The benefits might not be immediately apparent but lets address this question:
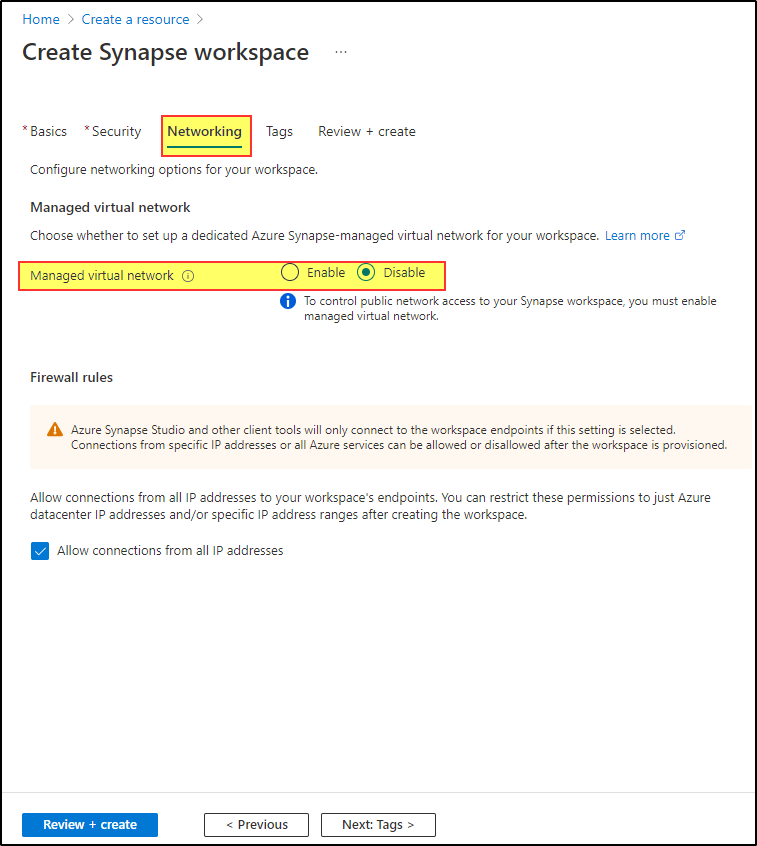
But then my question is: wouldn't you get the same security if you create a Synapse workspace (without managed VNet) and (1) remove all IPs in networking settings, (2) disable public network access and (3) add private endpoints for your sql/sqlpool/dev in whatever VNet your users are on.
- The IP range has a specific function. It controls the access to the workspace itself not data ingress. You can limit the IP range and then connect to data from anywhere
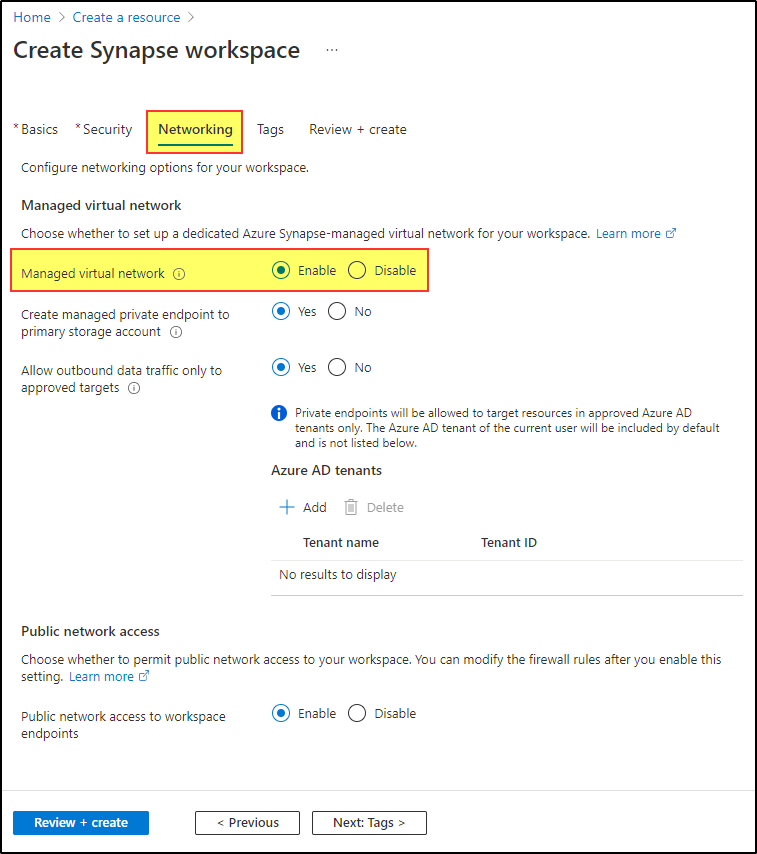
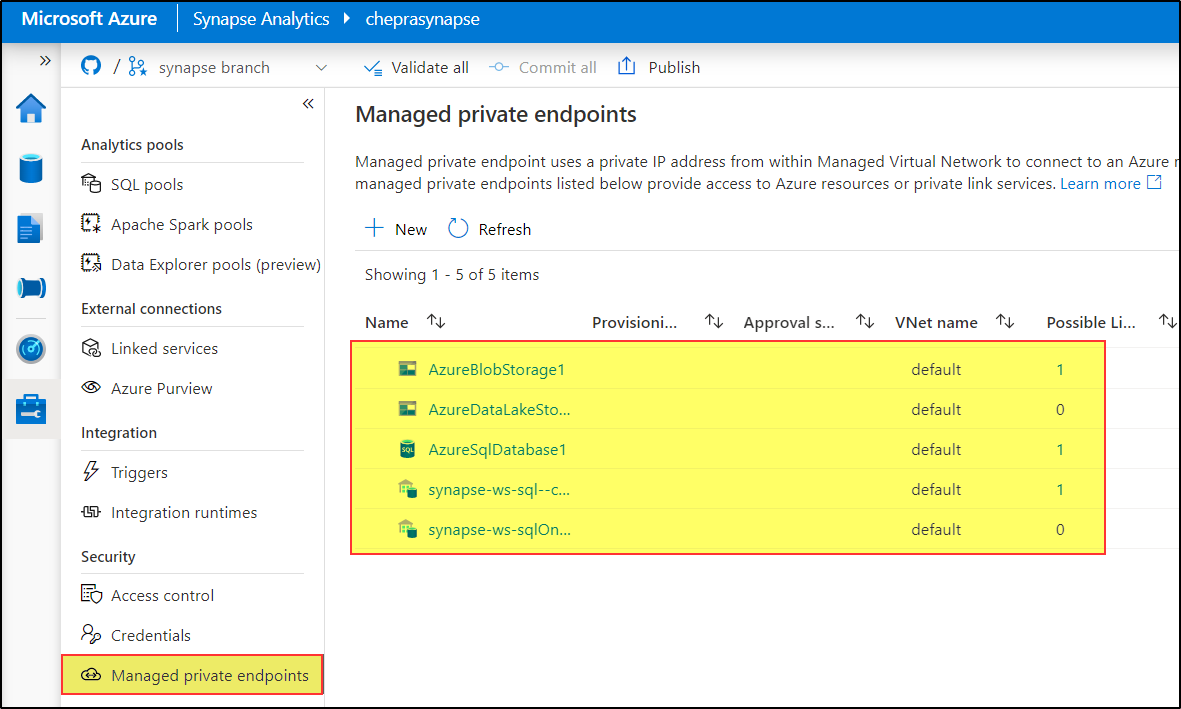
- The Managed VNET restricts the sources from which you can ingest data to the workspace so only sources which can sit behind a Managed Private Endpoint can be consumed. Side Notes
a) On-premise sources using a selfhosted IR are not protected by an private endpoint - I assume the SelfHosted IR is considered inside the Managed VNET and is secure
b) I've really struggled /failed to get other sources connected (REST, Office 365) and can't find much documentation for it. - Exfiltration Protection protects where you can save data to so protects the other way.
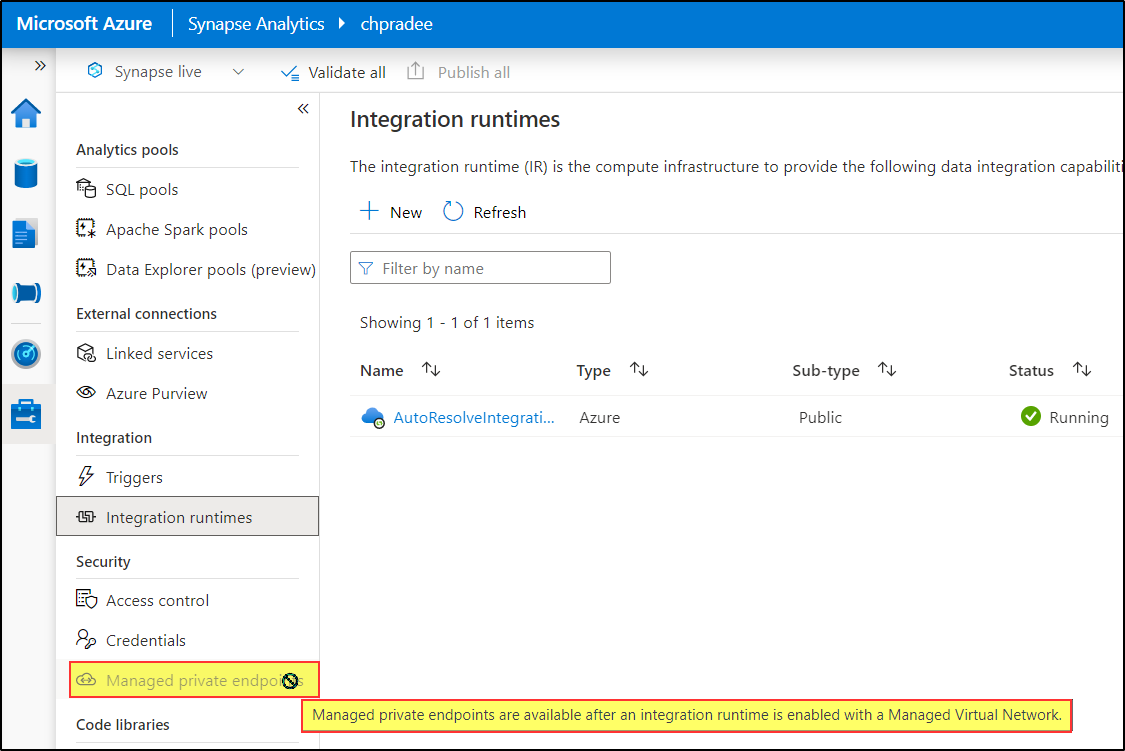
- Disabling Public network access can only be enabled if a Managed VNET is in place. The same is true Data Exfiltration.
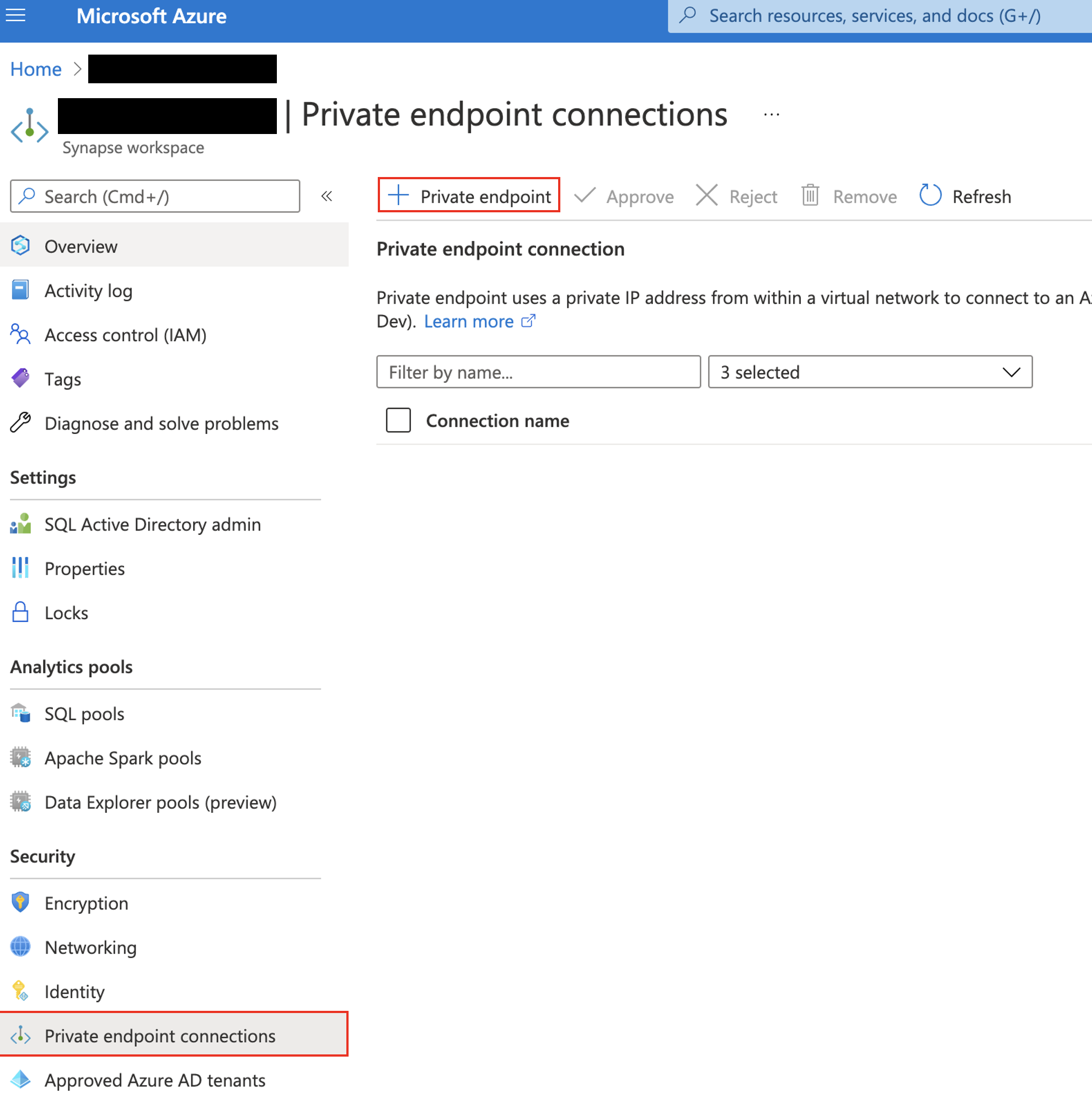
- Private End Points in your VNET only allow for private access to the Workspace and resources they do not enforce them, the documentation states
Alternatively, you can connect to your workspace using a managed private endpoint and private Link. Azure Synapse workspaces without the Azure Synapse Analytics Managed Virtual Network do not have the ability to connect via managed private endpoints."
So your hypothesis would not provide the protection that a Managed VNET would. Hope this clears up the specifics if not the more general question of "what's the point?".


 or upvote
or upvote  button whenever the information provided helps you. Original posters help the community find answers faster by identifying the correct answer. Here is
button whenever the information provided helps you. Original posters help the community find answers faster by identifying the correct answer. Here is