Sign in users for a sample ASP.NET Core web app in an external tenant
This how-to guide uses a sample ASP.NET Core web application to show the fundamentals of modern authentication using the Microsoft Authentication Library for .NET and Microsoft Identity Web for ASP.NET Core to handle authentication.
In this article, you'll register a web application in the Microsoft Entra admin center and create a sign in and sign out user flow. You'll associate your web application with the user flow, download and update a sample ASP.NET Core web application using your own external tenant details. Finally, you'll run and test the sample web application.
Prerequisites
- Although any IDE that supports ASP.NET Core applications can be used, Visual Studio Code is used for this guide. It can be downloaded from the Downloads page.
- .NET 7.0 SDK.
- An external tenant. To create one, choose from the following methods:
- (Recommended) Use the Microsoft Entra External ID extension to set up an external tenant directly in Visual Studio Code.
- Create a new external tenant in the Microsoft Entra admin center.
Register the web app
To enable your application to sign in users with Microsoft Entra, Microsoft Entra External ID must be made aware of the application you create. The app registration establishes a trust relationship between the app and Microsoft Entra. When you register an application, External ID generates a unique identifier known as an Application (client) ID, a value used to identify your app when creating authentication requests.
The following steps show you how to register your app in the Microsoft Entra admin center:
Sign in to the Microsoft Entra admin center as at least an Application Developer.
If you have access to multiple tenants, use the Settings icon
 in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.Browse to Identity >Applications > App registrations.
Select + New registration.
In the Register an application page that appears;
- Enter a meaningful application Name that is displayed to users of the app, for example ciam-client-app.
- Under Supported account types, select Accounts in this organizational directory only.
Select Register.
The application's Overview pane displays upon successful registration. Record the Application (client) ID to be used in your application source code.
Define the platform and URLs
To specify your app type to your app registration, follow these steps:
- Under Manage, select Authentication.
- On the Platform configurations page, select Add a platform, and then select Web option.
- For the Redirect URIs enter
https://localhost:7274/signin-oidc. - Under Front-channel logout URL, enter
https://localhost:7274/signout-callback-oidcfor signing out. - Select Configure to save your changes.
Enable implicit and hybrid flows
The application you build uses the implicit flow, which needs to be enabled.
- Under the Implicit grant and hybrid flows section, select the ID tokens option.
- Select Save.
Add app client secret
Create a client secret for the registered application. The application uses the client secret to prove its identity when it requests for tokens.
- From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
- Under Manage, select Certificates & secrets.
- Select New client secret.
- In the Description box, enter a description for the client secret (for example, ciam app client secret).
- Under Expires, select a duration for which the secret is valid (per your organizations security rules), and then select Add.
- Record the secret's Value. You'll use this value for configuration in a later step. The secret value won't be displayed again, and isn't retrievable by any means, after you navigate away from the Certificates and secrets. Make sure you record it.
Grant admin consent
Once you register your application, it gets assigned the User.Read permission. However, since the tenant is an external tenant, the customer users themselves can't consent to this permission. You as the admin must consent to this permission on behalf of all the users in the tenant:
From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
Under Manage, select API permissions.
- Select Grant admin consent for <your tenant name>, then select Yes.
- Select Refresh, then verify that Granted for <your tenant name> appears under Status for the permission.
Create a user flow
Follow these steps to create a user flow a customer can use to sign in or sign up for an application.
Sign in to the Microsoft Entra admin center as at least an External ID User Flow Administrator.
If you have access to multiple tenants, use the Settings icon
 in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.Browse to Identity > External Identities > User flows.
Select + New user flow.
On the Create page:
Enter a Name for the user flow, such as SignInSignUpSample.
In the Identity providers list, select Email Accounts. This identity provider allows users to sign-in or sign-up using their email address.
Under Email accounts, you can select one of the two options. For this tutorial, select Email with password.
- Email with password: Allows new users to sign up and sign in using an email address as the sign-in name and a password as their first factor credential.
- Email one-time-passcode: Allows new users to sign up and sign in using an email address as the sign-in name and email one-time passcode as their first factor credential. Email one-time passcode must be enabled at the tenant level (All Identity Providers > Email One-time-passcode) for this option to be available at the user flow level.
Under User attributes, choose the attributes you want to collect from the user upon sign-up. By selecting Show more, you can choose attributes and claims for Country/Region, Display Name, and Postal Code. Select OK. (Users are only prompted for attributes when they sign up for the first time.)
Select Create. The new user flow appears in the User flows list. If necessary, refresh the page.
To enable self-service password reset, use the steps in Enable self-service password reset article.
Associate the web application with the user flow
For the customer users to see the sign-up or sign-in experience when they use your app, you need to associate your app with a user flow. Although many applications can be associated with your user flow, a single application can only be associated with one user flow.
On the sidebar menu, select Identity.
Select External Identities, then User flows.
In the User flows page, select the User flow name you created earlier, for example, SignInSignUpSample.
Under Use, select Applications.
Select Add application.
Select the application from the list such as ciam-client-app or use the search box to find the application, and then select it.
Choose Select.
Once you associate your app with a user flow, you can test your user flow by simulating a user’s sign-up or sign-in experience with your application from within the Microsoft Entra admin center. To do so, use the steps in Test your sign-up and sign-in user flow.
Clone or download sample web application
To obtain the sample application, you can either clone it from GitHub or download it as a .zip file.
To clone the sample, open a command prompt and navigate to where you wish to create the project, and enter the following command:
git clone https://github.com/Azure-Samples/ms-identity-ciam-dotnet-tutorial.gitDownload the .zip file. Extract it to a file path where the length of the name is fewer than 260 characters.
Configure the application
Navigate to the root folder of the sample you have downloaded and directory that contains the ASP.NET Core sample app:
cd 1-Authentication\1-sign-in-aspnet-core-mvcOpen the appsettings.json file.
In Authority, find
Enter_the_Tenant_Subdomain_Hereand replace it with the subdomain of your tenant. For example, if your tenant primary domain is caseyjensen@onmicrosoft.com, the value you should enter is casyjensen.Find the
Enter_the_Application_Id_Herevalue and replace it with the application ID (clientId) of the app you registered in the Microsoft Entra admin center.Replace
Enter_the_Client_Secret_Herewith the client secret value you set up in Add app client secret.
Run the code sample
From your shell or command line, execute the following commands:
dotnet runOpen your web browser and navigate to
https://localhost:7274.Sign-in with an account registered to the external tenant.
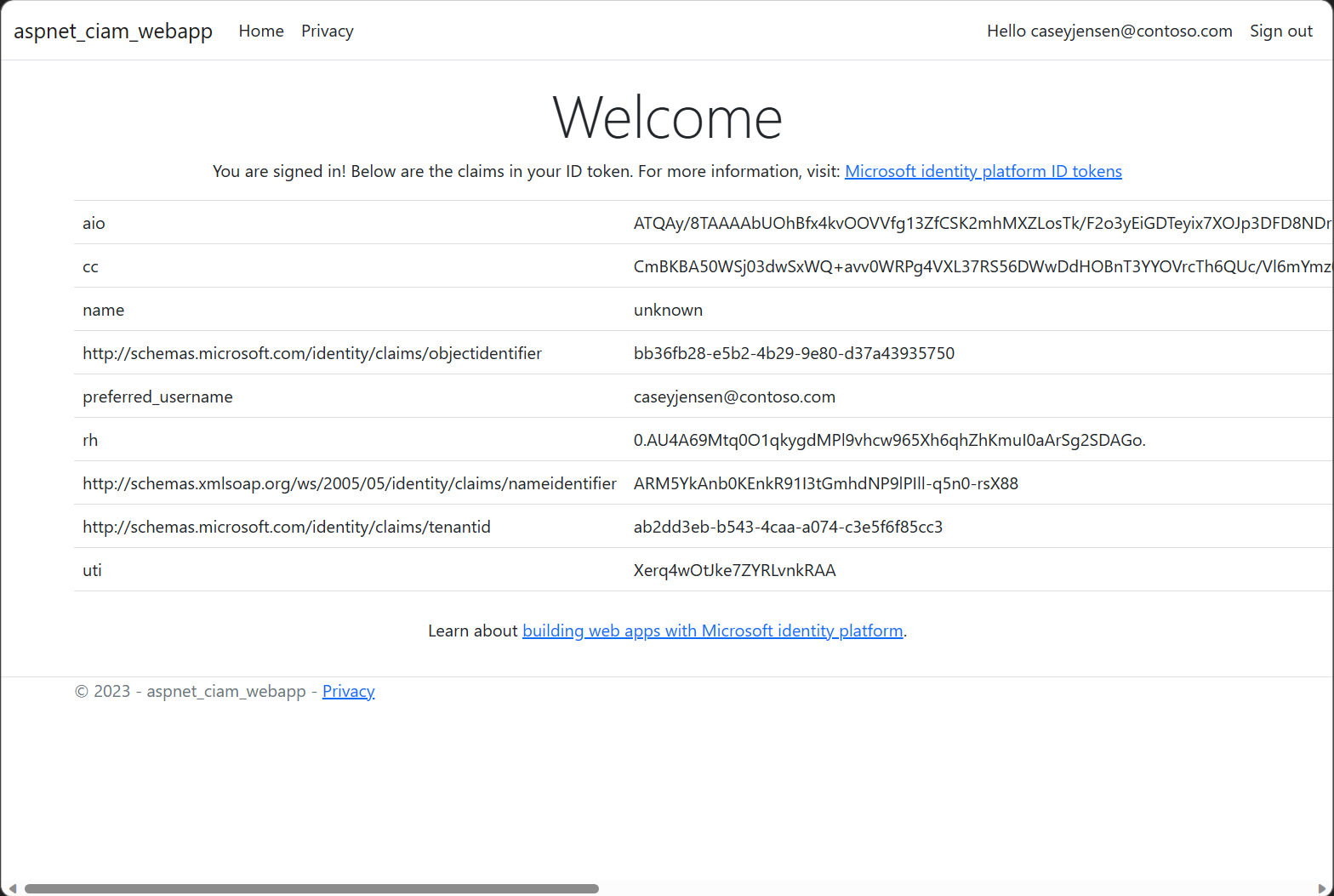
Once signed in the display name is shown next to the Sign out button as shown in the following screenshot.
To sign out from the application, select the Sign out button.