Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
With at least the permissions of a SharePoint Administrator in Microsoft 365, you can block or limit access to SharePoint and OneDrive content from unmanaged devices (those not hybrid AD joined or compliant in Intune). You can block or limit access for:
All users in the organization or only some users or security groups.
All sites in the organization or only some sites.
What happens when access is blocked or limited?
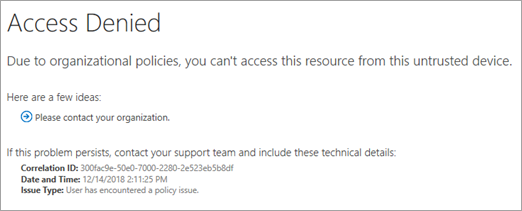
Blocking access helps provide security but comes at the cost of usability and productivity. When access is blocked, users see the following error:
Access Denied. Due to organization policy, you can't access this resource from this untrusted device.
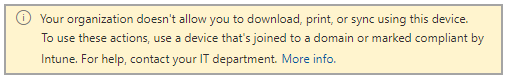
Limiting access allows users to remain productive while addressing the risk of accidental data loss on unmanaged devices. When you limit access, users on managed devices have full access (unless they use one of the browser and operating system combinations listed in Supported browsers). Users on unmanaged devices have browser-only access with no ability to download, print, or sync files. They also won't be able to access content through apps, including the Microsoft Office desktop apps. When you limit access, you can choose to allow or block editing files in the browser. When web access is limited, users see the following message at the top of sites.
Note
- Blocking or limiting access on unmanaged devices relies on Microsoft Entra Conditional Access policies. Learn about Microsoft Entra ID licensing For an overview of conditional access in Microsoft Entra ID, see Conditional access in Microsoft Entra ID.
- For info about recommended SharePoint access policies, see Policy recommendations for securing SharePoint sites and files.
- If you limit access on unmanaged devices, users on managed devices must use one of the supported OS and browser combinations, or they will also have limited access.
- Because Microsoft Entra ID doesn't offer Multi-Geo Capabilities, blocking or limiting unmanaged devices impact all Geos within the Microsoft 365 tenant.
How do I control device access across Microsoft 365?
The procedures in this article only affect SharePoint access by unmanaged devices. If you want to expand control of unmanaged devices beyond SharePoint, you can Create a Microsoft Entra Conditional Access policy for all apps and services in your organization instead. To configure this policy specifically for Microsoft 365 services, select the Office 365 cloud app under Cloud apps or actions.
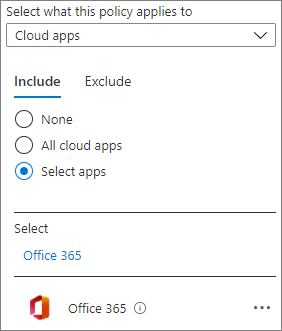
Using a policy that affects all Microsoft 365 services can lead to better security and a better experience for your users. For example, when you block access to unmanaged devices in SharePoint only, users can access the chat in a team with an unmanaged device, but will lose access when they try to access the Files tab. Using the Office 365 cloud app helps avoid issues with service dependencies.
How do I block access?
Go to Access control in the new SharePoint admin center, and sign in with an account that has admin permissions for your organization.
Note
If you have Office 365 operated by 21Vianet (China), sign in to the Microsoft 365 admin center, then browse to the SharePoint admin center and open the Access control page.
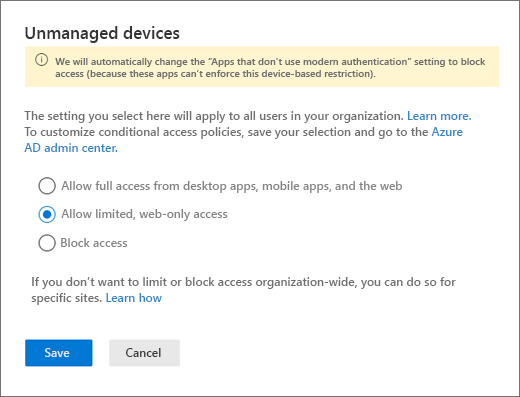
Select Unmanaged devices.
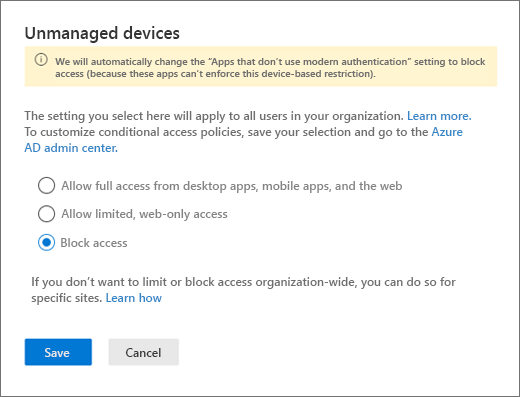
Select Block access, and then select Save.
Important
- Selecting this option disables any previous conditional access policies you created from this page, and creates a new conditional access policy that applies to all users. Any customizations you made to previous policies won't be carried over.
- It can take up to 24 hours for the policy to take effect. It won't take effect for users who are already signed in from unmanaged devices.
- If you block access from unmanaged devices, we recommend also blocking access from apps that don't use modern authentication. Some third-party apps and versions of Office prior to Office 2013 don't use modern authentication and can't enforce device-based restrictions. This means they allow users to bypass conditional access policies that you configure in Azure. In Access control in the new SharePoint admin center, select Apps that don't use modern authentication, select Block access, and then select Save.
How do I limit access?
Go to Access control in the new SharePoint admin center, and sign in with an account that has admin permissions for your organization.
Note
If you have Office 365 operated by 21Vianet (China), sign in to the Microsoft 365 admin center, then browse to the SharePoint admin center and select Policies to expand, then select Access Control.
Select Unmanaged devices.
Select Allow limited, web-only access, and then select Save. (Note that selecting this option disables any previous conditional access policies you created from this page and create a new conditional access policy that applies to all users. Any customizations you made to previous policies won't be carried over.)
If you revert back to Allow Full Access, it could take up to 24 hours for the changes to take effect.
Important
- If you limit access from unmanaged devices, we recommend also blocking access from apps that don't use modern authentication. Some third-party apps and versions of Office prior to Office 2013 don't use modern authentication and can't enforce device-based restrictions. This means they allow users to bypass conditional access policies that you configure in Azure. In Access control in the new SharePoint admin center, select Apps that don't use modern authentication, select Block access, and then select Save.
- If you limit access and edit a site from an unmanaged device, image web parts won't display images that you upload to the site assets library or directly to the web part. To work around this issue, you can use this SPList API to exempt the block download policy on the site assets library. This allows the web part to download images from the site assets library.
- When Access Control for Unmanaged Devices in SharePoint is set to Allow limited, web-only access, SharePoint files can't be downloaded but they can be previewed. The previews of Office files work in SharePoint but the previews don't work in Microsoft Viva Engage.
How do I limit access using PowerShell?
Download the latest SharePoint Online Management Shell.
Note
If you installed a previous version of the SharePoint Online Management Shell, go to Add or remove programs, and uninstall SharePoint Online Management Shell.
Connect to SharePoint with at least the permissions of a SharePoint Administrator in Microsoft 365. To learn how, see Getting started with SharePoint Online Management Shell.
Run the following command:
Set-SPOTenant -ConditionalAccessPolicy AllowLimitedAccessNote
By default, this policy allows users to view and edit files in their web browser. To change this, see Advanced configurations.
How do I block or limit access to a specific SharePoint site or OneDrive?
To block or limit access to specific sites, follow these steps. If you have configured the organization-wide policy, the site-level setting you specify must be at least as restrictive as the organization-level setting.
Manually create a policy in the Microsoft Entra admin center by following the steps in Use app-enforced restrictions.
Set the site-level setting by using PowerShell, or a sensitivity label:
To use PowerShell, continue to the next step.
To use a sensitivity label, see the following instructions and specify the label setting for Access from unmanaged devices: Use sensitivity labels to protect content in Microsoft Teams, Microsoft 365 groups, and SharePoint sites.
To use PowerShell: Download the latest SharePoint Online Management Shell.
Note
If you installed a previous version of the SharePoint Online Management Shell, go to Add or remove programs and uninstall SharePoint Online Management Shell.
Connect to SharePoint with at least the permissions of a SharePoint Administrator in Microsoft 365. To learn how, see Getting started with SharePoint Online Management Shell.
Run one of the following commands.
To block access to a single site:
Set-SPOSite -Identity https://<SharePoint online URL>/sites/<name of site or OneDrive account> -ConditionalAccessPolicy BlockAccessTo limit access to a single site:
Set-SPOSite -Identity https://<SharePoint online URL>/sites/<name of site or OneDrive account> -ConditionalAccessPolicy AllowLimitedAccessTo update multiple sites at once, use the following command as an example:
Get-SPOSite -IncludePersonalSite $true -Limit all -Filter "Url -like '-my.sharepoint.com/personal/'" | Set-SPOSite -ConditionalAccessPolicy AllowLimitedAccessThis example gets the OneDrive for every user and passes it as an array to Set-SPOSite to limit access.
Note
By default, a setting that includes web access allows users to view and edit files in their web browser. To change this, see Advanced configurations.
What are the advanced configurations for limiting access?
You can use the following parameters with -ConditionalAccessPolicy AllowLimitedAccess for both the organization-wide setting and the site-level setting:
-AllowEditing $false Prevents users from editing Office files in the browser.
-ReadOnlyForUnmanagedDevices $true Makes the entire site read-only for impacted users.
-LimitedAccessFileType OfficeOnlineFilesOnly Allows users to preview only Office files in the browser. This option increases security but may be a barrier to user productivity.
-LimitedAccessFileType WebPreviewableFiles (default) Allows users to preview Office files in the browser. This option optimizes for user productivity but offers less security for files that aren't Office files. Warning: This option is known to cause problems with PDF and image file types because they can be required to be downloaded to the end user's machine to render in the browser. Plan the use of this control carefully. Otherwise, your users could be faced with unexpected "Access Denied" errors.
-LimitedAccessFileType OtherFiles Allows users to download files that can't be previewed, such as .zip and .exe. This option offers less security. If this mode is enabled, then for downloading files like .zip or .exe, you can copy the url of the file and paste in browser (example: https://contoso.sharepoint.com/:u:/r/sites/test/Shared%20Documents/test1.zip).
The AllowDownlownloadingNonWebViewableFiles parameter is no longer supported. Use LimitedAccessFileType instead.
People outside the organization will be affected when you use conditional access policies to block or limit access from unmanaged devices. If users have shared items with specific people (who must enter a verification code sent to their email address), you can exempt them from this policy by running the following command.
Set-SPOTenant -ApplyAppEnforcedRestrictionsToAdHocRecipients $false
Note
"Anyone" links (shareable links that don't require sign-in) aren't affected by these policies. People who have an "Anyone" link to a file or folder will be able to download the item. For all sites where you enable conditional access policies, you should disable "Anyone" links.
How does this affect apps?
Blocking access and blocking download may impact the user experience in some apps, including some Office apps. We recommend that you turn on the policy for some users and test the experience with the apps used in your organization. In Office, make sure to check the behavior in Power Apps and Power Automate when your policy is on.
Note
Apps that run in "app-only" mode in the service, like antivirus apps and search crawlers, are exempted from the policy.
If you're using classic SharePoint site templates, site images may not render correctly. This is because the policy prevents the original image files from being downloaded to the browser.
For new tenants, apps using an ACS app-only access token is disabled by default. We recommend using the Microsoft Entra ID app-only model which is modern and more secure. But you can change the behavior by running set-spotenant -DisableCustomAppAuthentication $false (needs the latest SharePoint admin PowerShell).
Need more help?
See also
Policy recommendations for securing SharePoint sites and files
Control access to SharePoint and OneDrive data based on defined network locations