Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
Azure AD External Identities P2 has been retired in Azure AD B2C tenants. ID Protection as part of P2 remains available in workforce tenants. For details on billing and alternatives, see the P2 retirement FAQ.
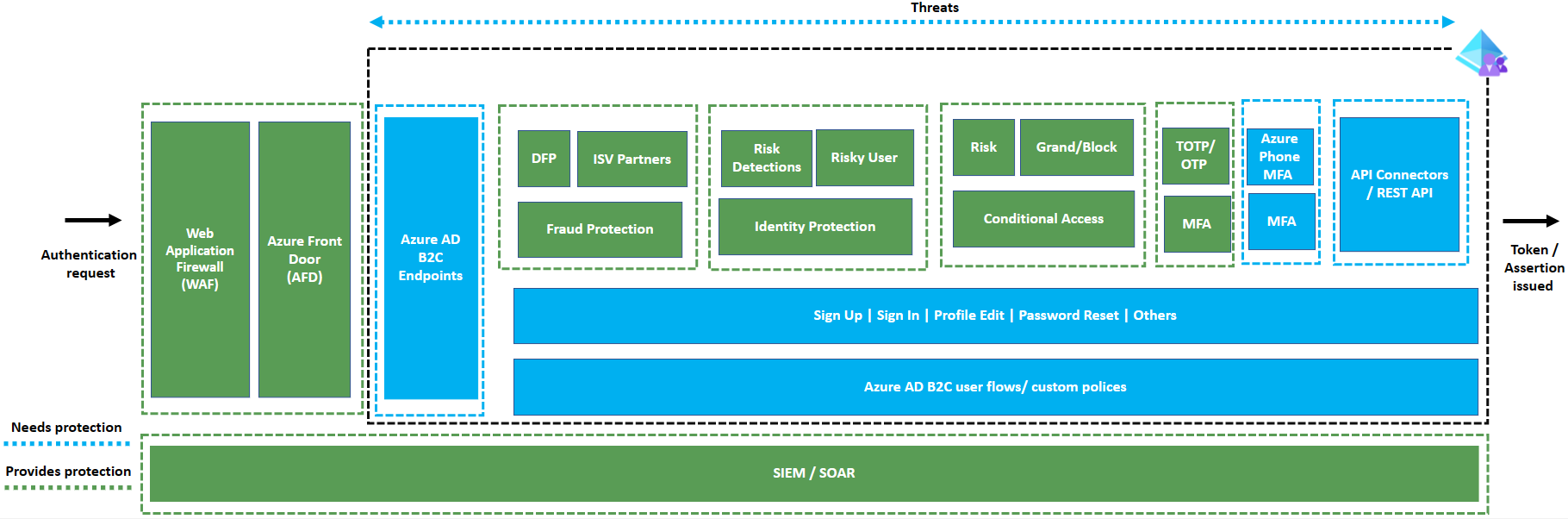
This article provides the best practices in securing your Azure Active Directory B2C (Azure AD B2C) solution. To build your identity solution using Azure AD B2C involves many components that you should consider protecting and monitoring.
Depending on your solution, you have one or more of the following components in scope:
- Azure AD B2C authentication endpoints
- Azure AD B2C user flows or custom policies
- Sign in
- Sign up
- Email One-time-password (OTP)
- Multifactor authentication controls
- External REST APIs
You must protect and monitor all these components to ensure your users can sign in to applications without disruption. Follow the guidance in this article to protect your solution from bot attacks, fraudulent account creation, international revenue share fraud (ISRF), and password spray.
How to secure your solution
Your identity solution uses multiple components to provide a smooth sign in experience. The following table shows protection mechanisms we recommend for each component.
| Component | Endpoint | Why | How to protect |
|---|---|---|---|
| Azure AD B2C authentication endpoints | /authorize, /token, /.well-known/openid-configuration, /discovery/v2.0/keys |
Prevent resource exhaustion | Web Application Firewall (WAF) and Azure Front Door (AFD) |
| Sign-in | NA | Malicious sign-in's may try to brute force accounts or use leaked credentials | Identity Protection |
| Sign-up | NA | Fraudulent sign-up's that may try to exhaust resources. | Endpoint protection Fraud prevention technologies, such as Dynamics Fraud Protection |
| Email OTP | NA | Fraudulent attempts to brute force or exhaust resources | Endpoint protection and Authenticator App |
| Multifactor authentication controls | NA | Unsolicited phone calls or SMS messages or resource exhaustion. | Endpoint protection and Authenticator App |
| External REST APIs | Your REST API endpoints | Malicious usage of user flows or custom policies can lead to resource exhaustion at your API endpoints. | WAF and AFD |
Protection mechanisms
The following table provides an overview of the different protection mechanisms you can use to protect different components.
| What | Why | How |
|---|---|---|
| Web Application Firewall (WAF) | WAF serves as the first layer of defense against malicious requests made to Azure AD B2C endpoints. It provides a centralized protection against common exploits and vulnerabilities such as DDoS, bots, OWASP Top 10, and so on. It's advised that you use WAF to ensure that malicious requests are stopped even before they reach Azure AD B2C endpoints. To enable WAF, you must first enable custom domains in Azure AD B2C using AFD. |
|
| Azure Front Door (AFD) | AFD is a global, scalable entry-point that uses the Microsoft global edge network to create fast, secure, and widely scalable web applications. The key capabilities of AFD are:
|
|
| Identity Verification & Proofing / Fraud Protection | Identity verification and proofing are critical for creating a trusted user experience and protecting against account takeover and fraudulent account creation. It also contributes to tenant hygiene by ensuring that user objects reflect the actual users, which align with business scenarios. Azure AD B2C allows the integration of identity verification and proofing, and fraud protection from various software-vendor partners. |
|
| Identity Protection | Identity Protection provides ongoing risk detection. When a risk is detected during sign-in, you can configure Azure AD B2C conditional policy to allow the user to remediate the risk before proceeding with the sign-in. Administrators can also use identity protection reports to review risky users who are at risk and review detection details. The risk detections report includes information about each risk detection, such as its type and the location of the sign-in attempt, and more. Administrators can also confirm or deny that the user is compromised. | |
| Conditional Access (CA) | When a user attempts to sign in, CA gathers various signals such as risks from identity protection, to make decisions and enforce organizational policies. CA can assist administrators to develop policies that are consistent with their organization's security posture. The policies can include the ability to completely block user access or provide access after the user has completed another authentication like MFA. | |
| Multifactor authentication | MFA adds a second layer of security to the sign-up and sign-in process and is an essential component of improving the security posture of user authentication in Azure AD B2C. The Authenticator app - TOTP is the recommended MFA method in Azure AD B2C. | |
| Security Information and Event management (SIEM)/ Security Orchestration, Automation and Response (SOAR) | You need a reliable monitoring and alerting system for analyzing usage patterns such as sign-ins and sign-ups, and detect any anomalous behavior that may be indicative of a cyberattack. It's an important step that adds an extra layer of security. It also you to understand patterns and trends that can only be captured and built upon over time. Alerting assists in determining factors such as the rate of change in overall sign-ins, an increase in failed sign-ins, and failed sign-up journeys, phone-based frauds such as IRSF attacks, and so on. All of these can be indicators of an ongoing cyberattack that requires immediate attention. Azure AD B2C supports both high level and fine grain logging, as well as the generation of reports and alerts. It's advised that you implement monitoring and alerting in all production tenants. |
Protecting your REST APIs
Azure AD B2C allows you to connect to external systems by using the API Connectors, or the REST API technical profile. You need to protect these interfaces. You can prevent malicious requests to your REST APIs by protecting the Azure AD B2C authentication endpoints. You can protect these endpoints with a WAF and AFD.
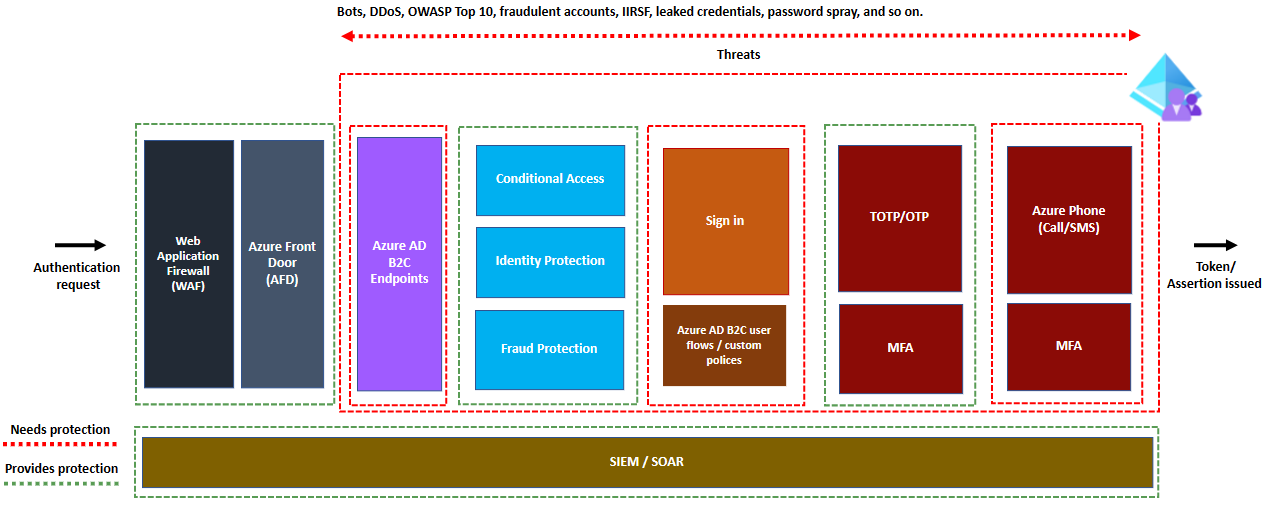
Scenario 1: How to secure your sign-in experience
After you create a sign-in experience, or user flow, you'll need to protect specific components of your flow from malicious activity. For example, if your sign in flow involves the following, then the table shows the components you need to protect, and associated protection technique:
- Local account email and password authentication
- Microsoft Entra multifactor authentication using SMS or phone call
| Component | Endpoint | How to protect |
|---|---|---|
| Azure AD B2C authentication endpoints | /authorize, /token, /.well-known/openid-configuration, /discovery/v2.0/keys |
WAP and AFD |
| Sign in | NA | Identity Protection |
| Multifactor authentication controls | NA | Authenticator app |
| External REST API | Your API endpoint. | Authenticator app, WAF and AFD |
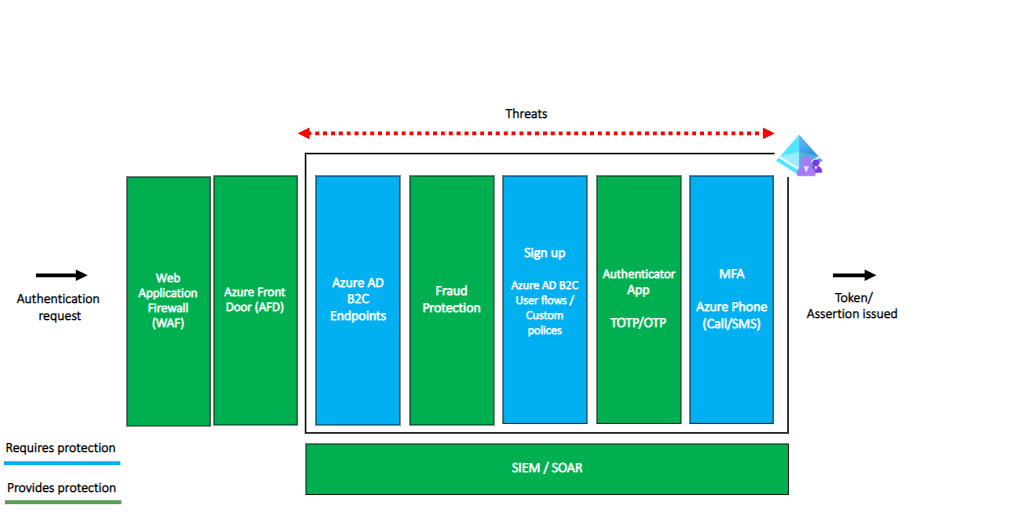
Scenario 2: How to secure your sign-up experience
After you create a sign-up experience, or user flow, you need to protect specific components of your flow from malicious activity. If your sign in flow involves the following, then the table shows the components you need to protect, and associated protection technique:
- Local account email and password sign-up
- Email verification using email OTP
- Microsoft Entra multifactor authentication using SMS or phone call
| Component | Endpoint | How to protect |
|---|---|---|
| Azure AD B2C authentication endpoints | /authorize, /token, /.well-known/openid-configuration, /discovery/v2.0/keys |
WAF and AFD |
| sign up | NA | Dynamics Fraud Protection |
| Email OTP | NA | WAF and AFD |
| Multifactor authentication controls | NA | Authenticator app |
In this scenario, the use of the WAF and AFD protection mechanisms protects both the Azure AD B2C authentication endpoints and the Email OTP components.
Next steps
- Configure a Web application firewall to protect Azure AD B2C authentication endpoints.
- Configure Fraud prevention with Dynamics to protect your authentication experiences.
- Investigate risk with Identity Protection in Azure AD B2C to discover, investigate, and remediate identity-based risks.
- Securing phone-based multifactor authentication to protect your phone based multifactor authentication.
- Configure Identity Protection to protect your sign in experience.
- Configure Monitoring and alerting to be alerted to any threats.