Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Applies to:
- Microsoft Defender for Endpoint Plan 1
- Microsoft Defender for Endpoint Plan 2
- Microsoft Defender XDR
- Microsoft Defender Antivirus
Applies to
- Windows
Want to experience Defender for Endpoint? Sign up for a free trial.
Platforms
- Windows
What is controlled folder access?
Controlled folder access helps protect your valuable data from malicious apps and threats, such as ransomware. Controlled folder access protects your data by checking apps against a list of known, trusted apps. Controlled folder access can be configured by using Microsoft Defender for Endpoint Security Settings Management, Microsoft Intune, Microsoft Endpoint Configuration Manager, or the Windows Security App.
Controlled folder access works best with Microsoft Defender for Endpoint, which gives you detailed reporting into controlled folder access events and blocks as part of the usual alert investigation scenarios.
Requirements for controlled folder access
Controlled folder access is supported on:
- Windows 11
- Windows 10
- Windows Server 2025
- Windows Server 2022
- Windows Server 2019
- Windows Server 2016
- Windows Server 2012 R2
Controlled folder access requires:
Microsoft Defender Antivirus to be the primary antivirus (active mode).
Real-Time Protection (RTP) needs to be on.
Tip
Controlled folder access blocks don't generate alerts in the Alerts queue. However, you can view information about controlled folder access blocks in the device timeline view, while using advanced hunting, or with custom detection rules.
How does controlled folder access work?
Controlled folder access works by only allowing trusted apps to access protected folders. Protected folders are specified when controlled folder access is configured. Typically, commonly used folders, such as those used for documents, pictures, downloads, and so on, are included in the list of controlled folders.
Controlled folder access works with a list of trusted apps. Apps that are included in the list of trusted software work as expected. Apps that aren't included in the list are prevented from making any changes to files inside protected folders.
Apps are added to the list based upon their prevalence and reputation. Apps that are highly prevalent throughout your organization and that haven't ever displayed any behavior deemed malicious are considered trustworthy. Those apps are added to the list automatically.
Apps can also be added manually to the trusted list by using Configuration Manager or Intune. Other actions can be performed in the Microsoft Defender portal.
Why controlled folder access is important
Controlled folder access is especially useful in helping to protect your documents and information from ransomware. In a ransomware attack, your files can get encrypted and held hostage. With controlled folder access in place, a notification appears on the computer where an app attempted to make changes to a file in a protected folder. You can customize the notification with your company details and contact information. You can also enable the rules individually to customize what techniques the feature monitors.
The protected folders include common system folders (including boot sectors), and you can add more folders. You can also allow apps to give them access to the protected folders.
You can use audit mode to evaluate how controlled folder access would impact your organization if it were enabled.
Windows system folders are protected by default
Windows system folders are protected by default, along with several other folders:
The protected folders include common system folders (including boot sectors), and you can add other folders. You can also allow apps to give them access to the protected folders. The Windows systems folders that are protected by default are:
c:\Users\<username>\Documentsc:\Users\Public\Documentsc:\Users\<username>\Picturesc:\Users\Public\Picturesc:\Users\Public\Videosc:\Users\<username>\Videosc:\Users\<username>\Musicc:\Users\Public\Musicc:\Users\<username>\Favorites
Default folders appear in the user's profile, under This PC, as shown in the following image:
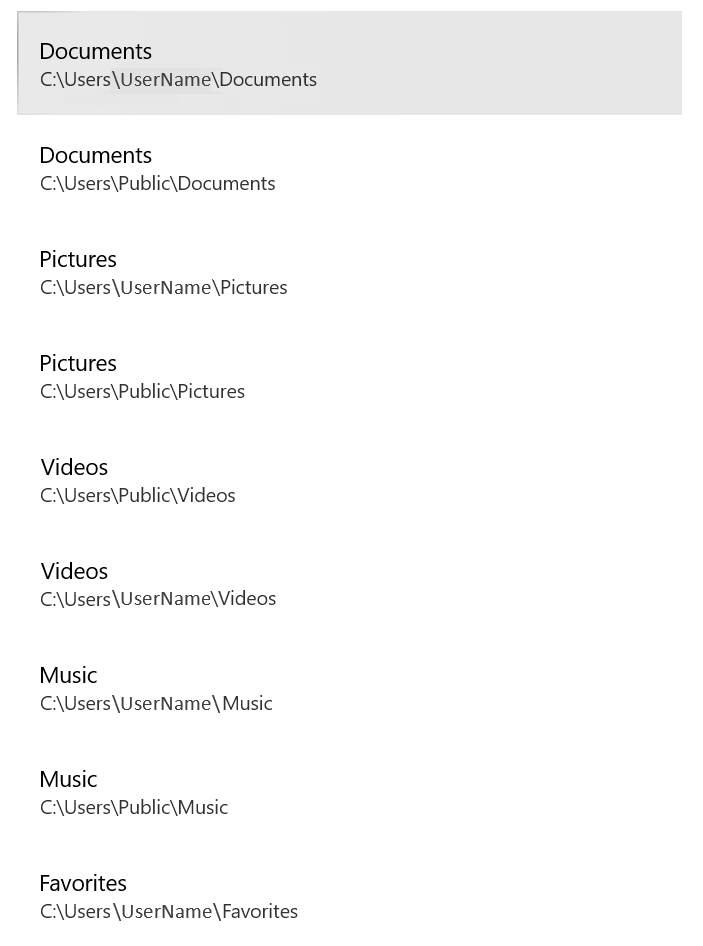
The same profile folders are also protected for system accounts, such as LocalService, NetworkService, systemprofile, and so on. For example, C:\Windows\System32\config\systemprofile\Documents is also protected (if it exists).
Note
You can configure more folders as protected, but you can't remove Windows system folders that are protected by default.
Note
Scripting engines like PowerShell aren't trusted by controlled folder access, even if you create an "allow" indicator by using certificate and file indicators. The only way to allow script engines to modify protected folders is by adding them as an allowed app. See Allow specific apps to make changes to controlled folders.
Review controlled folder access events in the Microsoft Defender portal
Tip
Controlled folder access blocks don't generate alerts in the Alerts queue. However, you can view information about controlled folder access blocks in the device timeline view, while using advanced hunting, or with custom detection rules.
Defender for Endpoint provides detailed reporting into events and blocks as part of its alert investigation scenarios in the Microsoft Defender portal. For more information, see Microsoft Defender for Endpoint in Microsoft Defender XDR.
You can query Microsoft Defender for Endpoint data by using Advanced hunting. If you're using audit mode, you can use advanced hunting to see how controlled folder access settings would affect your environment if they were enabled.
Example query:
DeviceEvents
| where ActionType in ('ControlledFolderAccessViolationAudited','ControlledFolderAccessViolationBlocked')
Review controlled folder access events in Windows Event Viewer
You can review the Windows event log to see events that are created when controlled folder access blocks (or audits) an app:
Download the Evaluation Package and extract the file cfa-events.xml to an easily accessible location on the device.
Type Event viewer in the Start menu to open the Windows Event Viewer.
On the left panel, under Actions, select Import custom view....
Navigate to where you extracted cfa-events.xml and select it. Alternatively, copy the XML directly.
Select OK.
The following table shows events related to controlled folder access:
Event ID Description 5007Event when settings are changed 1124Audited controlled folder access event 1123Blocked controlled folder access event 1127Blocked controlled folder access sector write block event 1128Audited controlled folder access sector write block event
Controlled folder access experience
A user tries to install an application that triggers Controlled folder access, if the software or application has an unknown reputation, a toast notification presents the user with the following:
Virus & threat protection
Unauthorized changes blocked
Controlled folder access blocked C:\...
\ApplicationName... from making changes to memory.
And in the Protection history, you will see:
Protected memory access blocked
MM/DD/YEAR HH:MM AM/PM
View or change the list of protected folders
You can use the Windows Security app to view the list of folders that are protected by controlled folder access.
On your Windows 10 or Windows 11 device, open the Windows Security app.
Select Virus & threat protection.
Under Ransomware protection, select Manage ransomware protection.
If controlled folder access is turned off, you need to turn it on. Select protected folders.
Take one of the following steps:
- To add a folder, select + Add a protected folder.
- To remove a folder, select it, and then select Remove.
Important
Don't add local share paths (loopbacks) as protected folders. Use the local path instead. For example, if you have shared
C:\demoas\\mycomputer\demo, don't add\\mycomputer\demoto the list of protected folders. Instead addC:\demo.
Windows system folders are protected by default, and you can't remove them from the list. Subfolders are also included in protection when you add a new folder to the list.
Tip
Do you want to learn more? Engage with the Microsoft Security community in our Tech Community: Microsoft Defender for Endpoint Tech Community.