Azure DevOps Roadmap
| What's New | Developer Community | DevOps Blog | Documentation |
Product roadmap
This feature list is a peek into our roadmap. It identifies some of the significant features we are currently working on and a rough timeframe for when you can expect to see them. It is not comprehensive but is intended to provide some visibility into key investments. At the top you will find a list of our large multi-quarter initiatives and the features that they break down into. Further down you will find the full list of significant features we have planned.
Each feature is linked to an article where you can learn more about a particular item. These features and dates are the current plans and are subject to change. The Timeframe columns reflect when we expect the feature to be available on Azure DevOps Services; the Server columns reflect when we expect the feature to ship in Azure DevOps Server.
Initiatives
GitHub Advanced Security for Azure DevOps
GitHub Advanced Security (GHAS) for Azure DevOps is now generally available. Any project collection administrator can now enable Advanced Security for their organization, projects and repos from the Project Settings or Organization Settings. You can learn more about how to configure GitHub Advanced Security for Azure DevOps in our documentation.
New capabilities we expect to deliver in the upcoming semester include:
Similar to GHAS-for-GitHub, any third-party open source or commercial security analysis pipeline task that generates results in conforming SARIF format can display those results in the Advanced Security Code Scanning alerts hub. This gives you a single pane of glass natively built into Azure DevOps to view your repository code security alerts from all your analysis tools.
Support for custom CodeQL queries.
Detection and blocking of more kinds of secrets.
Minimizing the risks associated with credential theft
Azure DevOps supports many different authentication mechanisms, including basic authentication, personal access tokens (PATs), SSH, and Microsoft Entra ID (formerly Azure Active Directory) access tokens. These mechanisms are not created equally from a security perspective, especially when it comes to the potential for credential theft. For example, unintended leakage of credentials like PATs can let malicious actors into Azure DevOps organizations where they can gain access to critical assets like source code, pivot toward supply chain attacks, or even pivot toward compromising production infrastructure. To minimize the risks of credential theft, we will focus our efforts in the upcoming quarters in the following areas:
Enable administrators to improve authentication security through control plane policies.
Reducing the need for PATs and other stealable secrets by adding support for more secure alternatives.
Deepening Azure DevOps' integration with Microsoft Entra ID to better support its various security features.
Avoiding the need to store production secrets in Azure Pipelines service connections.
| Feature | Area | Service | Server |
|---|---|---|---|
| PAT lifecycle APIs | General |  2022 Q4 2022 Q4 |
N/A |
| Control plane for personal access tokens (PAT) | General |  2022 Q4 2022 Q4 |
2022.1 |
| Managed Identity and Service Principal support (preview) | General |  2023 Q1 2023 Q1 |
N/A |
| Workload identity federation for Azure Deployments (preview) | Pipelines |  2023 Q3 2023 Q3 |
N/A |
| Granular scopes for Azure Active Directory OAuth | General |  2023 Q3 2023 Q3 |
N/A |
| Managed Identity and Service Principal support (GA) | General |  2023 Q3 2023 Q3 |
N/A |
| Workload identity federation for Azure service connection (GA) | Pipelines | 2024 Q1 | N/A |
| Workload identity federation for Docker service connection | Pipelines | 2024 H1 | N/A |
| Full web support for Conditional Access Policies | General | 2024 Q1 | N/A |
| Policies to disable authentication methods | General | Future | N/A |
Updated Boards experience
The Azure Boards user experience has been updated from the ground up. While the functionality remains the same, you can expect a more modern design, responsive reflows, improved performance, and improved accessibility. This quarter we are rolling out the New Boards Hub as the default experience to all organizations.
Note that most new features we are shipping in Boards are only available in the New Boards Hub. These investments include:
| Feature | Area | Service | Server |
|---|---|---|---|
| Move to position | Boards |  2022 Q2 2022 Q2 |
Future |
| Adding Assigned To avatar to child items on cards | Boards |  2022 Q2 2022 Q2 |
Future |
| Move to Column and Move to Swimlane | Boards |  2022 Q1 2022 Q1 |
Future |
| Filter to work item history | Boards |  2022 Q3 2022 Q3 |
Future |
| Copy work item attachment URL | Boards |  2022 Q4 2022 Q4 |
Future |
| Maintain backlog hierarchy when filters are applied | Boards |  2022 Q4 2022 Q4 |
Future |
| Ability to change link type from Web UI | Boards |  2022 Q4 2022 Q4 |
Future |
| Swimlane colors on Kanban board | Boards |  2023 Q1 2023 Q1 |
Future |
| Swimlane rules on Kanban board | Boards |  2023 Q2 2023 Q2 |
Future |
| Markdown editor for work item comments (preview) | Boards |  2023 Q2 2023 Q2 |
Future |
| Automated team work item rules | Boards |  2024 Q1 2024 Q1 |
Future |
| New Boards Hub on by default for all organizations | Boards | 2024 Q2 | Future |
Improved Boards + GitHub Integration
The existing Azure Boards + GitHub integration has been in place for several years now. The integration is a great starting point, but it does not offer the level of traceability that our customers have grown accustomed to. Based on customer feedback, we have put together set of investments to enhance this integration. Our goal is to improve upon it so that Azure Boards customers who choose to use GitHub repositories can maintain an equivalent level of traceability to having repositories in Azure DevOps.
These investments include:
| Feature | Area | Service | Server |
|---|---|---|---|
| Improved AB#{ID} validation | Boards |  2023 Q4 2023 Q4 |
Future |
| Add link to GitHub commit or pull request from work item (preview) | Boards |  2024 Q1 2024 Q1 |
Future |
| Show more details about a GitHub pull request (preview) | Boards |  2024 Q1 2024 Q1 |
Future |
| Create branch on GitHub repository from work item | Boards | 2024 Q2 | Future |
| Improve scalability when searching and linking GitHub repos to an Azure DevOps project |
Boards | 2024 Q2 | Future |
Pipelines agent Node lifecycle
Azure Pipelines tasks can be authored either in Node or PowerShell, and they use the corresponding runner in the Azure Pipelines agent. Node has a regular cadence of releases, with Node 16 being the LTS and Node 18 the Current version as of October 2022. The original design of the Node task runner did not make Node version upgrades straightforward for task authors, and as a result has not kept up with the latest Node releases. We've heard feedback from customers on this, and are now making a number of changes to enable Azure Pipelines agents to keep installed Node versions in sync with the Node release cadence and support lifecycle while minimizing impacts on task and pipeline authors.
As a first step, we recently released a new Node 16 task runner for the agent. Over the next few months, we plan to provide improved guidance for task authors to keep up with Node updates. Because not all tasks in the Marketplace will be continuously updated to run on the latest versions of Node, we will also provide pipeline authors the ability to continue using non-upgraded tasks. Once all these features are available, we'll remove end-of-life versions of Node from Microsoft hosted agents and self-hosted agent images.
| Feature | Area | Service | Server |
|---|---|---|---|
| Node 16 task runner in pipeline agent | Pipelines |  2022 Q3 2022 Q3 |
2022.1 |
| Tasks can express compatibility with multiple Node runners | Pipelines |  2022 Q3 2022 Q3 |
2022.1 |
| All in-the-box tasks run on Node 16 | Pipelines |  2023 Q4 2023 Q4 |
Future |
| Ability to run tasks on next available Node version, if targeted version is not available | Pipelines |  2023 Q4 2023 Q4 |
2022.1 |
| Removal of Node 6 and 10 from Microsoft hosted pools | Pipelines | Future | Future |
| Ability to download and install old runners on self-hosted agents | Pipelines |  2023 Q4 2023 Q4 |
2022.1 |
| Stop shipping Node 6 and Node 10 runners with the agent | Pipelines | Future | Future |
| Ship a Node 16+ only agent in addition to the one that has all versions | Pipelines | 2024 Q1 | Future |
YAML and release pipelines feature parity
Customers prefer YAML pipelines over classic for builds (CI). However, for releases (CD), many customers have continued to use classic release management pipelines over YAML. The primary reason for this is the lack of parity in various CD features between the two solutions. Over the next year, we'll invest in bridging these gaps.
As a first step, we'll focus on checks. Checks are the primary mechanism in YAML pipelines to gate promotion of a build from one stage to another.
| Feature | Area | Service | Server |
|---|---|---|---|
| Auditing for checks | Pipelines |  2022 Q4 2022 Q4 |
Future |
| Custom variables in checks | Pipelines |  2023 Q1 2023 Q1 |
Future |
| Checks scalability | Pipelines |  2023 Q2 2023 Q2 |
Future |
| Bypass approvals and checks | Pipelines |  2023 Q4 2023 Q4 |
Future |
| Sequencing approvals and other checks | Pipelines | 2024 Q1 | Future |
| Deferred approvals | Pipelines | 2024 Q1 | Future |
| Service connections in checks | Pipelines | Future | Future |
| Checks extensibility | Pipelines | Future | Future |
Next, we'll focus on deployment functionality, to make it possible to have deployment strategies in YAML pipelines similar to the ones in classic release pipelines.
| Feature | Area | Service | Server |
|---|---|---|---|
| Manual queuing of stages | Pipelines | 2024 Q1 | Future |
| Rerun single stage | Pipelines | 2024 Q1 | Future |
| Stage-level concurrency | Pipelines | 2024 Q1 | Future |
| Stage-level traceability | Pipelines | 2024 Q1 | Future |
Streamlined Dashboard Experience
Azure DevOps is enhancing the dashboard experience, focusing on simplifying the user flow for both creation and maintenance. We're fine-tuning our approach to improve workflow. Our aim is to streamline the onboarding process, ensuring that users can set up their dashboards quickly and start working without hassle. To boost productivity and enhance decision-making through dashboard insights, we plan to deliver the following features.
| Feature | Area | Service | Server |
|---|---|---|---|
| Work Item Chart Filtering | Reporting |  2023 Q4 2023 Q4 |
Future |
| New Dashboard directory experience | Reporting |  2023 Q4 2023 Q4 |
Future |
| Dashboard Global Parameter | Reporting | 2024 H1 | Future |
| Dashboard Template | Reporting | 2024 H1 | Future |
All features
How to provide feedback
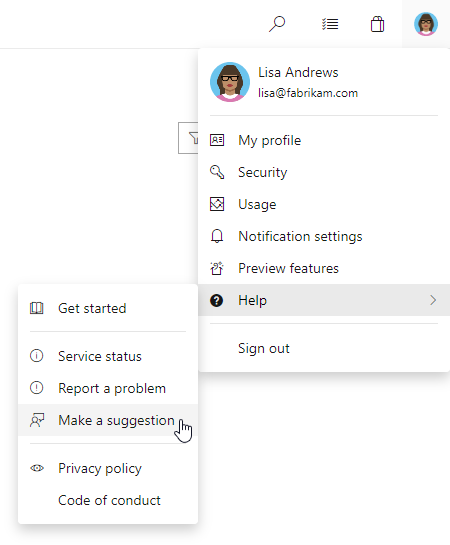
We would love to hear what you think about these features. Report any problems or suggest a feature through Developer Community.
You can also get advice and your questions answered by the community on Stack Overflow.