Configure SAM-R to enable lateral movement path detection in Microsoft Defender for Identity
Microsoft Defender for Identity mapping for potential lateral movement paths relies on queries that identify local admins on specific machines. These queries are performed with the SAM-R protocol, using the Defender for Identity Directory Service account you configured.
This article describes the configuration changes required to allow the Defender for Identity Directory Services Account (DSA) to perform the SAM-R queries.
Tip
While this procedure is optional, we recommend that you configure a Directory Service account and configure SAM-R for lateral movement path detection to fully secure your environment with Defender for Identity.
Configure SAM-R required permissions
To ensure that Windows clients and servers allow your Defender for Identity Directory Services Account (DSA) to perform SAM-R queries, you must modify the Group Policy and add the DSA, in addition to the configured accounts listed in the Network access policy. Make sure to apply group policies to all computers except domain controllers.
Important
Perform this procedure in audit mode first, verifying the compatibility of the proposed configuration before making the changes to your production environment.
Testing in audit mode is critical in ensuring that your environment remains secure, and any changes will not impact your application compatibility. You may observe increased SAM-R traffic, generated by the Defender for Identity sensors.
To configure required permissions:
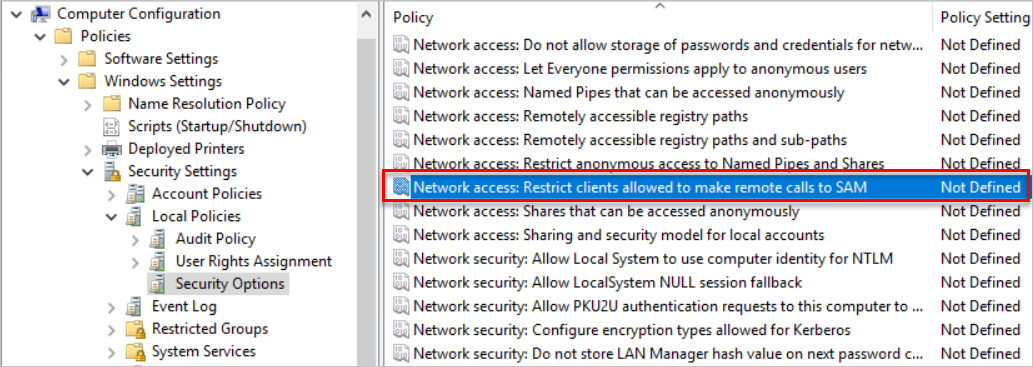
Locate the policy. In your Computer configuration > Windows settings > Security settings > Local policies > Security options, select the Network access - Restrict clients allowed to make remote calls to SAM policy. For example:
Add the DSA to the list of approved accounts able to perform this action, together with any other account that you've discovered during audit mode
For more information, see Network access: Restrict clients allowed to make remote calls to SAM.
Make sure the DSA is allowed to access computers from the network (optional)
Note
This procedure is only required if you've ever configured the Access this computer from the network setting, as the Access this computer from the network setting isn't configured by default
To add the DSA to the list of allowed accounts:
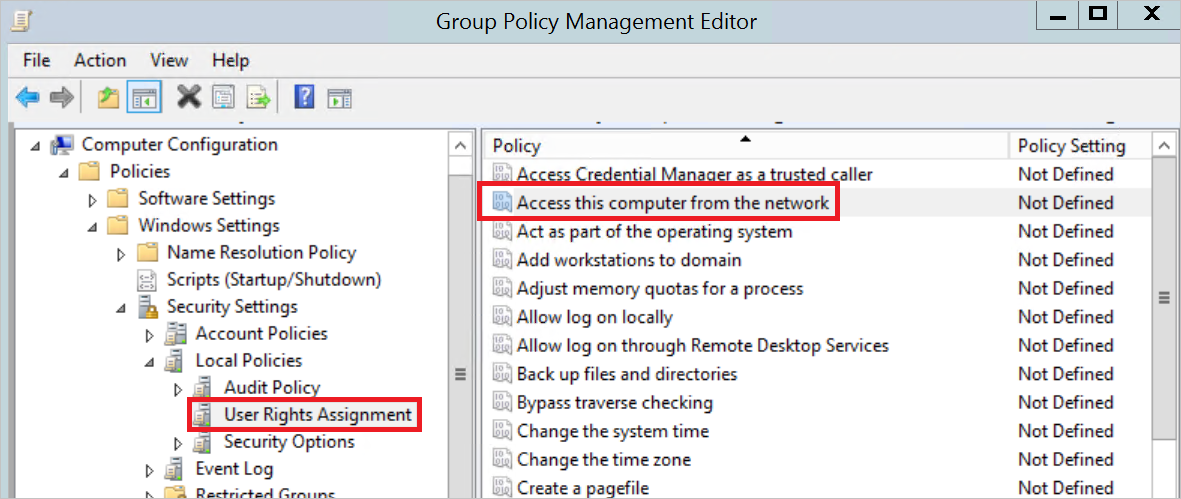
Go to the policy and navigate to Computer Configuration -> Policies -> Windows Settings -> Local Policies -> User Right Assignment, and select the Access this computer from the network setting. For example:
Add the Defender for Identity Directory Service account to the list of approved accounts.
Important
When configuring user rights assignments in group policies, it's important to note that the setting replaces the previous one rather than adding to it. Therefore, make sure to include all the desired accounts in the effective group policy. By default, workstations and servers include the following accounts: Administrators, Backup Operators, Users, and Everyone
The Microsoft Security Compliance Toolkit recommends replacing the default Everyone with Authenticated Users to prevent anonymous connections from performing network sign-ins. Review your local policy settings before managing the Access this computer from the network setting from a GPO, and consider including Authenticated Users in the GPO if needed.
Configure a Device profile for Microsoft Entra hybrid joined devices only
This procedure describes how to use the Microsoft Intune admin center to configure the policies in a Device profile if you're working with Microsoft Entra hybrid joined devices.
In the Microsoft Intune admin center, create a new Device profile, defining the following values:
- Platform: Windows 10 or later
- Profile type: Settings catalog
Enter a meaningful name and description for your policy.
Add settings to define a NetworkAccess_RestrictClientsAllowedToMakeRemoteCallsToSAM policy:
In the Settings picker, search for Network Access Restrict Clients Allowed To Make Remote Calls To SAM.
Select to browse by the Local Policies Security Options category, and then select the Network Access Restrict Clients Allowed To Make Remote Calls To SAM setting.
Enter the security descriptor (SDDL):
O:BAG:BAD:(A;;RC;;;BA)(A;;RC;;;%SID%), replacing%SID%with the Defender for Identity Directory Service account SID.Make sure to include the built-in Administrators group:
O:BAG:BAD:(A;;RC;;;BA)(A;;RC;;;S-1-5-32-544)
Add settings to define an AccessFromNetwork policy:
In the Settings picker, search for Access From Network.
Select to browse by the User Rights category, and then select the Access From Network setting.
Select to import settings, and then browse to and select a CSV file that contains a list of users and groups, including SIDs or names.
Make sure to include the built-in Administrators group (S-1-5-32-544), and the Defender for Identity Directory Service account SID.
Continue the wizard to select the scope tags and assignments, and select Create to create your profile.
For more information, see Apply features and settings on your devices using device profiles in Microsoft Intune.