Provide managed security service provider (MSSP) access
Important
Some information in this article relates to a prereleased product which may be substantially modified before it's commercially released. Microsoft makes no warranties, expressed or implied, with respect to the information provided here.
Important
Procedures in this article use features that require at a minimum Microsoft Entra ID P2 for each user under scope of management.
Applies to:
To implement a multitenant delegated access solution, take the following steps:
Enable role-based access control for Defender for Endpoint via the Microsoft Defender portal and connect with Microsoft Entra groups.
Configure entitlement management for external users within Microsoft Entra ID Governance to enable access requests and provisioning.
Manage access requests and audits in Microsoft Myaccess.
Enable role-based access controls in Microsoft Defender for Endpoint in Microsoft Defender portal
Create access groups for MSSP resources in Customer Microsoft Entra ID: Groups
These groups are linked to the Roles you create in Defender for Endpoint in Microsoft Defender portal. To do so, in the customer AD tenant, create three groups. In our example approach, we create the following groups:
- Tier 1 Analyst
- Tier 2 Analyst
- MSSP Analyst Approvers
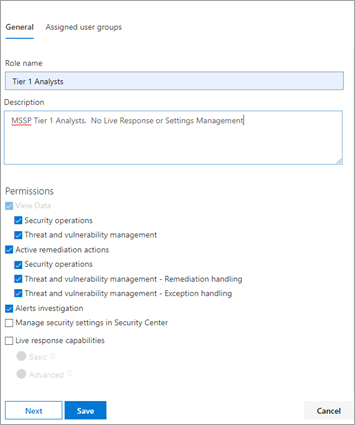
Create Defender for Endpoint roles for appropriate access levels in Customer Defender for Endpoint in Microsoft Defender portal roles and groups.
To enable RBAC in the customer Microsoft Defender portal, access Permissions > Endpoints roles & groups > Roles with a user account with Security Administrator rights.
Then, create RBAC roles to meet MSSP SOC Tier needs. Link these roles to the created user groups via "Assigned user groups".
Two possible roles:
Tier 1 Analysts
Perform all actions except for live response and manage security settings.Tier 2 Analysts
Tier 1 capabilities with the addition to live response.
For more information, see Manage portal access using role-based access control.
Configure Governance Access Packages
Add MSSP as Connected Organization in Customer Microsoft Entra ID: Identity Governance
Adding the MSSP as a connected organization allows the MSSP to request and have accesses provisioned.
To do so, in the customer AD tenant, access Identity Governance: Connected organization. Add a new organization and search for your MSSP Analyst tenant via Tenant ID or Domain. We suggest creating a separate AD tenant for your MSSP Analysts.
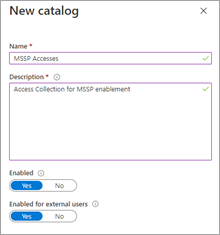
Create a resource catalog in Customer Microsoft Entra ID: Identity Governance
Resource catalogs are a logical collection of access packages, created in the customer AD tenant.
To do so, in the customer AD tenant, access Identity Governance: Catalogs, and add New Catalog. In our example, we'll call it MSSP Accesses.
Further more information, see Create a catalog of resources.
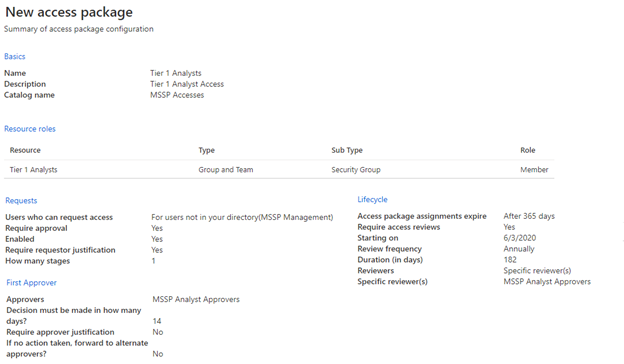
Create access packages for MSSP resources Customer Microsoft Entra ID: Identity Governance
Access packages are the collection of rights and accesses that a requestor grants upon approval.
To do so, in the customer AD tenant, access Identity Governance: Access Packages, and add New Access Package. Create an access package for the MSSP approvers and each analyst tier. For example, the following Tier 1 Analyst configuration creates an access package that:
- Requires a member of the AD group MSSP Analyst Approvers to authorize new requests
- Has annual access reviews, where the SOC analysts can request an access extension
- Can only be requested by users in the MSSP SOC Tenant
- Access auto expires after 365 days
For more information, see Create a new access package.
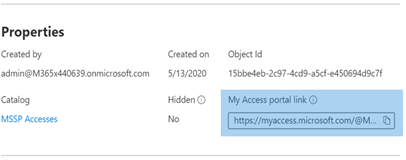
Provide access request link to MSSP resources from Customer Microsoft Entra ID: Identity Governance
The My Access portal link is used by MSSP SOC analysts to request access via the access packages created. The link is durable, meaning the same link might be used over time for new analysts. The analyst request goes into a queue for approval by the MSSP Analyst Approvers.
The link is located on the overview page of each access package.
Manage access
Review and authorize access requests in Customer and/or MSSP myaccess.
Access requests are managed in the customer My Access, by members of the MSSP Analyst Approvers group.
To do so, access the customer's myaccess using:
https://myaccess.microsoft.com/@<Customer Domain>.Example:
https://myaccess.microsoft.com/@M365x440XXX.onmicrosoft.com#/Approve or deny requests in the Approvals section of the UI.
At this point, analyst access has been provisioned, and each analyst should be able to access the customer's Microsoft Defender portal:
https://security.microsoft.com/?tid=<CustomerTenantId>with the permissions and roles they were assigned.
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender XDR Tech Community.