Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Note
This data connector will be deprecated and will stop collecting data in April 2026. We recommend transitioning to the new Threat Intelligence Upload Indicators API data connector as soon as possible to ensure uninterrupted data collection. For more information, see Connect your threat intelligence platform to Microsoft Sentinel with the upload API.
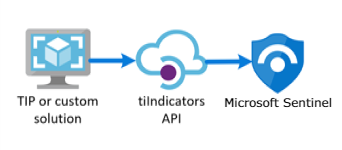
Many organizations use threat intelligence platform (TIP) solutions to aggregate threat indicator feeds from various sources. From the aggregated feed, the data is curated to apply to security solutions such as network devices, EDR/XDR solutions, or security information and event management (SIEM) solutions such as Microsoft Sentinel. By using the TIP data connector, you can use these solutions to import threat indicators into Microsoft Sentinel.
Because the TIP data connector works with the Microsoft Graph Security tiIndicators API to accomplish this process, you can use the connector to send indicators to Microsoft Sentinel (and to other Microsoft security solutions like Defender XDR) from any other custom TIP that can communicate with that API.
Note
For information about feature availability in US Government clouds, see the Microsoft Sentinel tables in Cloud feature availability for US Government customers.
Learn more about threat intelligence in Microsoft Sentinel, and specifically about the TIP products that you can integrate with Microsoft Sentinel.
Important
Microsoft Sentinel is generally available in the Microsoft Defender portal, including for customers without Microsoft Defender XDR or an E5 license.
Starting in July 2026, Microsoft Sentinel will be supported in the Defender portal only, and any remaining customers using the Azure portal will be automatically redirected.
We recommend that any customers using Microsoft Sentinel in Azure start planning the transition to the Defender portal for the full unified security operations experience offered by Microsoft Defender. For more information, see Planning your move to Microsoft Defender portal for all Microsoft Sentinel customers.
Prerequisites
- To install, update, and delete standalone content or solutions in the Content hub, you need the Microsoft Sentinel Contributor role at the resource group level.
- To grant permissions to your TIP product or any other custom application that uses direct integration with the Microsoft Graph TI Indicators API, you must have the Security Administrator Microsoft Entra role or the equivalent permissions.
- To store your threat indicators, you must have read and write permissions to the Microsoft Sentinel workspace.
Instructions
To import threat indicators to Microsoft Sentinel from your integrated TIP or custom threat intelligence solution, follow these steps:
- Obtain an application ID and client secret from Microsoft Entra ID.
- Input this information into your TIP solution or custom application.
- Enable the TIP data connector in Microsoft Sentinel.
Sign up for an application ID and client secret from Microsoft Entra ID
Whether you're working with a TIP or a custom solution, the tiIndicators API requires some basic information to allow you to connect your feed to it and send it threat indicators. The three pieces of information you need are:
- Application (client) ID
- Directory (tenant) ID
- Client secret
You can get this information from Microsoft Entra ID through app registration, which includes the following three steps:
- Register an app with Microsoft Entra ID.
- Specify the permissions required by the app to connect to the Microsoft Graph tiIndicators API and send threat indicators.
- Get consent from your organization to grant these permissions to this application.
Register an application with Microsoft Entra ID
In the Azure portal, go to Microsoft Entra ID.
On the menu, select App Registrations, and then select New registration.
Choose a name for your application registration, select Single tenant, and then select Register.
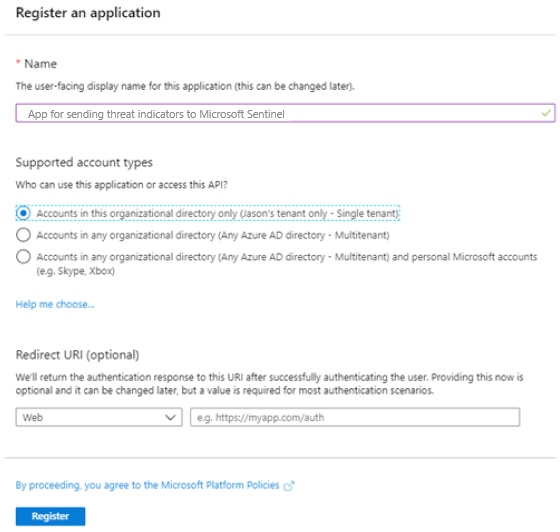
On the screen that opens, copy the Application (client) ID and Directory (tenant) ID values. You need these two pieces of information later to configure your TIP or custom solution to send threat indicators to Microsoft Sentinel. The third piece of information you need, the client secret, comes later.
Specify the permissions required by the application
Go back to the main page of Microsoft Entra ID.
On the menu, select App Registrations, and then select your newly registered app.
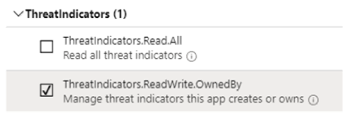
On the menu, select API Permissions > Add a permission.
On the Select an API page, select the Microsoft Graph API. Then choose from a list of Microsoft Graph permissions.
At the prompt What type of permissions does your application require?, select Application permissions. This permission is the type used by applications that authenticate with app ID and app secrets (API keys).
Select ThreatIndicators.ReadWrite.OwnedBy, and then select Add permissions to add this permission to your app's list of permissions.
Get consent from your organization to grant these permissions
To grant consent, a privileged role is required. For more information, see Grant tenant-wide admin consent to an application.
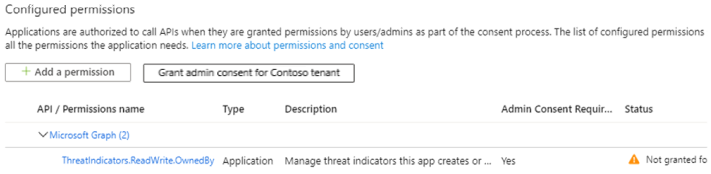
After consent is granted to your app, you should see a green check mark under Status.
After your app is registered and permissions are granted, you need to get a client secret for your app.
Go back to the main page of Microsoft Entra ID.
On the menu, select App Registrations, and then select your newly registered app.
On the menu, select Certificates & secrets. Then select New client secret to receive a secret (API key) for your app.
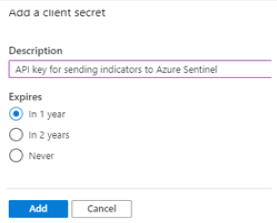
Select Add, and then copy the client secret.
Important
You must copy the client secret before you leave this screen. You can't retrieve this secret again if you go away from this page. You need this value when you configure your TIP or custom solution.
Input this information into your TIP solution or custom application
You now have all three pieces of information you need to configure your TIP or custom solution to send threat indicators to Microsoft Sentinel:
- Application (client) ID
- Directory (tenant) ID
- Client secret
Enter these values in the configuration of your integrated TIP or custom solution where required.
For the target product, specify Azure Sentinel. (Specifying Microsoft Sentinel results in an error.)
For the action, specify alert.
After the configuration is finished, threat indicators are sent from your TIP or custom solution, through the Microsoft Graph tiIndicators API, targeted at Microsoft Sentinel.
Enable the TIP data connector in Microsoft Sentinel
The last step in the integration process is to enable the TIP data connector in Microsoft Sentinel. Enabling the connector is what allows Microsoft Sentinel to receive the threat indicators sent from your TIP or custom solution. These indicators are available to all Microsoft Sentinel workspaces for your organization. To enable the TIP data connector for each workspace, follow these steps:
For Microsoft Sentinel in the Azure portal, under Content management, select Content hub.
For Microsoft Sentinel in the Defender portal, select Microsoft Sentinel > Content management > Content hub.Find and select the Threat Intelligence solution.
Select the
 Install/Update button.
Install/Update button.For more information about how to manage the solution components, see Discover and deploy out-of-the-box content.
To configure the TIP data connector, select Configuration > Data connectors.
Find and select the Threat Intelligence Platforms - BEING DEPRECATED data connector, and then select Open connector page.
Because you already finished the app registration and configured your TIP or custom solution to send threat indicators, the only step left is to select Connect.
Within a few minutes, threat indicators should begin flowing into this Microsoft Sentinel workspace. You can find the new indicators on the Threat intelligence pane, which you can access from the Microsoft Sentinel menu.
Related content
In this article, you learned how to connect your TIP to Microsoft Sentinel using a method on path for deprecation. To connect your TIP using the recommended method, see Connect your TIP with the upload API.
- Learn how to get visibility into your data and potential threats.
- Get started detecting threats with Microsoft Sentinel.