Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
In this tutorial, you learn how to use Service Connector to connect an Azure Storage account to a pod in an Azure Kubernetes Service (AKS) cluster using workload identity. You complete the following tasks:
- Create an AKS cluster and an Azure Storage account.
- Create a connection between the AKS cluster and the Azure Storage account using Service Connector.
- Clone a sample application that connects to the Azure Storage account from the AKS cluster.
- Deploy the application to a pod in the AKS cluster and test the connection.
- Clean up resources.
Prerequisites
- Basic understanding of containers, workload identity, and AKS. For more information, see Tutorial: Prepare an application for Azure Kubernetes Service (AKS).
- An Azure subscription where you have Azure resource write permissions, in an Azure region that supports Service Connector and has sufficient AKS support and compute quota to run the tutorial. Create an account for free.
- The
Microsoft.ServiceLinker,Microsoft.ContainerService,Microsoft.ContainerRegistry, andMicrosoft.ManagedIdentityresource providers registered in the Azure subscription. You can runaz provider register -n Microsoft.[service]to register the providers. - Git to access and clone the sample repo.
- Docker and kubectl installed to manage container image and Kubernetes resources. Install
kubectllocally by runningaz aks install-cli. - Azure CLI installed.
Create Azure resources
Sign in to Azure by running az login and following the prompts.
Create an Azure resource group to use for this tutorial, replacing the
<region>placeholder with a valid value. Thelocationmust be an Azure region where your subscription has sufficient compute quota for the Azure resources and no restrictions on any of the services.az group create \ --name MyResourceGroup \ --location <region>Create an AKS cluster to contain the service connection, pod definition, and sample application by running the following command. For more information, see Quickstart: Deploy an Azure Kubernetes Service (AKS) cluster using Azure CLI.
az aks create \ --resource-group MyResourceGroup \ --name MyAKSCluster \ --enable-managed-identity \ --node-count 1Connect to the cluster by running the following command.
az aks get-credentials \ --resource-group MyResourceGroup \ --name MyAKSClusterCreate an Azure Storage account to be the target service that the AKS cluster connects to and the sample application interacts with. For more information, see Create an Azure storage account. Run the following command, replacing
<storageaccountname>with a name that is 3-24 lowercase or numeric characters and is unique across Azure.az storage account create \ --resource-group MyResourceGroup \ --name <storageaccountname> \ --sku Standard_LRSCreate an Azure container registry to host the application container image consumed by the AKS pod definition. For more information, see Quickstart: Create an Azure container registry by using the Azure portal. Run the following command, replacing
<registryname>with a name that is 5-50 lowercase or numeric characters and is unique across Azure.az acr create \ --resource-group MyResourceGroup \ --name <registryname> \ --sku StandardEnable anonymous pull so the AKS cluster can consume the registry images. Replace the
<registryname>placeholder with your registry name.az acr update \ --resource-group MyResourceGroup \ --name <registryname> \ --anonymous-pull-enabledRun the following command to create a user-assigned managed identity that the service connection creation can use to enable workload identity for AKS workloads. For more information, see Manage user-assigned managed identities using the Azure portal.
az identity create \ --resource-group MyResourceGroup \ --name MyIdentity
Create a service connection using Service Connector
Create a service connection between the AKS cluster and the Azure Storage account by using Azure CLI or the Azure portal.
Run the following Azure CLI command to create a service connection to the Azure storage account. Replace <storageaccountname> with your storage account name and <user-identity-resource-id> with your user-assigned managed identity resource ID.
You can get your user-assigned managed identity resource ID from the output of the preceding az identity create command, or use the format /subscriptions/<subscription-id>/resourceGroups/MyResourceGroup/providers/Microsoft.ManagedIdentity/userAssignedIdentities/MyIdentity.
az aks connection create storage-blob \
--resource-group MyResourceGroup \
--name MyAKSCluster \
--target-resource-group MyResourceGroup \
--account <storageaccountname> \
--workload-identity <user-identity-resource-id>
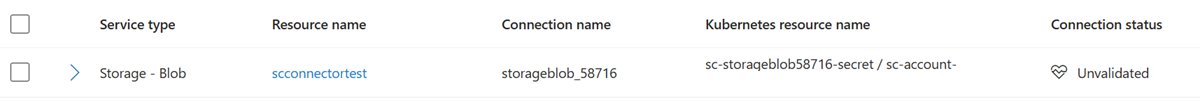
Once the connection is created, the Azure portal Service Connector page shows information about the new connection. You can use this information when you edit the pod.yaml file later in this tutorial.
Create the sample application
Clone the sample repository, and then change to the directory that contains the sample app. Run the remaining commands from this folder.
git clone https://github.com/Azure-Samples/serviceconnector-aks-samples.git cd serviceconnector-aks-samples/azure-storage-workload-identityBuild and push the images to your container registry using the
az acr buildcommand. Replace the<registryname>placeholder with your registry name.az acr build --registry <registryname> --image sc-demo-storage-identity:latest ./View the image in your container registry using the
az acr repository listcommand. Replace the<registryname>placeholder with your registry name.az acr repository list --name <registryname> --output table
Run application and test connection
Replace the following placeholders in the pod.yaml file in your local app folder:
<YourContainerImage>: Replace with the image name in your container registry, for example<registryname>.azurecr.io/sc-demo-storage-identity:latest.<ServiceAccountCreatedByServiceConnector>: Replace with the service account Service Connector created after connection creation. You can check the service account name on your AKS cluster Service Connector page in the Azure portal.<SecretCreatedByServiceConnector>: Replace with the secret Service Connector created after connection creation. You can check the service account name on your AKS cluster Service Connector page in the Azure portal.
Deploy the pod to your cluster using
kubectl apply. The command creates a pod namedsc-demo-storage-identityin the default namespace of your AKS cluster.kubectl apply -f pod.yamlCheck that the deployment is successful by viewing the pod using
kubectl.kubectl get pod/sc-demo-storage-identityCheck that the connection is established by viewing the logs using
kubectl.kubectl logs pod/sc-demo-storage-identity
Clean up resources
If you no longer need the Azure resources you created for this tutorial, you can delete them by deleting the MyResourceGroup resource group.
az group delete \
--resource-group MyResourceGroup