuthenticateAsync
Metoden AuthenticateAsync försöker autentisera begäran. Här är metodsignaturen:
Task AuthenticateAsync(
HttpAuthenticationContext context,
CancellationToken cancellationToken
)
Metoden AuthenticateAsync måste göra något av följande:
- Ingenting (no-op).
- Skapa en IPrincipal och ställ in den på begäran.
- Ange ett felresultat.
Alternativ (1) innebär att begäran inte har några autentiseringsuppgifter som filtret förstår. Alternativ (2) innebär att filtret har autentiserat begäran. Alternativ (3) innebär att begäran hade ogiltiga autentiseringsuppgifter (till exempel fel lösenord), vilket utlöser ett felsvar.
Här är en allmän disposition för implementering av AuthenticateAsync.
- Leta efter autentiseringsuppgifter i begäran.
- Om det inte finns några autentiseringsuppgifter gör du ingenting och returnerar (no-op).
- Om det finns autentiseringsuppgifter men filtret inte känner igen autentiseringsschemat gör du ingenting och returnerar (no-op). Ett annat filter i pipelinen kan förstå schemat.
- Om det finns autentiseringsuppgifter som filtret förstår kan du försöka autentisera dem.
- Om autentiseringsuppgifterna är felaktiga returnerar du 401 genom att ange
context.ErrorResult. - Om autentiseringsuppgifterna är giltiga skapar du en IPrincipal och anger
context.Principal.
Följande kod visar metoden AuthenticateAsync från exemplet med grundläggande autentisering . Kommentarerna anger varje steg. Koden visar flera typer av fel: Ett auktoriseringshuvud utan autentiseringsuppgifter, felaktiga autentiseringsuppgifter och felaktigt användarnamn/lösenord.
public async Task AuthenticateAsync(HttpAuthenticationContext context, CancellationToken cancellationToken)
{
// 1. Look for credentials in the request.
HttpRequestMessage request = context.Request;
AuthenticationHeaderValue authorization = request.Headers.Authorization;
// 2. If there are no credentials, do nothing.
if (authorization == null)
{
return;
}
// 3. If there are credentials but the filter does not recognize the
// authentication scheme, do nothing.
if (authorization.Scheme != "Basic")
{
return;
}
// 4. If there are credentials that the filter understands, try to validate them.
// 5. If the credentials are bad, set the error result.
if (String.IsNullOrEmpty(authorization.Parameter))
{
context.ErrorResult = new AuthenticationFailureResult("Missing credentials", request);
return;
}
Tuple<string, string> userNameAndPassword = ExtractUserNameAndPassword(authorization.Parameter);
if (userNameAndPassword == null)
{
context.ErrorResult = new AuthenticationFailureResult("Invalid credentials", request);
}
string userName = userNameAndPassword.Item1;
string password = userNameAndPassword.Item2;
IPrincipal principal = await AuthenticateAsync(userName, password, cancellationToken);
if (principal == null)
{
context.ErrorResult = new AuthenticationFailureResult("Invalid username or password", request);
}
// 6. If the credentials are valid, set principal.
else
{
context.Principal = principal;
}
}
Ställ in ett felresultat
Om autentiseringsuppgifterna är ogiltiga måste filtret ställa in context.ErrorResult till en IHttpActionResult som skapar ett felsvar. Mer information om IHttpActionResult finnsi Åtgärdsresultat i webb-API 2.
Exempel på grundläggande autentisering innehåller en AuthenticationFailureResult klass som är lämplig för det här ändamålet.
public class AuthenticationFailureResult : IHttpActionResult
{
public AuthenticationFailureResult(string reasonPhrase, HttpRequestMessage request)
{
ReasonPhrase = reasonPhrase;
Request = request;
}
public string ReasonPhrase { get; private set; }
public HttpRequestMessage Request { get; private set; }
public Task<HttpResponseMessage> ExecuteAsync(CancellationToken cancellationToken)
{
return Task.FromResult(Execute());
}
private HttpResponseMessage Execute()
{
HttpResponseMessage response = new HttpResponseMessage(HttpStatusCode.Unauthorized);
response.RequestMessage = Request;
response.ReasonPhrase = ReasonPhrase;
return response;
}
}
Implementera ChallengeAsync
Syftet med metoden ChallengeAsync är att lägga till autentiseringsutmaningar i svaret om det behövs. Här är metodsignaturen:
Task ChallengeAsync(
HttpAuthenticationChallengeContext context,
CancellationToken cancellationToken
)
Metoden anropas för varje autentiseringsfilter i begärandepipelinen.
Det är viktigt att förstå att ChallengeAsync anropas innan HTTP-svaret skapas, och eventuellt även innan kontrollantåtgärden körs. När ChallengeAsync anropas context.Result innehåller en IHttpActionResult, som används senare för att skapa HTTP-svaret. Så när ChallengeAsync anropas vet du ingenting om HTTP-svaret än.
Metoden ChallengeAsync bör ersätta det ursprungliga värdet context.Result för med en ny IHttpActionResult. Denna IHttpActionResult måste omsluta det ursprungliga context.Result.
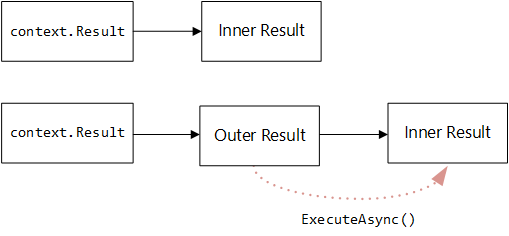
Jag anropar det ursprungliga IHttpActionResult det inre resultatet och det nya IHttpActionResult det yttre resultatet. Det yttre resultatet måste göra följande:
- Anropa det inre resultatet för att skapa HTTP-svaret.
- Granska svaret.
- Lägg till en autentiseringsutmaning i svaret om det behövs.
Följande exempel är hämtat från exemplet med grundläggande autentisering. Den definierar en IHttpActionResult för det yttre resultatet.
public class AddChallengeOnUnauthorizedResult : IHttpActionResult
{
public AddChallengeOnUnauthorizedResult(AuthenticationHeaderValue challenge, IHttpActionResult innerResult)
{
Challenge = challenge;
InnerResult = innerResult;
}
public AuthenticationHeaderValue Challenge { get; private set; }
public IHttpActionResult InnerResult { get; private set; }
public async Task<HttpResponseMessage> ExecuteAsync(CancellationToken cancellationToken)
{
HttpResponseMessage response = await InnerResult.ExecuteAsync(cancellationToken);
if (response.StatusCode == HttpStatusCode.Unauthorized)
{
// Only add one challenge per authentication scheme.
if (!response.Headers.WwwAuthenticate.Any((h) => h.Scheme == Challenge.Scheme))
{
response.Headers.WwwAuthenticate.Add(Challenge);
}
}
return response;
}
}
Egenskapen InnerResult innehåller den inre IHttpActionResult. Egenskapen Challenge representerar ett Www-Authentication-huvud. Observera att ExecuteAsync först anropar InnerResult.ExecuteAsync för att skapa HTTP-svaret och lägger sedan till utmaningen om det behövs.
Kontrollera svarskoden innan du lägger till utmaningen. De flesta autentiseringsscheman lägger bara till en utmaning om svaret är 401, vilket visas här. Vissa autentiseringsscheman lägger dock till en utmaning i ett lyckat svar. Se till exempel Negotiate (RFC 4559).
Med tanke på AddChallengeOnUnauthorizedResult klassen är den faktiska koden i ChallengeAsync enkel. Du skapar bara resultatet och kopplar det till context.Result.
public Task ChallengeAsync(HttpAuthenticationChallengeContext context, CancellationToken cancellationToken)
{
var challenge = new AuthenticationHeaderValue("Basic");
context.Result = new AddChallengeOnUnauthorizedResult(challenge, context.Result);
return Task.FromResult(0);
}
Obs! Exempel på grundläggande autentisering abstraherar den här logiken lite genom att placera den i en tilläggsmetod.
Kombinera autentiseringsfilter med Host-Level-autentisering
"Autentisering på värdnivå" är autentisering som utförs av värden (till exempel IIS) innan begäran når webb-API-ramverket.
Ofta kanske du vill aktivera autentisering på värdnivå för resten av programmet, men inaktivera det för dina webb-API-kontrollanter. Ett vanligt scenario är till exempel att aktivera formulärautentisering på värdnivå, men använda tokenbaserad autentisering för webb-API.
Om du vill inaktivera autentisering på värdnivå i webb-API-pipelinen, anropa config.SuppressHostPrincipal() i din konfiguration. Detta gör att webb-API:et tar bort IPrincipal från alla begäranden som går in i webb-API-pipelinen. I själva verket ogiltigförklarar det begärans autentisering.
public static class WebApiConfig
{
public static void Register(HttpConfiguration config)
{
config.SuppressHostPrincipal();
// Other configuration code not shown...
}
}
Ytterligare resurser
ASP.NET Säkerhetsfilter för webb-API (MSDN Magazine)