Configure OpenVPN client for P2S certificate authentication connections - Linux
This article helps you connect to your Azure virtual network (VNet) using VPN Gateway point-to-site (P2S) and Certificate authentication from Linux using an OpenVPN client.
Before you begin
Verify that you are on the correct article. The following table shows the configuration articles available for Azure VPN Gateway P2S VPN clients. Steps differ, depending on the authentication type, tunnel type, and the client OS.
| Authentication | Tunnel type | Client OS | VPN client |
|---|---|---|---|
| Certificate | |||
| IKEv2, SSTP | Windows | Native VPN client | |
| IKEv2 | macOS | Native VPN client | |
| IKEv2 | Linux | strongSwan | |
| OpenVPN | Windows | Azure VPN client OpenVPN client version 2.x OpenVPN client version 3.x |
|
| OpenVPN | macOS | OpenVPN client | |
| OpenVPN | iOS | OpenVPN client | |
| OpenVPN | Linux | Azure VPN Client OpenVPN client |
|
| Microsoft Entra ID | |||
| OpenVPN | Windows | Azure VPN client | |
| OpenVPN | macOS | Azure VPN Client | |
| OpenVPN | Linux | Azure VPN Client |
Prerequisites
This article assumes that you've already performed the following prerequisites:
- You created and configured your VPN gateway for point-to-site certificate authentication and the OpenVPN tunnel type. See Configure server settings for P2S VPN Gateway connections - certificate authentication for steps.
- You generated and downloaded the VPN client configuration files. See Generate VPN client profile configuration files for steps.
- You can either generate client certificates, or acquire the appropriate client certificates necessary for authentication.
Connection requirements
To connect to Azure using the OpenVPN client using certificate authentication, each connecting client requires the following items:
- The Open VPN Client software must be installed and configured on each client.
- The client must have the correct certificates installed locally.
Workflow
The workflow for this article is:
- Install the OpenVPN client.
- View the VPN client profile configuration files contained in the VPN client profile configuration package that you generated.
- Configure the OpenVPN client.
- Connect to Azure.
About certificates
For certificate authentication, a client certificate must be installed on each client computer. The client certificate you want to use must be exported with the private key, and must contain all certificates in the certification path. Additionally, for some configurations, you'll also need to install root certificate information.
The OpenVPN client in this article uses certificates exported with a .pfx format. You can export a client certificate easily to this format using the Windows instructions. See Export a client certificate - pfx. If you don't have a Windows computer, as a workaround, you can use a small Windows VM to export certificates to the needed .pfx format. At this time, the OpenSSL Linux instructions we provide only result in the .pem format.
Configuration steps
This section helps you configure Linux clients for certificate authentication that uses the OpenVPN tunnel type. To connect to Azure, download the OpenVPN client and configure the connection profile.
Note
OpenVPN Client version 2.6 is not yet supported.
Open a new Terminal session. You can open a new session by pressing 'Ctrl + Alt + t' at the same time.
Enter the following command to install needed components:
sudo apt-get install openvpn sudo apt-get -y install network-manager-openvpn sudo service network-manager restartNext, go to the VPN client profile folder and unzip to view the files.
Export the P2S client certificate you created and uploaded to your P2S configuration on the gateway. For steps, see VPN Gateway point-to-site.
Extract the private key and the base64 thumbprint from the .pfx. There are multiple ways to do this. Using OpenSSL on your computer is one way.
openssl pkcs12 -in "filename.pfx" -nodes -out "profileinfo.txt"The profileinfo.txt file contains the private key and the thumbprint for the CA, and the Client certificate. Be sure to use the thumbprint of the client certificate.
Open profileinfo.txt in a text editor. To get the thumbprint of the client (child) certificate, select the text including and between "-----BEGIN CERTIFICATE-----" and "-----END CERTIFICATE-----" for the child certificate and copy it. You can identify the child certificate by looking at the subject=/ line.
Open the vpnconfig.ovpn file and find the section in the following example. Replace everything between "cert" and "/cert".
# P2S client certificate # please fill this field with a PEM formatted cert <cert> $CLIENTCERTIFICATE </cert>Open the profileinfo.txt in a text editor. To get the private key, select the text including and between "-----BEGIN PRIVATE KEY-----" and "-----END PRIVATE KEY-----" and copy it.
Open the vpnconfig.ovpn file in a text editor and find this section. Paste the private key replacing everything between "key" and "/key".
# P2S client root certificate private key # please fill this field with a PEM formatted key <key> $PRIVATEKEY </key>Don't change any other fields. Use the filled in configuration in client input to connect to the VPN.
To connect using the command line, type the following command:
sudo openvpn --config <name and path of your VPN profile file>&To disconnect using command line, type the following command:
sudo pkill openvpnTo connect using the GUI, go to system settings.
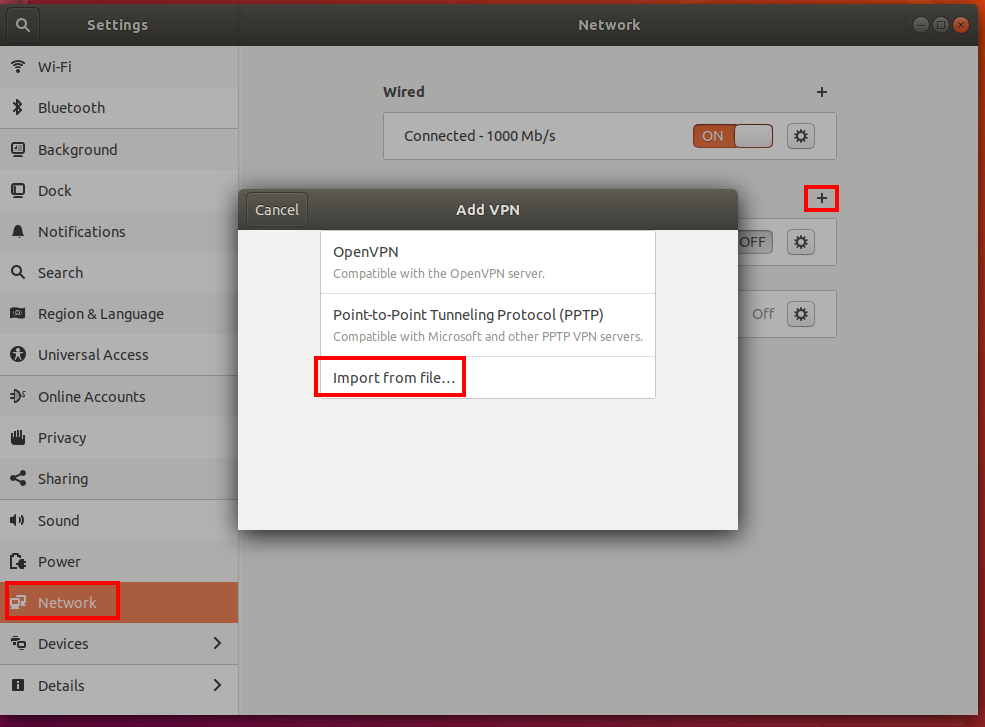
Select + to add a new VPN connection.
Under Add VPN, pick Import from file….
Browse to the profile file and double-click or pick Open.
Select Add on the Add VPN window.
You can connect by turning the VPN ON on the Network Settings page, or under the network icon in the system tray.
Next steps
For additional steps, return to the P2S Azure portal article.