Hi @⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀⠀ ,
Thanks for reaching out.
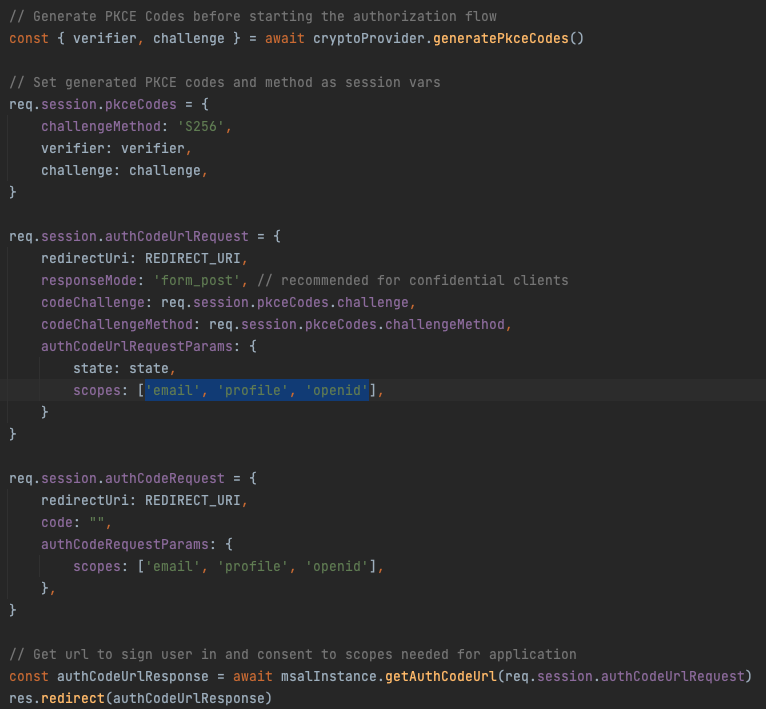
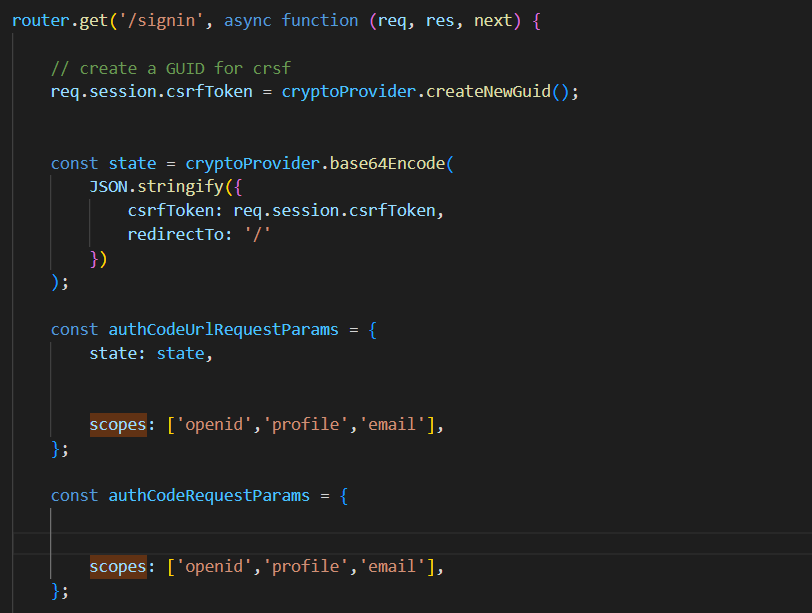
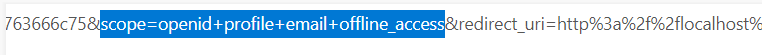
I understand you are trying to get the openid, profile and offline_access scopes in the access token and not able to get the email scope.
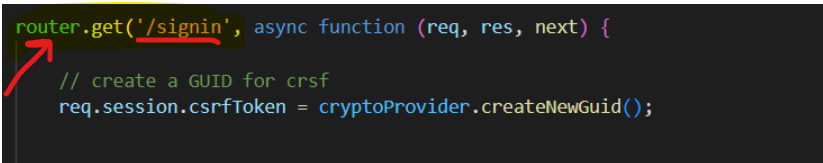
Could you please confirm when you are saying getting three scopes - profile, openid and offline_access. Where and how you are able to check that?
Did you tried to decode the token you are getting using jwt.ms and not getting email there?
Did you tried the same request using postman and facing the same issue there as well?
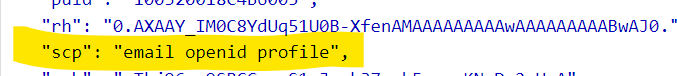
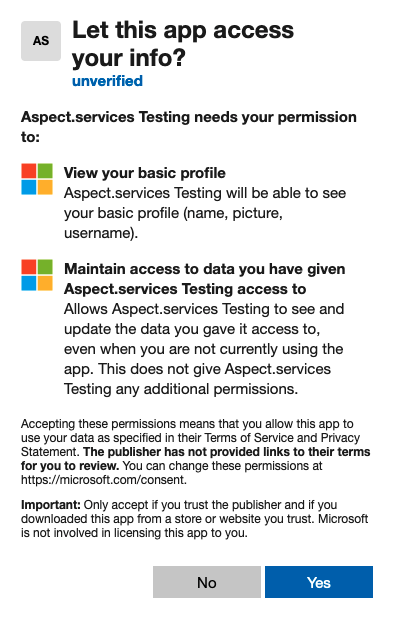
openID, profile and email are built in scopes provided by openID connect so application can request access to large amount of information about the user which is required for authentication.
There might be chance that there is no email address associated with the Azure AD account, then even if you include the email scope you may not get any email claim back. If you are getting another profile related claims like family_name and given_name, then this might be the problem of not getting email claim.
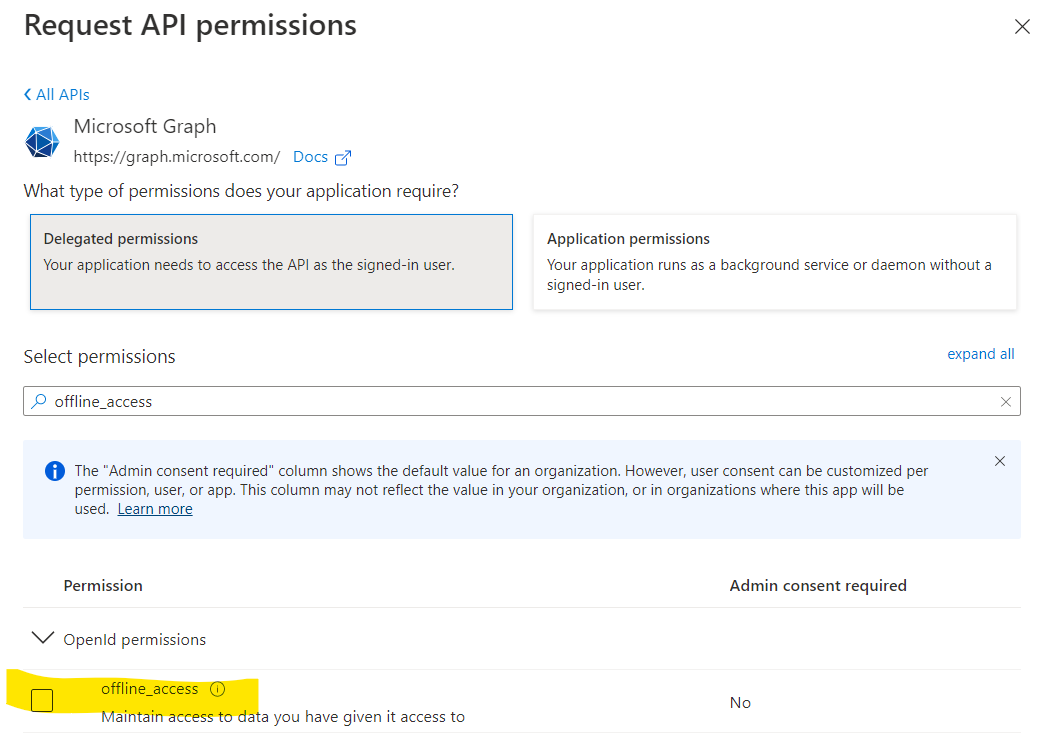
However, the offline_access scope is used to request for Refresh Token and is never returned as a scope because it cannot be a part of the access token. If you are getting the offline_access scope , could you check the permissions you provided while registering the application in the portal and remove the offline_access permission if granted.
Please confirm the above, so that we can help you further.
Thanks,
Shweta