Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Being able to easily share files and documents with the right people while preventing oversharing is key to an organization's success. This includes being able to share confidential or other sensitive data safely with only those who should have access to it. Depending on the project, this might include sharing sensitive data with people outside your organization.
This guidance includes components to help you:
- Deploy Teams with the right level of protection for each project
- Configure external sharing with appropriate security settings for each project
If versatile and easy-to-use file collaboration tools aren't available, users will often collaborate by emailing documents. This is a tedious and error-prone method of collaboration, and can increase the risk of inappropriate sharing of information. If people find sharing files too difficult, they could revert to using consumer products that aren't governed by IT. This can pose an even greater risk.
With Microsoft 365, you can deploy Teams with various configurations that help:
- Protect your intellectual property
- Enable easy collaboration with documents and other files
- Create a balance between security and usability that increases user satisfaction and reduces the risk of shadow IT
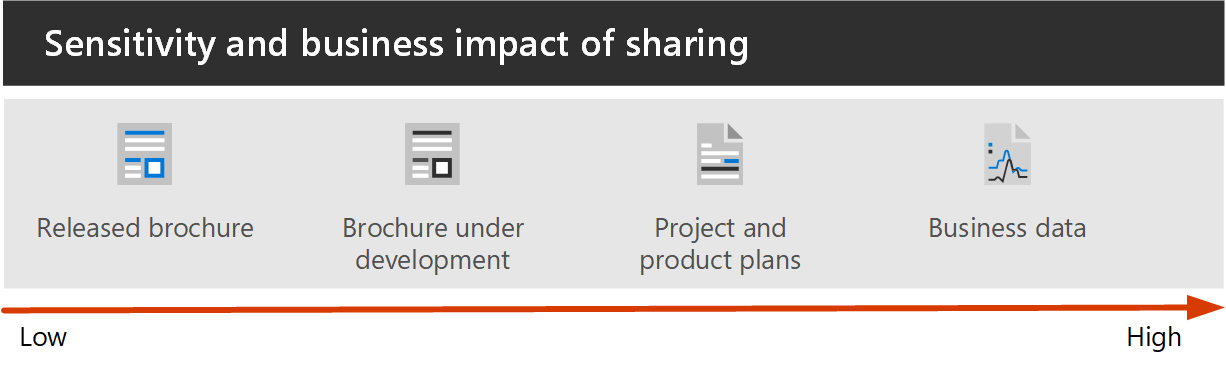
Most organizations have a variety of information, with varying degrees of sensitivity and varying degrees of business impact if the information is inappropriately shared. Depending on the sensitivity of a given piece of information, you may want to allow sharing with:
- Anyone (unauthenticated)
- People inside the organization
- Specific people inside the organization
- Specific people inside and outside the organization
Information such as marketing brochures are meant for sharing broadly outside the organization. Information such as cafeteria menus aren't meant for external sharing, but would have no business impact if they were shared externally. These types of information need little or no protection.
Those same marketing brochures, while under development, might only be shared inside the organization. In this case, the default sharing settings in Teams may be sufficient.
Information about a new product that is under development might be considered sensitive, even within the organization. A greater degree of protection might be appropriate in this case. You could restrict access to this information to members of a specific team, for example. Depending on the project, you may need to collaborate with people outside your organization, such as a vendor or partner organization.
Information that is critical to your organization's success, or has stringent security or compliance requirements might require even greater levels of protection.
For all the scenarios noted above, you can use Teams to store, share, and collaborate on the information.
To configure secure collaboration, use these Microsoft 365 capabilities and features:
| Product or component | Capability or feature | Licensing |
|---|---|---|
| Microsoft Defender for Office 365 | Safe Attachments for SharePoint, OneDrive and Microsoft Teams; Safe Documents; Safe Links for Teams | Microsoft 365 E1, E3 and E5 |
| SharePoint | Site and file sharing policies, Site sharing permissions, Sharing links, Access requests, Site guest sharing settings | Microsoft 365 E1, E3 and E5 |
| Microsoft Teams | Guest access, private teams, private channels, shared channels | Microsoft 365 E3 and E5 with a Microsoft Teams Enterprise license |
| Microsoft Purview | Sensitivity labels | Microsoft 365 E3 and E5 |
| Microsoft Syntex - SharePoint Advanced Management | Site access restrictions, conditional access policies for sites, default sensitivity labels for libraries | Microsoft Syntex - SharePoint Advanced Management |
Collaboration governance framework for Teams and Microsoft 365
Microsoft 365 provides many options for governing your collaboration solution. We recommend you use this deployment content alongside the collaboration governance content to create the best collaboration solution for your organization.
Securing Teams for sensitive and highly sensitive data
To manage access to information with different sensitivities, we've developed three different tiers of protection for Teams. You can customize any of these tiers to better address the needs or your business.
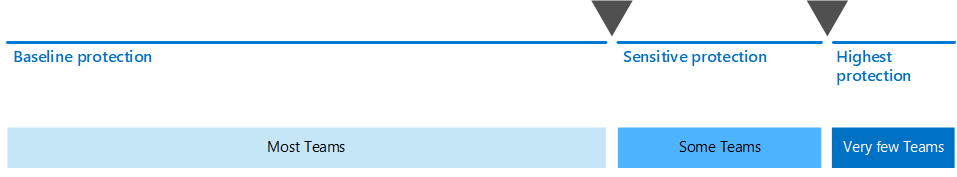
These tiers - baseline, sensitive, and highly sensitive - gradually increase the protections that help prevent oversharing and potential information leakage, as shown in the following table.
| - | Baseline tier | Sensitive tier | Highly sensitive tier |
|---|---|---|---|
| Public or private team | Either | Private | Private |
| Unauthenticated sharing | Allowed | Blocked | Blocked |
| File sharing | Allowed | Allowed | Limited to people in the team. |
| Team membership | Anyone can join public teams. Team owner approval required to join private teams. |
Team owner approval required to join. | Team owner approval required to join. |
| Document encryption | Available with sensitivity label | ||
| Guest sharing | Allowed | Can be allowed or blocked | Can be allowed or blocked |
| Unmanaged devices | No restriction | Web-only access | Blocked |
Configuring these tiers involves:
- Configuring settings in Teams for guest access and private and shared channels
- Configuring settings in a team's associated SharePoint site for internal and guest sharing, site access, and sharing links
- For the sensitive and highly sensitive tiers, configuring sensitivity labels to classify the teams, and control guest sharing and access from unmanaged devices
- For the highly sensitive tier, configuring a sensitivity label to encrypt the documents to which it's applied
Start with the baseline tier, and then add teams that use the sensitive and highly sensitive tiers as needed to help protect the information in your organization. See these resources to get started:
- Configure teams with baseline protection
- Configure teams with protection for sensitive data
- Configure teams with protection for highly sensitive data
Sharing with people outside your organization
You may need to share information of any sensitivity with people outside your organization. This could range from sharing a single document with a single person to collaborating on a major project with a large partner organization or freelancers from around the world. In Microsoft 365, this range of external sharing can be done easily and with the appropriate safeguards to help protect your sensitive information.
Read these articles to help you get started with setting up your environment for collaborating with people outside your organization:
- Collaborate on documents for sharing individual files of folders.
- Collaborate in a site for collaborating with guests in a SharePoint site.
- Collaborate as a team for collaborating with guests in a team.
- Collaborate with external participants in a channel for collaborating with people outside the organization in a shared channel.
Depending on the sensitivity of the information being shared, you can add safeguards to help prevent oversharing. Read these articles to help you set up the protections that you need for your organization:
- Best practices for sharing files and folders with unauthenticated users
- Limit accidental exposure to files when sharing with people outside your organization
- Create a secure guest sharing environment
If you have a major project with a partner organization, you can use either shared channels or Azure Entitlement Management to manage the people outside your organization who you need to collaborate with.
Training for administrators
These training modules from Microsoft Learn can help you learn the collaboration, governance, and identity features in Teams and SharePoint.
Teams
- MS-700 Prepare the environment for a Microsoft Teams deployment
- MS-700 Get started with managing Microsoft Teams
- MS-700 Manage chat, teams, channels, and apps in Microsoft Teams
Identity and access
- Manage identity and access in Microsoft Entra ID
- Manage identities and governance for Azure administrators
Training for end users
These training modules can help your users use Teams, groups, and SharePoint for collaboration in Microsoft 365.
| Teams | SharePoint |
|---|---|
 Create a team with templates |
 Create and share files in a library |
 Upload and share files |
|
 Collaborate in teams and channels |
Illustrations
These illustrations show how groups and teams interact with other services in Microsoft 365 and what governance and compliance features are available to help you manage these services in your organization.
Groups in Microsoft 365 for IT Architects
What IT architects need to know about groups in Microsoft 365
| Item | Description |
|---|---|
 PDF |Visio Updated August 2023 |
These illustrations detail the different types of groups, how these are created and managed, and a few governance recommendations. |
Microsoft Teams and related productivity services in Microsoft 365 for IT architects
The logical architecture of productivity services in Microsoft 365, leading with Microsoft Teams.
| Item | Description |
|---|---|
 PDF |Visio Updated September 2023 |
Microsoft provides a suite of productivity services that work together to provide collaboration experiences with data governance, security, and compliance capabilities. This series of illustrations provides a view into the logical architecture of productivity services for enterprise architects, leading with Microsoft Teams. |
Next steps
When you're ready to set up a secure collaboration environment, follow these steps:
- Configure the three different tiers of protection for Teams.
- Configure settings for sharing information of any sensitivity with people outside your organization.
See also
Microsoft 365 security documentation