Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
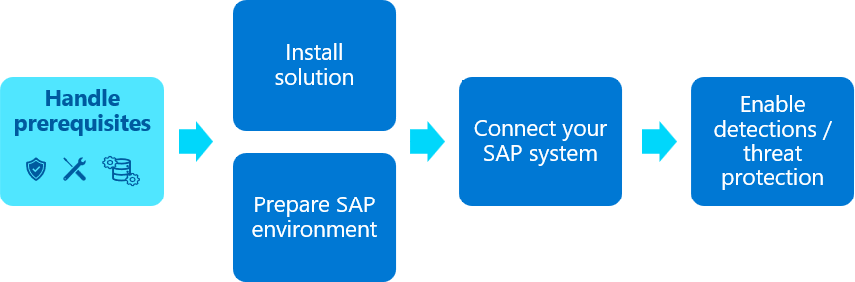
This article lists the prerequisites required for deployment of the Microsoft Sentinel solution for SAP applications, which differ depending on whether you're deploying a data connector agent or using the agentless data connector with the SAP Cloud Connector. Select the option at the top of this page that matches your deployment.
Reviewing and ensuring that you have or understand all the prerequisites is the first step in deploying the Microsoft Sentinel solution for SAP applications. Select a connection type to list the prerequisites for your environment.
Content in this article is relevant for your security, infrastructure, and SAP BASIS teams.

Content in this article is relevant for your security and SAP BASIS teams.
Important
Microsoft Sentinel's agentless data connector for SAP is currently in LIMITED PREVIEW. The Azure Preview Supplemental Terms include additional legal terms that apply to Azure features that are in beta, preview, or otherwise not yet released into general availability.
Azure prerequisites
Typically, Azure prerequisites are managed by your security teams.
| Prerequisite | Description | Required/optional |
|---|---|---|
| Access to Microsoft Sentinel | Make a note of your workspace ID and primary key for your Log Analytics workspace enabled for Microsoft Sentinel. You can find these details in Microsoft Sentinel: from the navigation menu, select Settings > Workspace settings > Agents management. Copy the Workspace ID and Primary key and paste them aside for use during the deployment process. |
Required |
| Permissions to create Azure resources | You must have the necessary permissions to deploy solutions from the Microsoft Sentinel content hub. You must also have an Owner role on the Microsoft Sentinel resource group, which is required for: - Creating the data collection rule and data collection endpoint. - Assigning the Monitoring Metrics Publisher role on the data collection rule. For more information, see Prerequisites for deploying Microsoft Sentinel solutions and Microsoft Entra built-in roles. |
Required |
| Permissions to create an Azure Key Vault or access an existing one | Use Azure Key Vault to store secrets required to connect to your SAP system. For more information, see Assign key vault access permissions. | Required if you plan to store the SAP system credentials in Azure Key Vault. Optional if you plan to store them in a configuration file. For more information, see Create a virtual machine and configure access to your credentials. |
| Permissions to assign a privileged role to the SAP data connector agent | Deploying the SAP data connector agent requires that you grant your agent's VM identity with specific permissions to the Microsoft Sentinel workspace, using the Microsoft Sentinel Business Applications Agent Operator role. To grant this role, you need Owner permissions on the resource group where your Microsoft Sentinel workspace resides. For more information, see Connect your SAP system by deploying your data connector agent container. |
Required. If you don't have Owner permissions on the resource group, the relevant step can also be performed by another user who does have the relevant permissions, separately after the agent is fully deployed. |
System prerequisites for the data connector agent container
Typically, system prerequisites are managed by your infrastructure teams.
| Prerequisite | Description |
|---|---|
| System architecture | The data connector component of the SAP solution is deployed as a Docker container. The container host can be either a physical machine or a virtual machine, can be located either on-premises or in any cloud. The VM hosting the container does not have to be located in the same Azure subscription as your Microsoft Sentinel workspace, or even in the same Microsoft Entra tenant. |
| Supported Linux versions | The SAP data connector agent is tested with the following Linux distributions: - Ubuntu 18.04 or higher - SLES version 15 or higher - RHEL version 7.7 or higher If you have a different operating system, you might need to deploy and configure the container manually. For more information, see Deploy the Microsoft Sentinel for SAP data connector agent container with expert options or open a support ticket. |
| Virtual machine sizing recommendations | Minimum specification, such as for a lab environment: Standard_B2s VM, with: - Two cores - 4-GB RAM Standard connector (default): Standard_D2as_v5 VM or Standard_D2_v5 VM, with: - Two cores - 8-GB RAM Multiple connectors: Standard_D4as_v5 or Standard_D4_v5 VM, with: - Four cores - 16-GB RAM |
| Administrative privileges | Administrative privileges (root) are required on the container host machine. |
| Network connectivity | Ensure that the container host has access to: - Microsoft Sentinel - Azure Key Vault (in deployment scenario where Azure Key Vault is used to store secrets - SAP system via the following TCP ports: 32xx, 5xx13, 33xx, 48xx (when SNC is used), where xx is the SAP instance number. |
| Software utilities | The SAP data connector deployment script installs the following required software on the container host VM (depending on the Linux distribution used, the list might vary slightly): - Unzip - NetCat - Docker - jq - curl |
| Managed identity or service principal | The latest version of the SAP data connector agent requires a managed identity or service principal to authenticate to Microsoft Sentinel. Legacy agents are supported for updates to the latest version, and then must use a managed identity or service principal to continue updating to subsequent versions. |
SAP prerequisites for the data connector agent container
We recommend that your SAP BASIS team verify and ensure SAP system prerequisites. We strongly recommend that any management of your SAP system is carried out by an experienced SAP system administrator.
| Prerequisite | Description |
|---|---|
| Supported SAP versions | The SAP data connector agent support SAP NetWeaver systems and was tested on SAP_BASIS versions 731 and above. Certain steps in this tutorial provide alternative instructions if you're working on the older SAP_BASIS version 740. |
| Required software | SAP NetWeaver RFC SDK 7.50 (Download here) Make sure that you also have an SAP user account in order to access the SAP software download page. |
| SAP system details | Make a note of the following SAP system details: - SAP system IP address and FQDN hostname - SAP system number, such as 00- SAP System ID, from the SAP NetWeaver system (for example, NPL) - SAP client ID, such as 001 |
| SAP NetWeaver instance access | The SAP data connector agent uses one of the following mechanisms to authenticate to the SAP system: - SAP ABAP user/password - A user with an X.509 certificate. This option requires extra configuration steps. For more information, see Configure your system to use SNC for secure connections. |
| SAP role requirements | To allow the SAP data connector to connect to your SAP system, you must create an SAP system role. We recommend creating the required system role by deploying the SAP NPLK900271 change request (CR). For more information, see Configure the Microsoft Sentinel role. |
| Recommended CRs for extra support | Deploy recommended CRs on your SAP system to retrieve extra details, such as client IP address and extra logs. For more information, see Configure support for extra data retrieval (recommended). |
Sign up for limited preview
To use the agentless data connector for SAP, sign up for the limited preview.
Azure prerequisites
Typically, Azure prerequisites are managed by your security teams.
| Prerequisite | Description | Required/optional |
|---|---|---|
| Permissions to create Azure resources | You must have: - The necessary permissions to deploy solutions from the Microsoft Sentinel content hub. For more information, see Prerequisites for deploying Microsoft Sentinel solutions and Microsoft Entra built-in roles. Owner on the Microsoft Sentinel resource group, required for: - Creation of data collection rule and data collection endpoint. - Monitoring Metrics Publisher role assignment on data collection rule. |
Required |
| Read permissions to shared keys for the workspace | For more information, see Install Log Analytics agent on Windows computers. | Required |
| Permissions in Microsoft Entra | You must have permissions in Microsoft Entra ID required to create app registrations. This permission can be obtained through membership of built-in Microsoft Entra ID role: - Application Developer. |
Required |
SAP prerequisites for the agentless data connector
We recommend that your SAP BASIS team verify and ensure SAP system prerequisites. The SAP BASIS admin should review SAP notes 3390051 and 382318 to ensure that NetWeaver is set up for integration.
We strongly recommend that any management of your SAP system is carried out by an experienced SAP system administrator.
| Prerequisite | Description |
|---|---|
| Supported SAP versions | The Agentless solution supports SAP NetWeaver systems with SAP_BASIS versions 750 and above. Change Docs logs running on Sybase aren't supported. If you're using Sybase, we recommend that you customize your system to turn off ingestion for Change Docs logs. For more information, see Customize data connector behavior (optional). |
| SAP environment | Your SAP environment must have: The RSAU_API_GET_LOG_DATA function module, remote enabled on your SAP System. For more information, see the SAP documentation. An SAP BTP Subaccount with following services enabled: - SAP Integration Suite - SAP Process Integration Runtime - Cloud Foundry Runtime For more information, see the SAP documentation. Trial accounts are supported. The SAP Cloud Connector deployed SAP NetWeaver version 7.5 or higher |
| SAP roles and permissions | You must have the following roles in your SAP systems: In SAP NetWeaver 7.5+: SAP Netweaver Administrator In SAP BTP, all of the following roles: - Subaccount administrator - Integration Provisioner - PI_Administrator - PI_Integration_Developer - PI_Business_Expert |
Plan your ingestion
We recommend that you test your systems to determine the number of logs that each of your SAP systems sends to Microsoft Sentinel. Microsoft Sentinel billing depends on log ingestion size, which in turn depends on factors such as system usage, modules deployed, number of users, running use cases, network traffic, and log types.
For more information, see:
- Solution pricing
- Plan costs and understand Microsoft Sentinel pricing and billing
- Reduce costs for Microsoft Sentinel
- Manage and monitor costs for Microsoft Sentinel