Using Microsoft Entra multifactor authentication
Applies to:
Azure SQL Database
Azure SQL Managed Instance
Azure Synapse Analytics
SQL Server on Azure VM
SQL Server enabled by Azure Arc
Microsoft Entra multifactor authentication is a security feature provided by Microsoft's cloud-based identity and access management service. Multifactor authentication enhances the security of user sign-ins by requiring users to provide extra verification steps beyond a password.
Note
Microsoft Entra ID was previously known as Azure Active Directory (Azure AD).
Multifactor authentication is a supported authentication method for Azure SQL Database, Azure SQL Managed Instance, Azure Synapse Analytics, and SQL Server 2022 (16.x) and later versions.
This article provides a brief overview of the benefits of multifactor authentication, explains how to configure it with Microsoft Entra ID, and shows how to use it to connect to a database with SQL Server Management Studio (SSMS).
Important
Databases in Azure SQL Database, Azure SQL Managed Instance, Azure Synapse, and SQL Server 2022 are referred to collectively in the remainder of this article as databases, and the server is referring to the server that hosts databases for Azure SQL Database and Azure Synapse.
Benefits of MFA
Microsoft Entra multifactor authentication helps safeguard access to data and applications while meeting user demand for a simple sign-in process. MFA adds an extra layer of security to user sign-ins by requiring users to provide two or more authentication factors. These factors typically include something the user knows (password), something the user possesses (smartphone or hardware token), and/or something the user is (biometric data). By combining multiple factors, MFA significantly reduces the likelihood of unauthorized access.
Microsoft Entra multifactor authentication provides all the benefits of Microsoft Entra authentication described in the Microsoft Entra authentication overview.
For the full list of authentication methods available, see What authentication and verification methods are available in Microsoft Entra ID?
Configuration steps
- Configure a Microsoft Entra tenant - For more information, see Administering your Microsoft Entra directory, Integrating your on-premises identities with Microsoft Entra ID, Add your own domain name to Microsoft Entra ID, Federation with Microsoft Entra ID, and Manage Microsoft Entra ID using Windows PowerShell.
- Configure MFA - For step-by-step instructions, see What is Microsoft Entra multifactor authentication?, Conditional Access (MFA) with Azure SQL Database and Data Warehouse. (Full Conditional Access requires a Premium Microsoft Entra ID. Limited MFA is available with a standard Azure AD.)
- Configure Microsoft Entra authentication - For step-by-step instructions, see Connecting to SQL Database, SQL Managed Instance, or Azure Synapse using Microsoft Entra authentication.
- Download SSMS - On the client computer, download the latest SSMS, from Download SQL Server Management Studio (SSMS).
Note
In December 2021, releases of SSMS prior to 18.6 will no longer authenticate through Microsoft Entra ID with MFA.
To continue utilizing Microsoft Entra authentication with MFA, you need SSMS 18.6 or later.
Microsoft Entra B2B support
Microsoft Entra multifactor authentication also supports Microsoft Entra B2B collaboration, which enables businesses to invite guest users to collaborate with their organization. Guest users can connect to databases either as individual users or members of a Microsoft Entra group. For more information, see Create guest user in SQL Database, Azure Synapse, and SQL Managed Instance.
Connect using MFA in SSMS
The following steps show how to connect using multifactor authentication in the latest SSMS.
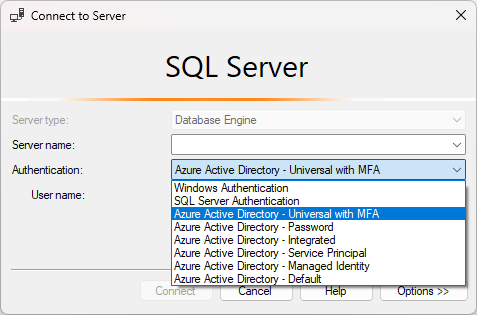
To connect using MFA, on the Connect to Server dialog box in SSMS select Azure Active Directory - Universal with MFA.
Fill the Server name box with your server's name. Fill the User name box with your Microsoft Entra credentials, in the format
user_name@domain.com.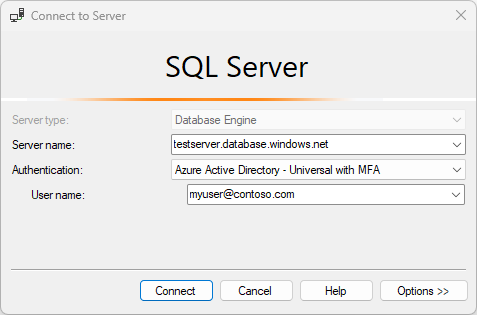
Click Connect.
When the Sign in to your account dialog box appears, it should be prepopulated with the User name you provided in step 2. No password is required if a user is part of a domain federated with Microsoft Entra ID.
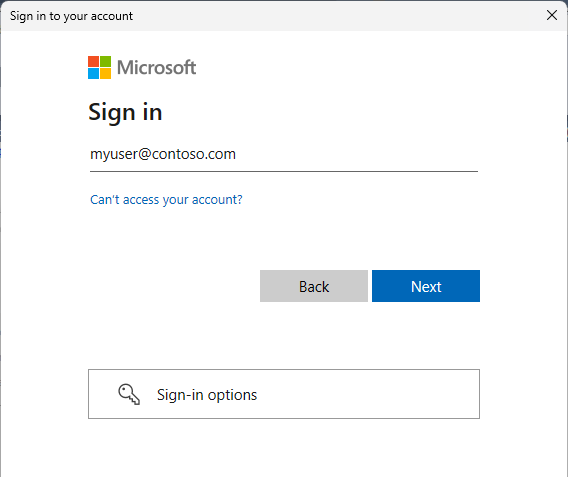
You'll be prompted to authenticate using one of the methods configured based on the MFA administrator setting.
When verification is complete, SSMS connects normally, presuming valid credentials and firewall access.
Microsoft Entra multifactor authentication is a supported authentication method for all SQL tools. For information on programmatically authenticating with Microsoft Entra ID, see the Overview of the Microsoft Authentication Library (MSAL).
Next steps
- Grant others access to your database: SQL Database Authentication and Authorization: Granting Access
- Make sure others can connect through the firewall: Configure a server-level firewall rule using the Azure portal
- Configure and manage Microsoft Entra authentication with SQL Database or Azure Synapse
- Create Microsoft Entra guest users and set as a Microsoft Entra admin
- C# interface IUniversalAuthProvider Interface
- Tutorial: Set up Microsoft Entra authentication for SQL Server
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for