Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Okta SSO Implementation Overview
This document outlines the necessary steps for LinkedIn Learning administrators to set up Single Sign-on with Okta. The Okta/LinkedIn Learning SAML integration currently supports the following features:
- IdP-initiated SSO
- SP-initiated SSO
- JIT (Just In Time) Provisioning
- Automated user management with SCIM
Prerequisites
To get started, you need the following:
- An Okta account
- A LinkedIn Learning enterprise account
- Full administrator privileges in both platforms
Configure Okta connection in LinkedIn Learning
To configure Okta as your organization's IdP, take the following steps:
After you log in, if you are not already in the Admin screen, select Go to Admin, then navigate to Authentication.

From the side navigation menu, select Configure single sign-on and click on Add new SSO.
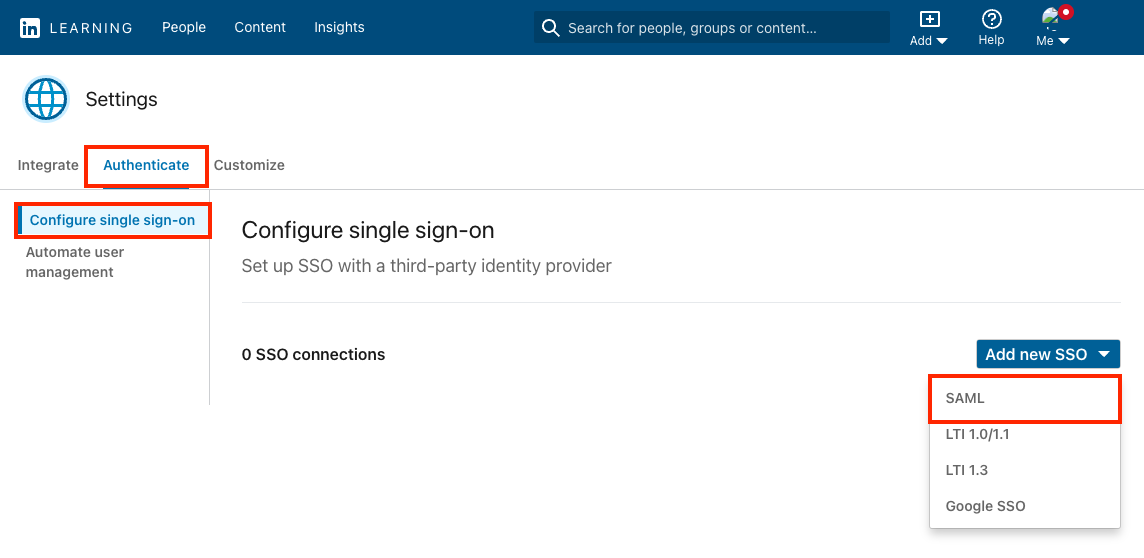
Select SAML.
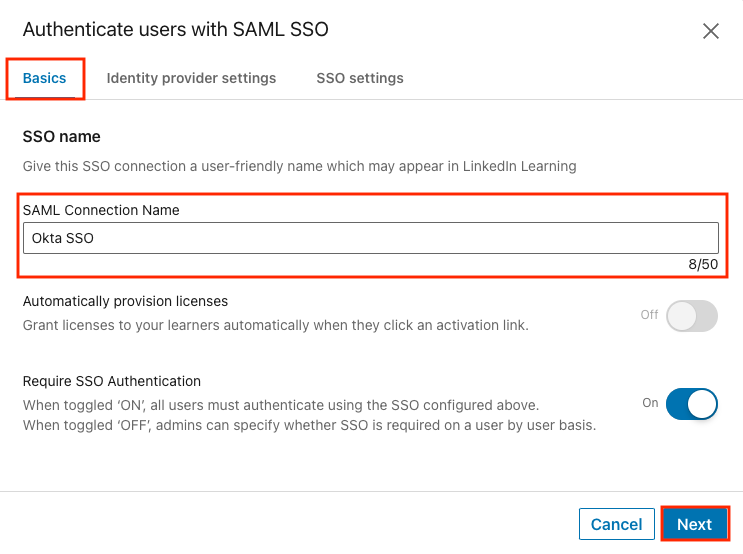
On the Basics tab, give your SSO connection a name and click Next.
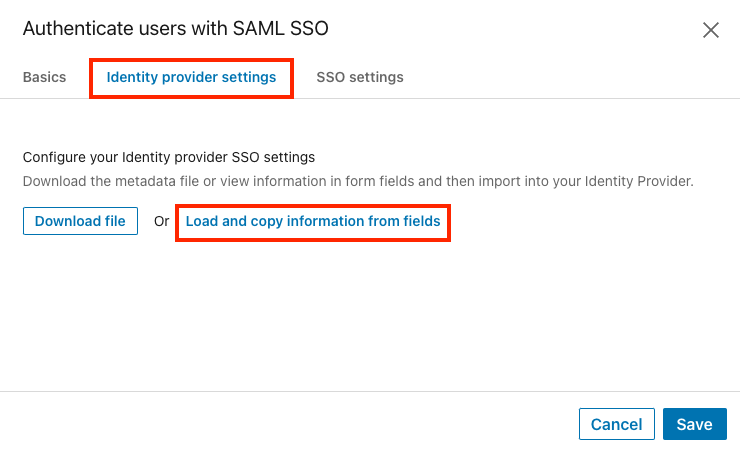
On the Identity provider settings tab, click Load and copy information from fields.
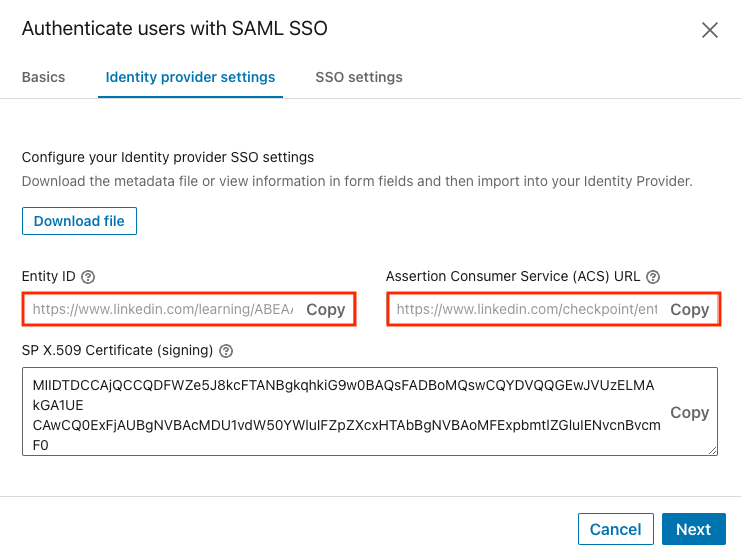
Copy the Entity ID and Assertion Consumer Service (ACS) URL values and paste them into a text document or keep this tab open. These values will be used in the next section to configure the application in Okta.
Configure LinkedIn Learning Application in Okta
To configure Single Sign-on for LinkedIn Learning, you should create a SAML 2.0 App Integration in Okta. There is an older LinkedIn Learning application available in the Okta catalog that does not support SCIM provisioning or custom attributes, so make sure you do not choose that application.
Open Okta in a new tab, navigate to the Admin section and choose Applications.
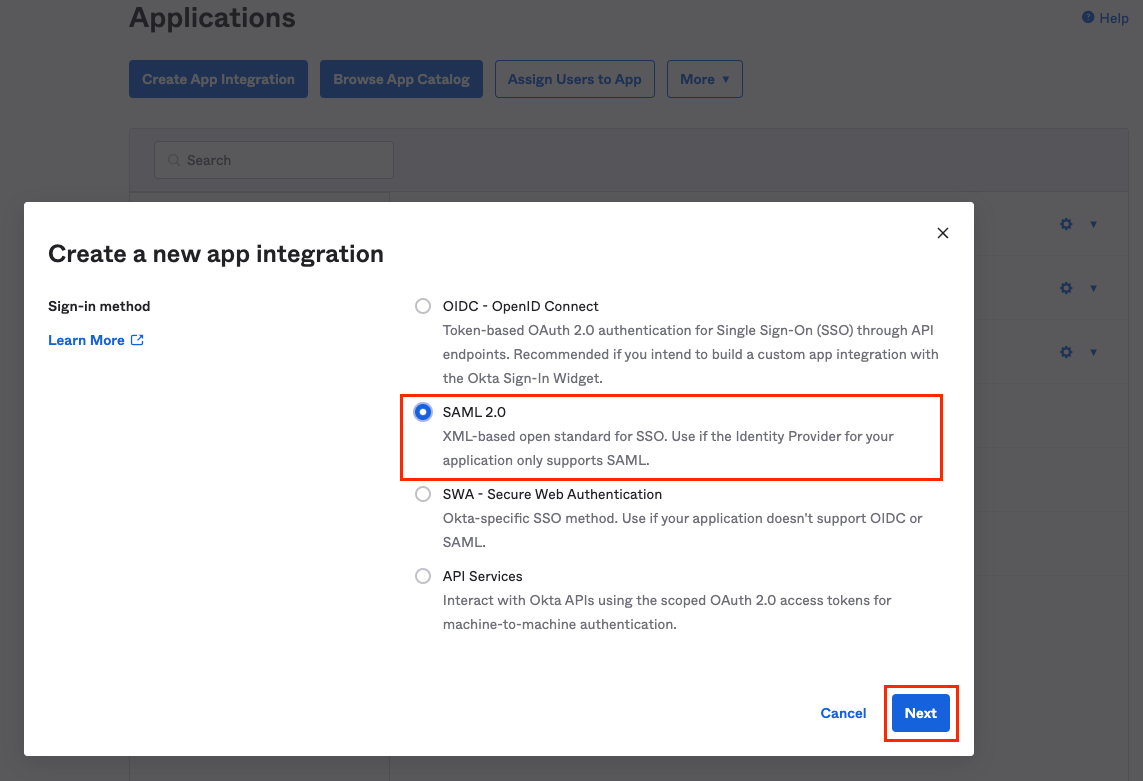
Click on Create App Integration and select SAML 2.0. Click Next.
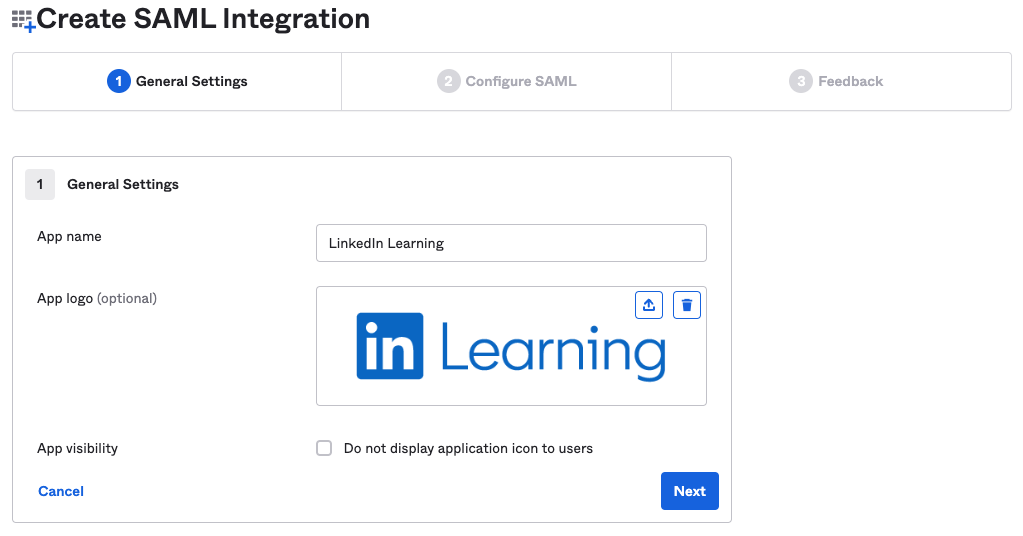
Give your app integration a name and upload a logo. LinkedIn Learning logos can be downloaded here, or you can use the image below. Click Next.
In the Configure SAML settings for the application, Paste the ACS URL from the previous section into the Single sign-on URL field. The "Use this for Recipient URL and Destination URL" option should be selected.
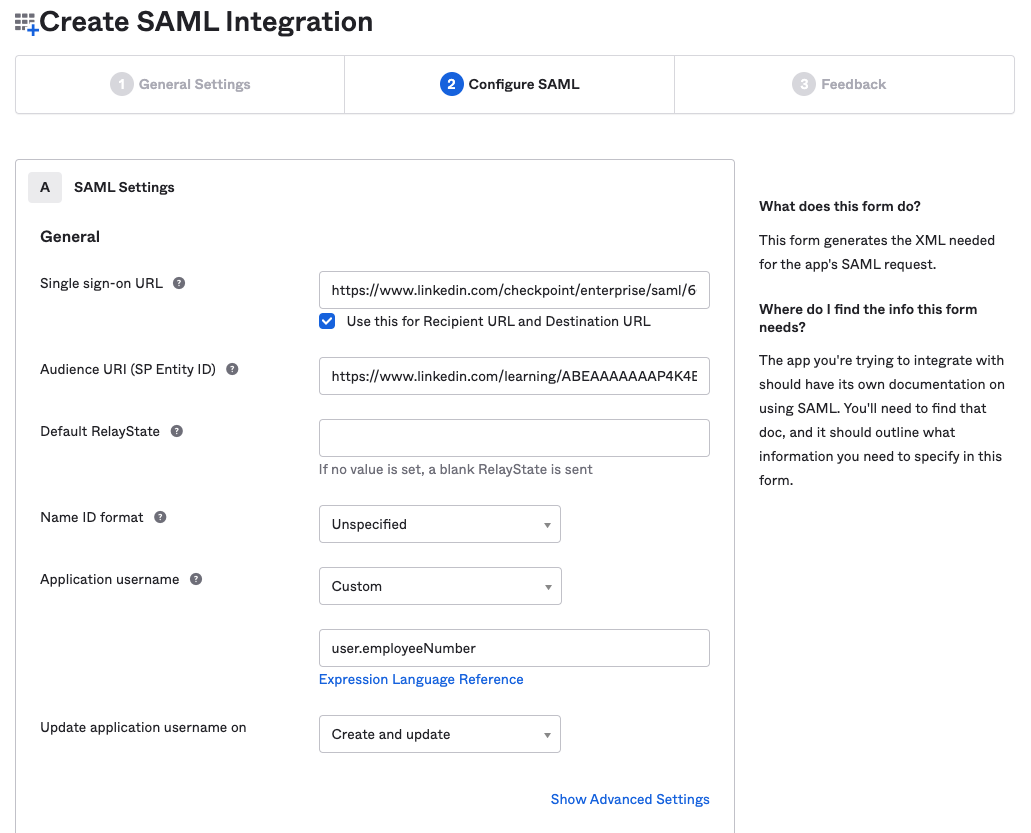
Paste the Entity ID from the previous section into the Audience URI (SP Entity ID) field.
Set the Application username to a unique, immutable user attribute. By default, this value is set to Okta username. If Okta Username values have the potential to change at your organization, you may want to change this identifier to user.employeeNumber or some other user attribute.
Note
If you are also integrating LinkedIn Learning into a Learning Management System, this value needs to match the User ID value in your LMS to ensure completion tracking.
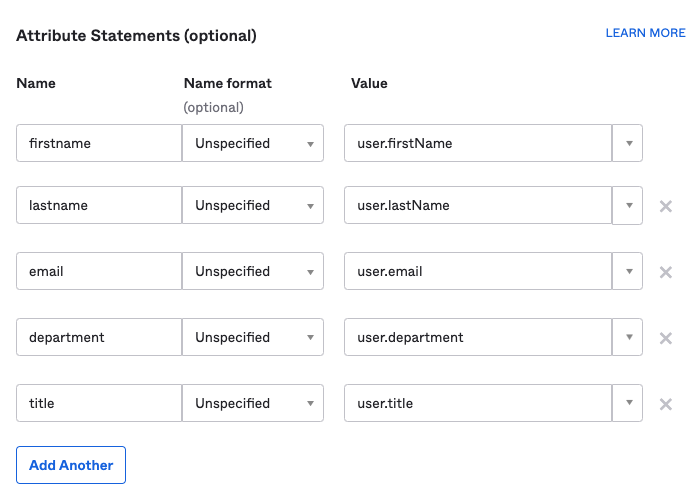
Scroll down to the Attribute Statements section. Add any user attributes you would like to include in the SAML assertion. At minimum, we recommend including firstname, lastname and email. There is no limit to the number of attributes you can include.
Click Next at the bottom of the page.
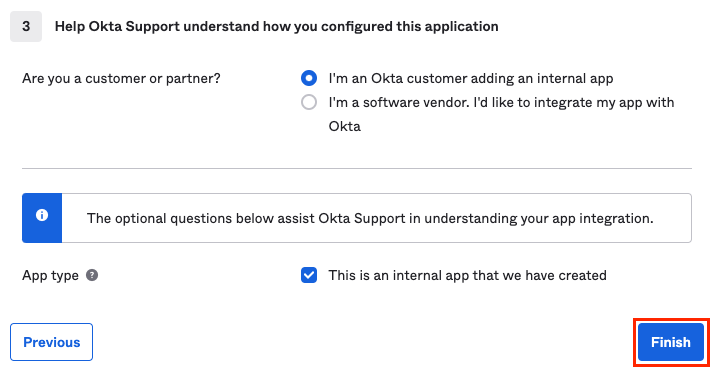
Answer the optional Feedback questions and click Finish.
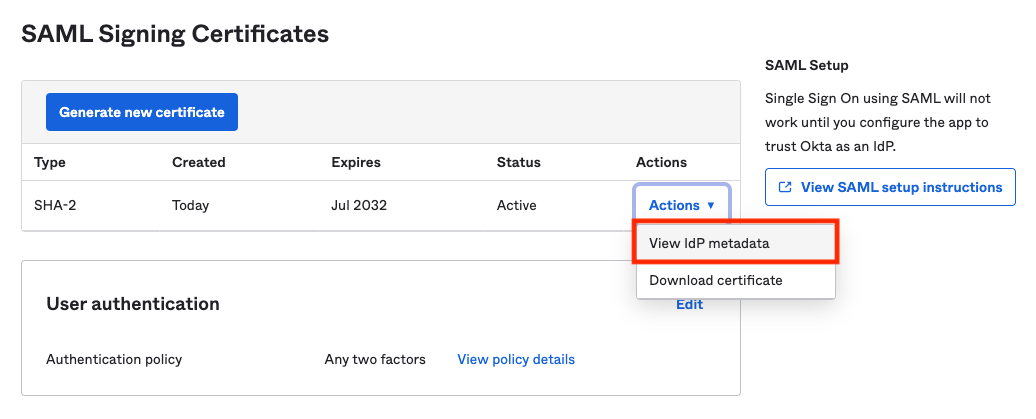
On the application's Sign On tab, scroll down to the SAML Signing Certificates section and locate the SHA-2 certificate. Click on Actions and select View IdP metadata.
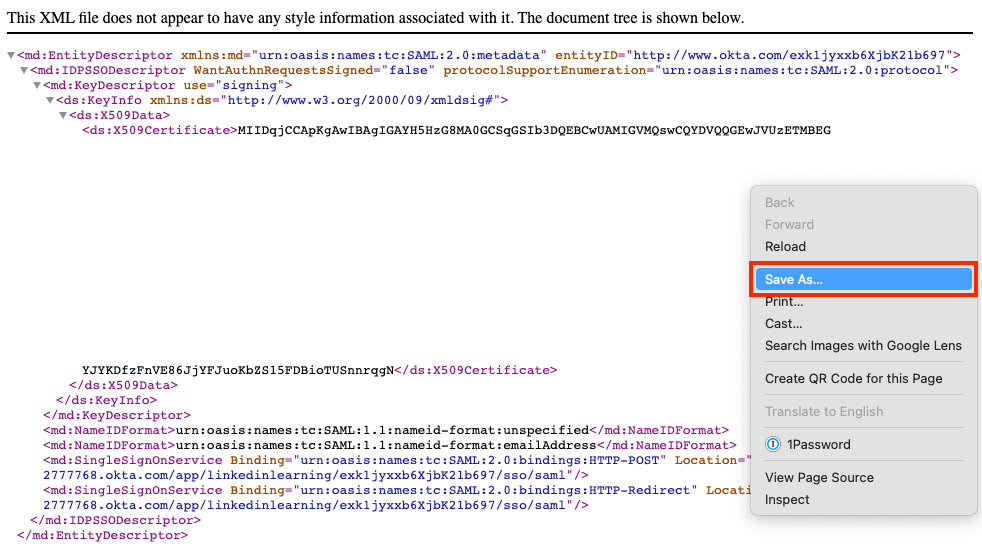
Right click on the page displaying the metadata and choose Save As. Save the file to your computer. This will be used in the next section to finish configuring the SSO connection in LinkedIn Learning.
Activate Okta connection in LinkedIn Learning
Return to the LinkedIn Learning admin tab in your browser.
On the SSO settings tab, click Upload XML file. Navigate to the metadata file you just downloaded on your computer, and upload the file to LinkedIn Learning.
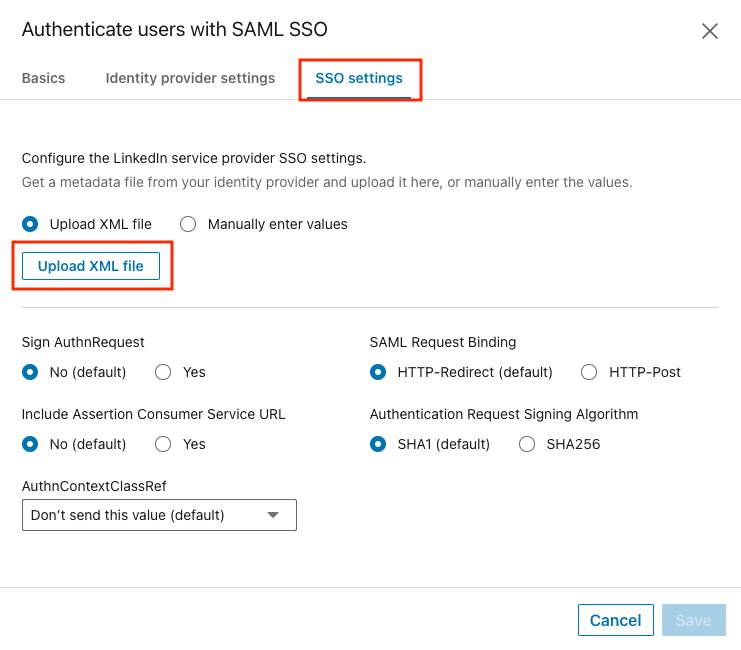
Click Save.
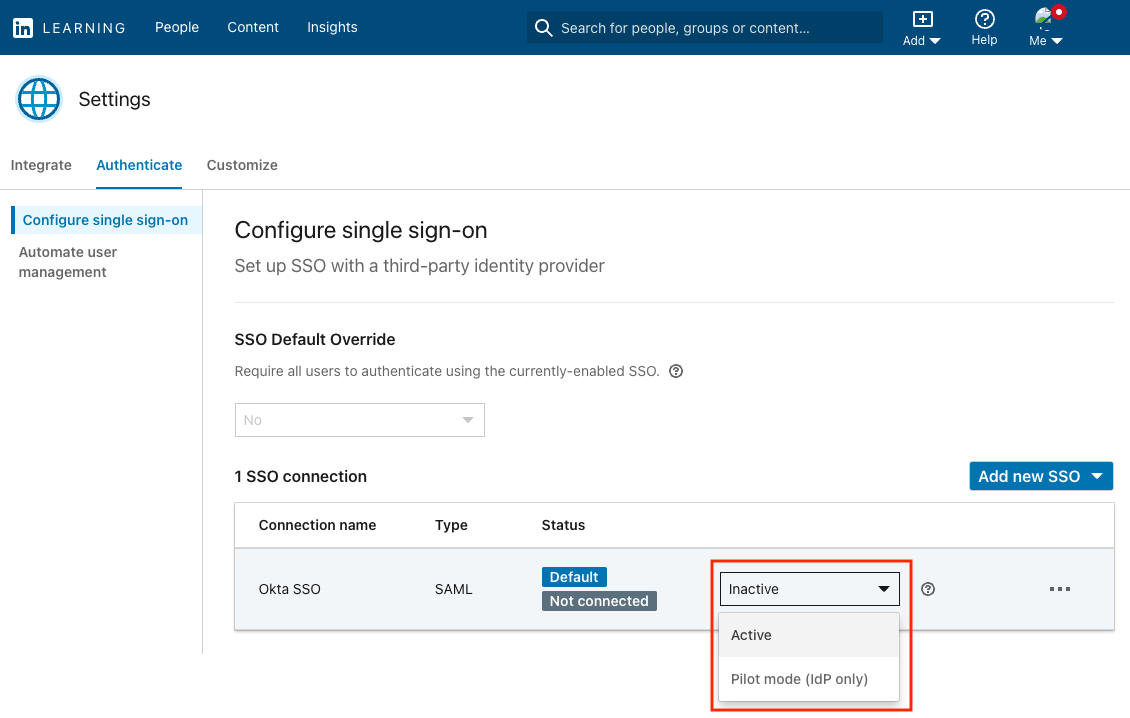
On the SSO configuration screen, activate your SSO connection by selecting Active from the drop down, then click Activate on the subsequent screen.
Verify your SSO
To validate your SSO configuration and invite learners, take the following steps:
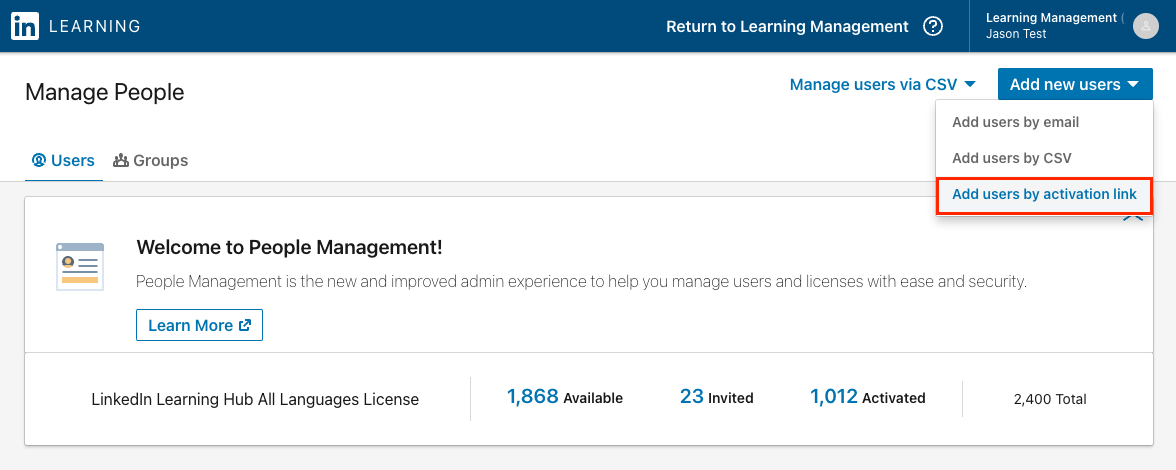
In the LinkedIn Learning admin interface, click on the People tab.
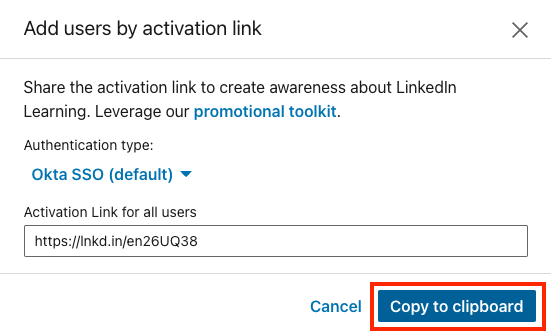
Click on Add new users and select Add users by activation link.
Copy the activation link and paste it into your browser. This will trigger a Service Provider-initiated authentication flow. This link can be sent to anyone who has been assigned the LinkedIn Learning application in Okta.
Connecting your LinkedIn profile to Learning
LinkedIn Learning allows learners to connect their personal LinkedIn profile to their organization's LinkedIn Learning account. This step, known as profile binding, allows LinkedIn Learning to surface content that aligns with your learners' goals and interests.
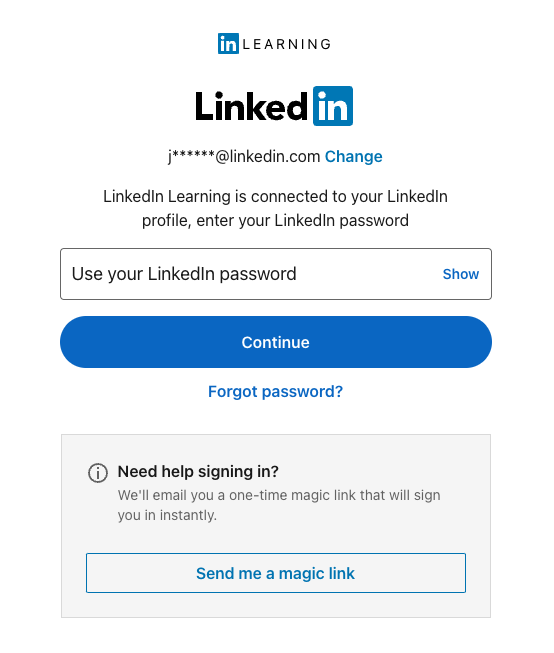
If you see the below login screen while testing SSO, it does not mean SSO is broken. It simply means you need to re-login to LinkedIn.com with your personal profile credentials, separate from your organization SSO.
Congratulations! Your learners now can access LinkedIn Learning via their Okta IdP instance.
Configure Automatic User Provisioning
Okta allows for automated provisioning in LinkedIn Learning to automate management of LinkedIn Learning licenses, user attributes and user group membership(s). Provisioning can be enabled in the same Okta SAML 2.0 application you just created. To configure automatic provisioning, follow the instructions in this document: Configure SCIM Automated User Management - Okta
If you are new to LinkedIn Learning and have not launched to your user base yet, make sure to only provision the application to the administrators and/or test group who should have access prior to your official launch.
Support
Below you can find supporting documentation and other resources.
Supporting Documentation
Technical Issues
If you have technical issues with the SSO setup, contact your account team or application support team through the LinkedIn Learning Help Center.
LinkedIn's Privacy and Data Security Policy
https://www.linkedin.com/legal/privacy-policy
LinkedIn Security Contacts
If you have any security questions or you would like to report a security issue, write to us at security@linkedin.com.