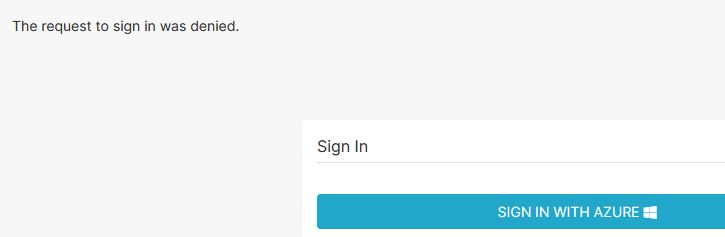
Azure AD b2C - get The request to sign in was denied.
Hi,
I'm trying to setup OAUTH Azure AD b2C for superset and I get a message The request to sign in was denied. after sign in.
Here is my setup from superset.
superset_config.py
from flask import session
from flask_appbuilder.security.manager import (
AUTH_DB,
AUTH_OAUTH,
AUTH_LDAP,
)
basedir = os.path.abspath(os.path.dirname(file))
ROW_LIMIT = 5000
SUPERSET_WORKERS = 4
AUTH_ROLE_ADMIN = 'admin'
AUTH_ROLE_PUBLIC = 'Public'
you can allow users to self register
AUTH_USER_REGISTRATION = True
AUTH_USER_REGISTRATION_ROLE = "admin"
AUTH_TYPE = AUTH_OAUTH
SECRET_KEY = "My_secret_key_supert_is_great"
CSRF_ENABLED = True
OAUTH_PROVIDERS = [
{
"name": "azure",
"icon": "fa-windows",
"token_key": "access_token",
"remote_app": {
"client_id": os.environ.get("AZURE_APPLICATION_ID"),
"client_secret": os.environ.get("AZURE_SECRET"),
"api_base_url": "https://login.microsoftonline.com/2c337311-0b43-4ca6-afcc-53efcaee4d5f/oauth2",
"client_kwargs": {
"scope": "User.read name preferred_username email profile upn",
"resource": os.environ.get("AZURE_APPLICATION_ID"),
},
"request_token_url": None,
"access_token_url": "https://login.microsoftonline.com/2c337311-0b43-4ca6-afcc-53efcaee4d5f/oauth2/token",
"authorize_url": "https://login.microsoftonline.com/2c337311-0b43-4ca6-afcc-53efcaee4d5f/oauth2/authorize",
},
},
]
15 answers
Sort by: Most helpful
-
-
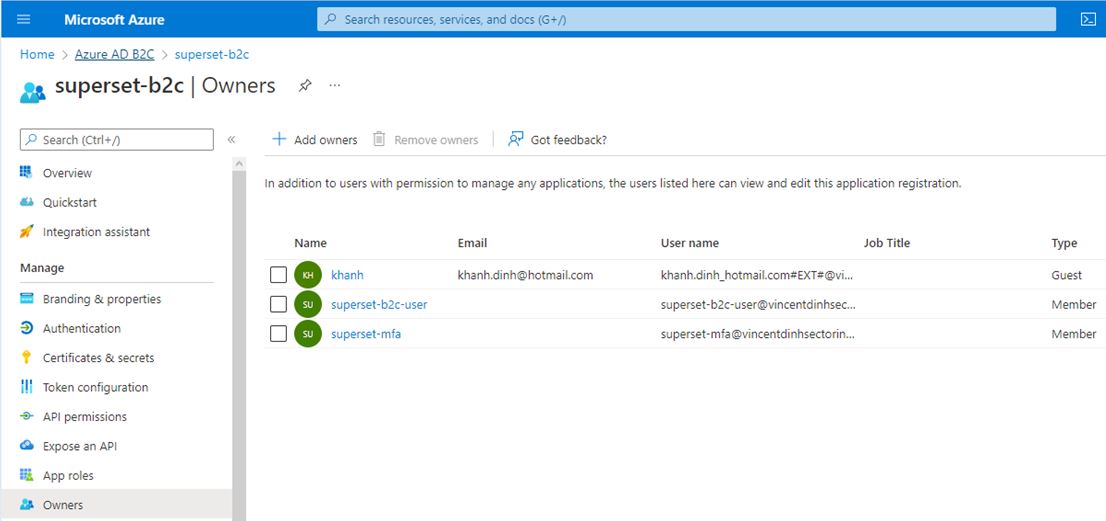
khanh 1 Reputation point
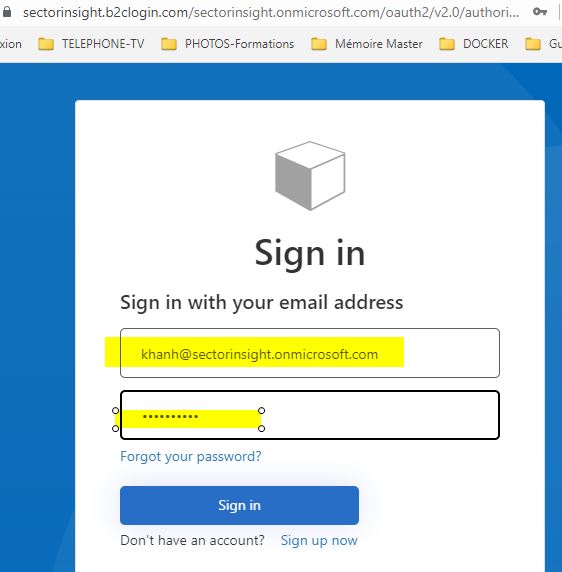
2022-06-13T18:13:29.503+00:00 Hi ShwetaMathur,
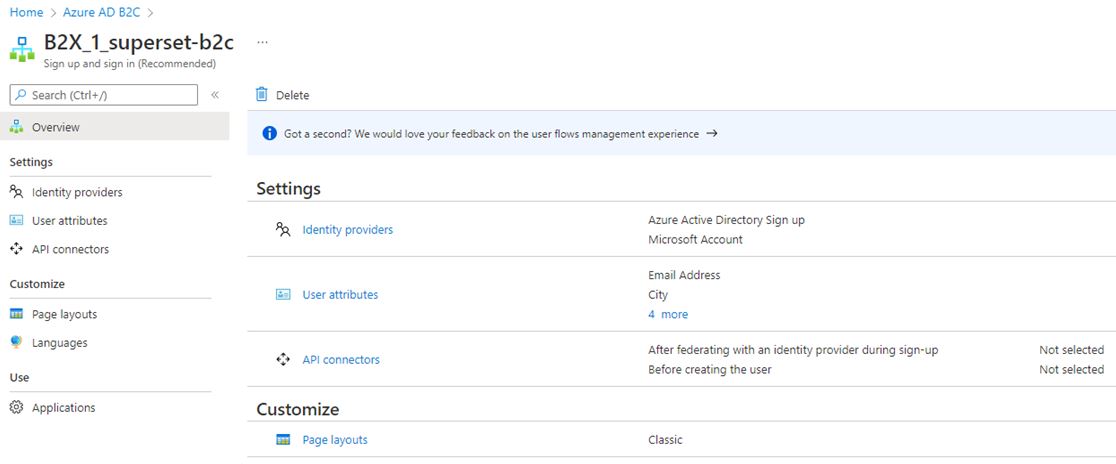
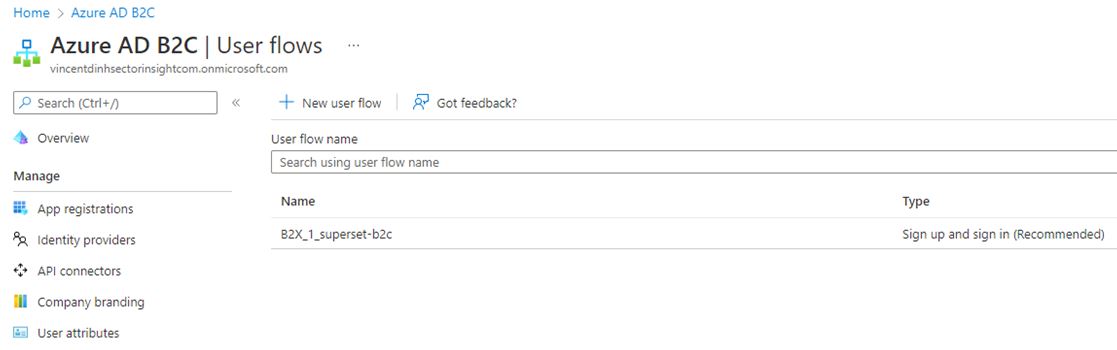
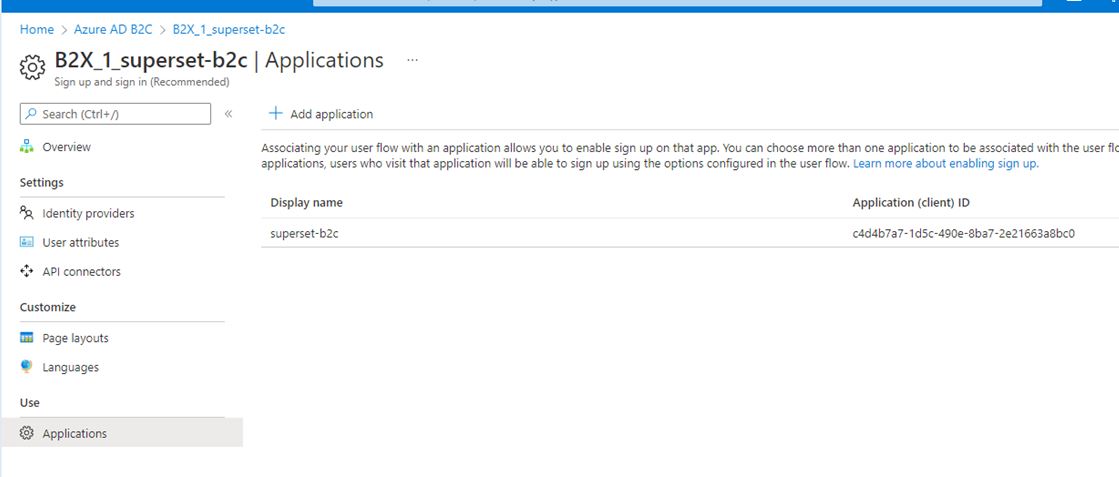
I'm able to create a new B2C tenant and run user flow
---------------------- Begin OAUTH Azure AD B2C --------------------------------------
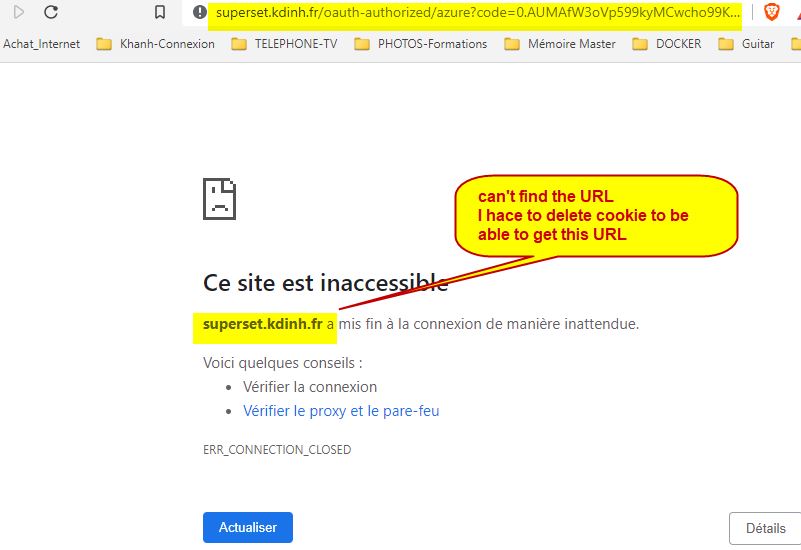
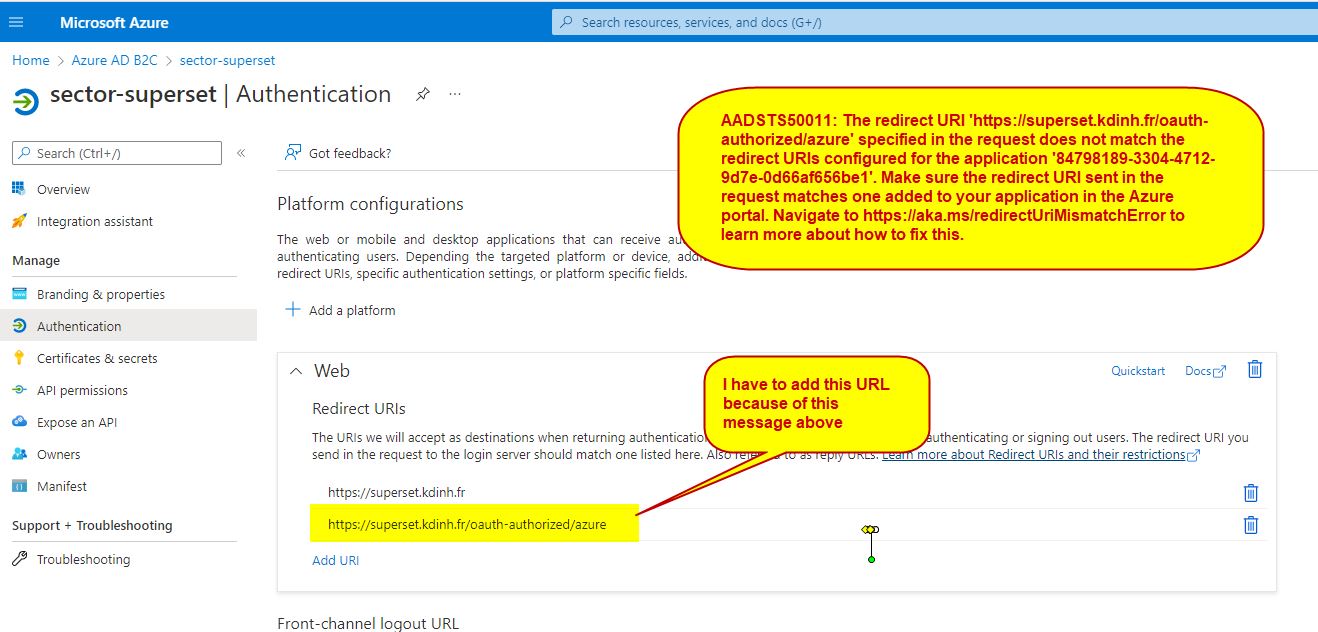
add fix for AADSTS50011: The redirect URI 'http://superset.kdinh.fr/oauth-authorized/azu
ENABLE_PROXY_FIX=True
from flask import session
from flask_appbuilder.security.manager import (
AUTH_DB,
AUTH_OAUTH,
)
basedir = os.path.abspath(os.path.dirname(file))
ROW_LIMIT = 5000
SUPERSET_WORKERS = 4AUTH_ROLE_ADMIN = 'admin'
AUTH_ROLE_PUBLIC = 'Public'you can allow users to self register
AUTH_USER_REGISTRATION = True
AUTH_USER_REGISTRATION_ROLE = 'admin'AUTH_TYPE = AUTH_OAUTH
OAUTH_PROVIDERS = [
{
'name': 'azure',
'icon': 'fa-windows',
'token_key': 'access_token',
'remote_app': {
'client_id': '84798189-3304-4712-9d7e-0d66af656be1',
'client_secret': 'mnew-secret----Hpbl8',
'api_base_url': 'https://login.microsoftonline.com/56e86d7d-7d9e-4cf6-8c0b-0721a3df4a32/oauth2',
'client_kwargs': {
'scope': 'User.read givenName sn email profile upn',
'resource': '84798189-3304-4712-9d7e-0d66af656be1',
},
'request_token_url': None,
'access_token_url': 'https://login.microsoftonline.com/56e86d7d-7d9e-4cf6-8c0b-0721a3df4a32/oauth2/token',
'authorize_url': 'https://login.microsoftonline.com/56e86d7d-7d9e-4cf6-8c0b-0721a3df4a32/oauth2/authorize',
},
},
]
##'scope': 'User.read name preferred_username email profile upn',---------------------- End OAUTH Azure AD B2C --------------------------------------
I get the same result.
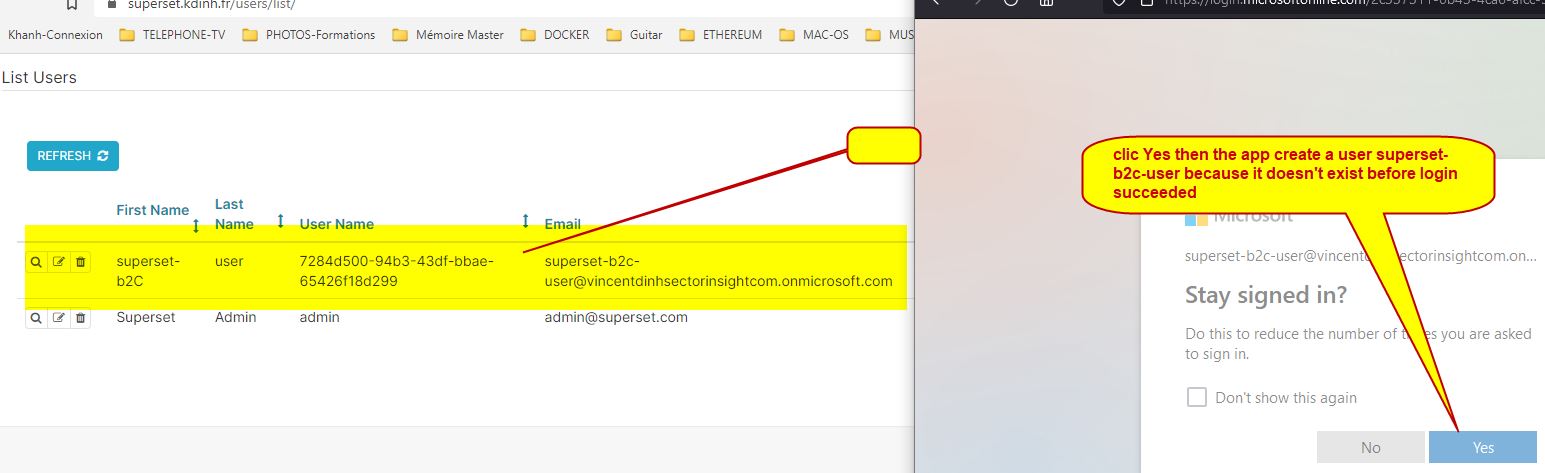
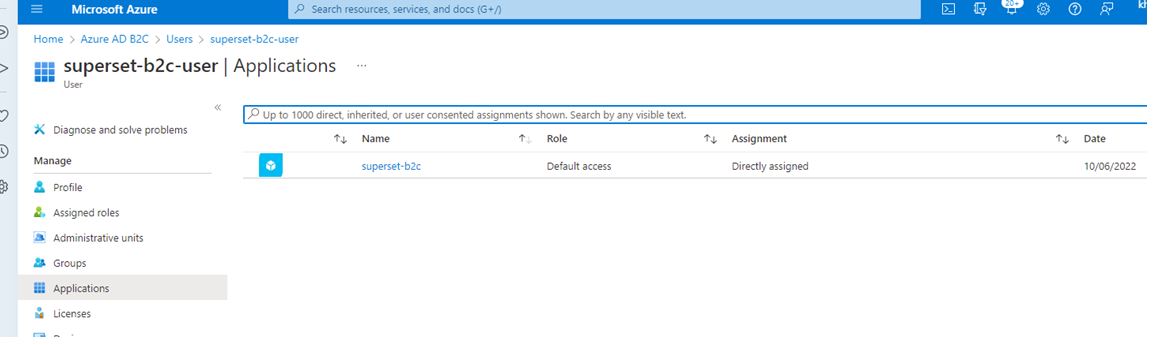
The login that doesn't exist in the app superset is created when first login but the web page still show loading....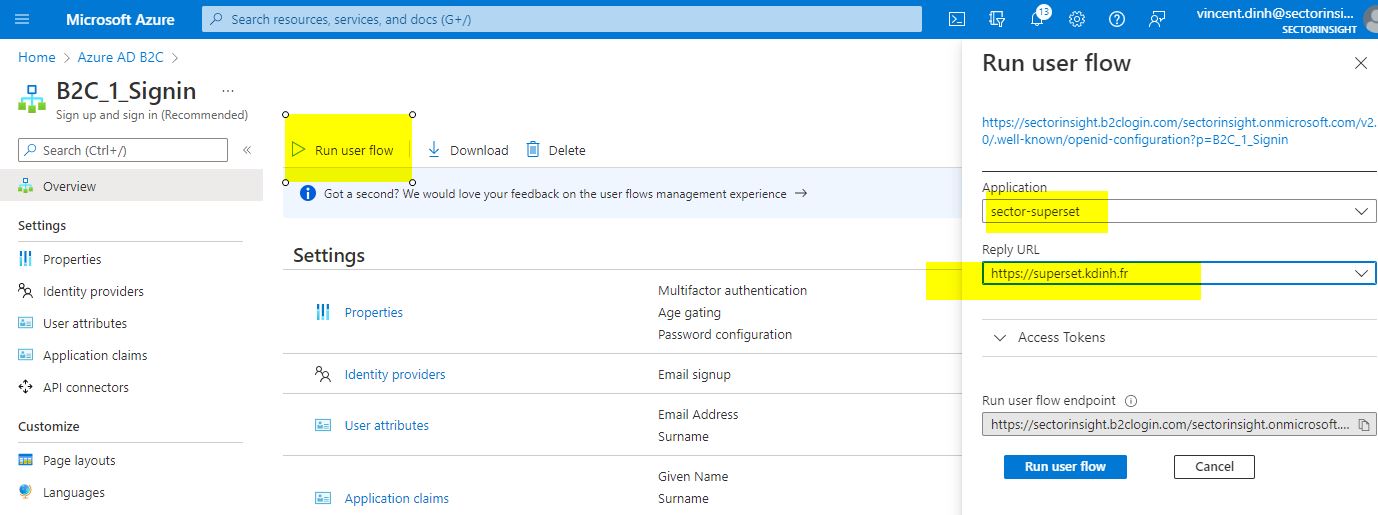

-
khanh 1 Reputation point
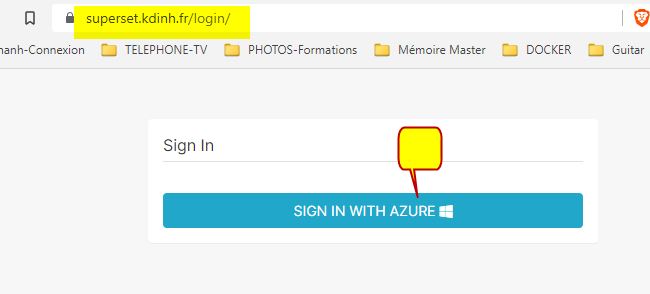
2022-06-13T18:17:57.007+00:00 May be something wrong on mu URL redirect ?
-
khanh 1 Reputation point
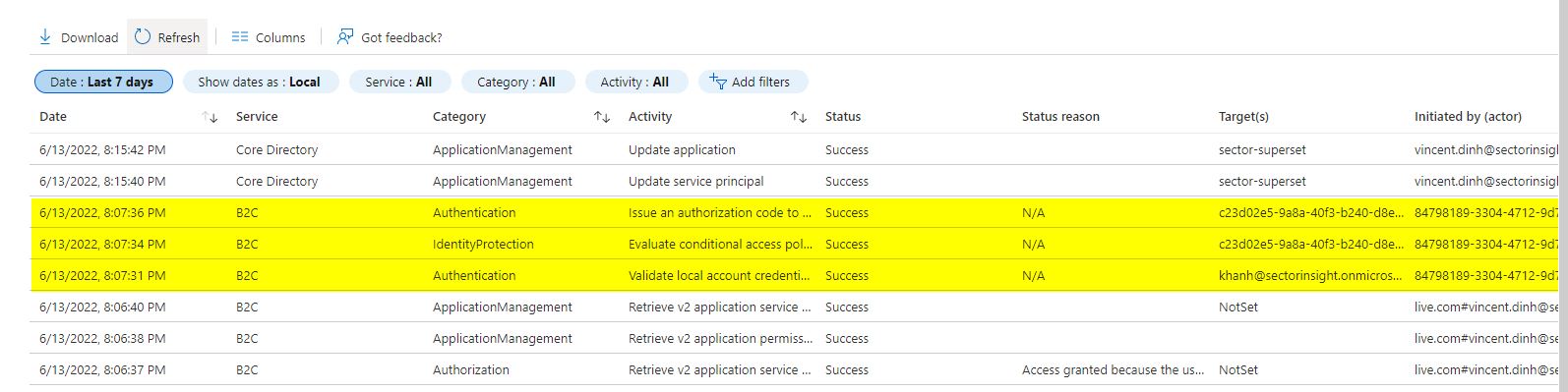
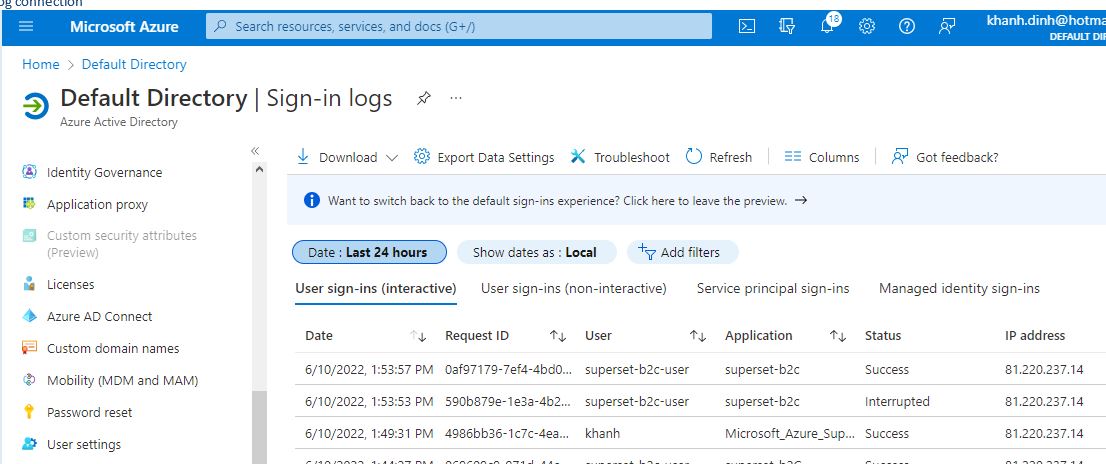
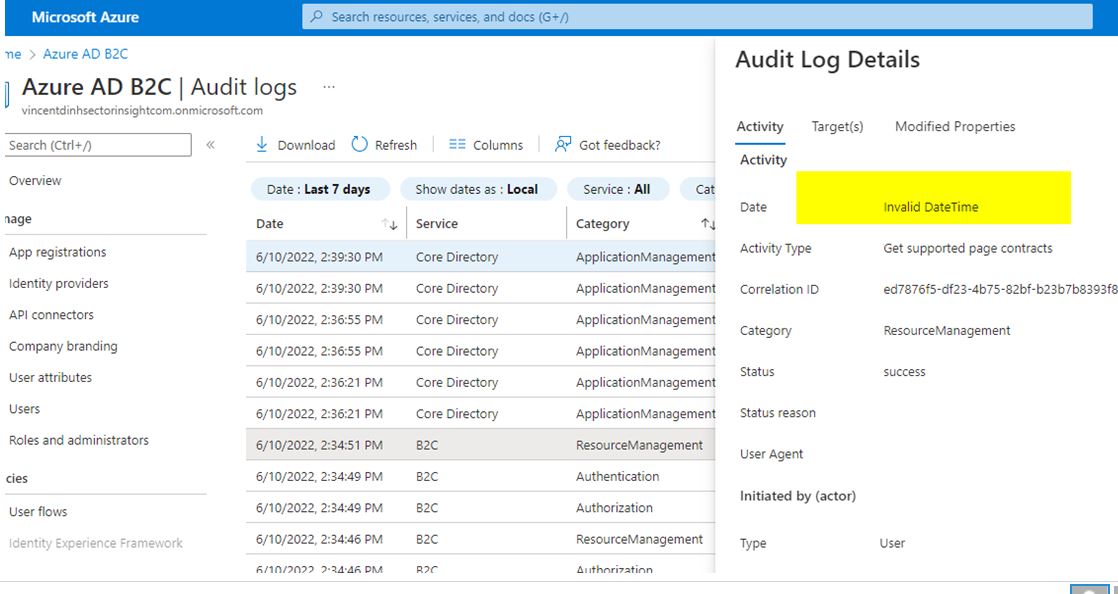
2022-06-13T18:23:47.2+00:00 audit logs , I can see that Authentication is succeeded
-
khanh 1 Reputation point
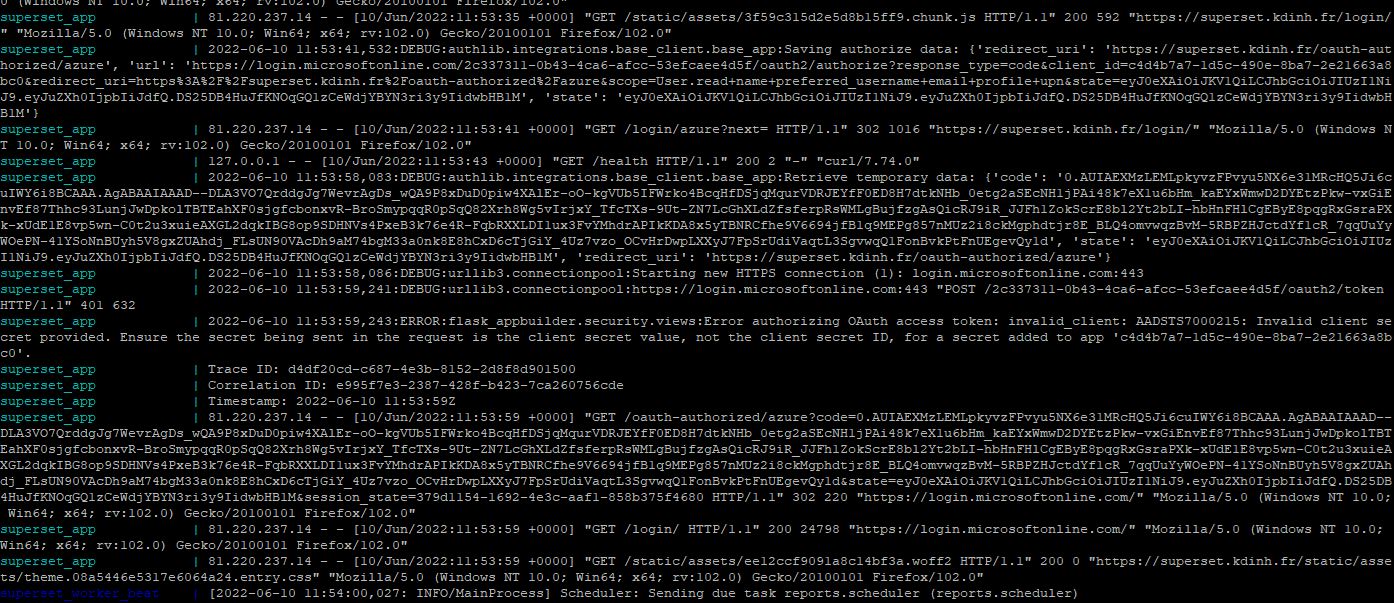
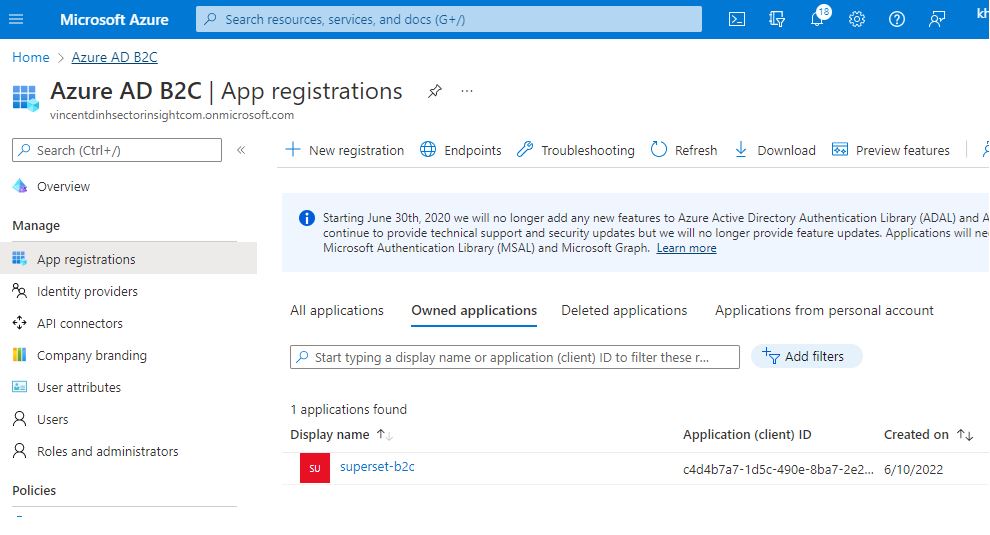
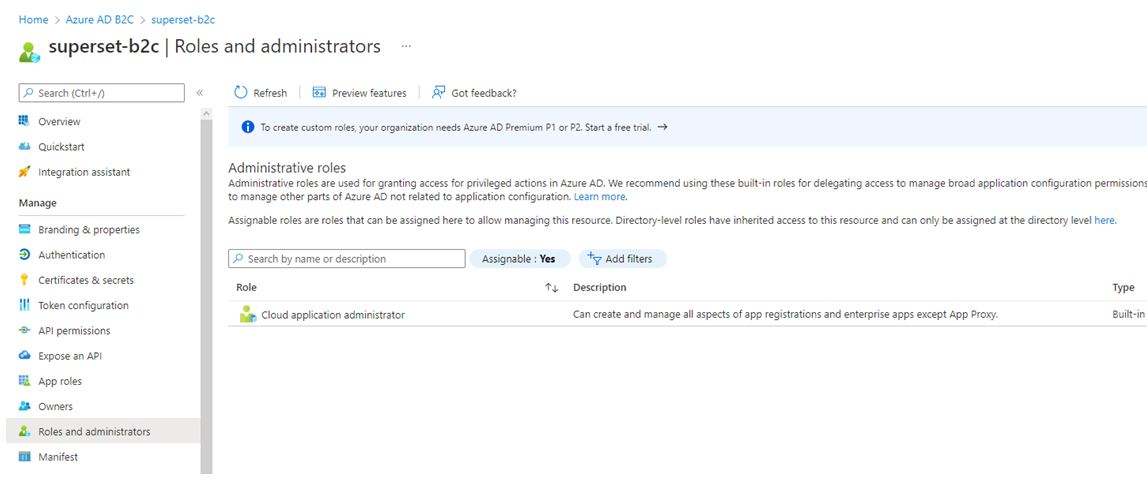
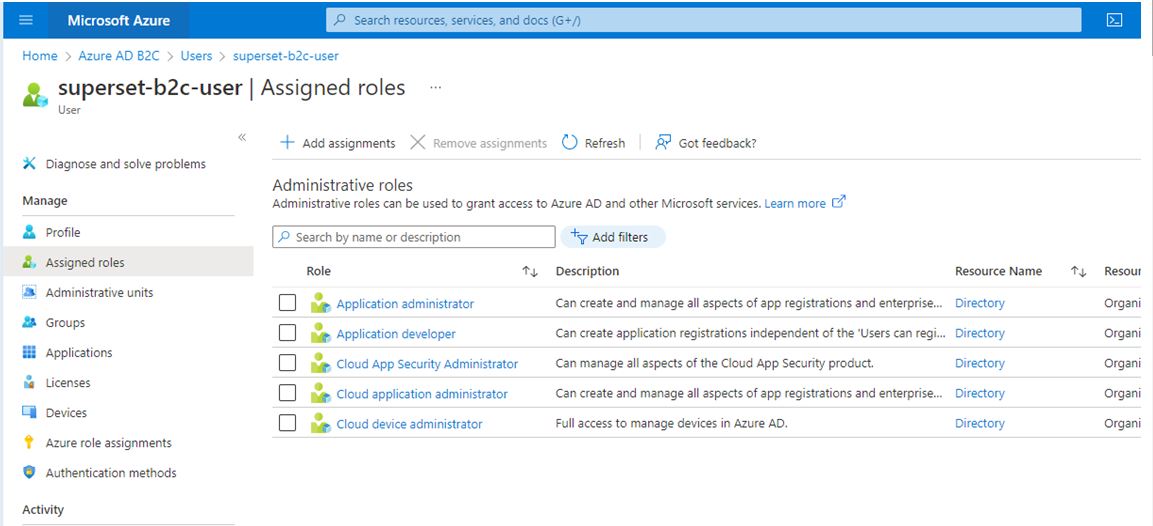
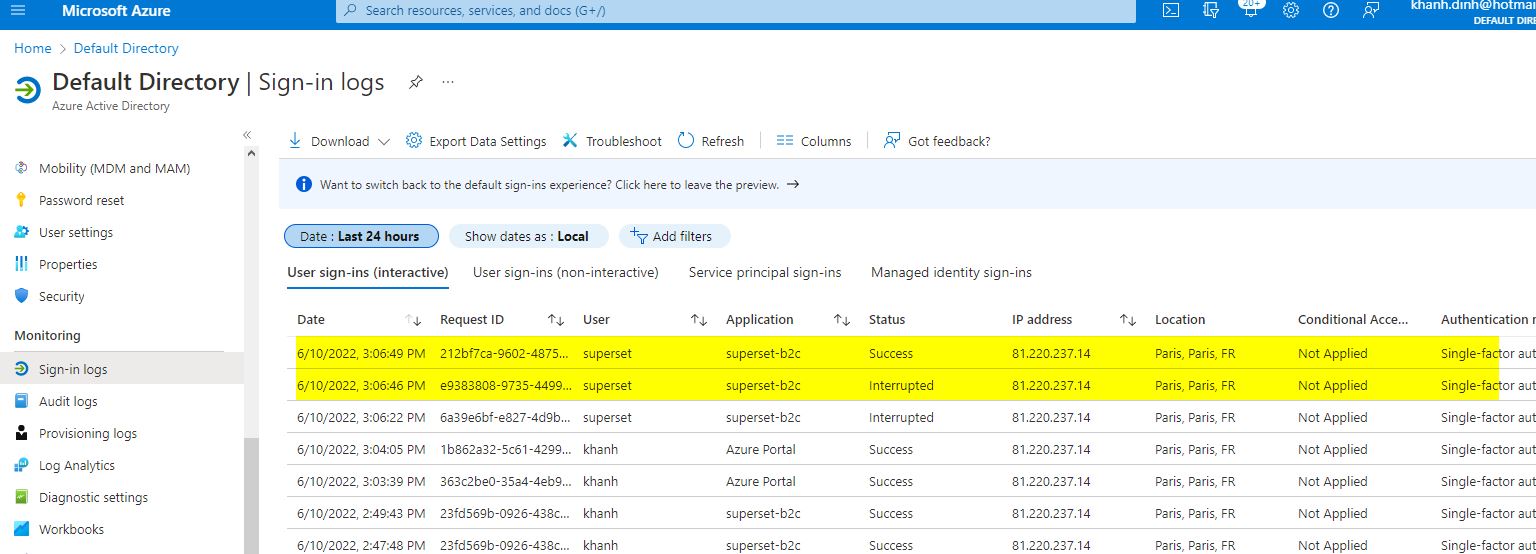
2022-06-13T19:56:47.08+00:00 i ShwetaMathur,
May be this log can help