I am also experiencing this same issue and Bitlocker key is not getting escrowed to AAD. Note: I am using MS Endpoint Manger (Intune)- Endpoint Security -Disk Encryption Policy Template and targeting Autopilot HAADJ Windows 10 laptops.
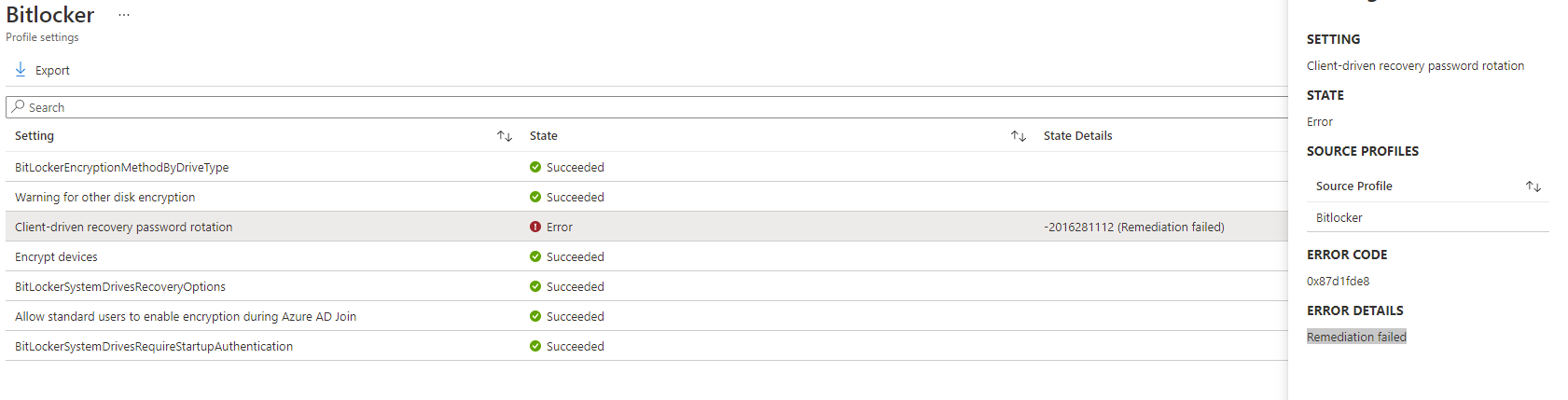
Microsoft Intune - BitLocker: Client-driven recovery password rotation error 0x87d1fde8 Remediation failed

Hello!
I'm trying to silently encrypt devices via Intune Device Configuration profile.
The endpoints are on-prem domain-joined + azureAD-registered Windows 10 machines (10.0.19042)
The error I'm getting is Client-driven recovery password rotation Fails with -2016281112 (Remediation failed) error code 0x87d1fde8
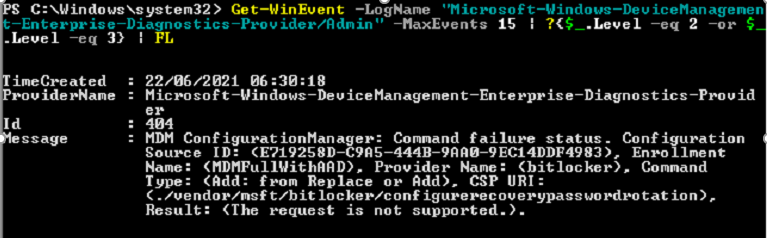
Event log on the endpoint shows that configure recovery password rotation URI request is not supported:
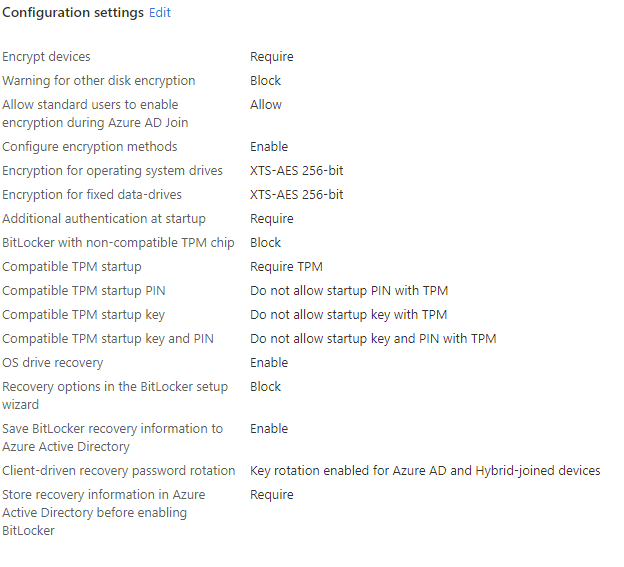
The Device configuration profile settings are:
Could you please help figure out how this can be fixed?
Microsoft Security | Intune | Configuration
Microsoft Security | Intune | Enrollment
12 answers
Sort by: Most helpful
-
-
 TG 1 Reputation point
TG 1 Reputation point2022-09-19T22:14:25.667+00:00 It looks like Intune policy doesn't automatically turn on BitLocker for Azure AD Registered devices, because they are technically joined then as personal devices.
For automatic BitLocker encryption via built-in Intune policy, the device should be Azure AD Joined and logged in to Windows with a Work or school account.
I created PowerShell scripts that can take care of automated BitLocker encryption and escrow in the case of AAD Registered devices.
-
Mo Mardini 1 Reputation point
2022-09-28T22:52:04.907+00:00 @TG - Would you be able to share your PS scripts please? This is causing a huge issue in our tenant and I would be eternally grateful! Thank you for your help.
-
Mo Mardini 1 Reputation point
2022-09-28T22:52:18.813+00:00 Was anyone else able to resolve this issue?
-
Viktor Georgievski 0 Reputation points
2023-03-22T13:35:03.61+00:00 I have noticed that this error is appearing when you haven't configured your TPM in the BIOS first.
Most of the laptops by default are with disabled TPM.
You should enable TPM and all storage keys there first and then roll your policy or Bitlocker rule again.