Link a variable group to secrets in Azure Key Vault
This article shows you how to create a variable group that links to secrets stored in an Azure key vault. By linking the variable group to the key vault, you can ensure that your secrets are stored securely and your pipelines always have access to the latest secret values at runtime.
Azure DevOps Services | Azure DevOps Server 2022 - Azure DevOps Server 2019
You can create a variable group that links to existing Azure key vaults and maps selected key vault secrets to the variable group. Only the secret names are mapped to the variable group, not the secret values. When pipelines run, they link to the variable group to fetch the latest secret values from the vault at runtime.
Any changes made to existing secrets in the key vault are automatically available to all the pipelines that use the variable group. However, if secrets are added to or deleted from the vault, the associated variable groups don't automatically update. You must explicitly update the secrets to include in the variable group.
Although Key Vault supports storing and managing cryptographic keys and certificates in Azure, Azure Pipelines variable group integration only supports mapping key vault secrets. Cryptographic keys and certificates aren't supported.
Note
Key vaults that use Azure role-based access control (Azure RBAC) aren't supported.
Prerequisites
- An Azure account with an active subscription. Create an account for free.
- An Azure DevOps organization. Sign up for free or an Azure DevOps Server.
- A DevOps project. Create a project if you don't already have one.
- An Azure Resource Manager service connection for your project.
Create a key vault
Create an Azure key vault.
- In the Azure portal, select Create a resource.
- Search for and select Key Vault, then select Create.
- Select your subscription.
- Select an existing resource group or create a new one.
- Enter a name for the key vault.
- Select a region.
- Select the Access and configuration tab.
- Select Vault access policy.
- Select your account as the principal.
- Select Review + create and then Create.
Create the variable group linked to the key vault
- In your Azure DevOps project, select Pipelines > Library > + Variable group.
- On the Variable groups page, enter a name and optional description for the variable group.
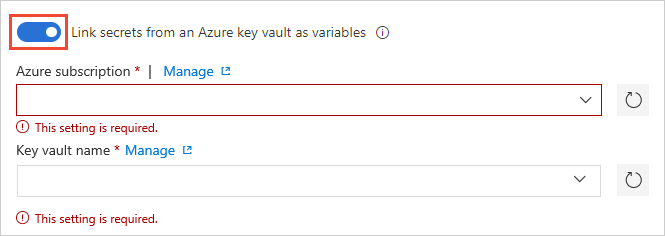
- Enable the Link secrets from an Azure key vault as variables toggle.
- Select your service connection and select Authorize.
- Select your key vault name and enable Azure DevOps to access the key vault by selecting Authorize next to the vault name.
- Select + Add and on the Choose secrets screen, select the secrets from your vault for mapping to this variable group, then select OK.
- Select Save to save the secret variable group.
Note
Your service connection must have at least Get and List permissions on the key vault, which you can authorize in the preceding steps. You can also provide these permissions from the Azure portal by following these steps:
- Open Settings for the key vault, and then choose Access configuration > Go to access policies.
- On the Access policies page, if your Azure Pipelines project isn't listed under Applications with at least Get and List permissions, select Create.
- Under Secret permissions, select Get and List, and then select Next.
- Select your principal, and then select Next.
- Select Next again, review the settings, and then select Create.
For more information, see Use Azure Key Vault secrets.