Merk
Tilgang til denne siden krever autorisasjon. Du kan prøve å logge på eller endre kataloger.
Tilgang til denne siden krever autorisasjon. Du kan prøve å endre kataloger.
Microsoft Defender for endepunkt er en sikkerhetsplattform for intelligent beskyttelse, oppdagelse, undersøkelse og respons. Defender for Endpoint beskytter endepunkter mot cybertrusler, oppdager avanserte angrep og databrudd, automatiserer sikkerhetshendelser og forbedrer sikkerhetsstillingen.
Denne artikkelen beskriver den forhåndsdefinerte integreringen som er tilgjengelig mellom Microsoft Defender for Cloud Apps og Microsoft Defender for endepunkt, noe som forenkler skyoppdagelse og aktivering av enhetsbasert undersøkelse.
Viktig
Denne artikkelen fokuserer på skyggefunksjoner for IT-søk fra Defender for endepunktlogger. Hvis du vil ha mer informasjon om skygge-IT-styrende funksjoner via Defender for Endpoint, kan du se Styre oppdagede apper ved hjelp av Microsoft Defender for endepunkt.
Forutsetninger
Microsoft Defender for Cloud Apps lisens
Enheter må være pålastet for å Microsoft Defender for endepunkt
Ett av følgende:
- Microsoft Defender for endepunkt med Plan 2
- Microsoft Defender for bedrifter (frittstående eller som en del av Microsoft 365 Business Premium)
Hvis du vil ha mer informasjon, kan du se Sammenligne sikkerhetsplaner for Microsoft-endepunkt.
Apper som bruker ett av følgende operativsystemer:
- Windows 10 versjon 1709 (OS-bygg 16299.1085 med KB4493441)
- Windows 10 versjon 1803 (OS-bygg 17134.704 med KB4493464)
- Windows 10 versjon 1809 (OS-bygg 17763.379 med KB4489899) eller nyere versjoner av Windows 10 og Windows 11
- macOS, på enheter med Defender for Endpoint versjon 20.123072.25.0 eller nyere
Hvis du vil støtte integreringer for macOS-apper, må du aktivere nettverksbeskyttelsesfunksjoner i Microsoft Defender for endepunkt. Siden nettverksbeskyttelse bare overvåker hendelser for avslutning av TCP-tilkobling, dekkes ikke UDP-protokoller for macOS-støtte. Hvis du vil ha mer informasjon, kan du se Aktivere nettverksbeskyttelse
(Anbefales) Aktiver Microsoft Defender Antivirus:
Obs!
Selv om Microsoft Defender Antivirus anbefales på det sterkeste for oppdagelse, er det ikke obligatorisk. Noen oppdagelsesdata er fortsatt tilgjengelige når Defender Antivirus er deaktivert.
Slik fungerer det
På egen hånd samler Defender for Cloud Apps logger fra endepunktene dine ved hjelp av logger du laster opp, eller ved å konfigurere automatisk loggopplasting. Den forhåndsdefinerte integreringen gjør det mulig å dra nytte av loggene Defender for Endpoint-agenten oppretter når den kjører på Windows og overvåker nettverkstransaksjoner. Bruk denne informasjonen til Skygge-IT-søk på tvers av Windows-enheter på nettverket.
Integreringen krever ikke ekstra distribusjonstrinn eller ruting eller speiling av trafikk fra endepunktene, og fungerer som følger:
- Logger fra endepunktene som sendes til Defender for Cloud Apps gir informasjon om brukere og enheter for trafikkaktiviteter. Sammenkobling av enhetskontekst med brukernavnet gir et fullstendig bilde på tvers av nettverket, slik at du kan finne ut hvilken bruker som gjorde hvilken aktivitet fra hvilken enhet.
- Når du identifiserer en risikabel bruker, må du kontrollere enhetene som brukeren fikk tilgang til for å oppdage potensielle risikoer. Hvis du identifiserer en risikabel enhet, må du kontrollere alle brukerne som brukte den til å oppdage ytterligere potensielle risikoer.
- Når trafikkinformasjonen er samlet inn, er du klar til å fordype deg i bruk av skyapper i organisasjonen. Defender for Cloud Apps drar nytte av Defender for Endpoint Network Protection-funksjoner for å blokkere enhetstilgang til skyapper for endepunkt. Hvis du vil ha mer informasjon om hvordan du styrer de oppdagede appene, kan du se Styre oppdagede apper ved hjelp av Microsoft Defender for endepunkt.
Kunder som integrerer med macOS-enheter, kan observere en økning i CPU-forbruk.
Tips
Se videoene våre som viser fordelene ved å bruke Defender for endepunkt med Defender for Cloud Apps.
Integrer Microsoft Defender for endepunkt med Defender for Cloud Apps
Slik aktiverer du Defender for endepunktintegrasjon med Defender for Cloud Apps:
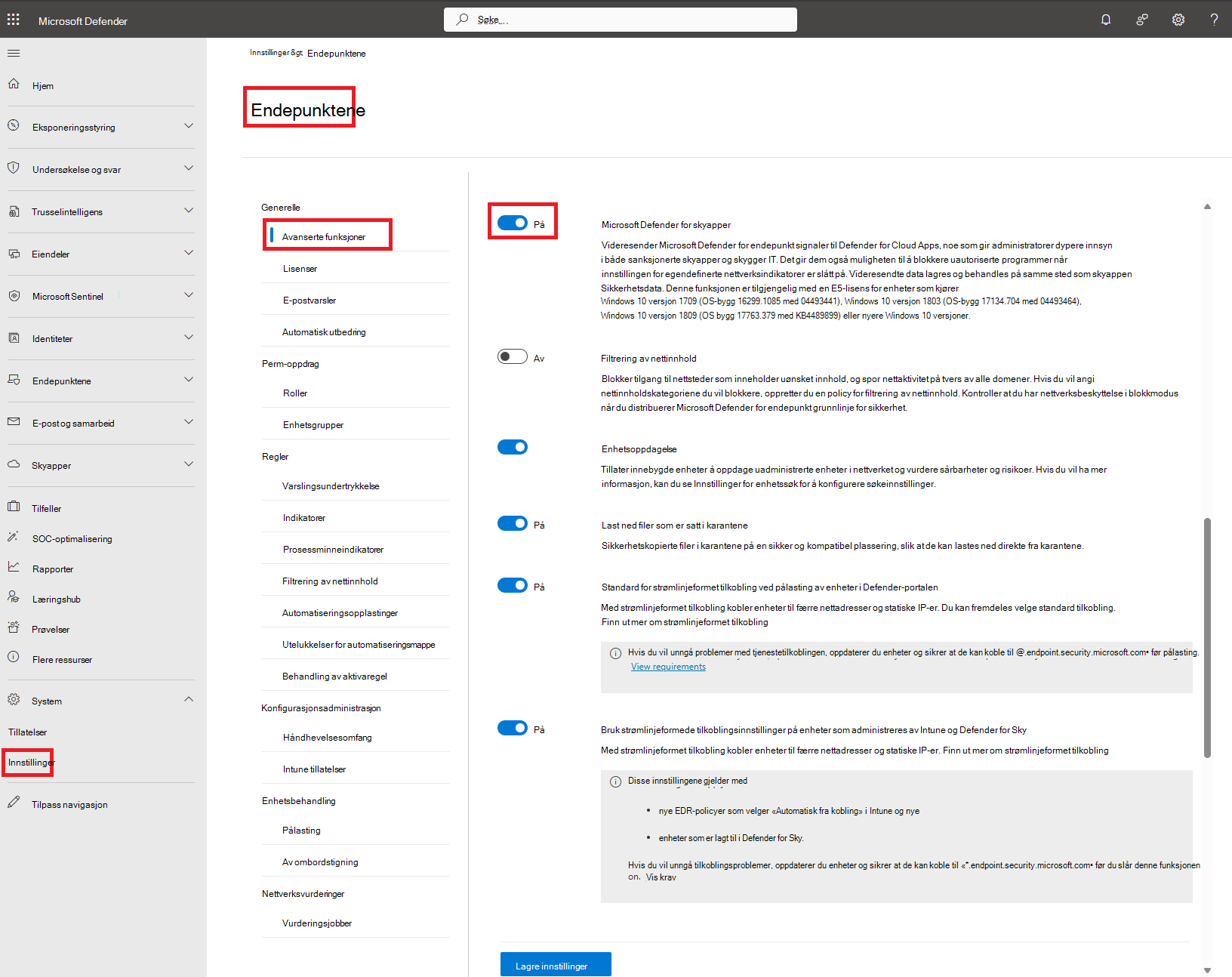
- Velg Innstillinger-endepunktenes>> generelle >avanserte funksjoner fra navigasjonsruten i Microsoft Defender-portalen.
- Aktiver/deaktiver Microsoft Defender for Cloud Apps til På.
- Velg Lagre innstillinger.
Obs!
Det tar opptil to timer etter at du har aktivert integrasjonen for at dataene skal vises i Defender for Cloud Apps.
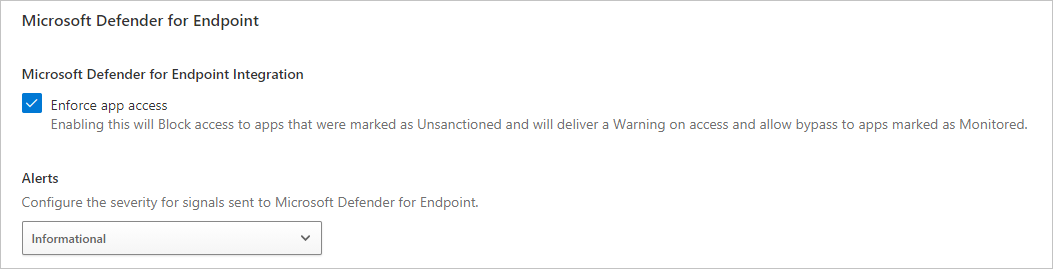
Slik konfigurerer du alvorsgraden for varsler som sendes til Microsoft Defender for endepunkt:
Velg Innstillinger> cloudapps>Cloud Discovery> i Microsoft Defender Portal Microsoft Defender for endepunkt.
Velg det globale alvorsgradnivået for varsler under Varsler.
Velg Lagre.
Neste trinn
Relaterte videoer
Hvis det oppstår problemer, er vi her for å hjelpe. Hvis du vil ha hjelp eller støtte for produktproblemet, kan du åpne en støtteforespørsel.