Hi @khanh ,
Thanks for reaching out.
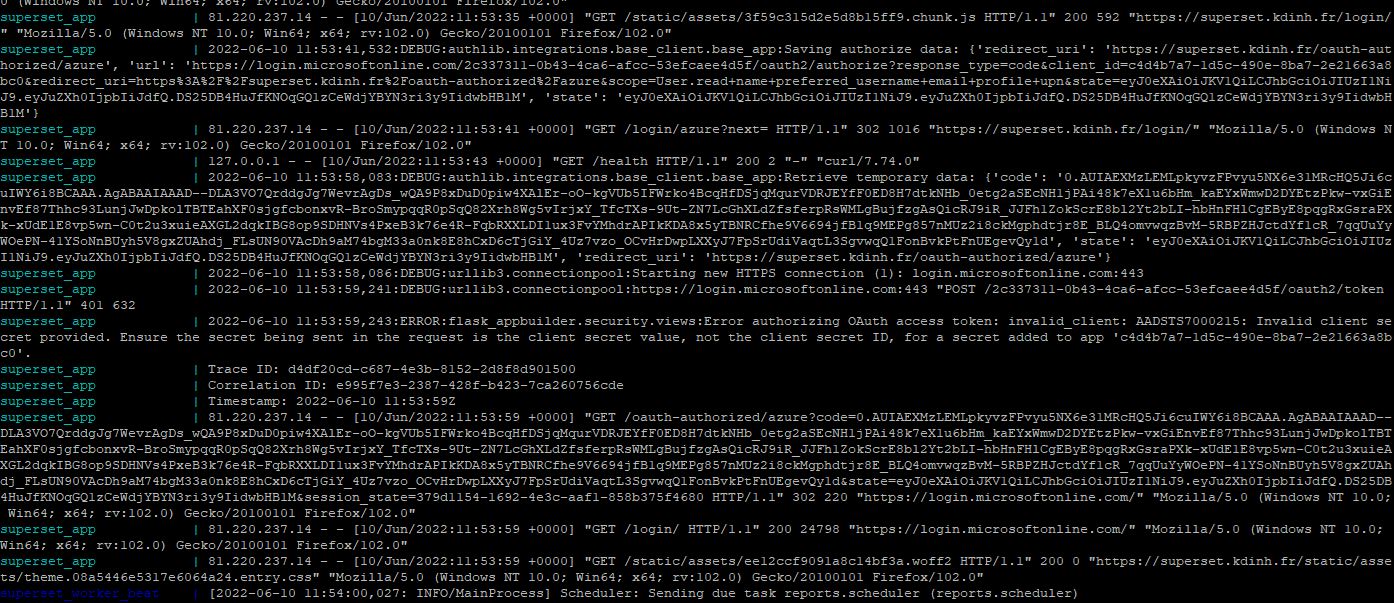
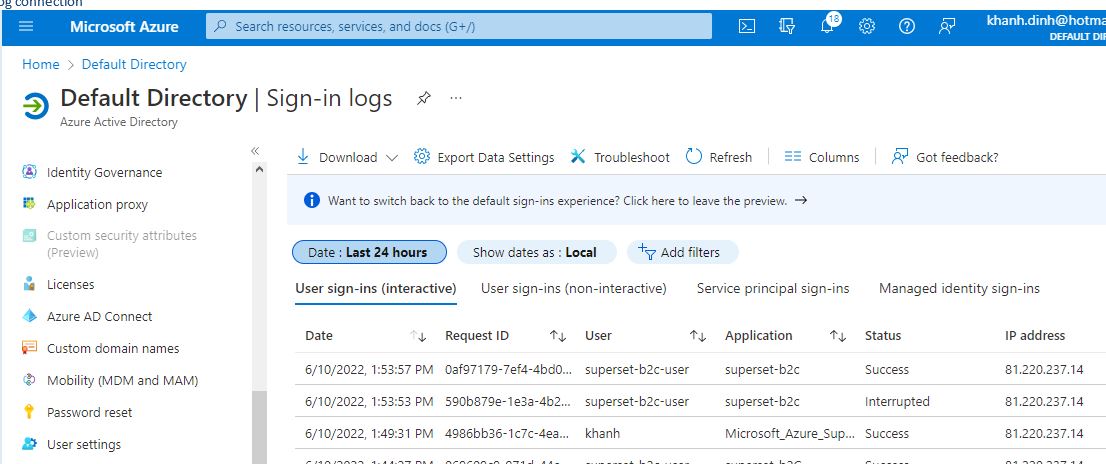
I understand you are looking to authenticate using Authorization code flow in Azure AD B2C and getting "AADSTS7000215: Invalid client secret is provided".
In authorization code flow, client secret is required in case of web applications where client can securely store the client secret.
The error you are getting is due to invalid client secret is provided in the application.
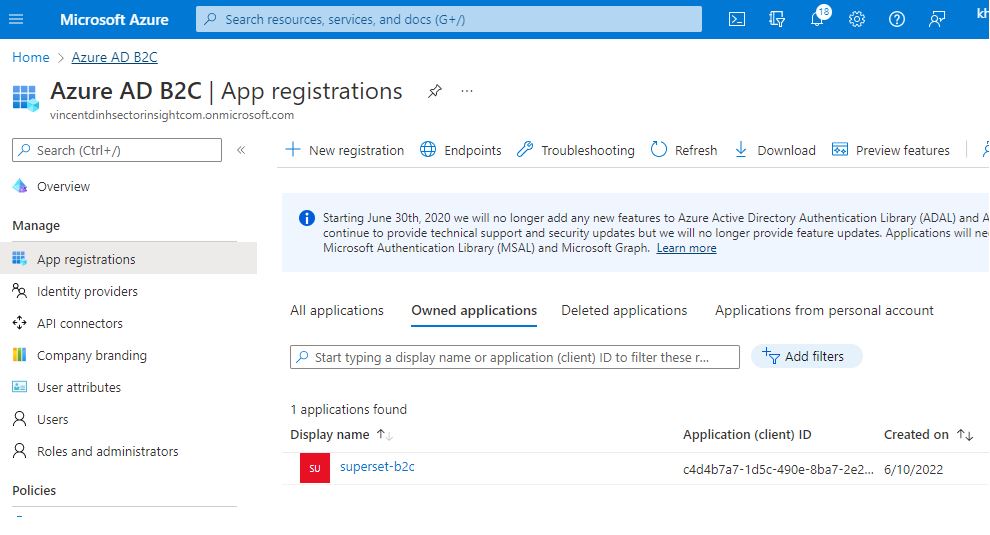
Make sure you are providing the value in client_secret and not the client secret ID.
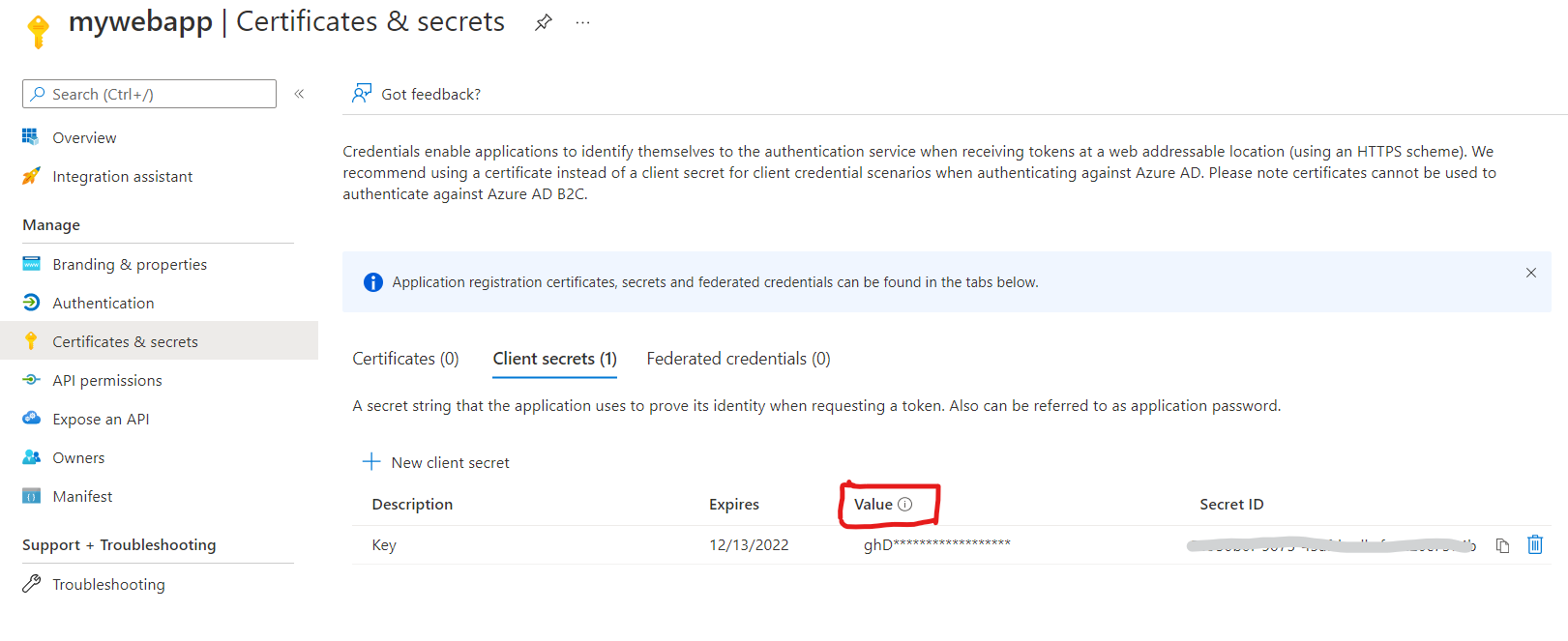
If issue still persists, try to create new secret key using "Certificates and Secrets" on application blade and provide new value to your application to get the token.
Hope this will help. If that doesn't help, please let us know to help you further.
Thanks,
Shweta
---------------------------------------
Please remember to "Accept Answer" if answer helped you.