Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
For complete protection of your on-premises deployment, we recommend activating the Defender for Identity sensor on all applicable servers. This article describes onboarding for domain controllers running Windows Server 2019 or later, including domain controllers that also run AD FS, AD CS, or Microsoft Entra Connect roles. For domain controllers running older operating systems, or AD FS, AD CS, and Microsoft Entra Connect servers, we recommend deploying the Defender for Identity sensor v2.x.
Prerequisites
See Microsoft Defender for Identity sensor v3.x prerequisites for all system requirements before proceeding with activating the sensor.
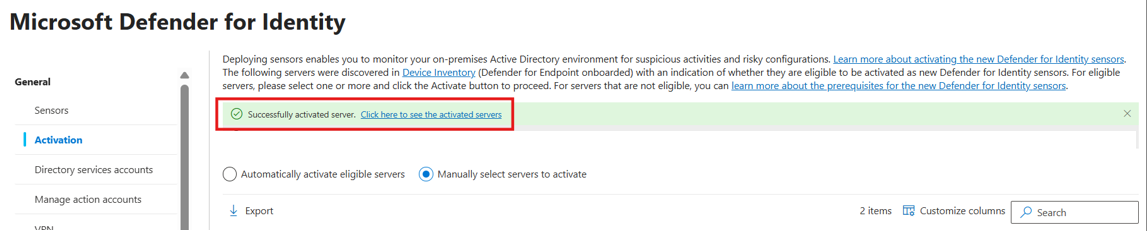
The Activation page
The Activation page displays all servers from your device inventory. Defender for Identity detects all of your servers and their configuration. The server's activation state lets you know what you need to do to onboard the domain controller to Defender for Identity.
You can choose to activate eligible domain controllers either automatically, where Defender for Identity activates them as soon as they're discovered, or manually, by selecting specific domain controllers from the list of eligible servers.
| Activation State | Next steps |
|---|---|
| Activate new sensor | The domain controller is already onboarded to Defender for Endpoint. Activate the sensor. |
| Install classic sensor | Deploy the classic Defender for Identity sensor from the Sensors page. |
| OS upgrade is required | This domain controller is running an unsupported operating system version for the new sensor. Upgrade the OS version to the latest version. |
Activate the Defender for Identity sensor
In the Microsoft Defender portal, go to System > Settings > Identities > Activation.
Select the domain controller where you want to activate Defender for Identity, and select Activate. Confirm your selection when prompted.
When the activation is complete, a green success banner shows. In the banner, select Click here to see the onboarded servers. This takes you to the Sensors page, where you can check your sensor health.
Confirm sensor activation
To confirm the sensor is working:
- In the Microsoft Defender portal, go to System > Settings > Identities > Sensors.
- Check that the activated domain controller is listed.
Note
The first time you activate the Defender for Identity sensor on your domain controller, it might take up to an hour for the first sensor to show as Running on the Sensors page. Subsequent activations are shown within five minutes. The activation doesn't require a restart/reboot.