Authenticate your API and connector with Microsoft Entra ID
Azure Resource Manager enables you to manage the components of a solution on Azure—components like databases, virtual machines, and web apps. This tutorial demonstrates how to enable authentication in Microsoft Entra ID, register one of the Resource Manager APIs as a custom connector, and then connect to it in Power Automate. You can also create the custom connector for Power Apps or Azure Logic Apps.
The process you follow in this tutorial can be used to access any RESTful API that's authenticated by using Microsoft Entra ID.
Prerequisites
- An Azure subscription
- A Power Automate account
- A sample OpenAPI file
Enable authentication in Microsoft Entra ID
First, you create a Microsoft Entra ID application that performs the authentication when calling the Resource Manager API endpoint.
Sign in to the Azure portal. If you have more than one Microsoft Entra ID tenant, make sure you're signed in to the correct directory by verifying that your user name appears in the upper-right corner.
On the left pane, select All services. In the Filter box, enter Azure Active Directory, and then select Azure Active Directory.
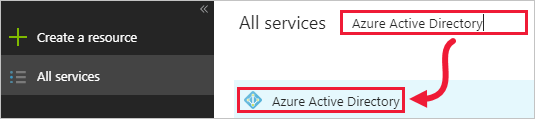
The Azure Active Directory blade opens.
On the left pane of the Azure Active Directory blade, select App registrations.
In the list of registered applications, select New application registration.
Enter a name for your application, and leave Application Type as Web app / API. For Sign-on URL, enter an appropriate value for your organization, such as
https://login.windows.net. Select Create.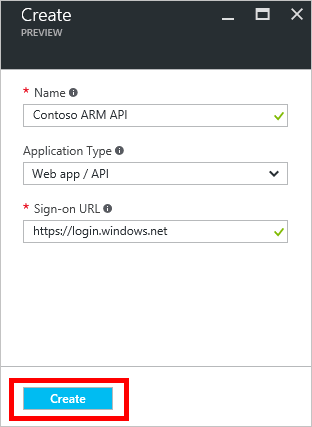
Copy the Application ID, because you need it later.
The Settings blade should also open. If it doesn't, select Settings.

On the left pane of the Settings blade, select Required permissions. On the Required permissions blade, select Add.
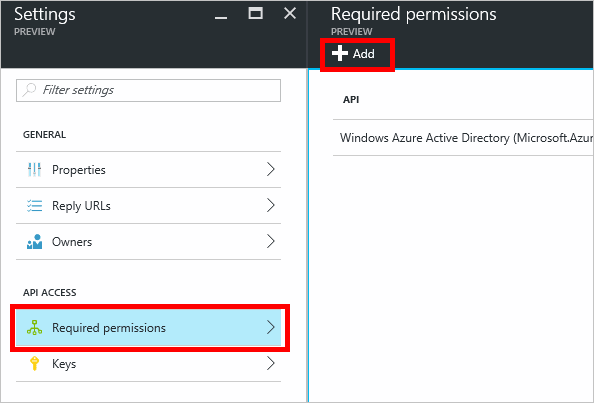
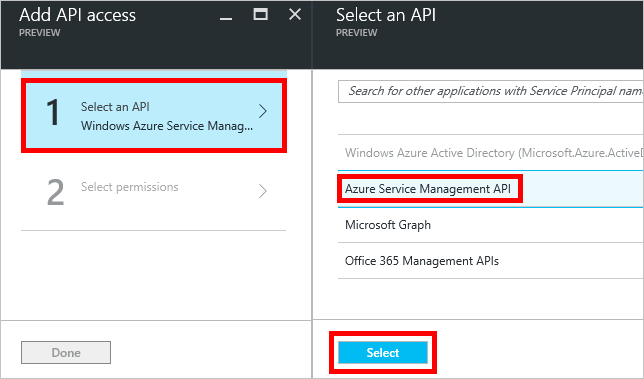
The Add API access blade opens.
On the Add API access blade, select Select an API, and then select Azure Service Management API > Select.
Under Delegated permissions, select Access Azure Service Management as organization users > Select.
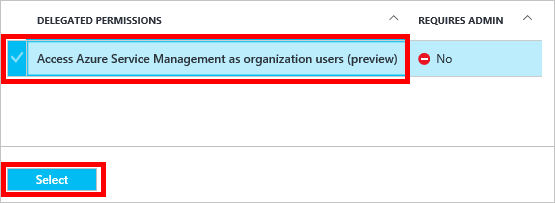
On the Add API access blade, select Done.
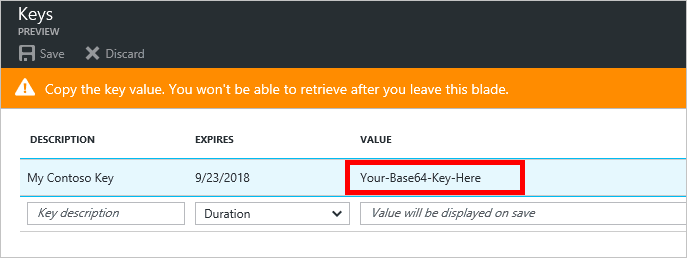
Back on the Settings blade, select Keys. On the Keys blade, enter a description for your key, select an expiration period, and then select Save.
Your new key is displayed. Copy the key value, because you need it later.
There's one more step to complete in the Azure portal, but first you create a custom connector.
Create a custom connector
Now that the Microsoft Entra ID application is configured, you create the custom connector.
In the Power Automate web app, select Settings (the gear icon) in the upper-right corner of the page, and then select Custom Connectors.
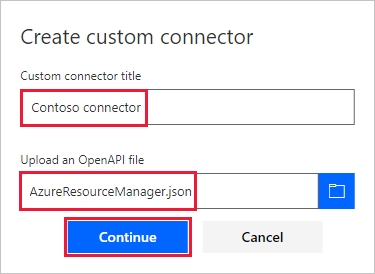
Select Create custom connector > Import an OpenAPI file.
Enter a name for the connector, browse to your sample OpenAPI file, and then select Continue.
The General page opens. Leave the default values as they appear, and then select the Security page.
On the Security page, enter Microsoft Entra ID information for the application:
Under Client id, enter the Microsoft Entra ID application ID value you copied earlier.
For Client secret, use the value you copied earlier.
For Resource URL, enter
https://management.core.windows.net/. Be sure to include the resource URL exactly as written, including the trailing slash.
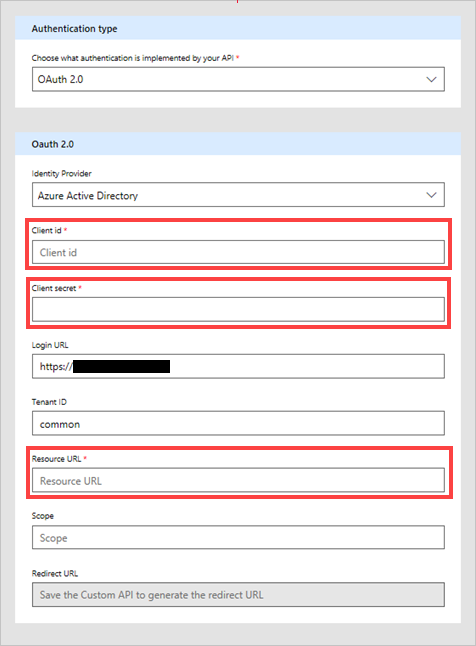
After entering security information, select the check mark (✓) next to the flow name at the top of the page to create the custom connector.
On the Security page, the Redirect URL field is now populated. Copy this URL so you can use it in the next section of this tutorial.
Your custom connector is now displayed under Custom Connectors.

Now that the custom connector is registered, create a connection to the custom connector so that it can be used in your apps and flows. Select the plus sign (+) to the right of the name of your custom connector, and then complete the sign-in screen.
Note
The sample OpenAPI doesn't define the full set of Resource Manager operations; currently, it only contains the List all subscriptions operation. You can edit this OpenAPI file, or create another OpenAPI file by using the online OpenAPI editor.
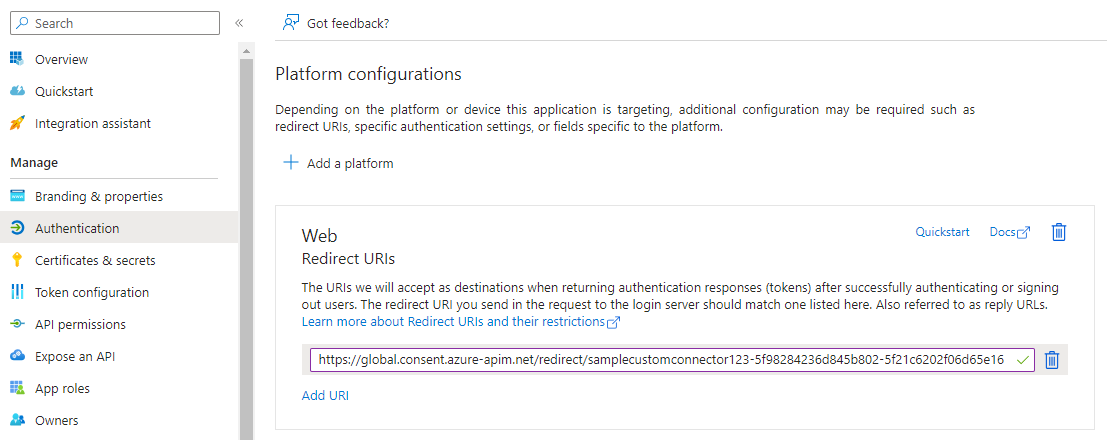
Set the reply URL in Azure
Select Azure Active Directory (Microsoft Entra ID), then select your app. Select Authentication from left menu, then select Add URI. Add the value you copied from the Redirect URI field in the custom connector—for example, https://global.consent.azure-apim.net/redirect/samplecustomconnector123-5f98284236d845b802-5f21c6202f06d65e16—and then select Save.
Related information
Use custom connectors in Power Automate.
To ask questions or make comments about custom connectors, join our community.
Provide feedback
We greatly appreciate feedback on issues with our connector platform, or new feature ideas. To provide feedback, go to Submit issues or get help with connectors and select your feedback type.