Hello Rakesh Kamboj,
Greetings! Welcome to Microsoft Q&A Forum.
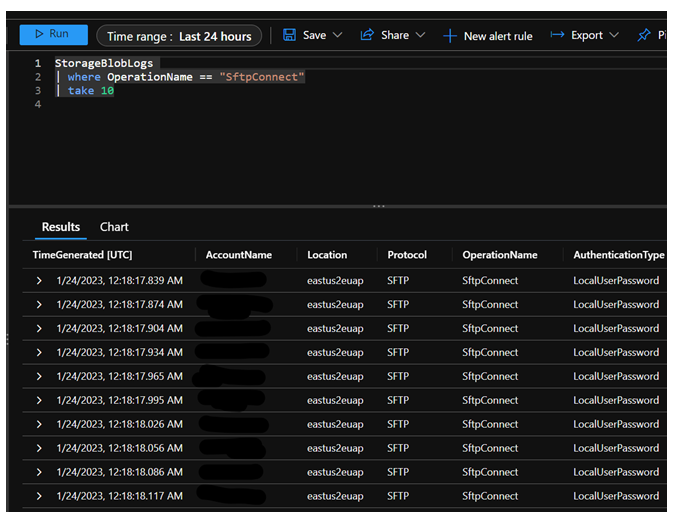
You just need to enable Azure Monitor logging in diagnostics settings: Azure Monitor Logs - Azure Monitor | Microsoft Learn
This feature is supported refer to this Doc: Blob Storage feature support in Azure storage accounts | Microsoft Learn
Classic Storage Analytics logging to $logs container is also supported, but note that not all pre-auth connection attempt failures are logged there.
Here is another similar thread that discusses the same- https://stackoverflow.com/questions/70682123/logs-for-azure-storage-account-sftp-service
If Storage account firewall setting "enabled for selected networks," but you are facing connectivity issues when connecting with an SFTP client in your environment, there are several factors to consider in order to securely allow SFTP access,
Firewall Settings:
- Verify that you have correctly added all the intended IP addresses to the whitelist.
- Ensure that your firewall rules are correctly configured to allow traffic from the whitelisted IPs.
- Confirm that the rules are applied to the correct network interface (public or private).
- check if there are any NSGs associated with your SFTP server’s subnet.
- Ensure that the NSGs allow traffic from the whitelisted IPs.
SFTP Client Configuration:
Please verify that your SFTP client is configured correctly to connect to Azure Blob Storage. Check that you are using the correct hostname, port (SFTP typically uses port 22), username and password.
Ensure that your SFTP client uses secure SFTP protocols.
Public PC Firewall and Proxy:
- Kindly check if the user PC has any local firewall or proxy settings that might be blocking the SFTP connection. You may temporarily disable local firewalls for testing purposes and check.
For limitation and known issues with SFTP, please refer: https://learn.microsoft.com/en-us/azure/storage/blobs/secure-file-transfer-protocol-known-issues
If you've checked all these points and are still experiencing issues, it may be helpful to provide specific error messages or details about the issue you're encountering.
Hope this helps. Please do let us know if you need any further assistance. Thank you!
Please "Accept the answer” and “up-vote” wherever the information provided helps you, this can be beneficial to other community members.