Microsoft Entra External ID enables your organization to manage customers’ identities, and securely control access to your public facing applications and APIs. Applications where your customers can buy your products, subscribe to your services, or access their account and data. Your customers only need to sign in on a device or a web browser once and have access to all your applications you granted them permissions.
To enable your application to sign in with External ID, you need to register your app with External ID. The app registration establishes a trust relationship between the app and External ID.
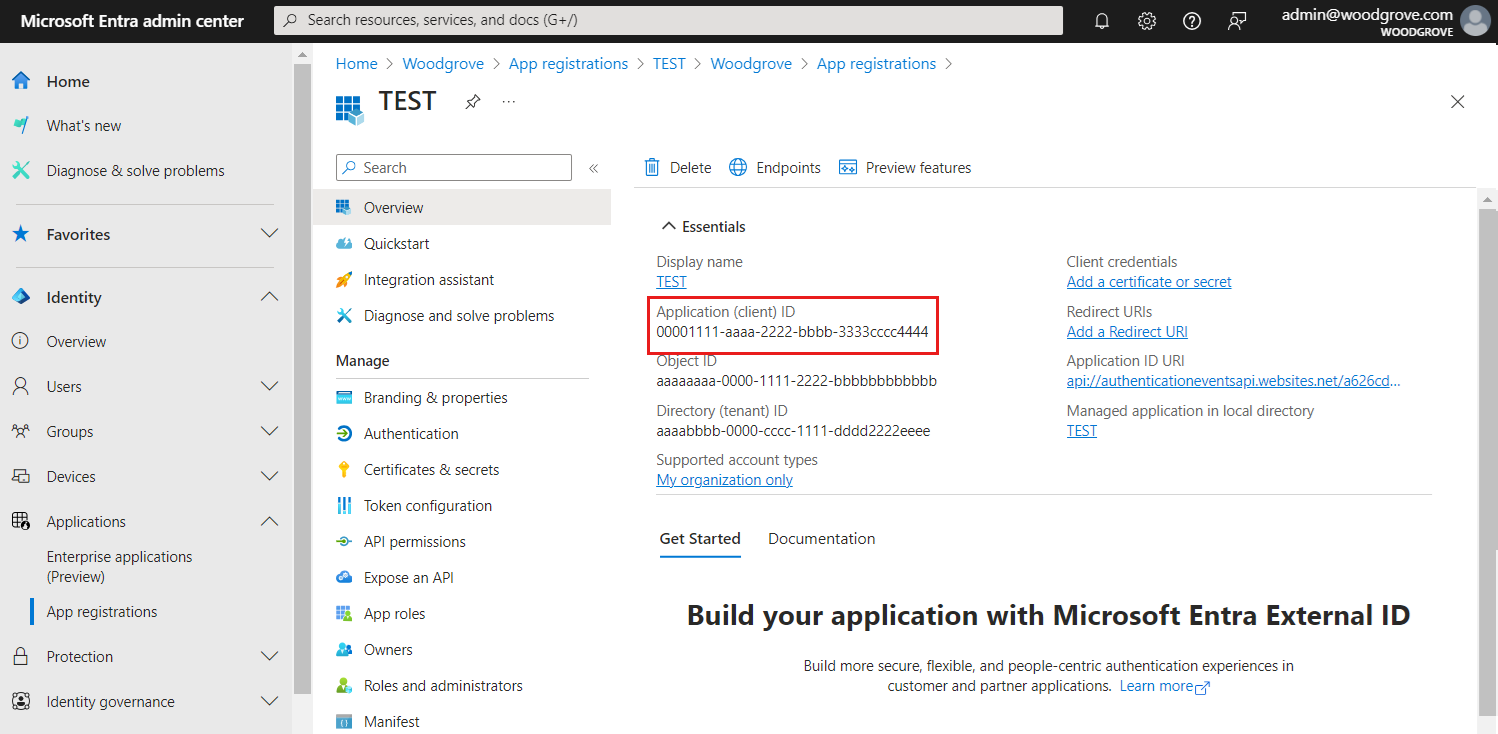
During app registration, you specify the redirect URI. The redirect URI is the endpoint to which users are redirected by External ID after they authenticate. The app registration process generates an application ID, also known as the client ID, that uniquely identifies your app.
External ID supports authentication for various modern application architectures, for example web app or single-page app. The interaction of each application type with the external tenant is different, therefore, you must specify the type of application you want to register.
In this article, you learn how to register an OpenID Connect (OIDC) application in your external tenant. You can also register a SAML app in your external tenant by adding it to your enterprise applications (learn more).
Register your Single-page app
External ID supports authentication for Single-page apps (SPAs).
The following steps show you how to register your SPA in the Microsoft Entra admin center:
Sign in to the Microsoft Entra admin center as at least an Application Developer.
If you have access to multiple tenants, use the Settings icon  in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
Browse to Identity > Applications > App registrations.
Select + New registration.
In the Register an application page that appears, enter your application's registration information:
In the Name section, enter a meaningful application name that is displayed to users of the app, for example ciam-client-app.
Under Supported account types, select Accounts in this organizational directory only.
Under Redirect URI (optional), select Single-page application (SPA) and then, in the URL box, enter http://localhost:3000/.
Select Register.
The application's Overview pane is displayed when registration is complete. Record the Directory (tenant) ID and the Application (client) ID to be used in your application source code.
About redirect URI
The redirect URI is the endpoint where the user is sent to by the authorization server (in this case, Microsoft Entra ID) after completing its interaction with the user, and to which an access token or authorization code is sent to upon successful authorization.
In a production application, it's typically a publicly accessible endpoint where your app is running, like https://contoso.com/auth-response.
During app development, you might add the endpoint where your application listens locally, like http://localhost:3000. You can add and modify redirect URIs in your registered applications at any time.
The following restrictions apply to redirect URIs:
The reply URL must begin with the scheme https, unless you use a localhost redirect URL.
The reply URL is case-sensitive. Its case must match the case of the URL path of your running application. For example, if your application includes as part of its path .../abc/response-oidc, do not specify .../ABC/response-oidc in the reply URL. Because the web browser treats paths as case-sensitive, cookies associated with .../abc/response-oidc may be excluded if redirected to the case-mismatched .../ABC/response-oidc URL.
The reply URL should include or exclude the trailing forward slash as your application expects it. For example, https://contoso.com/auth-response and https://contoso.com/auth-response/ might be treated as non-matching URLs in your application.
Grant admin consent
Once you register your application, it gets assigned the User.Read permission. However, since the tenant is an external tenant, the customer users themselves can't consent to this permission. You as the admin must consent to this permission on behalf of all the users in the tenant:
From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
Under Manage, select API permissions.
- Select Grant admin consent for <your tenant name>, then select Yes.
- Select Refresh, then verify that Granted for <your tenant name> appears under Status for the permission.
Grant API permissions (optional):
If your SPA needs to call an API, you must grant your SPA API permissions so it can call the API. You must also register the web API that you need to call.
To grant your client app (ciam-client-app) API permissions, follow these steps:
From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
Under Manage, select API permissions.
Under Configured permissions, select Add a permission.
Select the APIs my organization uses tab.
In the list of APIs, select the API such as ciam-ToDoList-api.
Select Delegated permissions option.
From the permissions list, select ToDoList.Read, ToDoList.ReadWrite (use the search box if necessary).
Select the Add permissions button. At this point, you've assigned the permissions correctly. However, since the tenant is a customer's tenant, the consumer users themselves can't consent to these permissions. To address this problem, you as the admin must consent to these permissions on behalf of all the users in the tenant:
Select Grant admin consent for <your tenant name>, then select Yes.
Select Refresh, then verify that Granted for <your tenant name> appears under Status for both scopes.
From the Configured permissions list, select the ToDoList.Read and ToDoList.ReadWrite permissions, one at a time, and then copy the permission's full URI for later use. The full permission URI looks something similar to api://{clientId}/{ToDoList.Read} or api://{clientId}/{ToDoList.ReadWrite}.
If you'd like to learn how to expose the permissions by adding a link, go to the Web API section.
Test the user flow (optional)
To test a user flow with this app registration, enable the implicit grant flow for authentication.
Important
The implicit flow should be used only for testing purposes and not for authenticating users in your production apps. Once you have finished testing, we recommend removing it.
To enable the implicit flow, follow these steps:
- Sign in to the Microsoft Entra admin center as at least an Application Developer.
- If you have access to multiple tenants, use the Settings icon
 in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
- Browse to Identity >Applications > App registrations.
- Select the app registration you created.
- Under Manage, select Authentication.
- Under Implicit grant and hybrid flows, select the ID tokens (used for implicit and hybrid flows) checkbox.
- Select Save.
Register your Web app
External ID supports authentication for web apps.
The following steps show you how to register your web app in the Microsoft Entra admin center:
Sign in to the Microsoft Entra admin center as at least an Application Developer.
If you have access to multiple tenants, use the Settings icon  in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
Browse to Identity > Applications > App registrations.
Select + New registration.
In the Register an application page that appears, enter your application's registration information:
In the Name section, enter a meaningful application name that is displayed to users of the app, for example ciam-client-app.
Under Supported account types, select Accounts in this organizational directory only.
Under Redirect URI (optional), select Web and then, in the URL box, enter a URL such as, http://localhost:3000/.
Select Register.
The application's Overview pane is displayed when registration is complete. Record the Directory (tenant) ID and the Application (client) ID to be used in your application source code.
About redirect URI
The redirect URI is the endpoint where the user is sent to by the authorization server (in this case, Microsoft Entra ID) after completing its interaction with the user, and to which an access token or authorization code is sent to upon successful authorization.
In a production application, it's typically a publicly accessible endpoint where your app is running, like https://contoso.com/auth-response.
During app development, you might add the endpoint where your application listens locally, like http://localhost:3000. You can add and modify redirect URIs in your registered applications at any time.
The following restrictions apply to redirect URIs:
The reply URL must begin with the scheme https, unless you use a localhost redirect URL.
The reply URL is case-sensitive. Its case must match the case of the URL path of your running application. For example, if your application includes as part of its path .../abc/response-oidc, do not specify .../ABC/response-oidc in the reply URL. Because the web browser treats paths as case-sensitive, cookies associated with .../abc/response-oidc may be excluded if redirected to the case-mismatched .../ABC/response-oidc URL.
The reply URL should include or exclude the trailing forward slash as your application expects it. For example, https://contoso.com/auth-response and https://contoso.com/auth-response/ might be treated as non-matching URLs in your application.
Grant admin consent
Once you register your application, it gets assigned the User.Read permission. However, since the tenant is an external tenant, the customer users themselves can't consent to this permission. You as the admin must consent to this permission on behalf of all the users in the tenant:
From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
Under Manage, select API permissions.
- Select Grant admin consent for <your tenant name>, then select Yes.
- Select Refresh, then verify that Granted for <your tenant name> appears under Status for the permission.
Create a client secret
Create a client secret for the registered application. The application uses the client secret to prove its identity when it requests for tokens.
- From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
- Under Manage, select Certificates & secrets.
- Select New client secret.
- In the Description box, enter a description for the client secret (for example, ciam app client secret).
- Under Expires, select a duration for which the secret is valid (per your organizations security rules), and then select Add.
- Record the secret's Value. You'll use this value for configuration in a later step. The secret value won't be displayed again, and isn't retrievable by any means, after you navigate away from the Certificates and secrets. Make sure you record it.
Grant API permissions (optional)
If your web app needs to call an API, you must grant your web app API permissions so it can call the API. You must also register the web API that you need to call.
To grant your client app (ciam-client-app) API permissions, follow these steps:
From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
Under Manage, select API permissions.
Under Configured permissions, select Add a permission.
Select the APIs my organization uses tab.
In the list of APIs, select the API such as ciam-ToDoList-api.
Select Delegated permissions option.
From the permissions list, select ToDoList.Read, ToDoList.ReadWrite (use the search box if necessary).
Select the Add permissions button. At this point, you've assigned the permissions correctly. However, since the tenant is a customer's tenant, the consumer users themselves can't consent to these permissions. To address this problem, you as the admin must consent to these permissions on behalf of all the users in the tenant:
Select Grant admin consent for <your tenant name>, then select Yes.
Select Refresh, then verify that Granted for <your tenant name> appears under Status for both scopes.
From the Configured permissions list, select the ToDoList.Read and ToDoList.ReadWrite permissions, one at a time, and then copy the permission's full URI for later use. The full permission URI looks something similar to api://{clientId}/{ToDoList.Read} or api://{clientId}/{ToDoList.ReadWrite}.
Test the user flow (optional)
To test a user flow with this app registration, enable the implicit grant flow for authentication.
Important
The implicit flow should be used only for testing purposes and not for authenticating users in your production apps. Once you have finished testing, we recommend removing it.
To enable the implicit flow, follow these steps:
- Sign in to the Microsoft Entra admin center as at least an Application Developer.
- If you have access to multiple tenants, use the Settings icon
 in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
- Browse to Identity >Applications > App registrations.
- Select the app registration you created.
- Under Manage, select Authentication.
- Under Implicit grant and hybrid flows, select the ID tokens (used for implicit and hybrid flows) checkbox.
- Select Save.
Register your Web API
Sign in to the Microsoft Entra admin center as at least an Application Developer.
If you have access to multiple tenants, use the Settings icon  in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
Browse to Identity > Applications > App registrations.
Select + New registration.
In the Register an application page that appears, enter your application's registration information:
In the Name section, enter a meaningful application name that will be displayed to users of the app, for example ciam-ToDoList-api.
Under Supported account types, select Accounts in this organizational directory only.
Select Register to create the application.
The application's Overview pane is displayed when registration is complete. Record the Directory (tenant) ID and the Application (client) ID to be used in your application source code.
Expose permissions
An API needs to publish a minimum of one scope, also called Delegated Permission, for the client apps to obtain an access token for a user successfully. To publish a scope, follow these steps:
From the App registrations page, select the API application that you created (ciam-ToDoList-api) to open its Overview page.
Under Manage, select Expose an API.
At the top of the page, next to Application ID URI, select the Add link to generate a URI that is unique for this app.
Accept the proposed Application ID URI such as api://{clientId}, and select Save. When your web application requests an access token for the web API, it adds the URI as the prefix for each scope that you define for the API.
Under Scopes defined by this API, select Add a scope.
Enter the following values that define a read access to the API, then select Add scope to save your changes:
| Property |
Value |
| Scope name |
ToDoList.Read |
| Who can consent |
Admins only |
| Admin consent display name |
Read users ToDo list using the 'TodoListApi' |
| Admin consent description |
Allow the app to read the user's ToDo list using the 'TodoListApi'. |
| State |
Enabled |
Select Add a scope again, and enter the following values that define a read and write access scope to the API. Select Add scope to save your changes:
| Property |
Value |
| Scope name |
ToDoList.ReadWrite |
| Who can consent |
Admins only |
| Admin consent display name |
Read and write users ToDo list using the 'ToDoListApi' |
| Admin consent description |
Allow the app to read and write the user's ToDo list using the 'ToDoListApi' |
| State |
Enabled |
Under Manage, select Manifest to open the API manifest editor.
Set accessTokenAcceptedVersion property to 2.
Select Save.
Learn more about the principle of least privilege when publishing permissions for a web API.
Add app roles
An API needs to publish a minimum of one app role for applications, also called Application Permission, for the client apps to obtain an access token as themselves. Application permissions are the type of permissions that APIs should publish when they want to enable client applications to successfully authenticate as themselves and not need to sign-in users. To publish an application permission, follow these steps:
From the App registrations page, select the application that you created (such as ciam-ToDoList-api) to open its Overview page.
Under Manage, select App roles.
Select Create app role, then enter the following values, then select Apply to save your changes:
| Property |
Value |
| Display name |
ToDoList.Read.All |
| Allowed member types |
Applications |
| Value |
ToDoList.Read.All |
| Description |
Allow the app to read every user's ToDo list using the 'TodoListApi' |
Select Create app role again, then enter the following values for the second app role, then select Apply to save your changes:
| Property |
Value |
| Display name |
ToDoList.ReadWrite.All |
| Allowed member types |
Applications |
| Value |
ToDoList.ReadWrite.All |
| Description |
Allow the app to read and write every user's ToDo list using the 'ToDoListApi' |
Register your Desktop or Mobile app
The following steps show you how to register your app in the Microsoft Entra admin center:
Sign in to the Microsoft Entra admin center as at least an Application Developer.
If you have access to multiple tenants, use the Settings icon  in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
Browse to Identity > Applications > App registrations.
Select + New registration.
In the Register an application page that appears, enter your application's registration information:
In the Name section, enter a meaningful application name that is displayed to users of the app, for example ciam-client-app.
Under Supported account types, select Accounts in this organizational directory only.
Under Redirect URI (optional), select the Mobile and desktop applications option and then, in the URL box, enter a URI with a unique scheme. For example, Electron desktop app's redirect URI looks something similar to http://localhost while that of a .NET Multi-platform App UI (MAUI) looks similar to msal{ClientId}://auth.
Select Register.
The application's Overview pane is displayed when registration is complete. Record the Directory (tenant) ID and the Application (client) ID to be used in your application source code.
Grant admin consent
Once you register your application, it gets assigned the User.Read permission. However, since the tenant is an external tenant, the customer users themselves can't consent to this permission. You as the admin must consent to this permission on behalf of all the users in the tenant:
From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
Under Manage, select API permissions.
- Select Grant admin consent for <your tenant name>, then select Yes.
- Select Refresh, then verify that Granted for <your tenant name> appears under Status for the permission.
Grant API permissions (optional)
If your mobile app needs to call an API, you must grant your mobile app API permissions so it can call the API. You must also register the web API that you need to call.
To grant your client app (ciam-client-app) API permissions, follow these steps:
From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
Under Manage, select API permissions.
Under Configured permissions, select Add a permission.
Select the APIs my organization uses tab.
In the list of APIs, select the API such as ciam-ToDoList-api.
Select Delegated permissions option.
From the permissions list, select ToDoList.Read, ToDoList.ReadWrite (use the search box if necessary).
Select the Add permissions button. At this point, you've assigned the permissions correctly. However, since the tenant is a customer's tenant, the consumer users themselves can't consent to these permissions. To address this problem, you as the admin must consent to these permissions on behalf of all the users in the tenant:
Select Grant admin consent for <your tenant name>, then select Yes.
Select Refresh, then verify that Granted for <your tenant name> appears under Status for both scopes.
From the Configured permissions list, select the ToDoList.Read and ToDoList.ReadWrite permissions, one at a time, and then copy the permission's full URI for later use. The full permission URI looks something similar to api://{clientId}/{ToDoList.Read} or api://{clientId}/{ToDoList.ReadWrite}.
Test the user flow (optional)
To test a user flow with this app registration, enable the implicit grant flow for authentication.
Important
The implicit flow should be used only for testing purposes and not for authenticating users in your production apps. Once you have finished testing, we recommend removing it.
To enable the implicit flow, follow these steps:
- Sign in to the Microsoft Entra admin center as at least an Application Developer.
- If you have access to multiple tenants, use the Settings icon
 in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
- Browse to Identity >Applications > App registrations.
- Select the app registration you created.
- Under Manage, select Authentication.
- Under Implicit grant and hybrid flows, select the ID tokens (used for implicit and hybrid flows) checkbox.
- Select Save.
Register your Daemon app
The following steps show you how to register your daemon app in the Microsoft Entra admin center:
Sign in to the Microsoft Entra admin center as at least an Application Developer.
If you have access to multiple tenants, use the Settings icon  in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
Browse to Identity > Applications > App registrations.
Select + New registration.
In the Register an application page that appears, enter your application's registration information:
In the Name section, enter a meaningful application name that will be displayed to users of the app, for example ciam-client-app.
Under Supported account types, select Accounts in this organizational directory only.
Select Register.
The application's Overview pane is displayed when registration is complete. Record the Directory (tenant) ID and the Application (client) ID to be used in your application source code.
Grant API permissions
A daemon app signs in as itself using the OAuth 2.0 client credentials flow. You grant application permissions (app roles), which is required by apps that authenticate as themselves. You must also register the web API that your daemon app needs to call.
From the App registrations page, select the application that you created, such as ciam-client-app.
Under Manage, select API permissions.
Under Configured permissions, select Add a permission.
Select the APIs my organization uses tab.
In the list of APIs, select the API such as ciam-ToDoList-api.
Select Application permissions option. We select this option as the app signs in as itself, but not on behalf of a user.
From the permissions list, select TodoList.Read.All, ToDoList.ReadWrite.All (use the search box if necessary).
Select the Add permissions button.
At this point, you've assigned the permissions correctly. However, since the daemon app doesn't allow users to interact with it, the users themselves can't consent to these permissions. To address this problem, you as the admin must consent to these permissions on behalf of all the users in the tenant:
- Select Grant admin consent for <your tenant name>, then select Yes.
- Select Refresh, then verify that Granted for <your tenant name> appears under Status for both permissions.
Test the user flow (optional)
To test a user flow with this app registration, enable the implicit grant flow for authentication.
Important
The implicit flow should be used only for testing purposes and not for authenticating users in your production apps. Once you have finished testing, we recommend removing it.
To enable the implicit flow, follow these steps:
- Sign in to the Microsoft Entra admin center as at least an Application Developer.
- If you have access to multiple tenants, use the Settings icon
 in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
- Browse to Identity >Applications > App registrations.
- Select the app registration you created.
- Under Manage, select Authentication.
- Under Implicit grant and hybrid flows, select the ID tokens (used for implicit and hybrid flows) checkbox.
- Select Save.
Register a Microsoft Graph API application
To enable your application to sign in users with Microsoft Entra, Microsoft Entra External ID must be made aware of the application you create. The app registration establishes a trust relationship between the app and Microsoft Entra. When you register an application, External ID generates a unique identifier known as an Application (client) ID, a value used to identify your app when creating authentication requests.
The following steps show you how to register your app in the Microsoft Entra admin center:
Sign in to the Microsoft Entra admin center as at least an Application Developer.
If you have access to multiple tenants, use the Settings icon  in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
Browse to Identity >Applications > App registrations.
Select + New registration.
In the Register an application page that appears;
- Enter a meaningful application Name that is displayed to users of the app, for example ciam-client-app.
- Under Supported account types, select Accounts in this organizational directory only.
Select Register.
The application's Overview pane displays upon successful registration. Record the Application (client) ID to be used in your application source code.
Grant API Access to your application
For your application to access data in Microsoft Graph API, grant the registered application the relevant application permissions. The effective permissions of your application are the full level of privileges implied by the permission. For example, to create, read, update, and delete every user in your external tenant, add the User.ReadWrite.All permission.
Under Manage, select API permissions.
Under Configured permissions, select Add a permission.
Select the Microsoft APIs tab, then select Microsoft Graph.
Select Application permissions.
Expand the appropriate permission group and select the check box of the permission to grant to your management application. For example:
User > User.ReadWrite.All: For user migration or user management scenarios.
Group > Group.ReadWrite.All: For creating groups, read and update group memberships, and delete groups.
AuditLog > AuditLog.Read.All: For reading the directory's audit logs.
Policy > Policy.ReadWrite.TrustFramework: For continuous integration/continuous delivery (CI/CD) scenarios. For example, custom policy deployment with Azure Pipelines.
Select Add permissions. As directed, wait a few minutes before proceeding to the next step.
Select Grant admin consent for (your tenant name).
If you are not currently signed-in, sign in with an account in your external tenant that's been assigned at least the Cloud Application Administrator role and then select Grant admin consent for (your tenant name).
Select Refresh, and then verify that "Granted for ..." appears under Status. It might take a few minutes for the permissions to propagate.
After you have registered your application, you need to add a client secret to your application. This client secret will be used to authenticate your application to call the Microsoft Graph API.
Create a client secret
Create a client secret for the registered application. The application uses the client secret to prove its identity when it requests for tokens.
- From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
- Under Manage, select Certificates & secrets.
- Select New client secret.
- In the Description box, enter a description for the client secret (for example, ciam app client secret).
- Under Expires, select a duration for which the secret is valid (per your organizations security rules), and then select Add.
- Record the secret's Value. You'll use this value for configuration in a later step. The secret value won't be displayed again, and isn't retrievable by any means, after you navigate away from the Certificates and secrets. Make sure you record it.
Test the user flow (optional)
To test a user flow with this app registration, enable the implicit grant flow for authentication.
Important
The implicit flow should be used only for testing purposes and not for authenticating users in your production apps. Once you have finished testing, we recommend removing it.
To enable the implicit flow, follow these steps:
- Sign in to the Microsoft Entra admin center as at least an Application Developer.
- If you have access to multiple tenants, use the Settings icon
 in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
- Browse to Identity >Applications > App registrations.
- Select the app registration you created.
- Under Manage, select Authentication.
- Under Implicit grant and hybrid flows, select the ID tokens (used for implicit and hybrid flows) checkbox.
- Select Save.
Register a native authentication application
To enable your application to sign in users with Microsoft Entra, Microsoft Entra External ID must be made aware of the application you create. The app registration establishes a trust relationship between the app and Microsoft Entra. When you register an application, External ID generates a unique identifier known as an Application (client) ID, a value used to identify your app when creating authentication requests.
The following steps show you how to register your app in the Microsoft Entra admin center:
Sign in to the Microsoft Entra admin center as at least an Application Developer.
If you have access to multiple tenants, use the Settings icon  in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.
Browse to Identity >Applications > App registrations.
Select + New registration.
In the Register an application page that appears;
- Enter a meaningful application Name that is displayed to users of the app, for example ciam-client-app.
- Under Supported account types, select Accounts in this organizational directory only.
Select Register.
The application's Overview pane displays upon successful registration. Record the Application (client) ID to be used in your application source code.
Grant admin consent
Once you register your application, it gets assigned the User.Read permission. However, since the tenant is an external tenant, the customer users themselves can't consent to this permission. You as the admin must consent to this permission on behalf of all the users in the tenant:
From the App registrations page, select the application that you created (such as ciam-client-app) to open its Overview page.
Under Manage, select API permissions.
- Select Grant admin consent for <your tenant name>, then select Yes.
- Select Refresh, then verify that Granted for <your tenant name> appears under Status for the permission.
Enable public client and native authentication flows
To specify that this app is a public client and can use native authentication, enable public client and native authentication flows:
- From the app registrations page, select the app registration for which you want to enable public client and native authentication flows.
- Under Manage, select Authentication.
- Under Advanced settings, allow public client flows:
- For Enable the following mobile and desktop flows select Yes.
- For Enable native authentication, select Yes.
- Select Save button.
After you register a new application, you can find the Application (client) ID from the overview in the Microsoft Entra admin center.
 Workforce tenants
Workforce tenants  External tenants (learn more)
External tenants (learn more) in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu. in the top menu to switch to your external tenant from the Directories + subscriptions menu.
in the top menu to switch to your external tenant from the Directories + subscriptions menu.