Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
- Starting August 15, 2025, Azure CDN from Microsoft (classic) will no longer support new domain onboarding or profile creation. Migrate to AFD Standard and Premium to create new domains or profiles and avoid service disruption. Learn more
- Starting August 15, 2025, Azure CDN from Microsoft (classic) will no longer support Managed certificates. To avoid service disruption, either switch to Bring Your Own Certificate (BYOC) or migrate to AFD Standard and Premium by this date. Existing managed certificates will be auto renewed before August 15, 2025, and remain valid until April 14, 2026. Learn more
- Azure CDN Standard from Microsoft (classic) will be retired on September 30, 2027. To avoid service disruption migrate to AFD Standard or Premium. Learn more.
- Azure CDN from Edgio was retired on January 15, 2025. Learn more.
After you've integrated your Azure Storage account with Azure Content Delivery Network, you can add a custom domain and enable HTTPS on that domain for your custom blob storage endpoint.
Note
Azure Content Delivery Network provides permanent access to Azure Storage resources and removing access requires manual steps.
Prerequisites
Before you can complete the steps in this tutorial, you must first integrate your Azure Storage account with Azure Content Delivery Network. For more information, see Quickstart: Integrate an Azure Storage account with Azure Content Delivery Network.
Add a custom domain
When you create a content delivery network endpoint in your profile, the endpoint name, which is a subdomain of azureedge.net, is included in the URL for delivering content delivery network content by default. You also have the option of associating a custom domain with a content delivery network endpoint. With this option, you deliver your content with a custom domain in your URL instead of an endpoint name. To add a custom domain to your endpoint, follow the instructions in this tutorial: Add a custom domain to your Azure Content Delivery Network endpoint.
Configure HTTPS
By using the HTTPS protocol on your custom domain, you ensure that your data is delivered securely on the internet via TLS/SSL encryption. When your web browser is connected to a web site via HTTPS, it validates the web site's security certificate and verifies if the certificate is issue by a legitimate certificate authority. To configure HTTPS on your custom domain, follow the instructions in this tutorial: Configure HTTPS on an Azure Content Delivery Network custom domain.
Shared Access Signatures
If your blob storage endpoint is configured to disallow anonymous read access, you should provide a Shared Access Signature (SAS) token in each request you make to your custom domain. By default, blob storage endpoints disallow anonymous read access. For more information about SAS, see Managing anonymous read access to containers and blobs.
Azure Content Delivery Network ignores any restrictions added to the SAS token. For example, all SAS tokens have an expiration time, which means that content can still be accessed with an expired SAS until that content gets purged from the content delivery network point of presence (POP) servers. You can control how long data is cached on Azure Content Delivery Network by setting the cache response header. For more information, see Managing expiration of Azure Storage blobs in Azure Content Delivery Network.
If you create multiple SAS URLs for the same blob endpoint, consider enabling query string caching. Doing so ensures that each URL is treated as a unique entity. For more information, see Controlling Azure Content Delivery Network caching behavior with query strings.
HTTP-to-HTTPS redirection
You can redirect HTTP traffic to HTTPS by creating a URL redirect rule with the Standard rules engine.
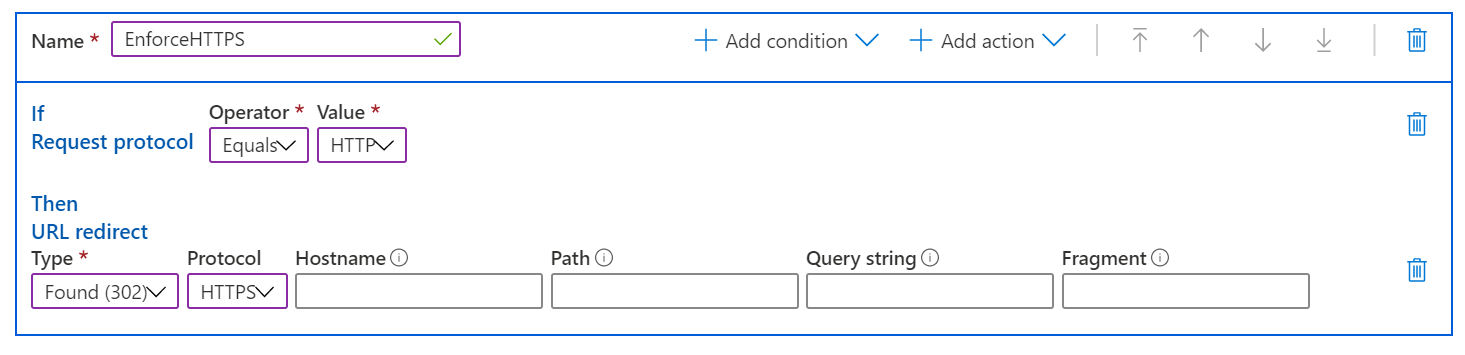
In the above rule, leaving Hostname, Path, Query string, and Fragment results in the incoming values being used in the redirect.
Pricing and billing
When you access blobs through Azure Content Delivery Network, you pay Blob storage prices for traffic between the POP servers and the origin (Blob storage), and Azure content delivery network pricing for data accessed from the POP servers.
For example, if you have a storage account in the United States that's being accessed using Azure Content Delivery Network and someone in Europe attempts to access one of the blobs in that storage account via Azure Content Delivery Network, Azure Content Delivery Network first checks the POP closest to Europe for that blob. If found, Azure Content Delivery Network accesses that copy of the blob and uses content delivery network pricing, because it's being accessed on Azure Content Delivery Network. If not found, Azure Content Delivery Network copies the blob to the POP server, which results in egress and transaction charges as specified in the Blob storage pricing, and then accesses the file on the POP server, which results in Azure Content Delivery Network billing.